Offensive Azure Security by Sergey Chubarov
Show transcript [en]
so let's get started um let me just tell a few few words about me a few more um one more thing i'm from russia if you're interested in that so um that's my burden to uh talk about hacking um yeah yeah absolutely right about certification so i don't want to read them again if you want to find me here's the linkedin so go ahead and find me there um so what this session is all about uh what the session is all about um i'm gonna i'm going to cover um the typical misconfigurations that you may find in azure because uh azure is pretty secure by itself but when you when you use that when company use that
they have like very typical scenarios that may be compromised i want to show you them so so because i do assessments and penetration tests for different companies and quite often i find they're repeatable scenarios uh tributable evidence patterns so i combine them all together in the single scenario and so that's what i want to show you here uh what is what is interesting about my session from my standpoint in general i don't really like to use slides i prefer live demos so this session mostly will be based on live demos uh of course i will show you some slides to just just just just give an idea where we are now uh but most of the time
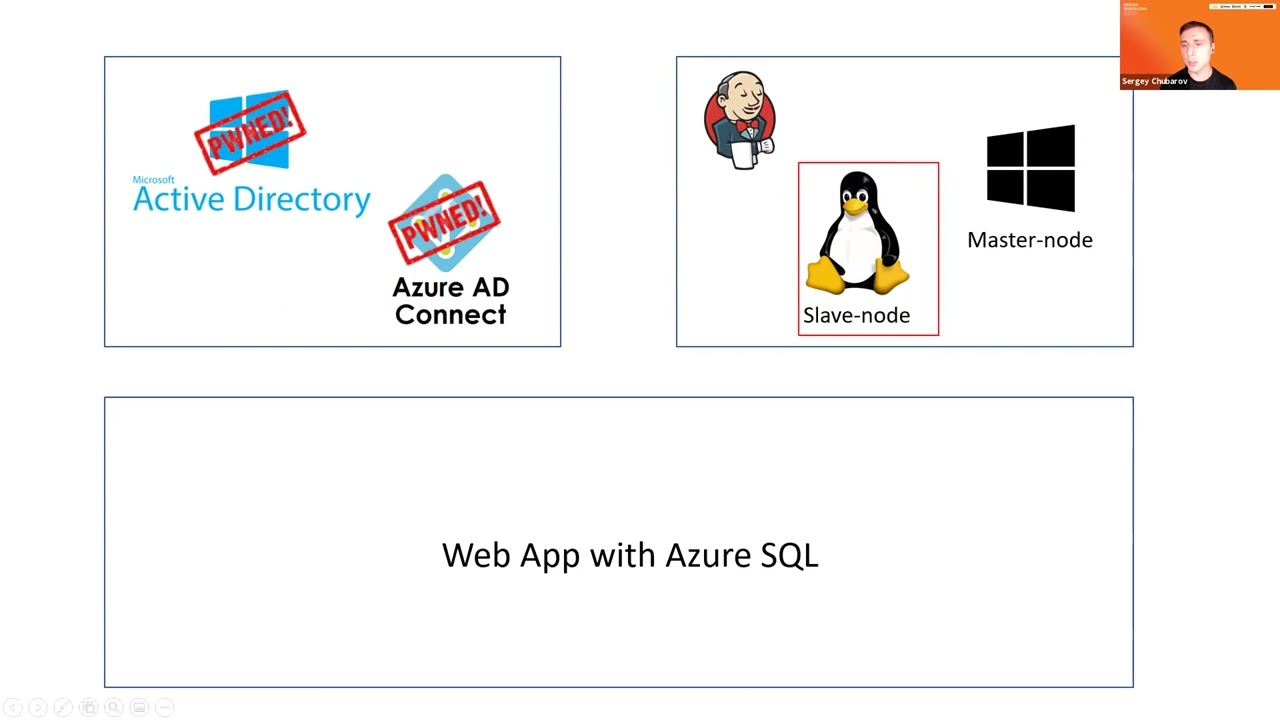
you may expect live demos um and in the end of session of course i will answer your questions and i will give you some ideas how can you mitigate that but once again that's going to be most of the most of the other the most of the session most of the time i will show you some offensive things um all right all right so let's get started uh that's my agenda so i will have like three environments uh three different type of different type of public type of environments and i will compromise them one by one and so i will move from one environment to another and so we're gonna start from hybrid active directory
and so in my hybrid ad i have the main controller and i have what's called azure ad connect and this service uh is we can synchronize accounts groups users and so on from on primacy directory to the cloud so company can reuse those accounts in the cloud so let me just jump to demo um and show you how it looks like so here's the azurity connect on the separate server um and um you may ask all right so 80 connect is very typical very typical configuration what's the problem with ad connect uh one of the problems with ad connect is configuration which is like um recommended some some some part of this configuration is recommended
so when you configure ad connect uh you must create what's called a deforest account uh this account uh will be created automatically that's the most recommended ways to create it automatically and one of the things when this about this account uh when you configure your ad connect uh you must specify different features and if you specify a feature which is highly recommended called password hash scene so it means that the hashes of passwords will be synchronized from on-prem id the cloud as well uh if you if you enable this feature and this feature is super useful because uh in this case in your azure your your users will have the same password and if you lose connectivity on
pram they will still be able to connect so password hashing is is very commanded by microsoft because it's resilient and but if you enable password hash sync account for synchronization will have this permissions replicate directory changes and replica directory changes all let me jump back to demo and show you on the main controller this account so just in case if if you haven't worked with ad connect before azure id connect before so that's the service that's installed on the separate server during the configuration you must create an account that will read active directory to grab accounts from there and sell the account that will be created for this synchronization it's called like this msrl and
random numbers and letters let me check permissions of this account if i look at the properties of the main controller and go to security tab i can find this msil and look at this so it has replicate and directly changes so what does it mean if i have urban directly changes i think you're familiar with a tag called dc sync when some attacker may synchronize uh some content from active directory so in fact replicating directory changes allowed me to do dc sync with mimikatz so this account become pretty powerful um uh but the question that you may have all right so this account is powerful but what is the password how can we find the password who can find a password
um generally speaking this account for this for this account we don't know password normally because this account generate automatically and password is managed by ad connect by itself so you don't have access to password directly but there is a way how can we do it there is a way how can we get access uh let me jump back to ad connect um and let's think about this let's think about this so if we have 80 connects if if we have an ad connect server an ad connect server somehow uses this account so somewhere this password must be stored this password is stored in sql database if i look at the sql database for that that has
