Reimagining The Intelligence Deliverables Using Structured Threat Content by Gert-Jan Bruggink
Show transcript [en]
appreciate that um my name is you can tell from my accent I'm not from around here I'm actually from the Netherlands uh Eindhoven to be precise and I'm here today to talk a bit about my research in structure threat content what I'd like to call stretch your third content and I'm hoping to share some stories with you today um it's a pleasure and I'd like to actually start with a small story and and that story uh is a bit into um why I got into this and um I'm not sure if you if any of you is familiar with that the sensation of receiving a report in your email box or website or whatever and then the day after you
receive another one and another one and another one and another one and it keeps going it keeps going so one of the things uh I found personally very annoying is exactly that you know how can we research that how we can do that more efficiently um turns out that is not so easy to change the way how we do things in the industry and you know um probably some of you are guilty of the same thing even I am guilty on the same thing but um I think this to me this was a way of looking so we're getting an infinite amount of uh reports every day but you know how do we I can't
I can't read up with that and and chat GPT isn't the answer for everything so how do we deal with that right so that's when I thought you know we have to look differently at the way how we provide these reports and one of the research thing I did on that was actually how we format the liberal how we structure our research and that is what I'll talk about today and I'll start with the end and I'd like to uh uh already apologize I'm Dutch so probably a bit blunt a bit direct um and one thing I'd like to highlight is my uh opinion of the of our current cyber security industry and I think that
we as an industry are extremely poor at storytelling and what I mean by storytelling is not just telling a story like sitting behind the campfire but actually making sure that the audience is understanding what we are talking about that our story is applicable to the person we are talking about that the security alert we saw and we're trying to communicate to a certain stakeholder that that is actually also the right way we tell that story and the problem of that is is that you then get a disconnect between the let's say client and the part the person or entity or company giving you a certain service to it so that it creates a bit of inherent disconnect between what the
ask is and what the question is what the ask is from the clients and what people are offering to actually answer that question and what I found over the over the last uh three years is because of a new I'll talk a bit more on that in a second what I found is that if you try to break up this kind of content then all of a sudden you know you can find a way to make it more efficient to make it to create more engagement um is that easy no certainly not but I'll share I'll talk you through my research at least today where I am and still also what are some of the points
that are open and some of the some of the pointers where you as an audience or as individuals can actually look at as well foreign my background is a bit broad um mostly specifically in cyber threat intelligence uh risk management I've spent a long time at a advisory company before that I was a security engineer I'm always interested in a little bit of tinkering looking at how things work looking at how we can decompose certain problems big problems into smaller problems so we can solve them more efficiently um and next to that I'm also very proficient at organizing that in a security program or a program to actually solve that and I've mostly been doing that in the FSI sector high tech
