What Cyber Insurance Doesn't Do For You - Amanda Draeger

Show transcript [en]
Uh, so I am for Liberty Mutual what is called a cyber risk engineer, which I'm sure means absolutely nothing to any of you. Don't worry about it. I'm going to talk about specifically what I do within the entire ecosystem of insurance here in a bit. Um, but of course working for a large old insurance company, I have an obligatory legal disclaimer. It is what it is. I will also add that during this talk I'm going to talk about some generalities about some things that are commonly found in insurance policies. They are not always true. They may not be true in your insurance policy, but they are things that are commonly true. So keep that in mind. Just because I
said a thing is normal doesn't mean it's always true. Um everything can and will be modified based on clauses in your policies. So, a little bit about me. I am a fiber arts enthusiast. >> It's green. >> Testing one, two. No, >> I touched nothing. >> Testing one, two. [sighs and gasps] >> All right. Sorry. And things were going so well. >> Yeah. [laughter] >> Yeah. >> Well, was caught for the recording, so that's cool. All right. So, little bit about myself. Uh, I am a something of a fiber arts enthusiast. Uh, knit, spin, weave, crochet. I do all of the fibery things. Uh, also prior military, which is why I can actually project my voice
to the back of the room. I am used to yelling at people in crowds. Uh, so definitely good at this task. And I have also throughout my career, mostly because the army wanted me to, uh, gotten entirely too many certifications. uh you name it, I've probably had it at some point and most of them I've let expire at this point other than the GSSE because I am not taking that thing again. And something that I learned with all of these certifications is especially the more management ones talk about risk management. And there's these four major areas of risk management that get talked about. You have risk reduction. There'll be chapters and chapters and entire books dedicated to
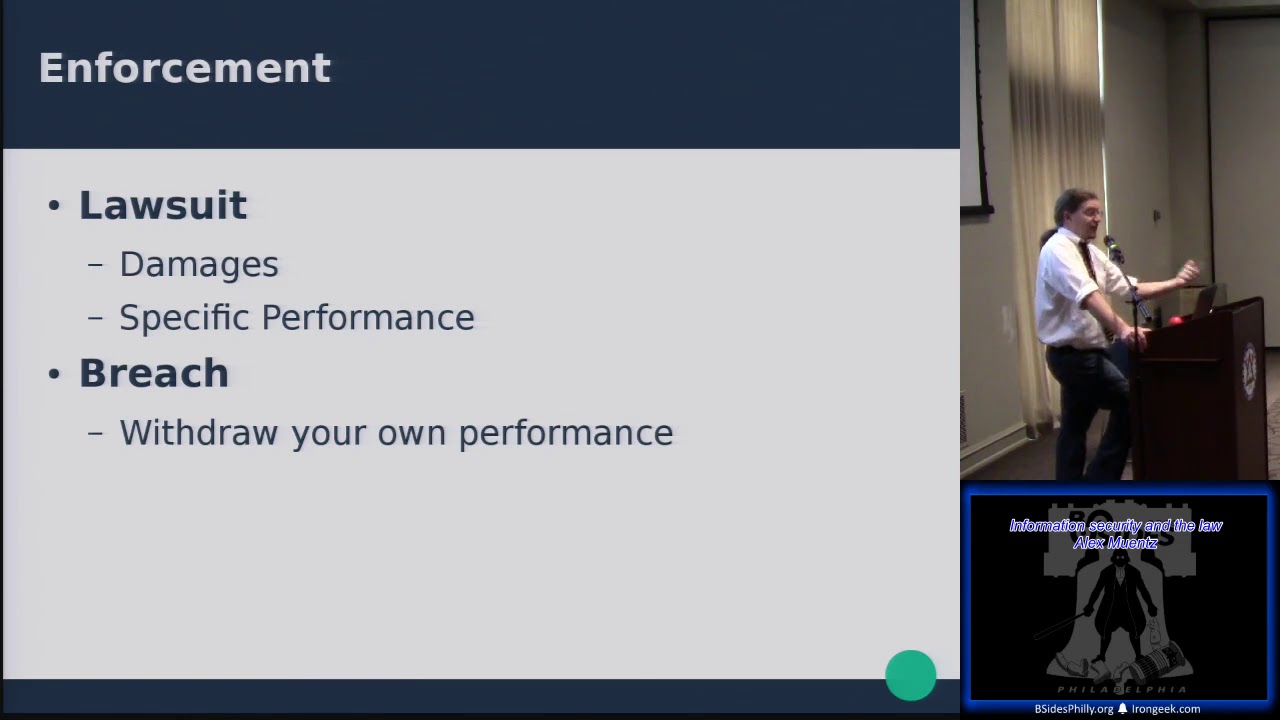
this. and risk avoidance and talking about how you know it's a risk decision about whether you avoid a risk by not taking part in a particular business activity or not. There's acceptance the fact that end of at the end of the day your business carries risk and so you have to decide what do you accept and then it says there's risk transfer that means buying insurance next slide like that is the sum total that you learn about risk transfer in these certifications so what the heck is risk transfer anyway like this is one of those things that I didn't understand really until I came to insurance like two years ago so hey here's what risk
