Demystifying APT42 Cyberoperations - Adrian Sanchez Hernandez & Asli Koksal
Show transcript [en]
welcome everyone today we are going to uh with my colleague Adrian we are going to present you about the ap42 operations so introducing us I'm a senior threat researcher in uh in SAR spash team of mandant which is now part of Google Cloud Google threat intelligence and I'm responsible for tracking and hunting uh Middle Eastern uh state sponsored actors such as ap42 that we are going to present today my name is Al Hernandez and I a senior analyst in advanced practices which is part of Google FR intelligence and my main role is to uh to provide intelligence to our managed uh defense services and IR Consultants providing them with threat analysis uh and attribution and on the side uh one of
the things I like the most is to uh research um um research dprk on North Korea um PR actors so today we are going to in the presentation we will start about mentioning or um introducing ap42 uh what is ap42 and who they are actually and now we going to do um we are going to explain their uh operations and then we will conclude our presentation with Outlook and implic ations so let's start with who and what is ap42 ap42 is not just bun for group of hackers uh it is a state sponsored cyber Espionage group uh believed to be associated with Iran directly uh getting commands and directives from Iranian government and uh their uh primary goal
is uh gather intelligence conduct surveillance and steal sensitive data that's in a way that will benefit uh Iran and during these operations they generally use the ttps uh mostly relying on spare fishing and social social engineering but we also have cases that they um use custom malware or they exploited the vulnerabilities and in these operations their primary targets are uh entities such as Government T tanks NOS U media civil society and um education uh entities also ap42 aligns with Iranian geopolitical and strategic interests so uh they focus on the entities uh in the Middle East or in a broader uh world that has the relationships in conflict with Iran they also Target the individuals such as journalists or Iranian diaspora
that has uh that they have influential positions um as I said such journalists and Iranian diaspora and when we look at the victimology map we see as I said they mostly target Middle East such as Lebanon Israel or United Arab Emirates but they also Target um other countries that has somehow conflict with Iran uh ab42 also really um fast they have quick reactions to the geopolitical events such as like M amen protests or covid-19 or Iranian elections or Israel Hamas War so I will explain them later on in their operations but uh they have these quick reactions and they use this um events in a way that they will build the trust with the target uh not really directly
uh targeting uh these uh entities but they use this events uh to conduct lure to build a trust with the target to have a broader understanding of uh why ap42 does what it does I wanted to show you what is our assessment of uh the irtc Cyber program or corent assessment is as ap42 uh Acts or operates in behalf of of the irtc io that is the sub branch of the irtc that stands for the Iranian revolutionary guard Corps this is a a military branch or a military entity that is is part of the Iranian armed forces the io stands uh for intelligence organization what does it mean what it means is that uh based on on the goals
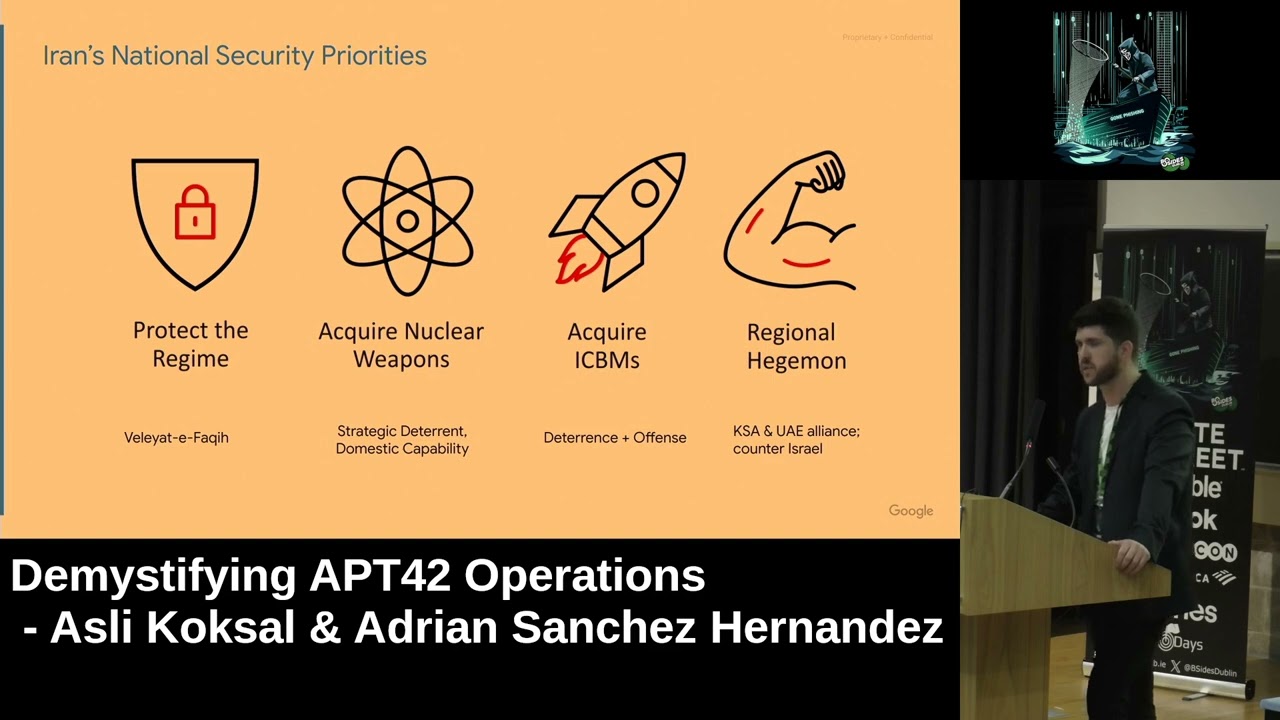
missions and targeting uh the orur assessment led us to conclude that um ab42 likely operates in behalf of the rcio because the they are constantly targeting those that um are in position either of documents or intelligence or information of values and and thus collection is the main purpose of ab42 however the RTC have uh multiple units and they have a completely different missions to explain as well why uh ap42 uh targets uh in the way does we need to understand what matters to Iran uh from a regim standpoint uh the the primary or most important priority for Iran is to protect the regime Iranian uh Iran can be uh described as an ideology with borders and as
