Cyber War Is Boring by Paddy Kerley
Show transcript [en]
hey everyone so uh i'm going to talk about how cyber war is boring for a bit of background uh i'm paddy there's a bit of noise and uh i'm normally someone who does uh cyber things that's what i'm supposed to do i'm originally from tu dublin but i spent more of my time as the community manager for the open source r for the arms control one network of blogs and podcasts where i mostly plan the needs of open source intelligence analysts for the future and do some research in myself some of which i've been lucky enough to have in the washington post and the economist and as well as this uh normally i have a giant
blog written with everything that i have sourced and some more things i'm not going to have the chance to talk about in a talk i don't have that blog written because this talk was written in nine days for b-sides so uh if you go to that link that'll uh eventually there will be a blog post up with everything you need from this as well as this a quick disclaimer i am going to be talking about the war in ukraine if you are sick of the war in ukraine this is definitely not the talk for you uh there is no dead bodies or anything like that but there are equipment on fire that kind of thing so
if you have ptsd or any triggers like that this might not be the talk for you and finally i stopped adding things to the presentation about 36 hours ago and i know some things have changed since i am aware of those but at some point i have to stop talking so um this kind the genesis of this talk comes from a friend of mine don edwards who said that uh there's been a lot of talk about cyber warfare but yet we have yet to see anything um so i'm gonna try and explain why we aren't seeing it and more importantly why it's quite a lot less interesting than a lot of people are led to believe
and the idea for war is boring comes from comic book artist david axe who said that cyber war is a lot more about politics paperwork and logistics than it is about the actual combat and in a lot of ways i think cyber is the same but rather it's more about politics the legalities around cyber and then perceptions that people have of cyber so if we look at the politics um uh the late looking at cyber through the lens of clouds is kind of the best way to kind of think about how cyber impacts people in these kind of ways so how states actually use it and much like war cyber is an extension of policy by other
means this is to say that if you look at the world as a runway you have a number of actions that governments can take they have the runway that is as long as it is and then using cyber or going to war allows you to add length onto the runway for you to continue different actions great example of this in recent memory comes from this thing here this is called the bronze soldier it's a statue in tallinn estonia this originally used to be in the city center in thailand and it marked the graves of 12 soviet soldiers who died fighting the nazis in world war ii [Music] estonia continued fighting for their freedom from the soviets into the 1950s
i think 53-54 they were still fighting the conflict so to a lot of estonians this right this statue represents a a kind of a way that they've had their freedom crushed by the soviets and to a lot of ethnic russians this statue represents victory over the nazis so this beca becomes a contentious issue and in the city center they decided we're going to move the statue the government um and they're going to move it elsewhere and of course this generated uh protests and the protests ran for a period of about two weeks but in those two weeks uh the kremlin started playing around with what we have become familiar with today as cyber warfare they started with ddos attacks
they defaced various websites but the thing that really got people motivated and got them going was commenting on news articles and this would generate massive rumors that people would then spread around and talk about outside of these news articles this then led to people having uh russian ethnic russian speakers then looking at this and going this is cultural genocide this is our heritage being destroyed and when you look at those things in that lens rather than this is a complicated symbol which has a lot of intricacies around it and you simplify it to that one narrow thing it then all of a sudden gets a little bit difficult so then over the course of about two days towards the
end of april in 2007 uh riots erupted in tallinn they originally came from where a kremlin-backed protester started to punch police officers and of course we have seen how police tend to respond when you punch them so this strategy is what's called hybrid warfare this is uh it's not a really well defined idea i kind of think of it best as it's a district it's a strategically aimed political warfare against democracies and democratic institutions so for example the government of ireland is a democracy you can target uh various operations against them or you could look at democratic institutions so when russia used chemical weapons in uh 2017 in salisbury in the uk to assassinate the