and Manufacturing as you can tell I'm a I'm a big Lego Aficionado you probably see some hints here and there um I like to call myself a cyber threat cartographer and everything I do I share in these conferences but also on LinkedIn Twitter and GitHub so anything I do you can basically find it there also hit me up there if you have any questions which we cannot answer maybe today right and I'd like to start with something um which is what I'd like to call threat informed risk management so we need to get the problem statement correct right and what I found over the years is that the uh what we do in our industry we
focus on risk right risk is recognizable risk is something that could potentially happen and when it happens this has a certain impact but when you're doing that based on threat which is also a known topic right it becomes a bit more difficult it becomes more nuanced but there are certain companies probably with all of you where actually knowing this kind of nuances will be the difference between let's say a small problem and bankruptcy if you don't prepare for that but then this is actually a balance a balance between what is a direct threat what is an immediate threat for you and that is actually a sliding scale sometimes because if you have seen for example new a Blog from Microsoft being
published on ttps on killnet or whatever then all of a sudden you have to think like is this a direct threat to us is this something we need to be concerned about does this does this hamper our operational priorities right because we still have a backlog of 2 000 tickets which we need to sort through what is more important right and you kind of see some all of the time you see the the actual the thread aspect falling off now another thing which I found pretty useful but obviously I'm biased because this is my profession but it's the understanding of Concepts like opportunity capability and intent that can help you drive this threat angle more specifically and also structuring
and standardizing but that those are two aspects that are on the opposite side of that scale and I find that um uh pretty interesting to keep that balance but just know that this is really hard um and I also like to a bit of address the the Lego elephant in the room and before I do that does anyone know what this thing is go on go on shout out come exactly do we agree with that doesn't work well I I think it works really well so this is called the the Lego separator and it's a a genius level thing from Lego they put it in each box and they just want to make sure that you can you
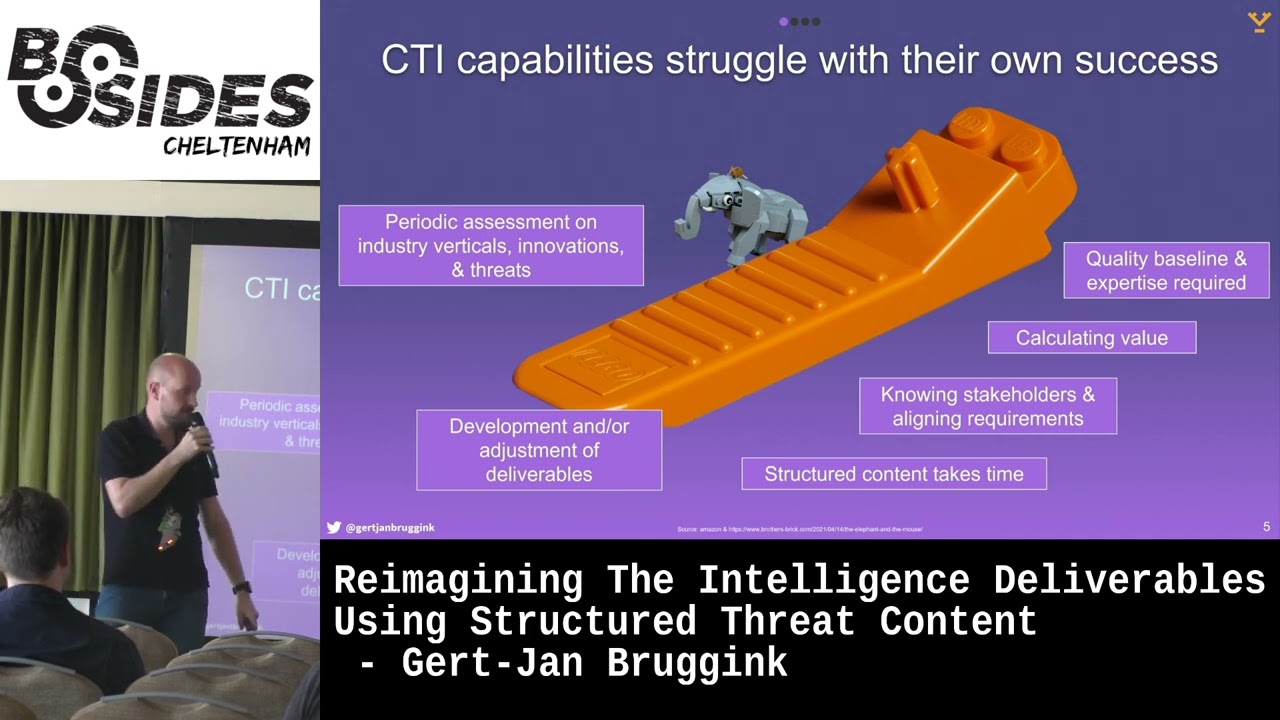
know pry the brakes open when uh when when when they're stuck together exactly so but but the thing is when I first got that I was like what is this how can I actually leverage it and that was actually the same question I always get when I'm building CTI teams so what is this what did they do how they add value I have no idea what this is um and what I found and that is actually the elephant in in I think in the CTI room is that you know these teams then focus on a certain thing because they all of a sudden they're pretty good they're prying stuff or they're pretty good at doing assessments on what is
happening in an industry or reporting on that um but then again you know then all of a sudden or they're really good at knowing the people they report to in the organization but they're really good at that one thing and that balance they become so good at it that they unfortunately then are not able to do everything else and have to select a certain thing and that actually impacts um so their own success is actually impacting them the quality Baseline they hold but also the uh their ability to know people to report to stakeholders and also to use structured content now as I mentioned in the beginning there's this problem I I took on head-on and I'd