does it is very important uh for Iran to protect its domestic policy and that involves uh targeting those that are contrary contrary to their regime within Iran and outside Iran in the other hand uh one of the uh most important goals or objectives of Iran is to project power in the region to become a regional hedge what I mean by that is that uh to Iran sa safeguarding its Integrity as a regime it's not is is is really really important but at the same time um it's fundamental for the Iranian regime and its ideology to uh to protect this power and influence and to uh to tackle all the the the differences and problems that they have with other regions in the
Middle East they have been obviously targeting the the primary target is Israel so um projecting power in the region against Israel or the the alliance they have with the United States it's uh one of its main objectives but it's not the only one uh we OB served Iranian operations targeting other countries in the Gulf such as uh Qatar United Emirates and the kingdom Saudi Arabia which are commonly targets of Iran C operations not only by f42 but other Iranian clusters as well so let's start talking about their operations as I said ap42 really like mostly relies on their social engineering or spare fishing operations to steal uh the targets uh credentials um so active from 2019 until
today today we identified at least three clusters of infrastructure used by pt42 and in these operations they were targeting mostly individuals uh perceived as a threat to the Iranian regime they were not they they also we also have cases that they are targeting the entities but mostly in these operations with credential harvesting they were targeting the uh individuals both their uh organizational emails and also uh personal emails and um these targets con consists of researchers journalists NGO leaders and human human rights rights activists um in these operations they use generally similar TTP but they have slightly they use slightly varied domains and masquerading patterns that's why we divided them into three clusters to understand um and track more easily
but the ttps they're using in all these operations even in the in this groups were uh slightly s mostly similar so such as in the step one they generally tries to build build the trust with the with the targets so they choose the target uh as I said in previous they like to use these geopolitical events or um they also use lures that are that is interesting to the selected Target and then they try to communicate they start they try to build trust by um communicating with legit uh doc sending legit documents lures that is interesting that will be interesting to the uh Target and in the step two when they build the trust they move on uh
they send a link um to the to the Target um that is in either of these three clusters a domain a fake domain that's M grading at either of these three clusters and that will be redirect redirected or hosting uh a fake Google Yahoo or Microsoft login page to harvest the target CR credentials so I will mention about these three clusters three groups and in the first group uh ap42 is using uh domains Mass grading as news outlets or Nos and you'll see here on the table that they are using uh known news outlets not only from Middle East but also from us and UK and they either use a different uh TLD uh of the leged
domain or they use the typos SED domain like in the first one you will see that there exist an extra l in the um sorry for my pronunciation but I think it's aat so they use an extra L uh to um to deceive the deceive the Target and here you'll see on this um tweet from Jerusalem Post um warning people about about to spare fishing s on behalf of her um saying that uh the the ap42 is targeting people by using jos. press where the legit domain for Jerusalem Post is jpost.com so I mentioned about ap42 they generally don't go and send the spare fishing email but they try to build the trust with the target before
like they do all these operations so I will mention this we will see more um detailed informations in the uh Group B where uh they use uh different domains than the new Outlets so in um February 2024 we identified an uh a a domain interview. site um redirecting to Dropbox and in this Dropbox folder uh it was there was a lure file named questioner PDF and it was this questioner PDF was shared by Jam N uh sorry again for my pronunciation um possibly referring an Iranian filmmaker and human's right activist and now when we go for this file questioner PDF we identify we we understand that uh the PDF title is women's struggles and protests and the content of this file is
