You're Gonna Need a Bigger Boat
Show transcript [en]
in general I think in in cyber some of the problems and how we can kind of rethink how we do things to kind of turn the tables I suppose um so a bit about myself um I actually run my own company um which has been going six years almost to the day and I've aged about 15 in that period of time um and we specialize in sort of cyber crisis management resilience that kind of thing for for organizations but that's kind of boring um I'm also a high altitude climber which I think is far more interesting um and when I was asked to put this presentation together today um I was asked to talk a little bit about the
industry and like how we could change things maybe bring in some aspects about diversity why we need to have a more diverse sort of cyber Workforce and so on and so forth and I was thinking about the problem and I was thinking about how sometimes you have a plan you have a trajectory and you need to suddenly change it up and you need to suddenly come up with new ideas and new solutions to address the problem and the perfect story for introducing this actually comes from a mistake I made so this uh is taken actually this summer in Peru climbing in the Andes um and this particular Mountain was a huge high altitude Peak it's about
6,700 odd meters it's massive um and this was one of the objectives that myself and my climbing Partners wanted to do and we had a plan we had looked at the toppos we' looked at trip reports we looked at other climbers who had failed on it that year what had they done wrong what what happened what were the problems and we sort of showed up and we thought pretty cockily like you know we've got this we're pretty fit we're pretty strong we know what we're going to do so couple of days in so you climb for a couple of days you get to this point here where this photo was taken which was high camp which is about 6,000 M so
21,000 fish um and it was beautiful we got there we saw this Sunset like the weather was calm there was no wind absolutely spectacular views and you're sort of sitting there and you're thinking this is just in the bag this is an easy win now like 100% we're getting to the summit not a problem and at 6,000 M there's about 50% of the partial pressure of oxygen that we're breathing here which means that when you're lying in your sleeping bag you're doing bit of a cardio workout you're sort of slightly out of breath which is really lovely sensation um and you get up at midnight for a summit day because you climb basically for8 nine hours get to the
summit come turn around come back before it gets dark so at midnight the alarm went off and I thought okay great ice axes crampons everything ready started off and it looked really nice it was really calm no wind beautiful all the weather forecasting that we checked looks perfect 3 hours into the summit attempt a storm came in that we hadn't seen anywhere maybe through negligence maybe not who knows um and a storm at 6,000 MERS is probably one of the worst things that can possibly happen and the wind was like nothing I've ever experienced in my life it got incredibly sketchy very very very quickly and we decided to abandon the summit attempt unfortunately the
wind was so horrific I got some surface level frostbite on my hands which was very attractive um but we also had to improvise so a lot of the things that we would do to normally get down the mountain safely we could no longer do we had to cut Corners we had to improvise we had to use things that we'd never otherwise use um we had to absil off one snow steak at one point where the person who was ABS sailing below me was going down and I could see this snow stake just kind of going so I stood on it and then realized that that meant I now needed to go down on that same snow state with nobody
standing on it so I went down with my eyes closed um but I'm here so it's it was a success but it made me think that there's actually sometimes the usual way of doing things just you have to just change it up you have to completely think of a different way of approaching something and sometimes that can be a bit scary and it's from mistakes or whatever um but I'm hopeful that we can talk a little bit and I'm hoping that this talk in some ways giv you more questions than it does answers actually so what I'm going to look at today is a couple of elements of this so looking at turning the tables because at the moment
