Information security and the law
Show original YouTube description
Show transcript [en]
I'd like to thank you all for coming out for hearing me hearing me ramble on for a little bit it's kind of ironic that I'm here at Drexel we're 28 years ago I got kicked out of the mechanical engineering program it seems that they didn't like my rule that said you know got kicked out for drinking because I thought the rule was if it spontaneously turned into beer while I was in my possession I wasn't bringing beer in they didn't like that argument they didn't like that argument much but obviously it shows why I've picked a different profession so disclaimer I'm not representing the opinions of any of our any of my company's clients are my
employer if I still have one at the end of this talk I may be a lawyer I'm not your lawyer I am however a certified information security professional trademark so follow that advice if you like this is for edutainment purposes only don't take anything I say with a grain take everything I say with a bit of a grain of salt if you actually have specific questions ask me later so how does the law affect okay who here is an information security professional trademark who here wants to be an information security professional trademark okay oddly enough the law affects us more so than in a lot of other industries because we this is one of the this is an industry where if a
bad day for us can be potentially criminal you know who here has ever been tested the wrong box who here is lying right you find out something's out of scope that's a fact can be a felony yeah like oh man I dropped I can I drop shell on this thing that's not ours Oh oops sorry and there's some sales guy going hey maybe we can sell them a pen test you've already done half the work no that's not a good idea maybe it is I don't know it's you know aggressive sales okay so what areas of law affect us as information security professionals first contracts and I'm gonna sum that up I'm gonna some three years of law
school into one PowerPoint slide contracts what you agreed to do regulatory law right it's it's two people or two companies or you know one person in a company decide to make an agreement if they love each other very very much and they sign a contract and sometime later they decided that they really don't like that agreement or one side wants out well you have to go back to the contract to figure out what on earth you actually agreed to do and oftentimes that can determine how you get out of the agreement or what happens if you don't uphold your side of it then there's regulatory law what you have to do if you are in health care
you're familiar with HIPAA if you're in financial services you're familiar with gramm-leach-bliley Act are really what dribbles out of that is the FFIEC guidelines and then there's criminal law what you must not do unless you like going to jail I used to work as a public defender jail is nasty from that perspective and I got to leave so walk through contracts basic idea is that a contract is a binding agreement it's not just a promise because we break promises all the time it's both a promise plus a what I'm going to give up if I don't do the thing it doesn't have to be reasonable I can sell my clock let's see I could sell my car for a dollar which
would be thoroughly unreasonable because my wife would probably understand I could also sell my car for a hundred thousand dollars and it's a 12 year old Saab so it's not worth $100,000 but the court if if it comes to a dispute will not say that was an unreasonable deal contracts are something for something I promise to perform a penetration test against your web application in exchange you're gonna give me all the monies it can't be one-sided as in it can't be I will do these things and I don't have to do anything on your side it's a it's a sum agreement by which each side is giving up something or doing something there are actually very few limits on the
contracts first is if it's actually against the law if it is unenforceable as in I cannot have a contract that says I get to kill you I can't have a contract that says I am going to delete you are going to deliver to me two kilograms of Peruvian blue flake that's an unenforceable contract for those of you unfamiliar that's legal that's you know Peruvian blue flag is cocaine otherwise known as the pentesters friend at Def Con that great this is gonna record it isn't it okay the other is if the contract itself is what we call unconscionable it is so one-sided that the the the the the two parties making the contract one has all
the power one doesn't you can sometimes try to void a contract or phrases of a contract by saying there wasn't any negotiation was not a fair one however the standards are fairly high you have to for you to to win on that you basically have to show that the other company had some kind of power over you there was duress there was some kind of some kind of control over you that forces you to sign that contract so just because Comcast has a great deal more power than I do when it comes to the triple play plan I can't say that the contract itself is unconscionable and unenforceable okay so let's talk about contracts relevant to us