Risk transfer is risk transfer is the transfer of some of the financial portion of the risk of a potential incident from one party to another. So what that means is if your company has an extremely no good very bad day it means that you get a little bit of payout for that. That is it. It doesn't mean that the incident doesn't happen. It doesn't mean that you have an easy button to magically fix everything. Insurance is just financial risk transfer. And so where did we get this idea of risk transfer? Because you know a lot of companies see this as ooh cyber insurance is really profitable like right now let me jump in on that but not
understanding what it really is. And so if you dial back the clock enough years you find that insurance wasn't really a corporate thing. It was a lot of times a bunch of people in a like industry for instance farmers who got together and went all right so we've noticed that most of the time an incident weather event crop failure what have you doesn't affect all of us at the same time. It'll affect like one of us really bad and the rest of us are still okay. So what we do is we form a mutual and so we all pay into this mutual and that was how that risk transfer started by all of the organizations spreading out that risk
amongst each other. One has a catastrophic event, you've got a pot of money to help them out and then the next year someone else might have a catastrophic event and so on and so forth and so you spread that risk out. Now it is worth noting that this is not related to the fact that when you outsource a function you're trying to you know do something to reduce some sort of risk that you have. Now understand that when you outsource you are still obligated to ensure that function is working correctly. You still own that risk. Yay, microphone. My voice thanks you. Uh, so when you're outsourcing functions, yes, you may reduce risk by getting access to additional expertise, but that
is not risk transfer. Risk transfer is totally different from that. And still like as a risk mitigation event or risk mitigation practice, the residual risk is still yours. It is still your organizations. So it is also worth talking about the general cyber insurance process here. And a lot of this is just corporate insurance in general. And this is going to look a little bit different from how you procure your personal lines of insurance, things like home, renters, auto, boat, so on and so forth. And there's really good reasons for that because when you're buying your home policies and renters, auto, what have you, the limits that are being covered up to are like the value of your home.