like to decompose it a bit uh on how I explain that to my clients but also in general you know if a friend calls me and this is how I'll explain it and it goes a bit like this so obviously when we do whatever we do when we talk about any some form of threats or how we manage that I first like to make clear like what is what is what is your language basically how do you communicate in your organization how do you communicate about risk and how do you actually explain some of the problems you have how do you explain that within your organization this may sound extremely trivial um this this calculation and there are
actually many but it is so fundamental and not a lot of people are actually doing it or at least discussing it and I I encourage all of you to actually do this and at least have a my key taker also is that there is no one thing that is correct or which I approve the only thing I'm saying is that you have to have an explicit conversation about this also and that's for me obviously relevant the threat axes how that then bolts into it because if you're just doing risk is impact times likelihood then where does the threat lies into and if you if you become a more if you become more complex in your um in your
capability in your security team then all of a sudden you have to have more thought on how this actually plays out we'll get to that in a second [Music] so now diving into the thread aspect so if we have um if we have threat in the context of risk I actually perceive it as threat is just simply some some actor who has a capability intent to exploit an opportunity at a given company risk reasons outside in and threat reasons inside out you know if we look at it that simple then you know then then we can actually start modeling this out and continue with that and one of the things I now get into is
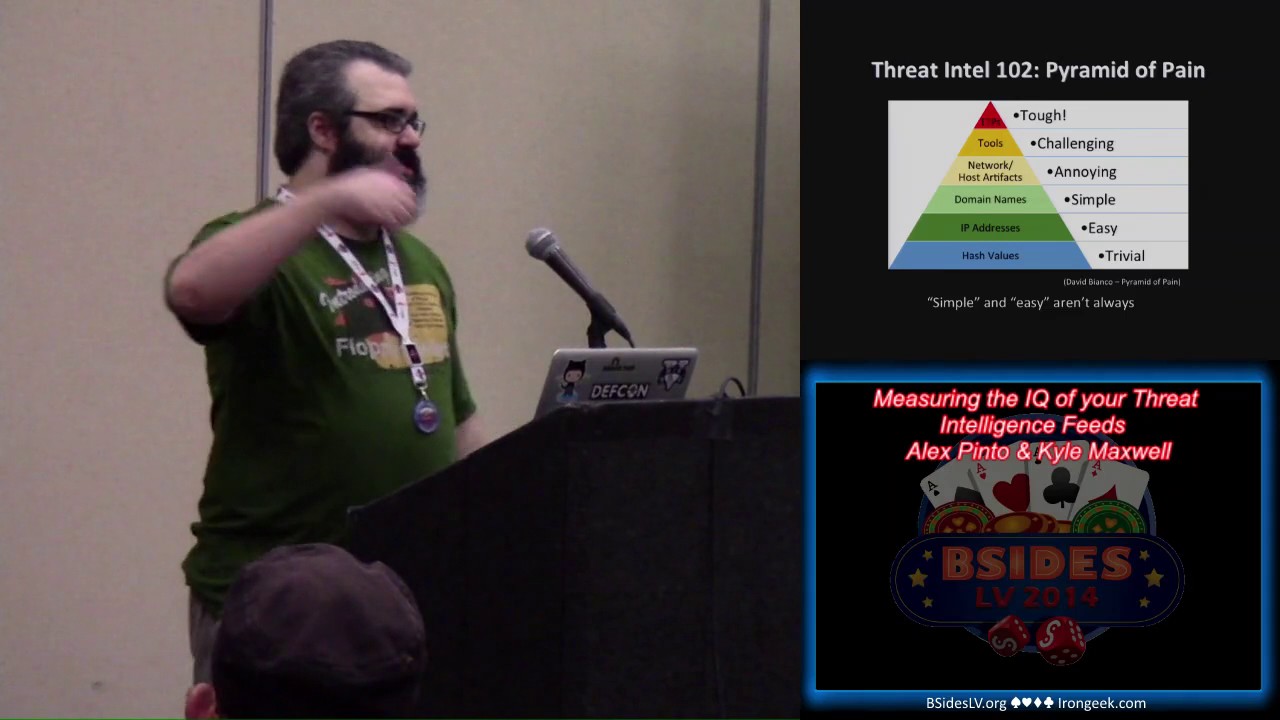
if we as this thing called the Pyramid of pin which actually breaks down several really practical nice and tangible stuff into um things we can actually track and detect and monitor but the reality is is when you talk about that's good for capability but you know intent is super hard right if you're not an intelligence agency then all of a sudden it's really difficult as a commercial company to have understanding of intent for example but this is where you actually see the disconnect in most teams happening where they they are failing to report uh correctly from the bottom upwards to where you for example see like this is the this is the things we see in the
network these are the techniques we used and then all of a sudden goes dark but the reality is is that you can go even further and or abstract on on on that using for example campaigns activity groups attributed groups um and this is where you actually see the the whole structured content arising and I'm not sure about you folks but I was completely lost in the weeds when I first looked into this there's so many stuff there and I just decided okay let's let's make this into a simple model or or a few and just make it explainable um I'm not going to go into each and every one of these aspects that's just beyond the point what I'd like you to at
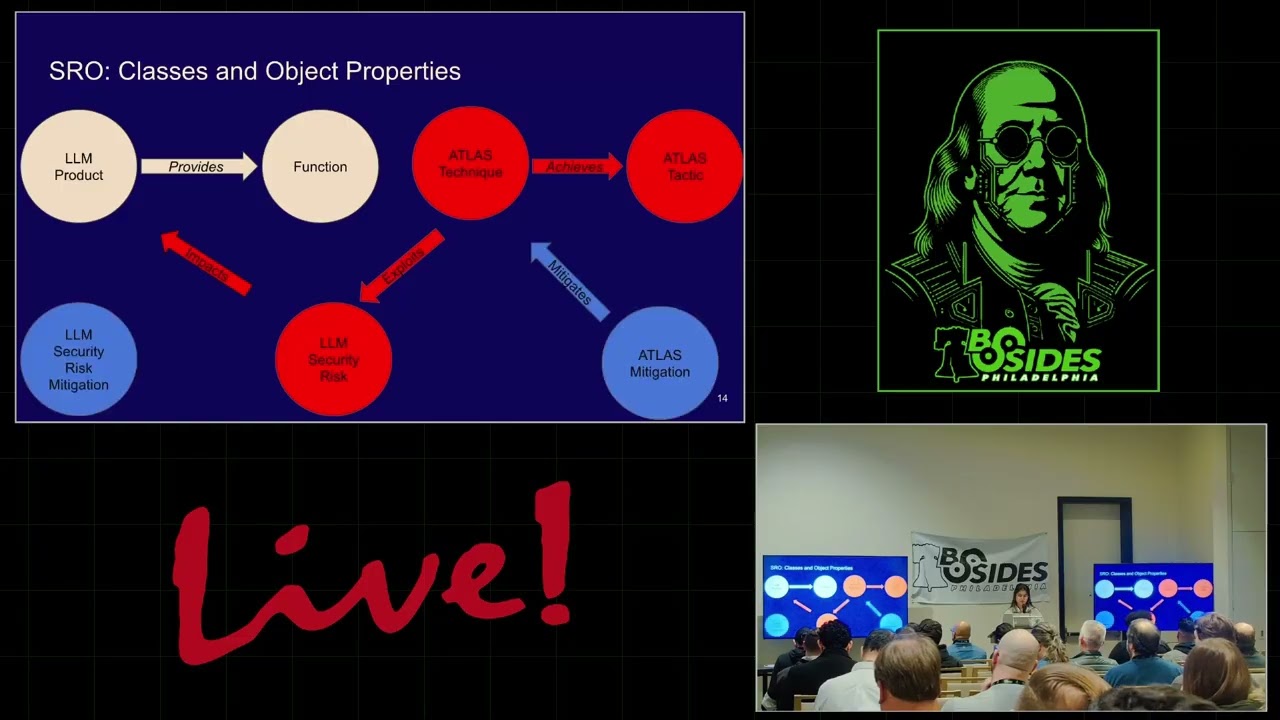