skripals uh what they were doing there was they were taking advantage of vulnerabilities that existed in the democratic organization that is the organization of for the prohibition of chemical weapons and the way that hybrid warfare works is that it blends a number of different uh means of warfare so conventional warfare which we've seen with the uprisings that are backed by russia in the donbasque and luhansk irregular warfare as we saw when the little green men uh which are russian soldiers turned up without badges which is you know legally dubious um in 2014 in crimea as well as that we see cyber warfare even as recently as a couple of weeks ago where we've seen websites
being defaced ddos attacks and you could say the bears are doing it you could say ghostwriter is doing it maybe it's both of them doing it maybe one is doing it at the behest of the other and then finally influence operations which is the stuff we see on a regular basis when it comes to disinformation maybe in in terms of propaganda which various governments are putting out or in the old russian favorite of active measures where they actually try and influence the direction that certain things are taking in governments a great example of that is the 2016 election in the united states and this entire idea falls into what's called gray area operations you can have
normal diplomatic relations where for example we recently saw michael martin in washington dc he meets with the president biden they have their back well i don't think they actually met because he's got covert now but in theory what's supposed to happen is he hands him this little basket of shamrocks and that is like our little bit of solidarity standing with them these are long-standing traditions that governments have in interacting with each other in very normal ways sometimes it's where ida ireland attracts businesses into ireland sometimes it's in the form of visiting academics coming here to teach skills or how we teach skills to say for example doctors in other part of the world here in ireland
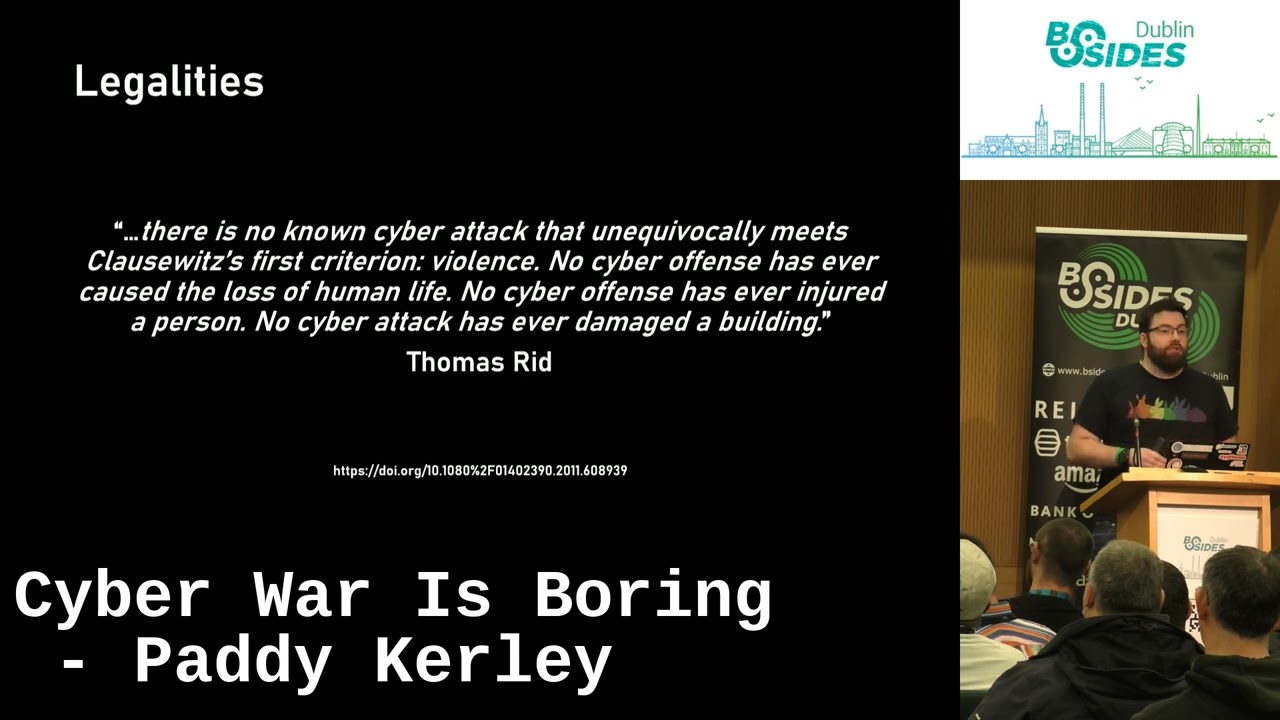
then you have armed conflict which is the actual war fighting that we see in ukraine between russia and ukraine at the moment and in between there is where we tend to see most of cyber operations happening it's where states are looking at this gray area between war and not war and they work in the area of not war to try and maximize any kind of advantages to advance their goals so uh as well as this uh there's the legal aspects of it uh there's a very important point in um when we look at cyber attacks in the international law terms where the criterion for one of the three criterion to define a cyber attack is that they
are violent in nature which is to say that again looking at clausewitz they cause damage or destruction to property or they injure or kill people and as we have seen there are arguments to be made for stuxnet so it's a little heavy out there but to date we're not aware of ransomware for example actually killing someone the germans have tried to prosecute that we're not aware of uh while there are attacks using difficulty are not defibrillators uh insulin pumps we're not aware of one of them actually being used to injure a patient on an insulin pump and we're also not aware of while the theory exists in the likes of the triton malware we have yet to see anything actually
damage or destroy equipment um if you look at this as well then in irish law the only place that the word attack exists is in the preamble to the law the reason for this is in irish law the word attack is a charged word implying violence in it and as we have also seen there has not been violent uh cases taken there as well so when you go and read through the act you see it as like interfering in the transmission of or intercepting in the transmission of rather than you did an attack um which leads me to take this really useless slide everywhere i go and hand it out to people but the three important
bits on it are there is some kind of a cyber operation someone is using cyber somewhere to accomplish some goal the person who is doing it is doing it for violent ends so they're looking to damage or destroy property or kill or injure humans and finally that whatever intrusion is taking place is being someone who is subjected to international law so when you're looking at this in regular terms all of us in the room here we're regular individuals we are not subject to international law if someone here is in the military and they're taking part in military operations they are subject to international law if there is uh well the whole government can't be in the
room but if the government is taking various different actions they are then also subject to international law so you need to meet all of these criteria and to actually be committing cyber attacks and this has then led thomas rid to go on in a papery route to describe how cyber war will not happen uh he has said it will not it has not taken place in the past it is not taking place now and it is highly unlikely that it will take place in the future and a lot of his thinking for this comes from a lot of what we see is sabotage espionage and more importantly subversion a lot of what we see on a day-to-day