So, you know, think think dollar values like half a million million dollars. Like that's, you know, what you're looking at with personal lines of insurance. With corporate lines of insurance, if you're talking about the property and casualty policy for a multi-billion dollar company, that property and casualty policy in total might be over a billion dollars. And so that needs a very different process from your personal lines of insurance. So here's what happens is oops wrong button. All right. So you have an insurance customer and within an organization that is usually not the CISO who is buying cyber insurance. It is someone like the chief risk officer, the chief financial officer, sometimes general counsel. It's going to be someone who
deals with the enterprise risk management process, not specifically the cyber process. Hopefully, if they're a good organization that has good security leader and a good corporate culture, they're going to bring in the CISO or their security leader into that process, but the CISO doesn't usually own it. So that person on the insurance customer is going to reach out to an insurance broker. This is someone whose job is to advocate for that insurance customer. They're going to connect customers to carriers. They're going to help that customer understand what their needs are. What are the sorts of coverages that they probably need based on their business operations, based on their revenue, based on where in the world they operate, based on the
particular regulatory factors that they face. Also, they should help the customer understand just how all of this is going to work. They're also going to ask the customer a whole bunch of questions. Usually, in my experience, it is the broker who has the customer fill out a self- assessment questionnaire. If you've ever had the misfortune of filling one of those out first, I am sorry. Um, but they vary a lot based on the broker. It might be five pages including three pages of legal ease. It might be well over a 100 pages of questions. Very, very indepth. And so it is the broker's job to help the customer fill that out. And then the broker connects
the customer to the insurance carriers. And so the carriers are the ones who are actually going to make that insurance underwriting decision. Primarily they're working with the underwriters. Now understand CRO, CFO, general counsel, brokers, underwriters, none of these people are cyber experts. They are risk experts. They are insurance experts. So when a company says yes, I don't do this particular control, but I have this compensating control. The underwriters and brokers are going okay. So that is where I come in. I am a risk engineer. So my job is to be that subject matter expert that the underwriter can reach out to and say, "Hey, this company said this. Is that legit? Is that a legitimate compensating
control? Is this port being exposed okay or is it the end of the world? Is this vulnerability one that we absolutely want them to fix before we underwrite them? or is it a we'd like them to patch that eventually sort of thing. And so I work very closely with the underwriters to help them understand the risk that they're underwriting, but also to provide hopefully actionable feedback to the brokers to pass on to the insurance customer, to pass on to their security team, to pass on to their IT team to hopefully take action and then send word back up that entire chain that they fixed it. So our underwriter can say, "Yes, we are cool underwriting this
risk. So yes, that is a lot. It is sometimes convoluted and this can take a while and this really takes a while when you have what is called a very large insurance tower. What on earth is an insurance tower? Don't worry, that's the next slide that you got a sneak peek of a minute ago. So let's say that your organization wants $40 million in cyber insurance. Again, you don't get to go to just, you know libertymutual.com say "Hey I want this much coverage." Answer a couple of questions and a couple minutes later, boop, you have a cyber insurance policy. Nope. Not how it works. For some really small organizations, there are some companies that'll work
like that, but if you're talking more than a couple million dollars of coverage, that's not how it works. In fact, you're not even probably going to be able to get that from a single carrier. This is where the concept of the insurance tower comes in. So, first actually before we start building the insurance tower itself, going to start at the bottom, which is with what is called a retention. You can think of this as your deductible. It is also called self insurance. Essentially, anything from zero to whatever that retention is. let's say $1 million in this case that is going to be on the insured organization. Uh there will also sometimes be some amount of waiting period. Think uh for
instance your renters or homeowners policy might have a in case your power has been out for x number of hours you get covered for food spoilage. Same concept. You have to have an incident that is x hours long before your cyber insurance policy kicks in. So you need both dollars and hours and then your policy starts kicking in. So let's say this particular insurance broker decided to break this $40 million of coverage into three layers. And again, we build it from the bottom up. So our first company that comes in, it's going to cover $10 million in limits. So they're going to cover incidents that are from one because the company covers the first million to $11 million. So they have $10
million there. They're what we call the primary. So any incident above that retention, they're going to be on the hook for. Then on top of that, you're going to have another insurance carrier. They are excess of primary. So we're going to call them first excess. So 11 to 20 $21 million. Rinse and repeat that for second excess, third excess. So now we have $40 million in coverage on top of $1 million in self- insurance retention, whatever word you want to use. As you go up the tower, the insurance carriers have less risk because this company up here on third excess is only going to pay out if an insurance claim is more than $31 million.
