Understanding, Preventing, And Responding To Cyber Extortion - Victor Onyenagubom
Show transcript [en]
thank you my name is Victor and I'm a I'm a lecturer in cyber security from TDE University from the London campus and I'm really nice to be here in brist this is my first time in brto so and I'm loving it so I'll be talking about um a topic called um decrypting ransomware understanding preventing and responding to cyber extortion um this topic is something that is um really really like coming up these days based on a couple of attacks that have been on so we'll be looking at the basics and how this can be prevented and what you can do around trainings and backups and also protecting your network making your network stronger so first of all what's a
ransomware a ransomware is a form of of malware where the attacker would usually infect your div infect your system after infecting your system most time they will decrypt your they would encrypt the file and ask for some amount of money most times this payment in Bitcoin most of the time and just in 2024 alone which is this year we've had a couple of like major um ransomware attacks from that of the NH okay so we had the ransom attack that attack like the COV covis is a is a partnership um it's a pathology partnership between the NHS some London hospitals in the NHS and C lab where they like um take blood samples and stuff like that so they had a ransomware
attack we've had some um ransomware issues in France and in Chicago in the largest Hospital in Louis um they also suffered like a ransom attack where children's like healthcare data was were taking advantage of and around somewhere actors were asking for some money for them to get their um data back you know so um ransomware is is a living and breathing issue it's not just like an abstract kind of concept it's something that like um happens sometimes okay so I've in the previous slide this is just a more detailed overview of what I said in the previous slide most times it Tak three steps but it just depends on what it just depends different scenarios it could be different it could
happen in different ways in different scenario most time this form where you probably get the malicious email get infected and of course your data is encrypted you know no longer have access to your data talking about the CIA Tri where you have to talk about your confidentiality your integrity and your availability you know your your data is no longer available for you to have access to them so it's encrypted it's useless to you you don't have the keys and the is going to like tell you I need some money for me to give you this description key and we have um we have different types of ransomwares crypto ransomwares we have crypto around somewhere normally that will be the one
way you encrypt your files and you need to pay for a decryption key we have the um Locker around somewhere where your files are locked and your files are shut down and there's also there's also the ransomware as the service we'll be looking at that when we talk about things around how ransomware in the future how Ransom are going to evolve in the future part of this talk part of this talk the last part of this talk talks about we look about we look around things where how would ROM evolve in the future what are the things we expect to see as regards ransomware in the future so we'll looking at that in the next couple
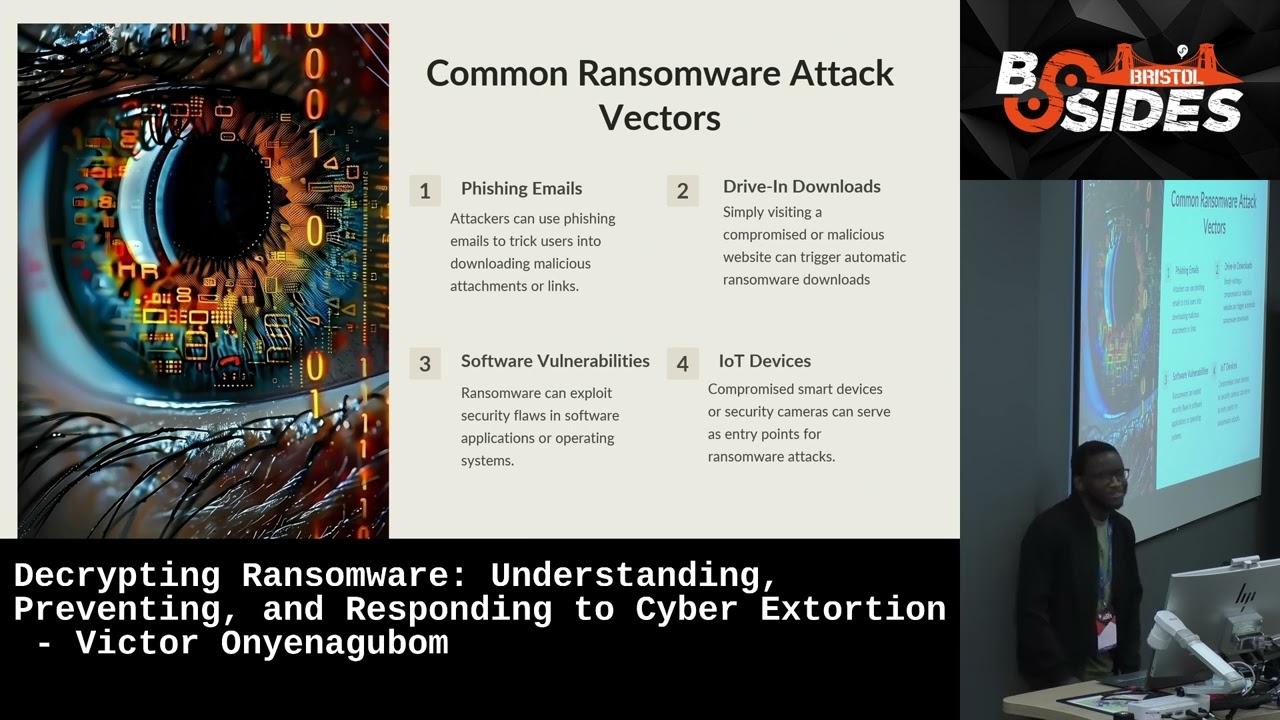
of slides so in understanding ransomware it's very important to understand how can you be vulnerable to a ransomware attack what are some common ransomware attack vectors by attack vectors we mean ch Channel through which you can actually get attacked what are the channels through which you can actually be vulnerable one of the most common ways you can actually be vulnerable from to a ransom attack would be fishing email which would be when somebody a malicious actor claims to be somebody they are not the most popular one sometimes is where you have like somebody claiming to be a CEO or someone you know maybe they've done some information gathering about you and they construct this email in
such a way that it's going to make so much sense to you and the email is going to be like very convincing and maybe you or your staff clicks a link and of course the malicious actor has control of your system and they start asking you for some amount of money we also have driving downloads driving downloads has to do with things around websites for instance um some websites are actually malicious I mean in 2013 I think there were couple of alleged reports around some developers who um who some there like a developer for with malicious sit and their systems are infected so there are certain websites you can actually visit that would make you um vulnerable
to attack so if you have like an organization you you have a company you know you're like a cyber security person you want to make sure that the site you visit with your system is actually um safe so that you don't become because some sit when you visit them probably like you know they get access to your systems from there then software vulnerabilities some companies outsourced not every company is able to like build the software they use in house um most people have to like Outsource and use vendor specific softwares so if for instance you using a particular software and this software has some vulnerabilities in them you know it makes you it makes you