the database of id connect and i look at the management agent here i can find oh let me just remove and columns i don't need remove this from this as well uh let's remove this those all right so let me run again and now let me find this account here and look at this so account i think it means that okay here we go so account is here and it says password we have password but password is encrypted stream so we cannot have direct access to passwords we can find the plain text password uh because if i look here it will be something encrypted uh but uh it's possible to decrypt and who can decrypt that anyone who has
permissions of local administrator on ad connect server and and here the typical misconfiguration is started because companies think like all right if ad connect is not a domain controller so we may allow uh like a server administrators manage ad connect because it's not domain controller and also it has different usually ad connect has different baselines not the same as domain controller as um yeah of course that has some different features but anyway um so the typical misconfiguration when company companies allow uh like server administrators manage ad connect let me show you what we can do with that um so you can decrypt this password you can do it manually but it's pain in the neck so it will take a lot
of time it will be longer than i have for my session but you may find also on the web uh the tool called ad connect dump so just just google about this you will find the tool and you will find the article of author and author describes how to do it manually but for the sake of time i will share that uh how can how can i do with one click so i'm gonna just i just run uh the script on my server on 80 connect server with admin permissions uh so i'm not the main admin here uh i might just restart just a regular local local administrator and i can have this username and password so let me
copy this value this this value and jump to client workstation so i'm going to open um cmd and i'm going to open cmd again as a different user so place here and let's sign this name and click ok so now what i want to do i want to i want to run that very typical well-known command called dc sync um using very well known tool minicats and you know but this is the in case i can synchronize the main administrator i can synchronize uh kirbtgt and create golden tickets if or if i synchronize my administrator i can run the hash so it it will give me a lot of permission so first before i start to do anything let me
check my permissions and who am i so in one command line uh i i'm a contoso j dom and what permissions do i have can i enumerate c drive for the of my controller no i can let's try another one here i am msl can i enumerate my controller no all right so let's open minicaps first as an smsl account let's run in cats and here i want to say um lsa dump dc sync end user is going to be trainer who is mydom administrator look at this so now i have a hash of the my administrator what next then i go to to to mimic it's again open as the regular domain user with location permission of course um
and run past the hash and so here i must copy and paste this hash all right so i have another command prompt let me just oh sorry wrong one and yeah i have access domain controller so that's a typical problem uh when companies allow ad connect to be managed by server administrators and those administrators they may become the main admins and we we find it very often it's many companies this configuration so let me jump back to to here so now we compromised uh on parameter directory and with ad connect uh and and we became the main admins now from here uh let's move to the next uh next infrastructure which is virtual machine so we have
virtual machines in azure and and they will be they they have in my case a jenkins application installed to be fair it doesn't really matter what is installed there i use jenkins just an example because jenkins may have multiple nodes with different operating system in my case windows and linux i just want to show you how linux and windows may be compromised in the same manner so let's move on and i'm going to jump back to demo and just want to continue this previous uh demo and and and in transit to the next scenario so now i'm in the main admin and i need somehow to get into azure and to if i want to pen test virtual
machines so if i'm at my admin i have multiple ways to do it so first of all i can create a new account in active directory and add account to some sort of groups and if if those group they have permissions in azure all of this will be synchronized that's a bit noisy first of all and second problem um second problem um i don't know i don't know what groups should i use because what groups have permissions i need i can try a different thing since i'm a domain admin i can also try to connect to any workstation and if i connect the workstation of administrators or developers i can find something interesting there let me share that real
quick so first of all i'm going to open a workstation that let's say belongs to me and i want to remove just one thing there [Music] all right that's fine uh let me open cmd uh on developer machine now let's type a z account list and output table it doesn't really matter i can anything i look at this so it shows me my subscriptions now if i do the same on the different workstation uh az account list and of output table so fingers crossed it should give me an error come on did oh so it doesn't work so that's that's easy that's the tool that very commonly used by administrators and developers to administer azure environment