it's very much in my opinion skewed towards the attackers um and I think there are a couple of things we can do to try and um shift the balance a little bit between our side and their side more disruption and regulation which we'll talk about in a moment thinking about the problem differently to how we're currently thinking about it and also looking at the diversity angle as well um and and the humans being the focal point of everything so I'm obviously a climber and one of the key sort of parts of training for climbing is your anerobic capacity so how you can exercise that cardio kind of exercise so I was watching this video on um aerobic
training and there were two guys one was interviewing the other and the interviewer uh the guy that was being interviewed said to the interviewer why do you breathe and he said to everyone watching this video just pause the video here and answer the question why do you breathe and I thought I know that take in oxygen pass out carbon dioxide simple done the interviewer gave very similar response and then the guy said okay cool um but why why do you take in oxygen and Bre out carbon dioxide so I paused the video again and I was like uh I don't know carbon dioxide a waste product so you have to get rid of it and Like
Oxygen you taking for like energy and stuff maybe I don't know something like that and I was kind of aware that my answer was now really starting to stretch the limits of my my knowledge of biology and the interviewer gave a very similar response and then he said again okay so how do you get um energy from oxygen and I was like I don't know I don't know why we breathe I have no idea why we breathe turns out I don't have a clue um but it was a really interesting uh way of thinking of of things and what I liked about it was when you ask the question why several times very quickly you
appreciate that your understanding of the thing that you thought you really really really understood actually you don't really really understand it and I thought quite cockily well of course I know why we breathe yeah I don't I didn't know why we breathe at all no clue I do now but back then definitely did not know and I think that's very true in cyber as well because I think there's a lot of times when we talk about things that we have a surface level of knowledge about which I think is good and I think we all need that but if you start to drill down into the why you quickly realize this isn't my area of expertise this is someone
else's area of expertise and perhaps we ought to turn to those people so I think the lesson really that I took from this was that if I am talking if I have a question asked to me about for example pen testing I don't know really anywhere near a sufficient amount of information about pentesting so I'm going to go to one of my friends who is a pentester and get them to answer the question and I think staying in your lane and understanding what you understand and and passing on to somebody else what you don't is really really crucial for collaboration and So speaking of disruption this is um for those of you who don't know this was Med the
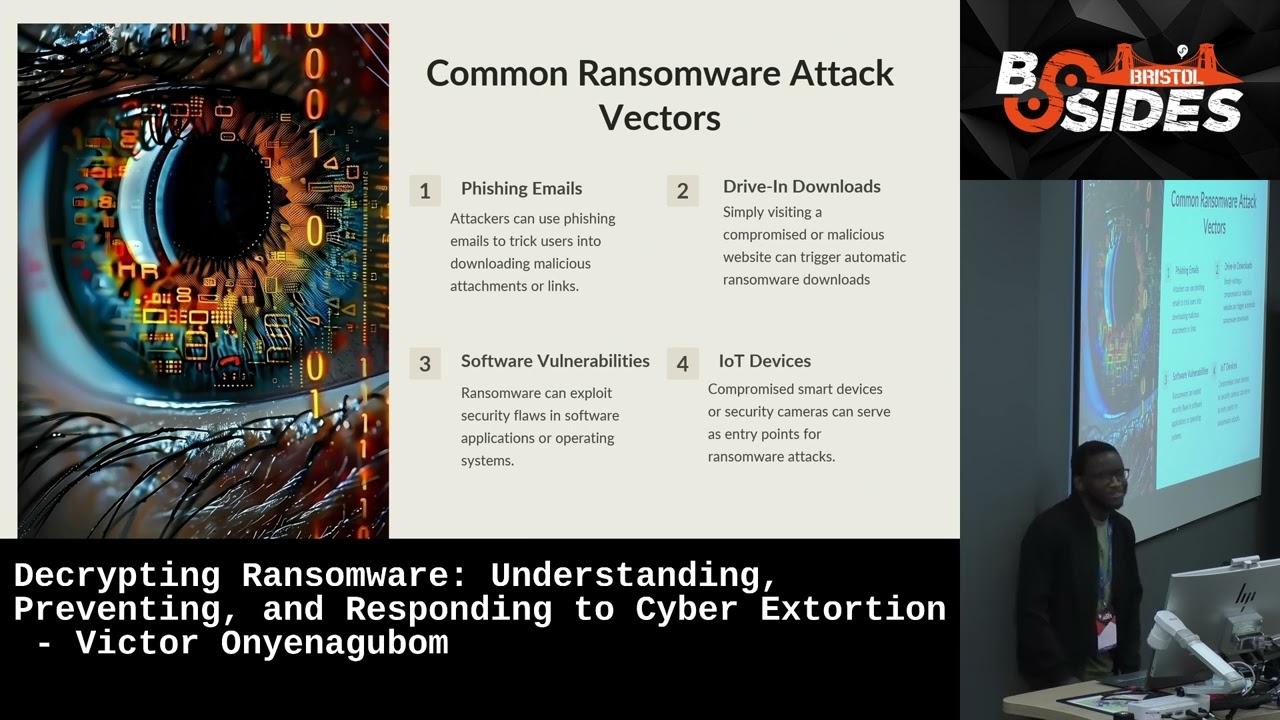
beginning of Medusa who a ransomware group they did a promo video video which if you haven't watched it go and watch it because it's absolutely awful um the production quality just isn't there for a group that earns that much money but anyway um so ransomware is kind of my thing and I talk an awful lot about ransomware and I think the one thing we have as an as an issue in the industry when it comes to ransomware is fundamentally we are making a really big mistake with how we talk about it how we discuss solutions to it how we talk about it as a sort of global issue as a micro issue um and that's because I
think for a lot of people we're living in a little bit of an idealistic uh scenario and what I mean by that is when I've done a lot of work in this space one of the things that I come across a lot are two sort of myths that get pushed out by the cyber security Community when it comes to ransomware and both of them are incorrect and both of them don't help us solve the ACT ual problem that we're seeing so the first one is if you pay they won't be true to their word now I would love that to be true I would really love that to be true because it would be a great stick to say do not pay
a ransom no one wants anyone to pay a ransom but the truth is that there is not an awful lot of evidence to back that up because actually what we're seeing is ransomware groups build Brands those brands are completely contingent upon being true to their word and if they say they have your data and um if you don't pay them they're going to dump it online and then you pay them and they still dump it online the next person is not going to pay them and they understand that and the insurance companies understand that and the ecosystem that has built up a around ransomware understands that and so as a result they often are true to their word