vulnerable to an attack and sometimes there's nothing you can actually do about this because you are not like the um the builder of the software you're not the one who developed the software you're not like in charge of checking for patches for this software it's your vendor so definitely if your vendor is not like doing the right things around like checking for patches to see where this software he or she has deployed for you is vulnerable or weak then you can actually get hacked from there if a malicious actor gets to see this vulnerability so for this particular um attack Vector there's little or nothing you can actually do to protect yourself that is like probably beyond your control then
iot devices um everywhere today we have iot devices um from our smart cameras to Smart doors I mean when we were coming in today we some of us use the automatic doors right so you you come in and everything is smart even your fridges today are smart you know and your you have Smart thermostats that tell us like the temperat the you know everything you you have Smart stuff around you basically today and it can actually be a form of vulnerability too if it is not adequately um protected passworded encrypted okay because your iot devices are connected to your network right so that can actually be a means through which you'll be hacked um another attack
Vector I didn't mention here would be a social engineering in the social in the social engineering perspective in the social engineering perspective attack vectors we have things around dumpster diving for instance when you are dealing with sensitive documents in your organization and you don't properly shred them and you dispose them carelessly if a hacker goes to the be and gets access to those documents you can actually make yourself liable to an attack also um today from with covid and everything lots of remote work here today people are working in cafes in airports you know working remotely there's also the concept of shoulder sing right you are you are trying to work you know meet meet up the deadline
you taking a train from somewhere from one point from point A to point B and you're just trying to do stuff and you're not bothering to like check who's looking on my right or who's looking on my left and you're putting like a secure password you know and you don't know who's actually looking and seeing okay okay your password is 1 2 3 5 7 oh your dog name and stuff like that you know so that actually makes you vulnerable to this kind of attack so sometimes what makes you vulnerable to an attack might not just be the technical stuff you might have all technical stuffs you know in there but if you're careless as a
human being if you're not um careful you might actually um fall victim um so around somewhere we also look at the of a ransomware attack ransomware is kind of different from some other attacks because when a hacker when a r somewhere attacker attacks you he's attacking you because he needs money from you there are some there are some people who hack because of his social cost they want to send a message right they are hacking because they just want to hack they just some people do it for fun right they just want to play around some people are careless you know they over push their B they just want to hack and stuff they don't have any um thing they don't want
they don't really want to get anything from you they just want some people just want to let you know that um your system is vulnerable I want you to know that system Isner that's I'm hacking you and stuff but for ransom attackers they want money from you and most of the time they would ask for like payment in crypto Bitcoin and you know that Bitcoin payment is not like when you convert it to like your the normal currency is dollars or pounds it's not like small it's not like a small figure you know so if you fall victim to Ransom attack it's going to have a direct effect a direct impact on your Revenue so it's going to
have a direct cost because you'll be spending and romare would normally would normally Target companies they that can pay them huge amounts of money okay so they will be they'll be they'll be charging you based on how much you know that oh your annal turnover probably 10 billion pounds yeah so you're probably going to give us maybe2 billion pound to make us happy before we give you your files back and stuff like that right so if you fall to ROM attack you can actually to have direct cost downtime then downtime is also one of it um I spoke about some Ransom attacks that happened in 2024 about the hospital where in Chicago where the children
hospital now imagine being um imagine imagine where this kids want to like do maybe some operations or they want to take they want to get healthare you know and the system is down you know it's going to have an effect on patient experience right patient experience in healthare and for the COV attack that happened with the NHS you see it's going to impact people who want to like you know use the lab you know so it's going to have direct it's going to have the downtime is going to have a direct impact on your business process if you are for if you actually in a manufacturing organization in a big Manufacturing organization where you probably have a target of producing