and so when i showed you before the previous workstation i typed the command and it didn't ask me for a password here it's it says hey you must authenticate first so it looks like those authentication token uh cached somewhere and let's find where this token is if i go to user profile user profile and here's the folder folder and profile called dot azure and the token will be cached here and if i'm the main admin i can connect to any workstation and and nothing stops me from getting this ticket let me take a ticket but token so let me zip it and copy that to my machine
all right and let's extract here all right let's try again cross your fingers for me and come on yeah now i have access to azure uh as some sort of administrator i don't know which one i mean i don't know what permissions i have but i know that i'm there i can do something there and i wasn't asked for password and what is the most important um it didn't prompt me it didn't show me any mfa prompt so i i just i can manage azure now uh from from my workstation um and i i don't have to be authenticate i don't even need to create the fancy ways to bypass mfa just just just here in the safe credentials
so so now if i have an access let's try to pen test virtual machines of course in the usual pen test we have a very long reconnaissance phase i don't know waste your time here because reconnaissance is it takes time uh let me just quickly just check what virtual machines i have here um so do you have any machines yeah i do and since my target once again is uh jenkins and both vms of jenkins i want to take those two vms those two vms uh and play with them a bit jinping's master and jenkins slave just just want to quickly remind you that jenkins mazda is windows server and jenkinslave is a linux server
all right so what can i do with virtual machines so for this demo first i want to i want to jump to the portal and show you in a more visual manner and then i will get back to the command prompt and will complete my attack so if i go to azure portal to azure portal um and i open any virtual machine let me open jenkins master um for in any for any virtual machine you may find uh this command called run commands run commands and run under run commands for windows uh it will be around powershell script so you may run partial script execute powershell it says here you may exit powershell if this is linux
of course this it will be shell script uh so that's that's the that's the same for both operand system types just a different uh different type of scripts of course uh powershell or shell um but now what is the most important about the search machines about this feature um what permissions you must have to run this feature oh by the way why do we need this feature in general you know that cloud is obstruction and they want us to administer cloud or fix some problems uh without logging locally to virtual machines so i i can try to do it i can try to run some scripts and fix something or configure something virtual machine without a local login and now
my goal will be use this feature to bypass authentication and get into virtual machine from my current position let me show you what permissions i must have if i want to i mean if i want to use this feature so if i go to roles on azure and i can click very typical role called reader so and for many companies they think oh that's just a reader this this this role cannot do anything bad or some some so just it can read it and nothing more so this in this role quite often you may find on subscription level and will be inherited by other resources so let me click reader look at the permissions and
find compute here um sorry and look at this run command this th this feature is available for readers all right now we we know what it is so i can run powerful scripts and shell scripts as well now let's jump back and do it um so first before i start running scripts what do they when where do you want to run what do i want to run probably if i want to get access to those virtual machines it will be shell i mean reverse shell of course metasploit but if you have antivirus maybe a bad idea or something custom which is which is better which is better at the end so let me first establish netcat listener
on this port another port for windows so let's try first let's try linux uh that's how can i do it from this command prompt let's click here by the way this feature is not super fast so let me just wait a bit it should be here fingers crossed again once again it takes time before that will be executed hopefully it will be and i didn't block it oh look at this so i have the shell on linux now let's try the same trick with windows for windows you know we don't have any native shells of course you may try something like power shell nishan shell or whatever i i just did a different thing i just create my own
shell on python and so i will download that and just run it and it shouldn't be detected by antiviruses because it's my custom thing all right let's run that let's run that um and let's wait for for windows shell as well let me just first explore linux uh let's see if i type id here i can see i'm root why i'm rude um am i running at this vm as a route uh it doesn't really matter oh look at this we have a shell for for windows as well it doesn't really matter because this this feature to run run commands work on behalf of a local system or on behalf of root so for on on window on linux i'm root on
