Securing Embedded Devices In Robotics And IoT
Show transcript [en]
Victor good everyone my name is um Victor um my an Hardware design engineer um basically I design intelligent systems uh my talk today is on securing embedded devices in robotics and iot thereby breeding the gap between Innovation and security um what are embeded devices now this they are found in um different sectors they are using different sectors um like the healthcare sector um manufacturing sector they are basically like the brain behind the the work that this um robots or Internet of Things um devices applications do um with the rise of Technology advancement uh we need to secure this um these devices now on the other hand internet of T refer to a network of interconnected um physical
devices embedded with sensors software and other technologies that enable them to collect exchange and add on data over the Internet so Internet of Things um is basically collecting exchanging of data over the internet and acting on those data uh what are we trying to what is we trying to address now despite the importance of these um devices um they are poorly secured um thereby making them um easy targets for cyber attackers um therefore leading to brushes leading to data loss and in critical cases physical har um our aim is to close the gap between Innovation and security and try to understand these threats and find ways to mitigate against them now why uh why is securing these prices
um important like I said they are very attractive for our Cy for cyber attackers because of their nature they're very vulnerable um it comprises of both the hardware the the firmware and the network um protocols so some examples could be um let's use the heal care sector as an example so in the healthare sector you could see uh maybe someone is trying to have access to a patient record and un authorized access to a patient records due to multiple login attempts um in the in in the manufacturing sector someone is trying to have access to the the sensitive data like the sensors data or trying to manipulate a robot and which could lead to to a patient lead to to to which
could lead to a harm of someone working there and in some cases they could shut down the the production cycle because of a Cyber attack or in critical infrastructures like the railway system where um the they use the Internet of Things um someone can try to um gain access to sensitive data this could lead to potential delays for travelers so these are the potential risk with in of and Robotics now we want to understand these challenges now for the hardware side of things someone could try to gain access to to this um devices or by physically tempering with them and gaining um access to sensitive data for example like an iot embedded camera someone could try to plug in the circuit and try
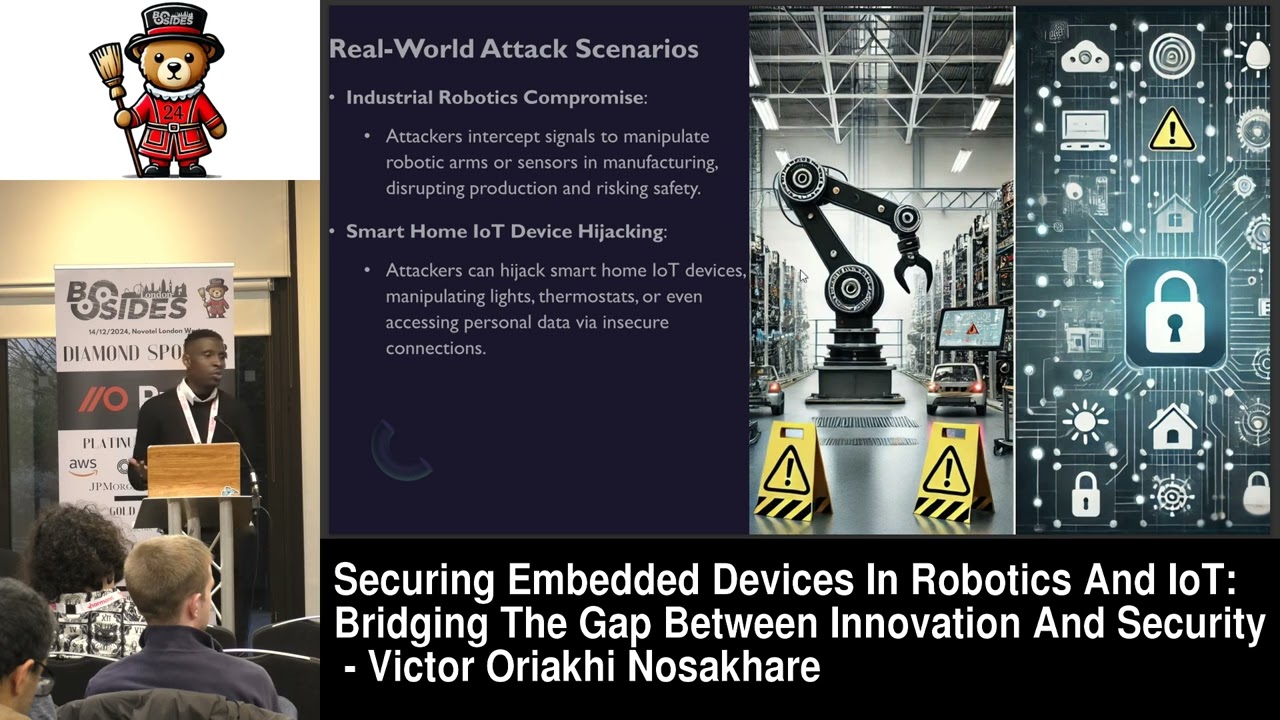
to get sensitive data um for the f and software vulnerabilities things like weak passwords um weak encryption this could be exploited if not properly secured then communication protocols like the Wi-Fi and Bluetooth which internet obtains rely on if not um properly encrypted it could be intercepted uh real world scenarios like I explained I talked about um I give an example about a robot in the manufacturing sector sector someone trying to manipulate it from a remote outside of the building or maybe in the healthare sector someone is trying to gain access to a patient record or a smart home um in of things device are Jing like someone's trying to have access to um trying to manipulate
um the devices in someone's home like raing the temperature of the thermostat switching on and turning off lights or even get access to sensitive data so what are security strategies we could adopt to mitigate against this thing this um cyber attacks on embedded devices one of them during design phase we could um include the we could build security into the design phase by using the hardware roote of trust method such that um any device that is connected to this um system it has to beated it has to be verified before it can be used within the system um during the development stage we could use secure coding practices and regular updates then during the deployment we could use
continuous monitoring of anomalies um anomalies are things that uh is basically used in um machine learning or AI um things that are not like they're not um Regular they different from the normal patterns we know for example like I want to use the banking sector which is which is quite different from what I'm talking about in the Bing sector maybe um we have a data of someone's um finances for the last 6 months since he has been in the um since he open that account maybe the highest transaction he has made was between um five between £5 to um to £600 and all of a sudden we're seeing a transaction of around £10,000 at all