about 200,000 units of whatever you're producing every day if you have a downtime for instance for 2 days that means you are shot by about 400,000 units right so it's going to have an the downtime is going to affect your business process then brand reputation obviously if you fall victim to a brand somewhere attack it's going to affect your brand it's going to affect your BR name um people be like uh that company so the first thing people are going to be able to associate with you whenever they he name of your company would be ah that company that fell victim to Ransom attack so so so time ago you know so it's going to it's going to take so
imagine the brand name you actually spent years trying to build build your brand name for a very long time and because of a little mistake you fall victim to this and you have to start all over again working on your PR to improve your image again so you see it's going to it's going to have like it's has a lot of like impact on you then potential lwuit and fin yes you can actually be fine you can actually gets um sued if for instance you are supposed to um provide a service to maybe some of your cents and they feel that okay maybe you couldn't meet up with when with when the the you guys are agreed and you're
trying to explain to them that oh because I had I had some issues with my system some people don't don't some some clients might not care you know they'll be like you've breached our contract and stuff like that and in terms of fines we'll be looking at legal and ethical issues later in this slide um you could be fin by the ICU for instance if you don't keep up to sorry if you don't keep up to the like reporting requirements you have so because of time I'll just looking at some quick ways we can actually prevent ransomware attacks so one of the ways would be for you to make sure you update your softwares regularly if you don't
produce if you don't develop your softwares inhouse you have to always check with your vendors to check that there are patches available your vendors most times are usually checking doing security patches to ensure that um to ensure that the vulnerabilities the vulnerabilities are taken care of so if you do not if you do not if you do not patch up your software then you are leaving yourself vulnerable to an attack encryption and passwords very important the sensitive files you have needs to be encrypted and password too um you should also this goes back the preventing around some where this particular section about encryption and passwords also goes back to um security awareness training in the sense that you
should your some of your staffs or your company you should encourage your staffs to change their password regularly shouldn't use a passw shouldn't be using one password for six months or a very long time your password should be um a specific character length and use some keywords um characters you know symbols and all that you know so there should be good um policies as regards um passwords for your sensitive details and employee log back up your data very important take out time to back up your data um so that if for instance if anything happens if you were to fall victim to a Cyber attack or a cyber incident you would be able to get back
quickly right so you want to make sure that you don't only back up your data you also test your backup your your restore process to Ure that um if I were to fall victim to a particular server attack now if I am trying to restore my data am I going to get a mirror an exact mirror of what I currently have okay so while backing up your data you also want to make sure that um your backup your restore process is also functional this has this ties in this ties in um a whole lot with your business continuity process right so that there's business continuity if there's any issue with your system then you have to be cautious
with emails and attachments some companies some some organizations what they do is to what they do is that after some after they do security awareness training around fishing you know they send random fishing they send like sample random fishing emails to their employees to check whether they actually they would actually fall you know then then employees that actually fall for the trick would have to do the training again so it's not just enough for you to for you to train your employees around fishing and actually think that oh everybody got it 100% so you need to test them regularly to ensure that your employees are actually cautious with emails and attachment so how would you prepare for
a ransomware incident sorry this this went so how would you prepare for ransom incident obviously in your maybe your security policy you would want to have you want to have a response plan and it's team you want to have a response plan as regards how would you respond to a cyber security incident when it actually happens in this case around somewhere incidents and in your in your response team you want to have a defined list of responsibilities rules and responsibilities as regards who is responsible for what accountability when something happens okay and who is going to be involved you know around depending you might have to involve certain big decisions to be taken you want sometimes
if you have a Cyber attack you want to manage information you know you want to know what do you want to say how do you say it you want to involve your public your the public relations team the Public Relation team you want to get your legal counsel involved to know how you're going to respond you know so that you don't you don't fall into lawsuit and things like that so your incident response plan and your and since around your incident response plan and the team you put together are like a very like very holistic process it's not just like a one size fit all it just depends on how how big your organization is then you also need to um look around