anyone here ever read an end user licensing agreement damn more masochists than I am those are binding even though many of the time people don't read them right you click through them but if you actually read through them are a turn of service and you'll is usually when you're talking about software the term of service is when you're talking about a web application or a website offering you some service or you know X as a service by using that by by agreeing to that you agree to each side gets to limit the use the other may use you can limit behavior such as say for example Facebook does not allow you to use their systems to harass other members Twitter
has a similar rule I understand because they're you know threatening to remove our president-elect from it which will probably make many members of his campaign staff happy but another would be limit modification I for example in a EULA are in a software license I'm a bar you from reverse engineering my software I'm a bar you from using it for certain purposes if you've ever read the iTunes you uh you may not use it for running a nuclear power plant if you find a way of operating a nuclear power plant with iTunes you're clearly you're deranged because the amount of fee like you know please enter your Apple ID to restart the core because it always seems to
forget mine yet it still holds me as certified as a Apple desktop engineer which I haven't had that certification for like 12 years it may limit republishing say for example if you reverse engineer the code you're not allowed to publish it you find vulnerabilities in the code you're not allowed to tell anyone but the manufacturer stuff like that we can put that in the contract that binds us and restricts the rights we might otherwise have another example for business contracts those who may end up working for a consulting firm which will probably be half of you because right now it seems to be that's that's those are the big people who are high those are the big
groups that are hiring us off out of out of college so if you go work for Accenture Pro tippity or Dell SecureWorks or some other large shop that just you know pipeline in pipeline out the MSA or PSA this is a contract that is often the first thing you sign when you engage a consulting firm it doesn't actually bind either party to paying anything or doing anything it just says any subsequent contracts will follow these rules payment will be on net 30 you have ten days to accept or reject the deliverable stuff AG that asana is in that it's basically sets the ground rules for how we're going to do business the next one is the statement
of work this is what each side agrees to do I will pen test this web app named this on these dates for this amount of money simple because you're relying on all the other boilerplate back in the master services agreement once you start doing consulting work these are your Bibles when you first get your you know first engagement my rule has always been to to juniors who have worked for me read the statement of work it doesn't matter what the salesman promised it matters what they signed to do you will not make their lives easier you're instead going to give them a five page deliverable showing all the vulnerabilities in their app have a nice day that's what your
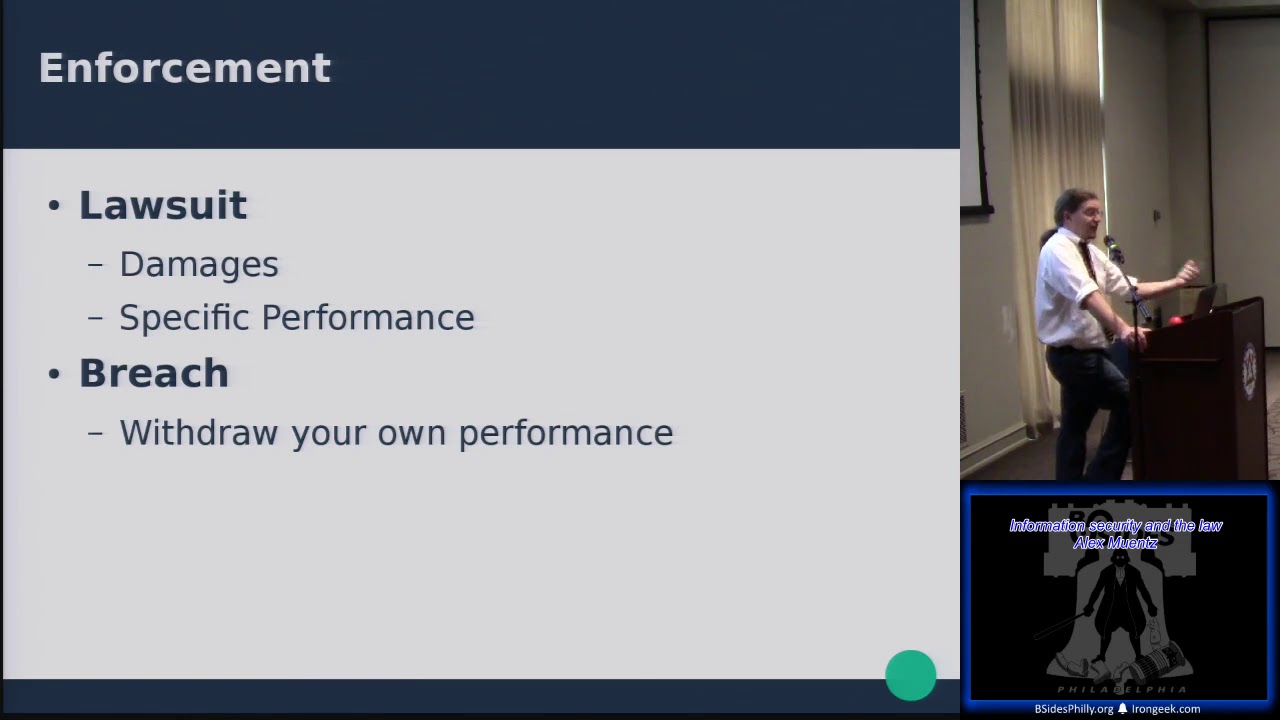
promise to do that's what you're getting paid for do that others non-disclosure agreement what you can do with the information you gain during that engagement and this may limit you so how do you enforce a contract you can follow a lawsuit say for example if one side is not performing to the likings of the other you can file a lawsuit saying I demand you either four four what you promised to do are pay me damages so for example I do a pen test for a company and I say it's going to be twenty thousand dollars to do a pen test with your network I perform it and they don't pay me well what are my damages
say I haven't given them the deliverable I've done the kickoff I've done the work I have a document my hand that describes it I have not necessarily given them anything of value I've done stuff I've expended effort I've expended time I can find I can sue them for damages what is caused for if I've done the pen test or the workers have done the pen test what it's cost me to pay them what business I may have forgone because I did that are I can sue them for specific performance give me the money or if I've done a contract for something like I want a piece of gear give me that piece of gear that I have requested are pay me damages
you can also if you decide you'd realized the other side is not going to perform you can do what's called anticipatory breach which is I will not perform either for example you find out that the company is not going to pay you you can stop work you can say I don't I have good faith to believe that they are not going to perform as they have done I'm gonna back out on my side of the contract are usually in the case of when you're doing information security work for a client as an consultant it's something like there's a cooperate you'll have a cooperation clause in the contract because you can't do a true black box pen test right you have to