which doesn't really help our moral argument of don't pay the ransom but that's the reality the second sort of myth that I see proliferated a lot is that if you pay the ransom you'll be hit again again very little evidence to support that at all in the wild and actually slash hilariously all of the clients I've worked with who have paay a ransom have actually got their um General councils to draft terms and condition agreements with the ransomware groups that say you promise not to hit us for two years which they sign um so that's the reality of the situation and the reason I say this and it is awward it's a difficult topic to
talk about because no one wants to advocate for paying a ransom I'm not advocating for paying a ransom but in order to fix the problem of ransomware and to start thinking about how we're going to innovate and change how this balance of power is operating we need to actually look at the reality of the situation and address the reality not address the idealistic situation that we want to be in that we hoped we would be in um and I think the the real areas here where we need to start um sort of innovating And discussing mainly around cryptocurrency so um when I talk about um how people talk about how we're going to disrupt ransomware because at the
moment ransomware groups a bit running a muck um they're all over the place they're making tons of money um and they're able to wash that money very very quickly so the problem from a crypto perspective is that um there's many from a crypto perspective but this particular problem um there's a a great piece from Pablo Escobar's accountant and he talks about in his book how the major problem they had for the median cartel was that they had all this money and they couldn't clean it they couldn't wash it through and put it into bank accounts and actually use it so what they would do is put them in farms put it in floorboards put it in all these
different locations and hide all this C cash and they lost billions every single year to rats rats were literally eating billions um from this cartel and what's kind of cool I suppose in a sort of dystopian way is that now we live in a world where you could have washed that through various different cryptocurrency blockchains um pretty much undetected and you don't have that issue so if we look at the disruption that we've actually managed to cause in terms of tracing the money the only case that ever really gets cited is colonial pipeline so dark side who were the ransomware group involved in that attack um I think probably if they were ever interviewed would say it was a mistake
to have hit Colonial pipeline um they hit Colonial pipeline Colonial pipeline paid the ransom um but the attack was so significant and so noisy that the FBI got got stuck in and they managed to recover a small percentage of the cryptocurrency um but not lots and overall that's pretty much the only case we ever really cite as an example of how we disrupted the flow of money so a lot of these problems um revolve around kind of coming out of thinking well just don't pay the ransom no one should pay the Ranson of course that's the idealistic situation we would love to get to but the reality is people pay the ransom saw a study that said 86% of
companies pay the ransom um Boeing got hit uh last week I think and it I'm not going to say they did pay the ransom all I'm saying is lock bit took them off the website you can draw your own conclusions as to what happened there um but people pay and in order for us to start thinking about how we disrupt ransomware and how we actually change his balance we have to acknowledge that people are paying we have to deal with that problem not say why should never pay which comes on to the next topic of problematic activity uh that I've been looking into really um recently which is disrupting hactivism so hactivism and I'm talking specifically about activism
in the context of armed conflict so I'm not talking about uh animal rights activists and people like that I'm talking about um activism that stems from armed conflict um that's going on in the world um so the icr you may have already seen this put out eight rules that they sort of said were sort of a um Rules of Engagement I suppose for activists that they suggested some of which were don't hit civilian targets don't hit hospitals you know the things that you typically expect under International humanitarian law and it was a good first start it was definitely a good first start the problem that we've been seeing is the it all started obviously predominantly with