basis in regular cyber uh like when what major cyber actors are doing uh at a state level against other states is espionage and subversion and then recently a paper was written by an academic called uh leonard meshmar where uh he coined the idea of the subversive trilemma this is where he set a set of criteria that defines the difference between what is theoretically possible with what is practically feasible because theoretically the us still launches its nuclear weapons using five and a half inch floppy drives in theory i can find out where they are doing them uh like minting those floppy drives lay my hands on them put some kind of corrupt data on them for my own
ends and use them to launch nuclear weapons but is that actually practically feasible as a thing you can do well to understand if it is his criteria for looking at that come down to operational speed the intensity of effects and system control and these are all interlinked so the faster you move means you have less time to do reconnaissance you have less time to develop your exploits you have less time to use the exploits and not get detected in the process and and then when you do get into a system on the other side of the exploits to learn whatever that's connected to how these various systems work if you get in the other side of a telephone
switch for example is it in erickson where erickson have their own language for programming telephones which is completely separate what other companies use or on the other side of it are you only familiar with cisco systems and then all of a sudden there are juniper systems on the other side of it you might need to learn the various different commands to use them and link to this is if you move fast you're obviously not going to have big effects with your cyber because obviously what you've done is not taken the time to develop these intense effects in the end and then how much control do you have over it the more commands you issue on a
system the more noise you make and the more noise you make the higher chance you have of being detected so if we then compare and contrast stuxnet to what we've seen recently in russia stuxnet took about five years to develop and cost the entire olympic games program cost somewhere around a billion us dollars and resulted in technically two pieces of malware and one patch um using that kind of speed they had incredible effects with the first version of stuxnet which is known as 0.5 it was used between 2007 and 2008 in natanz it ran completely autonomously without any c2 and they used that they used a system they had built in the y12 national security facility uh in oak
ridge tennessee to actually run at a small scale demo of the system and uh then there's the destructive one that well not destructive but the one that everybody is familiar with which uh is the one that became the worm so if you look at the way these kind of things worked in different fashions one of them resulted in possible equipment destruction and the other one did it nothing but slow the nuclear program down so you ended up with roughly similar lengths of time that they took to develop and use them and you had two wildly different effects one of them also ran completely unknown and wasn't detected until 2013 when it was detected by accident in virus total
and the other one as soon as it went loose in the wild everybody knew about it and it was all over the news so melding these things together stuxnet is a probably successful program that took a lot of time to have really specific intense effects using a lot of control over these systems but you can't move fast and have the other two effects so they did it really slowly russia then on the other hand well as live ua map got their hands on a number of documents related to the invasion vladimir putin uh approved it on the 18th of january they were to start on the 20th of february obviously didn't start for another i think eight
days uh maybe that's us information operations having worked very successfully to put off that attack maybe it's because they weren't able to get their false flag who knows we probably won't know for a long time and of course to end on march 6th which that's going well so uh this is the kind of trade-off where they had very limited time to develop their attack plans and to develop systems are to develop malware inside systems that they could use for big effects that people kind of expect and that's not what we've seen now maybe they did have stuff planted already but that's an idea i'm going to come back to in future finally the other thing is perceptions
when we were seeing uh the cyber partisans in belarus uh ransom wearing ticket machines or when we were seeing um the ukrainian uh websites getting defaced adam wallow said this is not the cyber war we're promised and i think a lot of this comes down to this this is the kind of picture that people have when they look at this is a real picture of a real military unit the 780th military intelligence brigade right you was like is it gonna work it is this dude here he has a usb cord being used as a sling for his rifle this guy has a trigger finger and he's holding it away from the trigger like he's ready to fire safely right and then