know things like what is the scope of your environment what applications do you run what sub businesses do you run you want to get information you want to necessarily ask them questions about things if they don't cooperate at all like I'm not gonna give you I'm not going to give you an IP list I'm not going to give you a list of my domains or I'm not going to give you a subject matter expert to walk things through well you can say that was a part of the contract without that I can't do my job well I'm backing out so that's contracts and contracts will come back to bite us in a bit regulatory law this is a bit more complicated
because this is no longer an agreement between two parties this is a this is when Congress the President and love each other very much and they create a new regulatory agency which is established by the legislature but it also has power from the executive executive branch and this is a little bit of civics a regulatory agency such as say Health and Human Services has given power by law to do things like regulate healthcare within the United States on one hand you should be thankful for it because many of you will learn that HIPAA is not a dirty word some of you if you are working for health care inside hip is the best that you have to get what you want I've I've
seen this more than once at health care organization where if you're a security engineer and you say something like I would actually like to pay for Splunk are I I need this tool to do a thing or we need enough Windows licences to actually match the number of PCs we have as I see a couple people smiling at me going yeah I've been there and you say it's a security problem and you watch us your management goes uh-huh but if you say if you use the magic words HIPAA non-compliance all of a sudden stays also payment yeah purchase orders get signed so it's a great stick to use however you can't overuse it I had a friend once try to
use it for something like it's HIPAA compliant for me to have a better parking spot like that's that's a challenge let's see how that works out for you I mean I once tried to I under FDA rules I tried to order Ducati through my job by claiming that it would get me to work faster and my boss well Volta say my boss said now also trying to get try to get it was quantum that made tape drives that we were ordering like can I get quantum to buy me a bike and just deliver it and call it tape library and that's why that's why I don't you know do purchase orders anymore so back to
regulatory law sorry I'm went on an aside there interpreted by courts and the law can be changed by Congress for example HIPAA could be changed by annex Congress however odds are usually the legislature will not revisit laws very often you have HIPAA and then hi-tech is like seven years later which affected some of Hippos requirements disappea security it takes time for the legislature to make decisions however the regulatory agency itself promulgates rules based on those laws so if you're thinking in sort of a IT governance space the law is like the policy right policy documents are usually unchanged vague high level as in data that is sensitive should be appropriately protected right that's a great thing to
reach for what does that mean what do I have to do as a system engineer or ARS assisant men or a networked grunt what what controls do I have to put in place and maintain in order to meet that goal well someone gives me a set of standards and hardening guides that I can follow right I can't figure out what adequate security is but I can definitely apply these patches turn off these services and limit users right that's easy that's a checklist I can follow so regulatory agencies generate regulations such as 45 CFR 160 and 164 Part A and Part C are the HIPAA Security Rule some of you are nodding and others you well you'll learn
they can be changed by Health and Human Services on a 90 day basis they can promulgate new rules and completely change what they want as long as it matches back to the legislation so they will still not change things quickly because they want to have sort of predictable they want to give predictable rules for entities to follow they're not gonna change things willy-nilly unless they're worried about something unless there's a change in regulatory focus and predicting regulatory focus is kind of a big chunk of my job nowadays which is how is Health and Human Services going to change the audit guidelines by which covered entities are far forced to to do how does Health and Human Services make
you follow HIPAA well they can find you they can find you for non-compliance they can also some in some regulatory scheme mistake an borrow from the market the FDA's biggest power for mishandling clinical data are filing false Clement clinical data for drug effectiveness and drug safety is they can bar you from the market that's great that you spent a billion dollars for that drug you can't sell it here have a nice day oh and by the way the shareholders are gonna start calling you soon that's a pretty big stick to threaten you with however most people want to follow the regulations they want to know what they mean so there's clarification and sort of prediction rules that are available