windows i'm local system and i can do whatever i want now on those virtual machines isn't cool so for for companies it may look like oh we just enable reader feature who cares but that's what i can do if i have reader permissions on virtual machine level so let me just just just do one more thing uh let me open jenkins error log i know it's not really important about the jenkins himself but let me just uh let me just check uh what i can i can find here and i can find here the password of jenkins uh it is the initial password there uh it will be an airlock um so let me try to do oh what is that
russ i forgot um let me try to log into jenkins and this is my password [Music] and yeah that works fine so uh that is uh that is virtual machine to be fair i don't really care for jenkins or something else i just want i just want to show you how virtual machines may be compromised all right so let's jump to the last scenario um and now we have something more advanced we have a pass application a platform as a service so here i have my application deployed on app service it stored data in azure azure sql database and it doesn't store credentials directly on the web application so we store credentials in key vault
um and and also credentials there will be rotated by this function and and also i have a application application firewall or vaf to protect application from outside so what how can we what can i do here uh how can i try to compromise this application probably my goal will be a sql database could because the data should be there but how can they do it where can i what should i where should they start um so of course i can start from uh web application but if i want to move on i must have my goals database and so if i look at the web application i will not find credentials there uh even if i get into the application so
it should be some different path to to try to get into sql database and that is going to be this function uh of course this is less typical misconfiguration but let me but but but that's what we also sometimes find uh in our customers so when we have key vault and credentials there it's recommended by microsoft to rotate those credentials so it means it will it will use some function function which is serverless application if i know if you're more familiar with amazon it's like a lambda in amazon or function in azure um and so uh the special special function will run periodically based on some triggers and you may define triggers yourself and rotate the credential storton
keyboard and sql database and sql database password as well so it will rotate those credentials application will will get transparently because because it has access onto key volt and so uh at the same time it will change the password and sql database and rotate this past the secret in keyword so what is the typical problem with this configuration so it seems very very secure but typical problem here because key vault companies know that key vault store it contains corporate secrets and they're very careful with kievault but when they have this function um what also may be found that they did not break inheritance and they still have this inherent permissions or either access to this function and
let's see what i can do if i have access to font so i may not have access to key volt but i may have access to function also by the way keyboard has a separate separate configuration to get connected to keys but i may or six per seconds but i may have access to function and on behalf of function i can get access from this keyboard uh let's try that let's try that i'm going to switch back to my demo as usual and first i'm going to show you on the portal with the key vault itself [Music] so let me open the keyboard here and if i go to secrets look at this so it says um your policy
not so the policy that configured at this moment does not allow you to see those values let me just quickly give myself permissions oh i don't have my permissions here at all let me just say just list just just allow the list permissions uh secrets [Music] save all right let's go back so i can i can i have two secrets here a username that's used by database uh and a password which is used by database as well now let me get permissions back so let me remove them i mean remove those permissions and now let's test this this function before i test that let me also show you how this function look like so i'm going to open function
application and this function is by the way is deployed just right from the microsoft github from from from microsoft page and it's recommended let me go to functions and here here we have two functions first one is triggered by custom events second one will be triggered by http trigger all right so two functions here um now let me tell you about a problem with problems with configuration if i have permissions to read that what i can do by default there are two misconfigurations will be here misconfiguration number one companies they usually don't use ftp to publish their functions but by default ftp is turned on so that's the default ftp state to access function and say they don't turn off ftp
access that's the first one first misconfigure second one i can read data and see what i can do here i can get pro get published profile and in this profile i will find ftp credentials so let's jump back to to my demo environment and let's do it oh let's close this and let's do it let's do it oh well let's do it from here because i will use filezilla for this purposes and so i don't need to jump from one window to another um so um let's first get a ftp address of this func function uplift of this function so let me function application let me copy this address place here and now i get i i want to have