But they also get less premium. You pay most to your primary, next most to first, excess, second, so on and so forth. Along with getting more risk and more premium, that company at primary has the most influence. The insurance carrier before underwriting can do what is called a subjectivity. Essentially that is saying we will only underwrite you if you meet this particular condition. So that might be closing a port, patching a system, providing uh some sort of tax documentation, those sorts of things. And the ability to make those subjectivities gets stronger when you're getting the most premium. Any questions so far? Because this very much sets up everything else. Yes. >> Why is what like [clears throat] like
what particularly in here? >> Why would a company not just >> why would a company not want to do the whole 40 million? I heard it back there. To distribute the risk. Um especially if you're a smaller insurance carrier, a $40 million incident might wipe you out. Whereas, you know, for us, it's like, okay, if I take on $10 million and you take on $10 million and he takes on 10 million and she takes on 10 million, we can each absorb a little bit of that. And then on top of this, there's also reinsurance. And so there's insurance for the insurance part of insurance. So like as Liberty Mutual, we provide insurance, we corporate have our own insurance
policies and then our insurance book, our insurance policies have their own insurance. So yeah, that all of this risk gets spread out so many different ways in the hopes that any single incident does not completely tear down an entire company. And this is really important when you look at say a large telecommunications provider. Um those insurance towers can be like $400 million tall. I do not want to pay $400 million. 10 is a hefty chunk of change, but like we can budget for that. 400 is going to suck. >> I was just thinking what you said about insurers insurance. That's what I would have expected. No company wants to deal with 50 companies their insurance. They
want to deal with one company and that company to offset their risk might insure their insurance. Yep. And so that is again where making sure that the company isn't dealing with 50 different companies. That's why the broker mediates all of that. You know each yes each company up that tower is going to be issuing a policy but everything is happening through the broker. Does that make sense? >> Yes. >> Uh is it correct assumption that some brokers are also a carrier like >> are some brokers carriers? Um for example >> yeah that definitely exists but it's going to be a different part of the company. So the same way like Liberty Mutual has you know it's corporate
insurance we have reinsurance as well but that is a different part of the company we are firewalled off from them. So when that exists there has to be segmentation to make sure we don't have a conflict of interest. >> So there are sorry for the stupid question but >> that's what I'm here for. So what you are saying is that insurance carriers do not work with their customers and directly they just hang out and wait to like broker connect them. >> By and large, yes. Um corporate insurance pretty much always happens through a broker. Uh again, for some of like the smaller business sorts of things that look and smell a lot more like personal lines of insurance,
um then you'll see a lot more of, you know, just going directly to that carrier. Um but that is like if you're talking $5 million or less in coverage, not these, you know, hundreds of millions of dollars towers that some companies deal with. >> Cool. Yes, sir. Yep.
>> One question.
>> Yeah. So what are the inputs to my process and how much do I trust them? Uh yet the customer questionnaire, the self- assessment questionnaire is a huge input. Uh we also use attack surface monitoring tools. Um a lot of them have insurance specific modules that allow us to do those sort of outside in scans to see at least what their supposed network footprint looks like. Keyword supposed um attribution is a very hard problem. And so I try to duct tape those together, look at other things, their website, how they talk about themselves. Uh, but even within those self- assessment questionnaires, especially where there are comments by the organization, that tells me a lot about who filled out that questionnaire,
what they're good at, what they're less good at. Um, I can tell very quickly whether it was an IT person or a security person or a finance person or a lawyer who filled out the questionnaires based on how they wrote the answers to them. And so that tells me where security sits within that organization, which tells me a lot about how that organization treats the security function, which probably tells me a lot not necessarily about a specific control, but how security generally looks within that organization. And so that's a very long way of saying I do a lot of reading between the lines. >> Yep. There's another question up here. >> Yeah. Are there entities of trade
insurance? >> How do you mean by trade insurance? So insurance,
>> I am not currently aware of any such buying of insurance contracts that are currently in force. Again, other than reinsurance, which is its own thing. Um, but It is definitely on the customer to decide whether at renewal they want to actually compete again. Um whether they want to be like no I will just stick with my current carrier or they're like no I I want people to bid on this. >> Yeah. >> Um so that is very much a thing. Does that get you close to an answer? >> Yes. >> Cool. Anything else? >> Yes. >> Right. So do risk engineers also define the standards or do you just see if are combined with the standards and then
calculate accordingly? >> Yep. So do risk engineers define standards? Uh that so it's difficult to talk about what standards are without then diving into the impact of market conditions. So in insurance terms we have hard markets and soft markets. You can think of them as sellers markets and buyers markets. And so we are currently in what is considered a soft market which is more of a buyer market which means a lot of insurance carriers are jumping on cyber insurance and so there's lots of competition so rates are low and a lot of carriers are competing for business. So I can say yeah you have to have this that the other and another carrier be like I'm going to underwrite it anyway I
don't care >> has changed based on the market >> correct right it is very much what is competitive at this moment >> yes >> yeah good question so in insurance bro you mentioned that they advocate for customers >> so [clears throat] can you explain how are they get get paid because advocating for customers like not always. >> Yeah. Yeah. How do brokers get paid? They absolutely get a cut. >> Yeah. But like doesn't make them >> um what encourages them to advocate for customers? A customer can go to a different broker. >> Yeah. it it it is if I do not like the service that I'm getting from this broker, if I don't feel like they
actually have my best interests at heart, I can go to a different broker and they will recompete everything hopefully based on my preferences. So yeah, the brokers have to compete with each other too. >> Yes. Yeah, that there are multiple layers here in the back. >> You want to move on? That's fine. My question >> y question is how often do policy holders make claims against is it very common or is it very >> how often are claims in aggregate very common um it it really depends on the customer and what type of claim and I'm going to get into a little bit of that in a moment. Um, so I'll hit pause on part of that.