of course you've a nerd like me who's a custom cherry keyboard right so we end up with like this is the picture we kind of have of what cyber should be but if we then look at other forms of warfare and how they kind of compare my favorite iowa class battleships they fire a volkswagen golf 30 nautical miles with a grand piano worth of explosives they don't really exist in war anymore but you know if you think modern naval combat this is one of the ideas that people have another idea that people have is early bird class destroyers they fire missiles out of vertical tubes and they go away and fly and blow things up
but this isn't where naval warfare got its start naval war warfare started about 4 000 years ago in ancient egypt where they literally built land on top of boats so they think they could have land battles on a boat at sea this is how naval war got started so there is a train that like of thought that has gone through millennia that is developed where we are today with naval warfare we see the same thing with aircraft where for example we have stealth aircraft that have like in this case a particularly fantastic weird metal camouflage system for some reason but that's not how aerial combat got started aerial combat didn't even start as combat it started as men throwing
hand grenades out of planes and using the mark one eyeball to try and determine where this will land and this is another idea that cloudswitch had is that every age has its own limiting conditions on warfare and peculiar preconceptions that impact how people think about war and a great example of this comes in world war one where we had curious years these are a type of horse infantry that can fight on horseback with sabres and dismount and fight with wet with guns right and they have horse hair helmets and breast plates like someone is going to come at them with a lance on a medieval battlefield 500 years prior to this actually existing but this unit doesn't go away because
the ultimate idea of it is units that can fight mounted on something and then dismounted and we can see the exact same unit exists today there that's them doing counter terrorism operations in mali there are guys on the ground dismounted ready to fight as well as these dudes here who are in like their recon tank thing right and we see them again where they actually have full-on tanks as well as dismounted infantry that are fighting dismounted so while the entire idea of how cavalry is used in warfare has gone away the way that they fight remains exactly the same they have limiting conditions on what they can do as a fighting force and if you then look at cyber
i prefer to think of it not so much as cyber but as information warfare for a number of reasons and one of them is it's something that's been thought about for a very long time sun tzu has been thinking about this for about 2 500 years 2 600 years now where he essentially wrote the book on information warfare he talked a lot in his book about how you can use deception to hide your strength deception operations are something modern militaries take part in all of the time if you look at how some of cyber is being used the hermetic wiper that we seen in ukraine last week it tried to deceive operators as to what it
was actually doing by running ransomware at the same time as it was physically wiping systems and then as well as that that you protect your own forces using operational security and day-to-day a lot of the cyber things that we do are operational security elements where we're attempting to secure access controls on how you gain entry to various systems or who can gain entry to systems or do you meet the criteria to gain entry to this system we also use the work of this man here this is an islamic scholar al-kundi from 1100 years ago he invented most of modern cryptography not only did he come up with most of modern cryptography he came up with
a lot of things he's a polymath he kind of invented modern chemistry modern islamic scholarship uh islamic philosophy optics but the thing he's most famous for in our realm or at least should be is if you've ever done cryptanalysis if you've ever done frequency analysis of various different pieces of uh encrypted information you can thank him for that and we while we still use a lot of his techniques today pen and paper using his methods were used until mechanical encryption came around in the 1920s so he had about a thousand year run of protecting information very securely using systems and if we then go to world war one we have this group here this is room 40
these are the people who birthed the idea of signals intelligence uh germany what they were doing in world war one was they had a bunch of code books but they weren't to hold encrypted information they were books that were like hundreds of thousands of pages long and they had entries in them for any message that you could possibly think of that you might want to send in peace or war and what you would do is uh tap out that message on page 4522 and that when that gets relayed back they then know okay i am headed north out of keel and that's all it means but they got their hands on the code books they