least remember is that structured content as it stands per uh what is it now five main three three June sorry um you have Frameworks they basically use schemas or models and they encode everything in machine readable formats right so at a good example of that is for example miter attack well known in the industry they basically uh model everything in sticks and they encode everything in Json right so if you follow that logic then you can actually pick and choose what you need for your team but also if you use one over the other you can already think like Okay so this format is actually reporting into something so how does that then work right
if we um now now if you have worked with the CTI team or you're a part of a CTI team then you have probably received not this book right but that actually the thing next to it which is an example we made in uh with one of my friends from rackfast which is a example report of how we deliver a briefing to a client this could be an email this could be a PDF document you know sick but the idea is that I think this is pretty good example of how you can actually do that but still that is not connecting to structured thread content right so if I basically decompose that and look at how
I can translate an intelligence deliverable to Sticks 2.1 which is one of the I think it was one of the the formats the models um then I can actually only copy like one thing practical and actionable into into structured thread content anything qualitative is not doable right now it is with nuances but the issue is is that it is hard and especially if you take it one step further because people want to have more more and more they just they don't want to see you receive ioc they want to see you know what is the entire Playbook we have in front of that or backwards of that and that requires way more understanding so this is for example a a
view of some research from a friend of mine and we are working together on something called cacao playbooks and I'll get uh this is something I'll get back to later today but they basically have some encode they found a new way to encode everything to tie it diff to tie it better to different stakeholders but if you want to so this looks nice right but if you want to compile that into a into a jsons file it looks like this that's absolutely horrible you know so all the arrows and yeah that is uh obviously terrible but I'm trying to illustrate that it is really hard even to this day to to go from qualitative contents to structure
threat content that that journey is happening but it's it's not very efficient so where does that leave us Lego of course but I think we have to look back and say what were we doing already pretty well from the last four to five thousand years which is storytelling right you know we used to do that all the time when we didn't have our telephones iPhones whatever um and I think to this day if I if I look at a a piece of paper or a deliverable I get in an email I'd like to think of that like what is what does it consist of can we actually break it down can we decompose it and can we look
at it as a a pile of blocks instead of uh uh and yet another email so what I did is um I did some research on that on how I can model that out and I basically shared that with the community and one of the the the philosophies I have behind that is this little thing you know this is how my intelligence delivers look like not necessarily in this format because otherwise people will laugh at me but the idea is you know exactly that this is about a penguin you know exactly that this is about that this consists of different uh pieces and you know exactly what the order is that we have to use it