how you can limit um privileges in your team so Access Control this ties in well with access control um you should periodically audit and limit access toally senstive resources um check if this person whether people have people are supposed to um have access is it is it is it do they need to actually have access is it necessary for them to actually have access if it's not necessary then they shouldn't have access if somebody for instance moved from the engineering team to the accounting team do they really need to have certain access to some engineering resources you know so you need to periodically che check people's access to see um how how how well how well um how how
limited they are and you know whether they actually should have access then I've spoken about testing your backup processes to see whether it actually works just in case you fall um victim then secure networks um you want to also have like secure networks everything around your firewalls your intrustion detection system you know have a team in place you know segmenting your network have a villain have a v using a VPN everything you can actually do on the technical on the technical on the technical part to actually make sure intelligence everything you can actually do to see that to to make sure that um you don't actually fall for um a ransomware attack then when you actually fall to around
somewh attack how do you respond the first step would be for you not to panic and for you to actually um isolate you try to isolate the infected system so that in some instances where just a section of your network has been infected you probably want to like isolate the infected system so that it doesn't spread forensic analysis for the second one where you have to collect evidence you probably do a reverse engineering to see what actually happened gather information about the attacks logs time stamps and infection files most times when they around somewhere attack happens um some sometimes um because this because it's like a hostage situation where this Ransom actor is trying to get something
from you they would be willing to communicate with you so by communicating with them you can actually get some information as regards how they actually got into your system right so even if you are not willing to actually even though you know that you're not going to pay by actually um speaking with them trying to um talk to them you know you can actually get some information as regards you know how to conduct a foric analysis to know how they actually got access to your system so they can actually tell you some oh maybe we have access to this you can ask for proof okay show us proof that you have this and stuff like that so that might
actually help you to an extent to know how far and what could possibly have been you know the vulnerability that made you that made you fall victim you know and another thing would be for you to contact law enforcement if to report the attack to the authorities when you have a bridge you contact law enforcement and number four do not pay the ransom um because paying the ransom does not actually guarantee that um you are going to get your files back and of course it's giving more money you're actually funding criminal activities because um paying the ransom actually means that they have more money and more resources at disposal to get more sophisticated um software then the legal analytical
issues there are legal antical issues around data bries obviously um reporting requirements for gdpr for instance if usually I think um for gdpr when there's a data bridge that has impacted the personal data of your customers you as a data controller you have um the the um you have a you have an obligation to report to report to the Ico and of course inform your you have you you have to report this to the IC and let them know that the information commission officer that to let them know that you have actually been impacted by data breach and data bre notifications um if your if your if your customers if you handle personal data obviously you have to let your customers
know that you've suffered a data bridge and of course their personal data has been compromised you know so that they can actually take um maybe safety requirement safety procedures you know since their personal data has been breached so another eal issue would be should you pay or should you not pay you know so um like I said in the previous slide paying the ransom is you you are not still sure whether it's going to restore access to your files and um it's also funds criminal activity then lastly so what what what would be like the future of ROM attacks um the future would be some part of fure would be things around ROM the service which is also like a
thing now where um certain certain actors provide like sophisticated um systems for people who are not that technically adapt to actually use so um people who conduct somewhere these days not really have don't you probably do not need to have so much so much technical skill to actually conduct Ransom with the ransom where as a Serv these actors will provide you like a software and you can actually you know conduct people can actually conduct this on their own so this is Ransom as a service probably how it works then there's increase sophistication where your files can be encrypted with a double encryption with a combination of like the AES and the RSA encryption or they can just encrypt like a double