started to figure out how to decipher them and how to use them and then they were able to use them to kind of force battles on the germans these things called decisive battles not going to get into it but not only that they also came up with another idea which has become very important in not just in cyber but generally in information warfare called radio direction finding if you've seen the lady earlier who was talking about open source uh using sdrs for radio frequency analysis it's the same kind of idea can you pinpoint where in the world the transmitter is based on how it works if you've ever had to try and find your wi-fi box uh in an apartment that you've
just moved into you want to find the code to use it you can use your phone and you can watch the strength increase as you walk along it's the same kind of idea but they you they turned the entirety of britain into a radio antenna and they were very able to very precisely figure out where various ships are so when german mine laying operations were taking place they knew exactly where those ships were to a huge degree of accuracy and they were able to then figure out exactly where the minefields were and when uh the battle of jutland happened in 1916 they were able to chase the germans into their own minefields because the british knew
where they were and this then comes on to world war two where we have dudes like this this is an operator of a system called hofduff high high frequency direction finding this is how they hunted u-boats the idea here is you move in a line and as you move along you were watching the radio frequency on the little scope thing he has there update as the u-boat is putting out its morse code and that allows you to then figure out the location of that u-boat in space go and charge it sync it and ultimately this then brings us on to claude shannon who came up with this mathematic mathematical theory of communication this then becomes not just
the fundamental underlying uh theory of how most cyber works it also becomes the fundamental underlying of how a lot of information warfare works because ultimately he's talking about how electrons fly around in space electronic warfare is all about manipulating those electrons in space and if you jump forward into the future then uh this is part of waypoint 2028 this is how the us army intends to fight wars against what they call near piers it's a very fancy word to say china and in it they have two major elements one is the theater fires command the theater fires command is basically instead of having you pick up your radio and call down to the artillery battery attached
to your unit you call theater fires command instead and theater fires command will use the assets they have at their disposal land sea air space and information to then util be utilized against your adversary for maximum effect now that could mean using one on its own it could mean using all five for maximum effect it could be any number in between they will use the assets that they have available at that time to deliver the most fire that you need and the other one is this fun unit little here this is the theater information advantage element and this is the cyber people information advantage is some an information advantage is something that allows you to
think and decide quicker and more effectively than your adversary so when you're fighting in a war if i have better information than anyone else i know more about you and what you're doing your unit dispositions and how to best fight against you with what i have so the us is attempting to do this and they're attempting to do what what they call enhanced non-lethal capabilities to conduct information warfare uh to protect friendly information and inform and influence activities through forward posture persistently engaged blah blah blah all of this comes from the 2018 us eod cyber strategy this is a policy document that they're giving to lawmakers to understand how the department of defense is going to be fighting wars so what
they're saying to policy people is cyber what they're saying to the troops is information warfare so these are the peculiar preconceptions that then we have when it comes to cyber it's a problem that's existed for about two and a half thousand years people have been thinking about it for about two and a half thousand years and it's not something that's just stuck to what i can do on computer magic keyboard cyber bullet pew pew as well as that claude shannon being the fundamental underlying theory of how it's used imposes a number of limitations on these systems you can only open up a certain number of attacks because there's only a certain number of vectors here unless of course
you want to attack yourself but that's not great so this opens up a tax where you can degrade these are what are considered attacks against information itself my favorite example of this it's not exactly coming up great unfortunately on the slide is not petcha not petcha is ransomware that was ransomware that was delivered by sand worm in 2016 using the eternal blue exploit and to move faster through the network they also had mini caps attached to it so that any credentials that were sitting in memory they would use to continue moving along the network and propagate the worm where it would encrypt as ransomware all of the systems when they had all the systems encrypted