the Russia Ukraine conflict uh and that sort of birthed I suppose an issue with a group in one group partic in particular known as KET um who also have videos you can go out and watch promo videos um and KET and Anonymous Sudan are obviously pro-russian um activist groups incredibly well resourced incredibly sophisticated very good at what they do um and have caused a lot of problems but I think what's more interesting in a sense was um the situation that has happened really recently with Israel and Palestine so on the Saturday when the attack happened um the first attack happened should I say um an Indonesian activist group um and the Moroccan cyber Army who are
unsurprisingly based in Morocco um went and attacked and took offline Israeli News sources so um newspapers Etc the were online took DS them took them offline in response to that the Indian cyber Army uh Indian cyber force sorry then hit Palestinian businesses took a load of Palestinian businesses offline um this is all basically within 24 hours of that first attack um that then caused Anonymous ghost who are a Palestinian group to attack the Indian government and several key businesses in India um and then we saw the same Palestinian group take um uh exploit of vulnerability in the red alert app which is the Israeli um sort of missile alert system and they sent fake notifications
to Israeli citizens saying there was a nuclear bomb that had been sent out so then Iran gets involved well Iran's activists should I say get involved cyber Avengers went after the durad power station in Israel and then the anti-iranian group The arving Club went after things in early IR on and very quickly within probably 5 days you had a bunch of countries brought into a conflict that otherwise really wouldn't have been involved in that conflict you know India wasn't going to typically be brought in two 24 hours after that um attack was launched but yet activists did that activists brought everybody involved and for the first time ever we are seeing sort of civilians if you like
being able to get involved um in armed conflict and influence government decisions influence government thought processes which is the first time in history because usually you would need to have weapons and you would need training and you would need people on the ground and now we have activists that can basically do all of this themselves so again we have to start thinking outside the box and one of the points I wanted to make about this was when the um icrc brought out their Rules of Engagement a lot of people in the community mocked it and they laughed and they made fun of it and I think they missed the point actually because I think the point of those rules was not
really to bring order to all of these groups that are kind of anarchistic within their nature I think the point of those rules was to start a discussion as to how we can start regulating this conduct which at the moment is quite frankly chaos and it's causing damages to to businesses it's causing damage to governments it has the risk of escalating armed conflict as well around the world so I think again when we're seeing people make attempts to start thinking outside the box start bringing in new ideas I think it's really important that instead of just shooting them down we actually start looking at how we could start a discussion from them and develop them further funnily
enough killet did say that they would abide by those rules I don't I don't know how much you want to trust that but that's what they said so another issue that obviously always comes out with this with regards to cyber is diversity the talents and skill shortage and burnout and I think the I always really struggle talking about diversity because I'm acutely aware that I'm a white woman from a pretty privileged background and I'm not really the most suitable person to start talking about diversity but I do think that um when we view risk the way we view risk and the way we manage risk is often built upon our person or experiences and what we
know from his you know our experiences in life what have we seen before what are the patterns that we've seen before and what did that lead to and if we all have very similar backgrounds we're all going to view risk in a very similar way which is going to lead leave us much more vulnerable to attack to not seeing opportunity to not seeing other things like that um and that kind of comes into burnout as well so one of the things that someone mentioned to me the other day was about the rate of burnout uh in Europe in the cyber security industry was some ridiculously high figure and I was thinking about it and I was thinking