first is regulatory statements the regulator people in the regulatory agency may make statements about areas of focus areas of interest for example SEC about two years ago said we're going to for four entities that are regulated by the Securities and Exchange Commission but not any of the other financial services rules under gramm-leach-bliley they said we're going to we're going to basically expect that any shop that falls under our regulatory agency has to follow the NIST cybersecurity guidelines and they left it that and you know my my my vend consulting shop got a lot of calls like how do we follow these well we're gonna come we're going to assess you we're gonna you know kind of walk you through
what these requirements are and nine times out of ten it's like adopt a policy kit and follow it but how do we know which one the SEC likes well we've watched and see if they're making any statements we watch and see if they've published guidance sometimes like for example Health and Human Services publishes guidance they publish the audit guidelines for the office of civil rights audits that they're doing that's now in Phase two it's basically saying these are how we interpret our rules for you to do a thing which is really nice it gives you more it gives you more color about how how am I supposed to interpret this rule that says I should
evaluate encryption to protect data everywhere at rest in transit only on some systems what and you look at the audit guidelines and go oh this is much more specific so you can use that to follow and come up with how you govern your IT infrastructure going further to be if you are a if you're in the my job is to secure these things is to say this is what HIPAA requires anything above it is gravy anything below it is well a gap we have to remediate it but think of you kind of much much better walking or marching orders then say just the legislation so criminal law this is both the least and most fun part because we
joke about how you go from being a pen tester to a criminal I don't give an example in a bit but violation of criminal law you have fines you have imprisonment neither of which is very much fun how are they interpreted well laws are passed by legislatures and then numerous court cases will come and better define what that means example that comes to my mind is the wiretap act 18 USC 25 11 that says it is unlawful to intercept electronic communications while in transit does an email on an email server if you pull that from storage is that a violation of the wiretap Act and four years nope every court case said no because it's in storage however
temporary it might when it's on the wire it's a violation so if you use a packet sniffer to recreate that that email and grab all the packets knock off the headers drop it back there's the email that's unlawful but if you grab it from the mail spool it doesn't violate the wiretap Act and that was good law for a bunch of years and then for a circuit change that a couple years ago and said no clearly that's interception as well have a nice day but it's interpreted by courts to say this is what we think the law means and the savvy lawyer can read the court cases and go this is how I think it's
gonna happen how your case is gonna fall out later so you can make a pretty good prediction about what a law how law is going to affect your individual practice or what you're trying to do so I'll give an example Computer Fraud and Abuse Act this is a lot of commenters have said fairly nasty things about this law I'm probably one of them because it is rather vague it is this is a subset of it to access a protected computer definition protected computers it's used in banking or by the US government are as involved in interstate commerce or communication so anyone can anyone think of an example of a non protected computer under this example and I think
the only one is like the the trs-80 model three that's in my basement powered off right like every one of us has a protected computer on there in their possession because this is a computer and it is involved in interstate commerce and communic our and our communication so accessing in with with uh without authorization are an access of authorization that's vague right like for example if I go to a website and I view the website that is accessing said website that's accessing a protected computer right because it's a in a web server is a is involved in interstate communication I am accessing it by hitting the website and I'm getting information from it I'm you know go to
index I pull index dot HTML I've obtained information from that system if what if I don't click on a link to get to that page but instead manually write the URL is that unauthorized access who here thinks it isn't who here thinks that is that if you write URL by hand is that without authorization okay I wrote a I wrote an amicus brief for weave so I'm a little familiar with them