they would delete the master boot record and then delete the partition table of where all of the files are so even if they didn't delete the encryption key which they did do you still wouldn't be able to recover any of your files the entire idea behind this was destructive and the reason they did this was it was distributed through ukrainian tax software called me doc they backdoored the update servers for it and they use that to distribute it then to anyone who was doing accounting in ukraine you had to have this software so this resulted then in anyone who had this just losing their data indiscriminately and this is just because russia doesn't like ukraine
so then if we pivot to today i love this this is what hackers have been doing attempting to jam russian communications by drawing my little pony and bumblebees and whatever that lion thing is so when you um i don't have audio for this one uh but what you hear when they're doing this is they're just putting out at specific frequencies beeps and these beeps come across it sounds like if you've ever picked up the phone when we had dial-up it sounds exactly like that it's exactly the same thing and they're doing this to try and mess with russian tactical communications as well as this we've seen ukraine inserting latency into gps communications which means that the
google maps locations that russia is using to target russian our ukrainian facilities such as this air defense facility because they are inserting the latency and we're talking about things that rely on atomic clocks tiny bits of latency mean you end up off by meters in your actual artillery fire so when they're trying to blow up these systems they're unable to uh you can also deny access to information the easiest and most common way to do this is to attack the receiver itself uh in intelligence terms you have collection assets where these could be for example a cam or webcam that you have on a building in keefe and you're using that to actually watch what's
going on so you would attack the camera now you could do that by cyber means but you know sledgehammers are pretty useful uh a great example of this comes in 2019 at the end of 2019 uh there was i don't know if anyone remembers that the other time recently we nearly had world war iii where uh you uh iran and the united states were kind of at loggerheads over a number of different issues one of the things that happened was the us flew a global hawk drone very close to ukrainian airspace this is essentially an intelligence gathering drone and when it crossed what you iran believed to be the line that demarcated iranian airspace from international airspace he
immediately shot it out of the sky with one of these batteries a severance and in response to this as a show of force what the united states did was they attempted to take out the fire control computers that actually allowed you to launch the missiles using cyber means now we don't know the specifics of what it is all we have is for example this new york times report that says it worked trust me it's fine and a few other reports that go along similar lines so you can use cyber to take out these receivers but as we've seen in the current conflict um bombs are kind of a hell of a lot more useful when you actually want to take
them out the other interesting thing you can do is instead of attacking the receiver you could look at who is using the information and attack them so for example uh instead of taking the receiver what if you leave the receiver up but you decide we want to figure out where the analysts are and then attack that facility this is something the us did in the first gulf war where uh this was sudan's regime command center where all aspects of the iraqi military were coordinated from and uh in the left is the pre-strike where they had decided where all of the important facilities were and then the right is post strike where they had it targeted and attempted to draw
destroy as much of them as possible with varying degrees of success um ukraine and the i on the other hand has been doing something slightly differently which is
recently in the news against the russian command post where they are attempting to degrade uh ukraine's ability to actually fight by taking out their generals and as of 36 hours ago this is the list of dead generals of and high ranking officers of various different ranks i would note there are two more to be added to this list since then and this is removing the ability for high-level russian forces to actually go forward and fight so when you're sometimes looking at stall not the stalled convoy that's probably logistics but if you all of a sudden look at why uh they have resorted to brute force shelling in certain parts of the country or they have resorted to