and have to create it so that means depending on the stakehold that it looks at this they will all look at different formats and they will know exactly what they will need for what aspect so um practically speaking what I did is create a framework like structure I interlinked that with different models not just choosing one for example miter attack I chose multiple ones and basically create a code 5 version which I then put in front of Academia and told them like whatever you're doing it doesn't work I don't want to create yet another one I'd like to make yours better so how can we improve it and that is actually working pretty well and I One scenario is actually open
sourced so you can use it you can use the format right now just grab it online and start playing around with it and this format actually allows me to dive into a bit more tagging into functions that I actually see but it also ties me into actor playbooks and specific things that are associated with certain groups I can tag and annotate and maintain that as you can see on the left this is obviously a uh the part of the penguin but the interesting bit is now you know exactly what what is our current understanding of that that just takes time but actually annotating that in a good structured fashion that is useful and a second uh more important thing
about this approach is also about you know talking about the walkthrough of a given scenario too much in our industry we spend a lot of time on talking about that new hype thing that actually has happened right I mean I was kind of surprised this morning on the second talk third talk on bad USB right I mean it's uh 2023 I'm still talking about USB drives being an issue even you know we've been talking about this for for what how long long um but my point with this statement is um we need to have a better discussion on where we want to defend you know there's a sequence are we actually defending at step eight or are we
defending at step four or step three or even and selecting a certain feature and that discussion never happens explicitly thank you now if you have in in my example so the scenario I'm not saying by the way that my Approach is the the Silver Bullet I'm just saying that this is approach I found extremely useful right and it works with you know the people I actually talk to and and practitioners who actually use this and give me feedback on it and one of the things you can actually do if you use that that specific format of mine is or loaded into something uh an open source tool called obsidian which is just a note keeping app and you can just load it in
and it automatically uses all the hashtags and tagging and then you can create these beautiful visuals like you see here automatically so if you start working on that and you have out of the box visualization tagging so completely for free amazing now another thing is the um the living of the land CTI and um most of you probably uh in your uh in your business life you have seen maybe Ira or something a tagging system or whatever or an asset management system and some of the things I actually always what always surprises me is that people are a bit unwilling to explore existing Solutions and rather buy a new one because that works right so what you see here is just something
called era Insight which is a asset management tool within era and if you basically repurpose some of the of the tagging you know you just name it a bit differently then all of a sudden you have a a tagging mechanism that allows you to see different things that have happened in the news you can actually annotate that to a certain group to a certain capability to a certain actor then you can link that to an existing asset and identify if your risk management teams actually work with that to a certain control and that is a bit you know corporate blah blah but the reality is that this is really hard and the point I'm trying