Then the second question you talked about your job to ader to ader. >> Yep. >> I'm a >> and I would benefit greatly by knowing what advice you're giving the carriers from a insurance perspective because I'm transferring that risk and I want to know what you're looking for so I know where to focus my energies. So, is that common? CIS. >> Yeah. Yeah. Um, I'm gonna say at the end I will have contact info. Hit me up. I will send you links. Okay. Towers. Any other questions on towers? Sweet. All right. So, hey, I said I was going to talk more about different types of insurance. Hey, look, different types of insurance. So when we talk about cyber
insurance, there's actually two major types of insurance that we're talking about here. Um cyber insurance proper which is first party and then there's various third-party coverages. Most commonly tech errors and emissions uh could also be depending on where in the world you are professional indemnity, miscellaneous professional liability, some other things. And I realize I'm speaking jargon. Don't worry, I'm going to translate. So when I say first party that is harm comes to you the insured. So that is you have an incident you have an outage a threat actor breaks into your network. So these are the direct harms that come to you the insured. Whereas third-party is essentially your liability coverage. Particularly if you are providing any sort of tech services,
consulting, software development, anything where you're providing a tech product to a client of yours. These are the things that basically gross oversimplification get you sued. And so these are things like wrongful collection of PII, of PHI, um all of your cookie tracking lawsuits, pixel tracking, all those sorts of things. Those are that sort of third-party coverage. So if you are a large tech services company, um you are constantly getting sued. Hey, you have lots of claims. Uh if you are a small manufacturer, you have basically no network footprint. you're probably not going to see a whole lot of claims. At least that's the current trends right now. Watch me put my foot in my mouth in a year.
So, it's important to understand that depending on the type of business you have is going to inform the type of coverage you should get in consultation with your broker who hopefully understands your business. Clear as mud. Cool. So what Hey, we have finally gotten to the actual title of the talk. What cyber insurance does and again this is going to vary a lot based on the type of business you are, the size of business you are. If you're a multi-billion dollar extremely mature, have internal sock thread intel, you have a staff of hundreds doing all of the techy things, cyber insurance might be just that financial risk transfer and hopefully it fits into your overall
corporate enterprise re uh enterprise risk management strategy. And so you know your chief risk officer understands the role of insurance and life is good. If you are not that sort of company then insurance can take a little bit different role because uh one of the things that insurance can provide if you have a good claims team is that sort of full service claims handling. It's when you have an incident. If you don't know where to start, again, if you have a good claims team, notify your insurance carrier and they will hook you up with a good breach coach, law firm, the good incident response firms, um, forensic accountants, all of the things that will help you get through that incident.