uh stall defensives it's probably because they have no one to make the final call because who wants to i don't know decide we should attack or should not attack when people mysteriously just fall out of windows in the country so you can also then corrupt information sources now this isn't where you attack information itself this is where you uh inject noise into information systems so that you can do various things so uh israel has these jets here these are a signals intelligence and an electronic intelligence aircraft um and the one in the foreground was part of a raid into syria in 2008 where they were attempting to blow up a suspected syrian nuclear weapons uh
our nuclear reactor that was being constructed and when they were going along this is what the radar picture looked like to the to the operator but using electronic warfare you can do what's called painting a false sky picture where you give a false sense to the operators of what it looks like by essentially injecting bits into the radar so they go along and all of a sudden this is the radar picture nothing has changed apart from the formation of israeli units has vanished and that's all because the bits they're sending along are saying there's nothing here ignore me don't look at that and we see this today in a lot of different ways recently um open facto
who is a french fact-checking website uh distribu uh uh discovered that there's a group of websites called inforos and inforos is approximately 1300 different websites that are run by russian military intelligence and what they are doing is uh basically acting as secondary propaganda arms to the state so not just have they uh rt sputnik those kind of news media sites um that are kind of showing particular views of the world that the regime is happy with they also run secondary propaganda operations that are doing local level to like um the uh rayons they're they're uh oblasts these are regions so like county dublin county galway county loud those kind of things as well as municipalities so
targeting uh not just all of dublin but greater dublin and then you could target cities so like limerick and cork and you would have specific propaganda targeted at those areas as well you could also do cool stuff like this which is after the russians brutally destroyed one of the greatest pieces of humanitarian equipment the world possesses the an225 mirror people then decided well we can spoof a dsb data we're going to bring it back to life we're going to fly it and lapse around uh kiev and we're going to have the call sign b putin and then uh something that i have to keep in mind for cyber people is uh when we're talking about corrupted
information sources we can use algorithms to create tailored messages for people my favorite example of this is twitter you can have a look at twitter and a few years ago you used to get as things came in by the second everything that was happening in your feed but now you don't get that you get the curated picture of what twitter wants to show you based on whatever filter bubble they have pigeonholed you into um this could also be used from like while twitter can do like okay jobs but this can be used for malicious purposes and my favorite example of that in recent memory is when the chinese property giant everground was collapsing it was huge news here in the west but it
was essentially not talked about beyond the great firewall and anytime people tried to send this information beyond the great firewall mysteriously vanish so you can use this to create curated pictures of what the world looks with algorithms and then finally we end up with attacks that exploit information and this isn't exploit in the traditional cyber sense this is exploit in intelligence terms where you are looking at how things are for example how data is moving around in your network and what you can learn by those data flows in your network so for example exfiltration can you look at how various things are happening in your network and see that that's an unusually large number of dns
text requests being made out to that weird server why is what's going on there so you can then figure out maybe someone's excellent trading data and you can decide to take actions based on that so we can then go to this this is my favorite game recently that i've been playing with everyone who's gotten this talk we're going to play find the army how many people can find the thousand people in this photograph
anyone no so ah there is whenever my pointer decides to work there is a command post here and some units behind it we can follow it up the road then and there's some more stuff and there's a dude out in the open and i know there's some stuff over here but i've yet to find them and we can look over here and there's more dudes here and the us is this really cool type of camouflage which is blends in with the natural background that makes people turn into rocks so you can actually do that and you know if you look at that you can blend in and hide a lot of stuff in that gap
but you'll notice there's also an antenna there and every soldier has tactical radios so what if you just start gathering the data instead of looking for the soldiers you can find them using electronic warfare