to make here is that you can use your existing tooling a lot um to uh to work with this now there's two final things I want to set you off with and I do need to wrap up but I think there's two things uh one of them is what is next on structure third content I showed you today a means on how you can actually decompose some of your deliverables how to look at that differently how you can use that um well one of the things I'm I'm still very curious about is what is the what will be the future encoding where my research will flow into I'm hoping that this will be the format called cacao
which is a an offensive encoding mechanism how we can encode attacks but also a way on how we can encode the defensive playbooks for example detections the plus side is we need a lot of data and information the and that is also a downside by the way and um I think another issue we see here is that we as humans we are pretty unable to actually comprehend more than just two dimensional images and for those of you who are a bit as this is the Back to the Future thing um I'm not sure if you guys there's no Minority Report when where you add the visuals where you could pop it up and do everything with your hands and stuff
like that really beautiful and go through the data quite efficiently we are not there yet but I think when we start structuring our content way more then we can use existing tools like machine learning models more efficiently to get through this kind of thing but it does require this kind of encoding now um final Lessons Learned start codifying this stuff today in your organization on Monday you can do that as you take some of the stuff you've seen today make sure that you align it with your stakeholder priorities some of the people I've talked to you wouldn't surprise me how many times they are still reluctant to talk with the people they report to because we know what they want right no
they don't so did you actually ask it see show me the the notes for example um but then then if they report into era for example then you can actually leverage that and make them their life successful they're reporting structure successful and um to that extent I also encourage you to reimagine your own approach to writing those emails and figuring out a new way I'm doing it through scenarios I'm not sure if that is the right way but that does allow me to then move into a new new areas where I can load this data into a large language model I can load it into an Excel file I can load it into whatever my audience needs
depending on that situation my friends that is what I have for you today uh I'll leave it at that thank you
can we still do questions all right any questions any takers go ahead sir
yeah so did everyone catch that question cool um it's about not just telling a story about cyber security in general risk management but also what is the added value of threat intelligence specifically I get this question often and as I as I mentioned with the Lego separator you know people normally are like I don't know what to do with this right but what I also found is that once they have seen a new way on how to connect risk to threat and it starts with the equation um then they can't do without so one of the the the Practical things I saw in in uh with my own clients is if we ta if we
find their calculation uh because that is usually what dick states to security investment right and uh what we found is if we tie our content our reports we report on a daily basis into their thing they call opportunity then we are actually showing instantly how there is daily risk assessments are can be done more efficiently that is just one way and the others uh we should talk after this session thank you any other questions no thank you folks