And one of the few plugs I'm going to make for direct action here is notify your insurance carrier sooner rather than later, especially if you're not that super mature organization because the claims team, you know, again, in aggregate sees this sort of stuff every day. This is their bread and butter. This is what they do. This is what incident response firms and breach coaches do every single day. Whereas hopefully for your organizations, an incident is a once- ina great while event. So hooking you up with the people that do this means that you're going to get the actions that we know reduce the cost and the timeline of those claims. Uh can also help you avoid common
mistakes like OFAC sanctions. We're in the US. Of sanctions are a thing. paying money to terrorists bad. Please don't do it. If you don't know how to check OFAC sanctions, get someone who does. Please uh can also get you access to people like me, people who are able to look at all sorts of organizations across different sizes, industries and give you a sense of what is the state of the industry. What does normal look like? Like we all have this concept of yes, we want to aspire to be here. But in a world where you're just you you don't need to outrun the bear, you need to outrun your hiking buddy. What is your hiking buddy doing? Like
what what are what is their workout routine so that you know to be just this much better than them, you know? Um, also, you know, depending on your insurance carrier, there might be some amount of vendor discounts we can hook you up with. Like, everyone loves a discount. Uh, what insurance does, depending on who you are, what you do, your industry, it's a compliance checkbox. Um, particularly that third party coverage, you might have a legal requirement to carry a certain amount of liability for contractual purposes. So, yay compliance. Um, compliance is not by itself security, but it's usually better than you would do otherwise. So, it's gross but not good. Uh, there's also the consultant effect. Uh, again,
gross but real. Me saying a thing is very different from your internal security team saying a thing. And so if there's something that I can see from the outside that you're fighting your leadership on, if I roll up and say the exact same thing and now it's your insurance carrier saying it, sometimes that carries some additional weight. And so that is still worth doing. Uh what cyber insurance doesn't. So this is the mythbusting portion of the talk. Uh it it absolutely does not instantly improve security. Uh one of my colleague uh former colleagues uh sent me a paper. He's like thinking of you. I'm like oh thank you so much. And it was this agent-based
modeling thing and they're like yes having cyber insurance does not reduce risk at all. I'm like yeah no kidding. It is just financial risk transfer. That is it by itself. Cyber insurance does not change your overall security posture. It does not change the likelihood of an adverse event. It somewhat affects severity because it means you can get reimbursed for some of that, but that's about it. And uh as I was saying before about you know market impacts I cannot magically compel changes. Uh because you know the market right now I have a hard time getting my underwriters to say yeah no we we are actually going to die on this hill because the market is not in a
place where we can do that. when it is a bit more of a stable or even into a harder market, that is where insurance starts to be able to a little bit compel changes. Several years ago, we had a harder market and that was when you saw MFA become much more ubiquitous because we were able to actually competitively say this is what the standard is and all the insurance carriers agreed on that and so we could provide financial incentives in that harder market. I'm not there today. uh cyber insurance does not mean you have solved all of your risk problems uh your risk is still your risk. It does not absolve you of doing the rest of the
security things well. Again just because someone underwrites you does not mean that you magically have a good security policy. So you know please continue to do things on top of get insurance. Please. Uh there is probably an entire talk here uh for the people who are particularly nerdy about legal language about exclusions. So exclusions are the things that are explicitly not covered by your policy. So again, for instance, with homeowners, usually flood is excluded. You need a special flood policy in order to cover flood events. Similarly, uh, war is a very common exclusion that you'll see in cyber insurance policies. This is a little bit of an interesting legal area because none of the current
war exclusions for cyber policies that exist have gone to court. So, we don't know how legally defensible they are. Question. >> I know the judgement. They got out of it because of They did not completely go through all of the legal hoops. So, they settled. >> Yeah. >> Yes. So, so close. Like that is the closest we've been to having a judgment on a war exclusion. But then there's also like seven different common languages that I'm aware of off the top of my head. So even if that one went through, we don't know how any of the other languages would fare. >> Yes. >> I'm getting there. [laughter] >> Another question back there. I'm just
ask