[Music] this is the disposition of those thousand people going the whole way back to the mountain and it also includes this bit here this is what's called train this is the logistics supply for those troops if they end up fighting and if we then look at the number one question that i've been asked why are the phone networks still up why do people have internet connectivity and you know in a way that's a really good question but a lot of it comes down to both russia and ukraine have been using the phone networks for their own c2 not all of them have tactical radios and the tactical radios they do have sometimes they're in the clear so the
only way to get communications out is to use phone calls and something ukraine has been doing is this
foreign
foreign
so what they're actually doing in individual terms is they're trying to direct how they're using their fire using artillery as well as that we also end up with this this is um tactical radio communications that a friend of mine actually captured of russian units and i have the translation there as well
so you can actually just sit and go along and do legitimate signals intelligence and gather the tactical communications that they're using and this isn't a rocket science thing because i have another one
so this generate the reason that the network stay up is because russia is desperately relying on them and ukraine is getting an incredible amount of intelligence out of using these systems the other thing as well is that the final point i want to make is when we're talking about these in military terms these are known as computer network operations and the ones everybody's kind of thinking about are computer network attacks i've also mentioned computer network exploitation using these systems to gather intelligence about what's going on but no one's talking about defense and i think the one thing that has been missing from any discussion that we have had about where are the cyber attacks is
the incredible role that defense has actually played there's a concept in military terms called battlefield shaping battlefield shaping is everything you do before the war starts to make sure the terrain is exactly as you want it and this is the list of successes that have happened on the defense side beginning in november 2011 or sorry uh 2001 or jesus i am bad at words now uh november 2021 where the us cyber command along with civilian contractors went into ukraine specifically going around critical pieces of infrastructure and bit by bit taking them apart and removing malware left right and center wherever they found us this was in the financial times just last week i have not seen people mentioning that this is
the case all that often then in january of 2022 people thought that viasat had their ka sat taken down and a number of communications receivers for it destroyed the nsa in january put out a warning saying if you have one of these vsat terminals updated and all of a sudden ukraine they continue to be able to use these systems because they had they paid attention to the intelligence that was coming in drag us in every i think it's three a month or so publish these little knowledge packets for their customers and they give you brief synopsis on their blog of what's available and they've discovered in destroyer or as they call it crash override which was used previously to take down
the power grid in keefe in 2016 and black energy which was used to take down the same power grid in 2014 um they talked about that in both january and in february microsoft mystic detected whisper gate in the week leading up to it eset detected hermetic wiper after everything had begun um microsoft detected something called foxblade we don't know anything about it but within the hour of the attacks beginning microsoft had detected this uh attack and then not just that within three hours they had patched the vulnerabilities that had gone into it and then finally fortinet have been providing free ddos uh protection to the ukrainian police who were the ones getting the brunt of ddos attacks at the
beginning of the campaign so where are the cyber attacks uh primarily problem is cyber is deeply misunderstood and people kind of think it's magic but it isn't the other thing is these things take time investment to prepare and pre-position russia had this and then it was taken away from them cyber has limitations that's a shock to people and uh as well as that people have been thinking about this for a very long time so this is just one of a range of options available to militaries and sometimes things that go bang or boom are just more effective than cyber and finally the defensive efforts just aren't sexy so they're under-reported so i'll take questions now but uh i
couldn't do this talk on my own so i'd like to thank tinfoil jack and aminal for wargaming ideas with me helping me find some of the documents and for generally good crack along with it um microbiota designed a ton of the graphics you've seen that i've used david helped me get the signals uh intercepts that you've seen victor helped me translate them and sign and help me with various pieces of linguistic support along the way so thank you for listening