encryption then we also have a fileless something called a fileless um ransomware attack is a type of ransomware that occurs in memory rather than where you can actually visibly see it on your hard drive so it's actually hard to detect or eradicate since it operates at the memory level then um there's also the AI power that tax these days ROM actors could actually do like a data analysis to know which clients are going to pay more they can do like an analysis to see um how do I identify high value targets how do I get high value targets and things like that who are who who is likely to pay me around some based on
the analys based on this analysis if I do like um they will do like maybe probably machine learning algorithm and things like that and see okay from this analysis this is who we are going to Target based on this analysis and with things around AI deep fakes and you know so many AI Technologies take my time is 5 minutes 5 minutes right with things are I power attacks today we have um automated automated fishing you know things are automated fishing and deep fakes you know that can actually make things seem like they are what they are when they are not you know so um these are some these are some ways that um R somewh attacks are expected to evolve in
the coming future and I really hope that if you if you're just like um trying to like get to know more about ROM attacks like this talk probably gives you like a bit more overview of uh what around some attack involves thank you very
much question yeah yeah thank you for your talk I was wondering as someone who's current s for I'm not iners yet what would be the best place to I guess learn how to verse Eng malware and I guess understand how malare works come again where do I learn what do I learn about M analysis and where do I how do I learn how to reverse engineer how now to reverse engineer malware um there are lots of resources online you know there are lots of resources around malware attacks there are lots of ethical hacking courses available online there are lots on YouTube there's also CCM security you know there are so many resources online if you want to learn things around
malware reverse engineering you know eal haing there are so many resources online for that okay yeah on your previous slide you has something called fireless randomware yeah which runs in the memory and has no tracing Hardware how does that work I haven't I just across thator yeah yeah yeah so this this is um this is because for Fess ransomware for instance now if it's running on memory you know if you fall victim to a particular ROM attack for instance now you probably want to do like go to your file explorer and you just check okay um this is on my file is on my hard drive I can actually find it somewhere but if this is running like on the memory level
on like the operating system level because in operating system you have like different levels in the system like the Kel and all that you know so if this is running like on the memory level it might it would take you would probably de it but you might not be able to deck it on time for you to actually give like an adequate like response or actually stop the system that's why sometimes it actually helps to like unplug everything before it actually before it spread but those decisions would be based on what the incident response team who is responsible in incident Response Team um would know but in an incident resport team there would be people there will be
specialist you know who would also be familiar with things around fireless um fireless from some ways yeah yeah who do I go to First yeah yeah yeah okay thank you for your speech first of all do we have any uh statistics that how percentage of businesses what percentage actually pay the on some okay what peration businesses try to analysis okay um okay so I don't have the exact figures at the moment but um I think earlier this week I think the national the National Crime agency spoke about the fact that ransomware attacks are like the most um serious cyber attacks that are facing the UK and the critical infrastructures in the UK so um ransomware attack is like a major threat
you know in the UK you know the exact numbers that affect I don't have specifics but there were there were actually research on that Artic there were numbers put out there by I think a research or something but I don't have the exact numbers but yeah around some attack like the major um attack like that the government actually identified that f is like physical Network infrastructure like things around your water your gas and things like that you know yeah so it's like a major major you know problem so how effective are like platforms like virus portal or any run how because somewhere has many variants many many divers we have like protection for all virus or yeah yeah um I think there
are lot of organization like that's why um things around pentesting pentesting this is where pentesting comes in helpful I mean I was speaking to was it mly I was speaking to today you know her company valid those things around they do things around helping you check they they kind of specialize around helping you check how vulnerable you might be to IR somewhere attack you know so yeah there are tools to help you check like how vulnerable you might be if you have a ransomware attack you know yeah I have to cut you off there very sorry if has any more questions feel please feel free to swamp this poor man at the end all right but yes thank you
very much thank you very much