yeah you had to manually write them nope he was convicted on that his appeal was on venue he could still be recharged so it actually was it you could still argue it's unauthorized access even though the hacking he did was manually type of your actually ran like a Python script I think to get them that's the that's the problem it's this is fake because if I send you with that link I'm not AT&T but I'm sending a link back to the AT&T iPad website that maybe unauthorized access to a TN t--'s web server so that's why this this law is rather vague and kind of dangerous because it shouldn't be unlawful it you should know when you're violating the
law if you get you know the analogy I'd come up with for this is if you get pulled over by a cop and the cop goes do you know what you're doing and you say actually no I don't and the cop says well you know like one I'm not dating you so I'm not so you know if you really cared you know what you did wrong but secondly you want to have clear rules on criminal law yeah ya know because the definition of protected computer is it's not necessarily that I have what we lit what we in law call a term of art the protected computers defined us anything used in in interstate commerce so it
doesn't actually require protections now protections may give you an idea that this is unauthorized access if I require you to enter a username and password to get in well clearly I'm trying to uh I'm trying to exclude you if you're not an authorized person but this law is still vague and this is why it's a little bit damaged this is why it's a little bit dangerous so how does this affect you as an InfoSec person you're likely to be under a bunch of contracts as it is right you are working as a pen tester for a company and you have a nondisclosure agreement you have an employment contract you have a statement of work with your come with the the test
that the test target you are attempting to follow regulatory compliance you're probably trying to ensure regulatory compliance for your client and you also want to stay out of jail so give this as an example pen tester John and if anyone gets the reference I'll give you a point no one's a find a dunk no one likes Dunkin minutes okay check out Dunkin minutes talks at gherkin they're awesome trolls so pen tester John is hired to pen test a B and C over at Ecore he gets show on D which is a system not in scope of the pen test but still owned by evil Corp he obtains healthcare information while pen testing system D what legal
action can pen test John be afraid of he's violated the contract right because he agreed I would test a B and C B is right out do not touch cannot has he may have violated the Computer Fraud and Abuse Act because he has he has access to protected computer without authorization and obtained information from it he has obtained pH I question is is it a HIPAA violation it may be a HIPAA violation for a corp if it is not securely held but pen test John may not be regulated by HIPAA so these are sort of how those how those laws affect pen tests John I realize I'm simplifying like hell but I no one needs a full-on
legal lecture for this so if pen test John only hit a B and C he hasn't violated the contract he likely hasn't violated the Computer Fraud and Abuse Act because he has authorization to do all those pen testy things to a B and C which is why it's scary when you do when you do a pen test and you have that scope document often fighting over what that scope means and you want a very very defined scope because you want to know what's safe and what isn't and I have run over scope once or twice and many if you will as well it's figuring out before you do anything dangerous violent validate scope that is the
easiest that's that's a simple thing to do before you waste time and risk liability so give a second example developer an she takes him job at evil Corp as well she signs a contract with a nondisclosure agreement and a non-compete and she develops a specific application for Ecore she then quits she wipes the drive of the work laptop to show that there's no evidence that she took her code she keeps the code base and she sells the competish sells all this stuff to a competitor of ecore what has she done and try to walk through this it's a contract breach she's violated the non-disclosed agreement she had with evil Corp now this is not inherently criminal but it
can result in financial impact to her she can be sued for the damages she also violated the non-compete which can bar her from working for the other company it can also bar she can get sued for the damages she also though has violated the Computer Fraud and Abuse Act she wiped the hard drive and this is one of those fun things there's actually a case in out of the Fifth Circuit out of Chicago called IAC vs. Citroen where a guy is working for a real estate development company he's using his work laptop to site locations he would like to buy for his own purposes he then decides I'm going to quit but he's sizing up these