hours you know that's an normal it's we have we have a data and all of a sudden we're seeing something different from what we understand so we could money use we could um include um anomaly detection in real time to ensure that these devices are monitored thereby leading to um safer a strong security for our embedded devices um what are defensive measures we could adopt one of them is AI driven anomal detction which I just explained that's like using machine learning so machine learning we can train this mod you can train this um data over time so it recognizes a pattern so is it something that is usual from what it knows it it spots it and knows that this
is like a cyber threat or a Cyber attack then the hardware Ro of trust method which I talked about out earlier so um so we we could secure our headu so that only undesignated devices can operate within the system only verified um devices can operate within the system such that um any system that's noton it can't operate with the system and thereby we could limit um this cyber attackers access to sensitive data another one is um we could regularly secure and equp our firmware or bits and this would also help to um reduce or prevent on on on authorized access to our embeded devices now what are the future Trends in embed security um the first one is
um um AI will enhance real time threat detection adapting defenses in response to evolving attack patterns so there's a lot of things going on right now in the AI industry so with the use of machine learning we're training models you train models to to recognize patterns you understand recognize patterns and by recognizing patterns we could know we could we could judge a legit legitimate um um legitimate um data from a one that is fraudulent or it's not authorized also things like Quantum resistance could cryptography is being developed to prepare embeded systems for future Quantum Computing threats there are also emerging standards that coming up um the National Institute of Standards and Technology n and the
European um UN Agency for cyber security they driving U improved security practices in Internet of things and Robotics now what are the practical take homes for engineers or developers and Security Professionals one of them is we should try to implement some secure coding and conduct regular vulnerability assessments by this way we'll be able to um reduce access to um these cyber attackers um also we should prioritize device firmware updates and use secure libraries for security professional specifically um Our advice will deploy more monitoring systems detect anomalies um create incident response plans uh for internet obtains and Robotics setups now as I conclude today while there is an increase in technology we also need to balance the
security side of things so that as we're involving the security side is also getting tighten tightened so that the future is safe and we have um more secured embedded devices and that's that it for me thank
you are you want does anyone have any question pass this down so just so it goes is there a a a space for education in uh solving this in that you're teaching boards and Executives that secure devices is good and also teaching Engineers what does good security look like or do they do they get taught that [Music] now I don't really get question um is is is education a gap in that um Engineers don't know how to do secure design it's not that they don't want to do secure design they just don't know that it's insecure but and or or do they know it's they what secureity design is but it takes longer and the
executives don't want them to spend time on it because it doesn't earn them any more money you can answer on the um um I think one of the problem is actually um education is part of it education is part of it um um know many with the the rise of technology today there's a lot of advancement in technology um is the reason for this for this um stock so we're trying to want to try to balance it you understand while there's a rise in technology we also need to because these devices are sophisticated you understand sated and because of their nature they they kind of like um they poly secured so we need to balance the the rise in technology
with security so that's the that's why this event is actually is a good event because it brings together professionals from different fields and we able to share ideas and try to adopt strategies to mitigate this um s attacks anyone else no in that case uh thank you very much indeed Victor thank you