um other things that companies will put onto their policies. Uh I mean ultimately if there's something you want and you're willing to pay for it, someone will underwrite it. I mean, it it is the thing that, you know, Lloyds will famously underwrite anything if you pay them enough. Um, you know, quarterbacks, arms, stuff like that. Uh, so yeah, you name it, it is possible to cover it. I can't think of any particular examples off the top of my head. Um, okay. So war being famous exclusion ransomware uh that is you know you would think ransomware is the reason you're buying insurance kind of sort of um but if we're looking at an organization we're like uh we don't want to deny them
but the they're not looking great. Excluding ransomware can be a way to get an organization coverage without coveraging the highest severity probability events. Um so you know that is very much a what is insurance actually good for? Depends on what coverages you're buying. All right. Infrastructure. I will cover infrastructure and then get back to you. Okay. >> Encryption event. ransom there or just like >> the entire event? >> Yep. >> Yeah. I I saw the paper recently on the value of the ransom itself if we're thinking of the same one. And yeah, very interesting but also very narrow. Um okay, so infrastructure if you have a network outage because you have a power outage with an infrastructure exclusion not the
insurance company's problem. that is a property problem. So the business interruption that happens due to power outage, water outage, other such infrastructure not inherently um my as the carrier's problem. Does that cover you? >> Yeah. Yep. >> Yeah. And so again, this is where policy language is really important because some policies will only cover against a threat actor event. Some policies will cover full system failure. So failure for basically any reason. So, you know, an administrative oopsie um might be covered under your policy depending on your language. Um but a lot of times that power outage is not an administrative oopsie and thus with an infrastructure exclusion would not be covered.
>> Okay, that is a whole other thing. Um gonna make the last point on here and come back to that because I am in fact almost done. Uh so last thing is uh cyber insurance does not generally cover the value of your data. Your data does not inherently have value according to most cyber insurance policies. What you're being covered for with cyber insurance is the cost to get back up and running. So whether that means incident response costs, whether that is the business interruption which is often an order of magnitude more than the incident response costs. Um those sorts of things are what is covered by your cyber insurance policy. So you know you can say your intellectual property is
valued at $7 billion. Cool story. I'm looking at the financial accounting to say how much profit did you lose during this period. That is what we are insuring. >> Yes. >> Does that include regulatory fines? Potentially. >> Right. Right. Um and that is one of those things where what can be covered under your policy depends very much on where in the world you are. So for instance I think it is in Netherlands where regulatory fines cannot legally be covered by insurance. So there's a whole lot of localization that has to happen with insurance policies. So, okay, suppliers going down that are like your IT suppliers, your software suppliers. Um, that gets into the world of contingent business
interruption or CBI. Contingent business interruption is a very fascinating coverage because when you call upon that particular coverage, yes, your insurance company can cover you for that outage. However, comma, when you do that, you are giving your insurance company the legal go-ahad to turn around to that supplier and claw that money back. So, consider carefully whether you want your insurance carrier to be involved in potentially a lawsuit with one of your critical suppliers. Depending on the relationship you have with your supplier, that might be fine. That might be the worst thing that could possibly happen to your business and it would cause you to go under anyway. So that is why contingent business interruption is absolutely coverage that
exists, but I don't actually see it used a whole lot. Okay. So, any other questions? Yes. It covers the whole incident. Does it also cover action afterwards? >> Yeah. Does it cover class action lawsuit? Uh, very frequently. Yes. Um, so yeah, it it's one of those things where there's a lot of extremely fuzzy math in trying to communicate how much incidents cost. Uh I have an entire other talk on that that I can point you towards the recording of. Uh but one of the few areas where I have really good math if you're in the US is notification of a data breach is about a dollar per person. So that is stamps handling all of that stuff. If you add on the um like
credit monitoring and what have you, that's about another $10 to $15 per person, which is really fascinating if you look at the number of records that are affected and you kind of think of that as your data liability. So, you know, we've for many years we've heard data is the new oil. It's interesting to think about it instead as nuclear waste. What can possibly go wrong? And so, you know, understanding if you hang on to a 100red million records of Americans, that means if all of that gets popped and you have to do credit monitoring, that's easily multiply times 15 100 million. That's Yeah, that that's a bunch of zeros. I don't want to think about that number.