locations to purchase he does a low-level format over rights to drive hands it back and says here's my work laptop oh by the way I'm gonna go compete with you and the company is working for Susan under the Computer Fraud and Abuse Act saying you have unlawfully accessed a protected computer your work laptop and destroyed information and his responses you gave me the laptop doesn't that assume authorization and the court says you weren't authorized to do that because you had decided you were going to quit and your actions show that you retro actively lost authorization that scares me right because at what point do I lose authorization it's not like I get a document that says you can't do this
anymore it's my actions have made me unauthorized had D authorized me from allowing to do this because I'm not acting in the best interest of the company so let's go back to an she was an authoress she might not have been authorized to wipe the drive she wasn't acting in the interest of her employer with that laptop she was acting in her own interests was that damaged well she's removed evidence she's from removed proof that the come that evil Corp can show that she stole the code so throw this out for other questions hopefully this made some sense he'd Asano's gonna act against the interests of the company yeah yeah it's not just like I've decided to quit it's you have
now done actions that are adverse to the company that if the company had known you were doing it would be you would lose you would get fired for or you'll get sanctioned for it
[Music]
I would agree with you and actually there was talk about reforming the Computer Fraud and Abuse Act after Aaron Schwartz's case because there is no the intent requirement under the Computer Fraud and Abuse Act is that you knew what you were doing you admit you did the act intentionally motive what you intended to have happen is not a part of it so a lot of argument in the in the weave amicus brief was the role that pentesters and independent security analysts have is that we are essentially consumer protection for the internet right we find vulnerabilities and we report them to if we're you know if you're white hats we then responsibly disclose them to the to the software
manufacturer or the website to say hey we found this you should fix it the problem is is that it's in it is under the Computer Fraud and Abuse Act unlawful to pen test that website without that websites permission and it matters not what our intent is if our intent is pure good where it says I'm looking for vulnerability sub a friend of mine and occasional client Sam bone does this where he by Google Dorking finds things like open FTP sites that are opened by pieces of malware and one case was he finds an open FTP site at a hospital chain in Louisiana and says I found documents in this FT this unsecured FTP site that no password is
required and there's patient records here either someone's really incompetent or you've been you've been poned and he goes and contacts them and they well they don't take this the way any of us would which would be you know I would hope if you're in a system in position and you get a phone call from someone saying hey I think you've been poned you should the answer should be thank you I'm looking into it rather than I'll have legal contact you and if you say you know and make threats but they instead it wasn't handled well technically that could be a CFA a violation because you are looking into a website you're looking to our site an
FTP site that has patient information has information that is potentially sensitive but you don't have authorization and while I might argue that a guest access FTP server is saying is equivalent to saying come on in you know the documents are fine the court may not agree with that the court may say you should have known just because it's open and available doesn't mean you can take it so that vagary is that vagary is kind of worrisome but it's that's I can only explain what American law is now I I don't foresees Computer Fraud and Abuse Act getting changed significantly in the in the near future with like a mode of requirement
so the let's let me see if I understand the high power authorized to do the pen test you're authorized to okay and so you can clearly go to the the company that hired you and said I found this this is bad your argument then is you find evidence of crime oh yeah there's a you should now whistleblower protection is this is whistleblower protections usually used for if you are an employee and you go to a regulatory agency with insider information your job is protected this is a little bit different because you're wondering about criminal liability there is a rule that says you generally don't have rights of privacy in evidence of crime so this is often used for drug
sniffing dogs the idea that it's not a search because the dog will only alert if there are drugs in your car or luggage or whatever we kind of there's evidence to show that this is not true but the the dog sniff case is run on the idea that if there's a magic wand you have that can only detect contraband in this case the this evidence of crime you don't have the if it's truly evidence of a crime you could go to law enforcement and say I found this as a part of my pen test I think you would be protected it would kind of tip it would depend on sort of the magnet not the magnitude of