credentials command will look like this and now i have this username and password as well let's click connect now i have a bunch of folders here i i want to have this function which is uh triggered by by um hdb and what what i did uh i renamed the standard what like a previous function which is which was a partial script and i called to run one because the function that will run just must have this name and i place my own um my own partial code and this code will exfiltrate data from keyboard so let me get data from keyboard let me just run and this is it may be triggered by um http triggers so i can do it right
from here let me let me just turn on this trigger and let's just wait for a moment before it's going to give me uh credentials should give me at least hopefully it will all right so in parallel let me open new tab uh because it will be super easy just close that and open filezilla again because we'll use that later on all right so now i have information from key vault so the username called webapp and the password is password and that's the credentials that application used to connect to database so i can try to connect database myself let's do it real quick so first of all i'm going to open sql mention studio and
i can say here so here this address that does not trust them to my sequel not my sim and my sql course um so i connected normally and now let's try to do the same from the different machine i'll damn it so i need to have this address [Music] and look at this i cannot log connect from this machine because it says hey you the firewall in azure will not allow you to connect to database so you must whitelist this ip address and here so you must sign in with permissions the credentials that has permission they have permissions to manage firewall let me jump back to a portal and show you this firewall so if i go to
sql database and open firewall so what you can find here so it doesn't have any rules except one rule this rule says allow azure services and the resources to access this server and that's another problem that i usually find in company environment because i i was able to log in from this machine because this machine in azure but this azure is it it's that's a different subscription that's a different region many companies think that if they if they say yes here they allow access of their or their resources that they have to this sql database like the virtual machine will be will have access uh no not at all any azure address from any customer from any
region in the world if it belongs to azure will will have access to your database of course you must have username and password but firewall will not blocked so the better solution will be turn it off and deny public accidental so in this case um i can connect to a sql database only from my web application let me run my application by the way my application on the on a free tier so oh that's worked that works fine uh even though three tier oh no that's not the free gear anymore so i just i i migrate from free tier right before the the demo and so that's a simple application and i can just say something like hey um besides
uh user and let me just add password as well oh sorry email um be at sites.com um and yeah yeah that that's working normally that's working fine this database it looks like a application has access to database normal access if i try to let me just reconnect to this database from azure machine but i don't have access anymore so it says uh access only allow only private access allowed so what i can do here i can try to access database from the actual application for this purposes i'm going to jump back to my demo so i think i have 10 minutes i should speed up speed up a bit so let me just um get the ftp so i will do the same i'm
still going to say i will get address um of ftp ftp address of this application let me just take this address because those applications they they use the same approach as uh kevo oh sorry here um it's here [Music] and let me oh the wrong one and let's take credentials as well and connect with ftp again
all right so i can see here php page and just one one pager and you you can guess if if i have f php application i can upload my share i have ftp access i can upload my shell and execute on the server side oh damn it sorry and now i have access to this server all right the last problem i have last problem i have is um how can i connect with sql database i need to have some tools to connect but looks like uh i'm not an admin here oh by the way before i start to do anything let me establish the new new shell because this one is not super interactive you know that's a web shell
um so let me just establish the new shell
so let's see id so i just regular uh www user uh not privileged user so for this purposes i need to have something some tools that may work without installation and this tool is called useql usql this tool allow me to connect a database without installation so let me connect the database and it looks like i did let's try to get tables um a list of tables so i can see two tables here and let's try to get content of table called registration and now i have this besides user there all right so that's that's what i can do that's what i can do to um find uh the path to this application of course