there's this culture online amongst us all which is very much about how you have to be working seven days a week and somehow you're not really committed if you're taking a holiday and you're not really committed if you're saying well I'm going to just take the week off and enjoy time with my family and somehow like you need to be online you need to be on LinkedIn you need to be posting you need to be doing this course and going to event and all of it actually isn't at all healthy and it's not really helping us get to a point where we can start seeing the problem seeing the wood through the trees so to speak and
actually starting to deal with it in creative ways because we're all literally maxed out and our bandwidth is completely taken up by everything else so I think again in terms of attitudes as a community it's really important to recognize that there's absolutely nothing wrong with someone taking a break there's absolutely nothing wrong with taking time out from work or taking a a break between between jobs that's completely fine and everyone can just you know do what's best for them which brings me to my final piece um and this is something that has um come to my attention really recently um sort of within the last year and it kind of links back to the ransomware group
issue and the issue that we have in cyber security is something that I think is best called cyber inequality and that happens at two levels so the first level that I would say needs to be sort of thought about um which relates to ransomware is that we've seen a huge spike in ransomware groups going after companies in Latin America in particular but also South Africa and countries like this and the reason they're doing that is twofold firstly it means that they can attack organizations in those countries and probably not attract the attention of europol and the FBI who probably aren't going to Care the second way the second benefit I suppose for them is that they get to try out new
tactic tactics and techniques without necessarily being picked up and looked at and they also can Harvest a load of money from these companies as well and the problem that we have is that these countries um in so South America for example don't necessarily have the same level of expertise in their law enforcement they haven't got the same um sort of maturity um as if going for a rapid digitalization process at the moment all of which leaves them hugely vulnerable but it also means that they can become safe harbors for a lot of these criminals as well because their law enforcement doesn't necessarily have this the sort of expertise that some of the other countries have who have dealt
with it much much longer the other side to the Cyber inequality um piece which I think is concerning within our and and hampering a lot of our progress as an industry is at a national level and and I was made aware of this at an event where I spoke to the ceso of a large bank and he said that his cyber team was 3,000 people and I thought wow what are they doing and then I thought I spoke to one of my friends Jake Moore and he was talking about farms and he was saying that Farms have a huge amount of sort of digitalization now in terms of to increase efficiency and productivity and things like that
but they're not going to have a ciso they're not going to have a security team they're not going to probably have anyone providing support for the most part for anything that they're doing yet in many ways they're critical National infrastructure you know if you were for example a activist group and you wanted to cause widescale disruption you'd have sort of some really weak areas in the UK just to name to name one country where you could hit them and cause maximum disruption with very very little support for those for those those Industries and I think one of the problems we always talk about the skills Gap what we're not talking about is how the complete lack
of talent complete lack of um people who are going into Industries lower down because there's a group of financial institutions who can afford to pay large six fig salaries they can afford to pay for all these people and have 3,000 cyber security people on their team but that leaves a massive void for a lot of other companies who now don't have any ability to do that so how do we start managing that um as well as a community because that's obviously giving us some really strong some really big weak points that I think um we need to address so I hope this has been a super depressing start to your day um go and check out the ransomware
group videos if you want to laugh because they are funny uh funny and a kind of funny not funny kind of way um if you want unhackable goat stickers I am around all day come and see me um someone go volunteer for the talk otherwise I've I think I have the right to select them do I not didn't we agree that um and if you have any questions I'm wandering around come find me um yeah enjoy your day guys