the crime would depend on your agreement with the company you might still not get the money for the contract because you have violated the non-disclosure agreement and you know you I mean generally though yeah you well they might I don't think they'd be able to sue you because you could defend on I violated the non-disclosure agreement because there's evidence of a crime and most of these contracts will have a I like pretty much every non-disclosure agreement I've read has said has it has a cut out for except to obey other legal requirements such as if you're subpoenaed right you know I have a non-disclosure agreement but a court has said I have to divulge this information I think you
would have some more protections this is probably one of those very very fact-specific because it might be that that evidence of a crime isn't actually evidence of the crime for example you know I think the hypothetical I I've had some odd co-workers and like this is evidence of a crime yes and this is a law firm of course they have evidence for crime they're defending somebody it's not evidence of the law firms criminal it's that their clients are scumbags yeah
[Music]
let's see my so say for example you negligence say it's say it's negligent right you you you you know you've been you've been hacking all night your eyes are crossed and you transpose to numbers so instead of 53 I hit 35 and you compromised it I think yeah this is this is one of those sometimes it's better to walk away and not say anything [Music] I mean I think it depends if it's a out of scope system owned by the same you know if your yeah then it's usually the better because you still have protection of look I was up I thought I was operating in scope I inadvertently did this because I'm thinking of one the one
I've done whereas out of scope was they had a DNS redirect and they gave me the domain names not the IPS so I didn't know about the redirect nor did the person who hired us and the redirect went to a box and Amazon's in AWS and you know Boop owned it and like oh this because I'm like look at the IP I'm like this is out of who was this piece of like oh it's Amazon's oops and we just like we found this sorry and it wasn't like because it was a web app the web app itself was kind of was that was what we were penned as I'm like technically it's still owned by the
company we just said like this installation of this was broken and we didn't mention that we hit it we just like assumed but if it's if it's clearly someone else's like in my case it's probably best to stop as soon as you notice it and just sit tight you know stop hitting that because odds are unless you've done something to it right you've just if you just poked it and went oh it's got vaunt you know it's got a bundle version of the Opera the application I got shell to stop back off and go not installing code not dropping a meterpreter shell into it not changing anything you're not leaving a touched file or anything like then it's going okay and
that way if you like you didn't continue exploiting it so it shows it's evidence to show if in case you do get prosecuted like it was a mistake you know sorry wrong house problem not a oh I got all this and then continued attacking because even though the law isn't clear it's often the the sort of the the narrative that comes with it if you are a pen tester and what do you do you break into boxes cuz you're paid to do it and that's all you do and you have a history of just that's what you do hitting the wrong box it's a different story than we've who if you veteran if you've read anything he's written or
interacted with them comes across rather abrasive you know he's he's a he's a troll and what I think convicted him more than running the script was the post breech chat locks where he talks about selling them any men sort of said that is a joke but it's one of those this is a bad fact that makes it more likely way for a prosecutor to say this is the story I have to sell the jury bad guy versus pen tester who couldn't shoot straight the second narrative is a lot easier because I've talked to people who have done this who have said I solve honor ability in fill in the blanks cite that they had access to one is a case they
the the state they were in had a website dedicated to paying taxes and they realized that in the URL was their social security number like a problem is of course he calls up a friend and goes like I think you're in this - can I borrow your social security number to test it and that's a sign of true friendship like hey - Pender's like hey what's your SSN I just just need it for a thing and they test on my chip I pulled up all your records with just your SSN didn't require you saying didn't require password and in the code in the URL was also you could toggle between he and you for something is like
T oh wait that's the taxpayer view what does the a stand for admin group there's the admin page with no authentication is like so he writes this up and sends it to him was like oh I mean he's being a good citizen right and he didn't get prosecuted but he did get a because the person who first responds to his call was like thanks for showing me that that's really good I'm gonna you know I'm the you know I'm the project manager in this I'm gonna give it to the engineering team and they're gonna they're gonna fix this and then a week later it's hi We're law enforcement from that state we'd like to ask you