all of this that i show you here um i found partially for many companies it's not one company that has all of those vulnerabilities and mismix configurations more correct but some of those misconfigurations may be found many companies and i just combine all those things together all right so last last thing here last thing is we have application gateway application firewall um and what it is so i don't need i don't want to explain you what vaf is because that's a security conference probably all of you know what buff what puff is i just want to show you the built-in buff that we have in azure um and um so we have firewall on the gateway level and
it's nothing more than very well known open source firewall um open source firewall forgot the name of the firewall open source uh dammit sorry um let me just go there and find that dress now let's try to and now let's try to run some some injections and accident access the knight um so i i i cannot run injection on this level so uh um and that is this buff which is all available in azure but of course if you wish you may try some other firewalls so um to be fair um that's that was my plan but it looks like we have six six more minutes so let me uh discuss with you uh how can we
mitigate all of those things so you you saw here you saw here that we compromised three different environments and the typical question how can we all right so we we now we know uh we we have problems what to do with them so let's start to to try to fix them i will not show you the like all of those how to fix but give you some ideas what in the first scenario in the first scenario when we have um when we compromised um directory very bad idea will be disabled password hashing no that's that's not that that not what should we do um is i know some companies that prefer to disable that but
i don't recommend because you will have more problems and benefits but you should keep in mind ad connect has may lead anyone to domain admin permissions so if you allow access to ad connect then this user may become the main admin easily so be careful about who can manage i highly recommend you to allow management of ad connect only by the my administrators next one this environment be careful about permissions keep in mind reader or either reader just the reader can do it so do not allow did not give permissions of even of reader to the user who shouldn't have those permissions keep in mind even reader may be pretty powerful and finally let's take a look here uh
what here here i can i can give you a bunch of recommendations so first of all uh credentials of key vault if we use key rotation the permissions here and permissions here must be equal so but uh unfortunately fine typical case when we have um smaller permissions here on on key vault at the same time some other users some administrators middle level administrators they have access to to actual uh function that may rotate credentials and then they use they may use of course doesn't mean they use that but but they may use a function to get data from application also disable ftp don't allow ftp here um because probably don't use that disable public access allow only private
access even with proud even with private access we can have access to um internal the infrastructure i mean the actual database use new application but if you have public access then you're absolutely open to the world even if you enable just uh only even if you allow only from azure is still open to too many not to everyone but for tomatoes and finally vav go ahead and use use buff it doesn't have to be a azure vav like built in azure uh um not doesn't have to be built in but um um um it should be last thing by the way about waffle i'm gonna show you is uh when i test this valve by one of the fuzzers
like in this in my case it was loft ninja um this built-in laugh showed me this so
by the way i finally remember the name uh it's mod security you know open source smart security well-known software-based firewall but they have pretty uh well-configured rules so all of those attempts to bypass to to to bypass firewall they were not successful i tried to to to run signal injection and it didn't work um all right so now if you have any questions go ahead thanks sergey that was uh an amazing uh talk and demo um one of the things that blew my mind was the access to any azure um resource anywhere in the world for any client any customer of azure that was crazy i don't even know why that's a load but anyway um we only applied for
maybe one question um one of them was that came in was how do we guard against abuse of the reader privilege in vm based attacks don't give permissions that's that that's the mo that's obvious quite uh answer because uh oh let me give you a bit more details here um so reader role is a role that built in don't use built-in roles so if i go to roles here and let me go to the level of a resource group at least if i click add oh sorry um i am and click add role here is the custom role create custom roles with according to principle of list privileges because built-in roles they have to even if they
they sound like hey just they're either uh they they they over privileged so create custom roles and provide only minimum privileges that you really need to provide very good that was uh that was an excellent talk sergey thanks very much