Sorry, public and math is hard. Um, math and public is hard. That >> [laughter] [snorts] >> it is clearly that time of day. Um but yes, so yes, that is absolutely a thing. And so that's one of the things that we look at when I'm looking at an organization is how much data that could be a liability do they hold? >> Yes. >> Okay. This may be a dumb question because I may not know what I'm talking about, but I'm going to ask it anyway. Okay. Um, is subregation a part of this process? Like do you would like like hypothetically would a company go after a nation state if it was proven that they were the source of the attack?
>> Yeah. So subregation towards a state actor I have not seen. Um, but >> ever >> I doubt I would see that from the insurance side of things. Um, I can definitely see a world in which we would be working with like our own DOJ or equivalent depending on where in the world this incident happened. Um, in order to get what we can um but yeah, going after a state would definitely be something I would leave up to justice and diplomatic channels, not insurance company. Um, but subregation as far as going after companies, that's that whole contingent business interruption thing I was talking about. >> It feels like a good like side [laughter] together. >> Yeah.
All right. And back >> organizations maturity over time if you have a team of 10 that has just a baseline and then months later they put a team together, they bought solutions. Is that something they come back to with another question on there any kind of change there? >> Yeah, how do you communicate changes over time? Uh mostly that's going to happen at renewal. uh if there were any subjectivities that we gave a time period. So like let's say it was you know within 90 days of binding the policy we need this then you know we would have some communication at that point. Uh but for the most part it would happen at renewal and again your
main communication method is going to be that self- assessment questionnaire. Depending on the size and type of organization you are, there might actually also be an underwriting meeting in which the potential insurance carriers get to listen to your team doing your presentation on what you do and you largely get to drive what gets presented to us. Uh, and so in those presentations, I've seen everything from the normal checklist to, hey, here's our cyber security culture maturity framework. I'm like, "Cool." Um, you had one first. >> Tracking cookies. Yes, lawsuits. They're a thing. >> Oh, they are. >> Yes, absolutely. Um, you name the data tracking mechanism. There's probably been a lawsuit in the US about it. And
so raw numbers, um, my claims team sees more like general data privacy lawsuit sorts of claims than actual like a company got ransomware claims in the last couple of years. Uh, so lawsuits are a very definitely a big thing that happens with insurance claims. >> Yes. MFA
is there.
>> Yeah. What are the technologies that are up and coming that I wish companies would do? Um, I would say one that I sometimes see on questionnaires is password managers. Anything that you can do to encourage your users to have unique passwords everywhere is goodness and just better credential management period because let's be real, identity is the hard problem right now. Um, the other one that I don't see being asked, and so I don't have data to back this up, but it's one of those things that most of us in this room probably know this. Um, ad blocking and similar sorts of network traffic filtering. Um, ads are extremely gross. the root cause of a lot of info steelers in particular
and info steelers are how creds are being stolen and then reused and so on and so forth. Um, so that would be one of my wish list items that I would like to see a lot of organizations move towards.
>> [sighs] >> So, how to get discounts? Uh, again, current market, it's really hard to get a discount because we're already borderline not profitable. um that there was some interesting news earlier in the week about um one of the major carriers, Beasley, kind of pulling out of the US market a little bit because it everyone is kind of on edge right now. Um but in general, yes, your security posture as you communicate it to your carrier helps to get better rates when we can in fact afford them. And also, you know, would help us to, for instance, you know, going back to those exclusions, like if you look good, I'm not even going to think about a
ransomware exclusion, that sort of thing. So, it gets you better coverages as well. >> Yes. >> So, I'm wondering back to this question of standard. So I work at PEN breached a month ago and immediately got sued by alone being negligent in [clears throat] their practices. From what I know, they were not negligent according to definitions, but nevertheless, I wonder to what extent insurance company standards end up defining that bar of look, if you're good enough to get insurance, are you good enough to not be >> the that is a I would have to go talk to a lawyer sort of question because I mean, you're talking about the legal standard of due care of due
diligence and I don't hold that in my head. >> It also seems very on point for pen lawyers to not waste any time while yeah um I do believe we are about time but I will continue to hang out um if you're not headed over to closing ceremonies. It has been awesome having you as an audience. Thank you so much. [applause]