some questions and evidently the way they said that gave him the fright and you know hired an attorney and it's one of those like I said when did I stop being a good guy and started becoming a bad guy even though your motives may have been clear we come across as weird to normal people right like you know who here has lockpicks in their possession right and it's like well of course you know like who doesn't know how to pick locks who doesn't rifle a desk because it's there who doesn't do things like you go through a TSA checkpoint and you watch the screens to see what they're doing just that's my natural curiosity as it
is most people in this industry that comes across as strange that comes across as malicious to normal people and we need to not be and also a lot of pen testers especially junior ones will try to be is what I call Oakley spookley as possible which is like as outrageous like I own all the things and it's we think it's funny until you try to explain that to 12 people couldn't get out of jury duty and then it's like yeah you're not cool anymore you're you know check interests yeah
[Music]
okay now the first question is your testing model like I do I have to authenticate that I own the website you're testing okay so we can pick any here it gets into a potentially strictly subject which is what information are you allowed to gather from a web web site that is authorized right presumably the actual content on the index page clearly that's like I've put it out there for it I'm go I would argue that some things like TLS headers and other things you would do to fingerprint an operating system and a web server would be there as well yeah mm-hmm okay Ryan my knee-jerk reaction is possibly both because you you have been you have put a system out there that can
be used you intentionally built it there you you and the analogy I would if I was a prosecutor uses you were the one who put the loaded pistol in the in the playground and left it there right because you put a tool that is very very dangerous and said anyone who wants to use it can use it yep well no cuz it's if I put the tool that you have to use right I download Kali I use it all I've given you is the tool that you have to you have to you have to build and use if it's just the website that the website itself your systems go out there's a slight difference there
right you're you're doing Kali as a service if if it's just download Kali and they're there there you're just running a gun store so you're giving people guns and saying now go to the playground I think the difference is you're giving more power to the set if you're running the gun store you're giving more power to the user if you are instead let's leasing leasing the tool there that you can use the website to attack another site are ting to obtain this information from another site you have I think a bit more liability it's I'm sorry yes CFA is very vague and it's I I've read enough stuff that says it was deliberately so to catch because
the belief was hackers are so super powerful that we that you can change your behavior to get through loopholes and laws and the problem is is that that is what we call obeying the law if you don't break the law oh that bastard you did exactly what it needs to be to not break the law yes we call that bing Vall biting but no we need to have these vague laws to catch those wily hackers and like I don't have a you know I don't have a bug strip in my and you know in that's bad like I don't have I don't have bear traps in my house to catch people you you shouldn't have these this
this very very broad space you can trip over yeah okay right usually there is an invention disclosure clause that you may have negotiated also many state laws German limit how much the company can demand that every piece of intellectual property you come up with is theirs so it the Bennett's presumably like they taught you something then are they showed you something at least got a good idea like oh you can do that huh I can monetize it over here then you're using some of their intellectual property so presumably then if they've had a half competent invention disclosure clause that's there's a kernel of this of your new invention that is theirs so you would have either half they would have
some rights to it that you would either have to license bat license to you or they might own it so it kind of comes down to that invention disclosure clause and the state law so it falls into the it falls into that depends on a lot of like very specific things depending on the state you're in or the country you're in and that invention disclosure clause as well as what Colonel you took from what they were doing if it's just no he'll write you you learned how to write faster code that might not be as protectable as some very very specific thing that hasn't yet been released so it falls down to a couple of things that
are much more specific