related with wom's rights and it's created by looking at the metadata of the document it's is created by uh David web possibly referring to Fox NS contributor so you'll see here that this and this do document doesn't have any malicious stuff so it's a completely clean document and you will see here how AP pt42 um likes to use uh or prefers to use legit personas um their names to build to make a legitimate to to make this operation or activity legitimate and also all these um activity was um around in about women's rights so with the content or with the Persona the leged Persona that they're using is all related with women's rights so what we expect here we
expect ap42 targeting here an a women's rights activist actually and later on when we see this is our this is their step two we see the same domain sending um or redirecting to uh Edmond's table right top and it was this domain was hosting uh serving a page a fake Google login page it's reducted here you cannot see but there uh in the in the Gmail it was actually uh the hardcoded name of the women's right activist so we were seeing what we were expecting from this operation and we see more other domains that is um doing the same or performing performing the same activity in 20 23 uh March I think and then March 2024 again
similar or same activity again with a hardcoded values of the target fake Google login pages and uh one was targeting a freelance journalist the other one was targeting a a n editor working in a Persian language U NS television channel another activity again similar um that will show how um ap42 actually using this geopolitical events so uh in March 2024 we identified a domain reconsider. site again redirecting to Dropbox and hosting a file named uh the secrets of Gaza tunnels both in Hebrew and also in English so what we expect here basically this thing is uh possibly related to Israel trying to leverage the uh Israel Hamas war and I'm possibly targeting not only Hebrew speaking or not not Israel
or Hebrew speaking um targets but also targeting uh non-hebrew speaking uh targets uh by using the U name of the document B in Hebrew and English and this is interesting this is really interesting than the other example because here we see the same domain Recons that side in the step to um directing to L Check le buz which is uh ap42 uh C2 but on here it's different it's not only targeting the Google login uh Google credentials of the targets but also they targeting yaho and uh Microsoft credentials too and then the interesting part here is um each and every uh fake page was hosting was having this um hard qued values of the target usernames and it was identified
by um all the uis so this last check leave bus has different and um specific uh URI values to um send the send the target to either uh Google login page or Yahoo login page or Microsoft login page in this group b we also identify ap42 using Google sites which is a web page creation tool and in this Google sites by using Google sites they uh create a fake Google meet uh in invite invitation page so by using this um Google meet fake invitation uh they try to um redirect to ap42 C2 uh together the credential and in this example we see that a fake Google meet page um allegedly invited by a fake persona U
Mona Lori uh and when we search for this mon Mona Lori Persona we identify that uh the person the Persona is humans rights activist and a researcher and actually we uh we think it's possibly a fake personal C by ap42 because uh further researching the name and also the picture we couldn't identify a leged person person and also later on we identify that this um profile was blocked uh as I said the once the target clicks on start verification the target will be redirected to redirected to kv. toop uh domain and in the previous slides if you remember that kv. toop domain was hosting actually a fake Google login page and in the group C uh we we see we
identify that ap42 is uh using domains MK raing as Nos and here you can see in the uh slide like Washington Institute they're using Washington Institute which is a US based think tank but instead of the letter i they prefer to use letter L so it is actually Washington institute.org and then we identify we can pivote on more domains uh in the server that's hosting uh Washington institute.org we identify more domains that is posing as M or demon service and from there we can jump to in this same group uh we can jump to another subcluster that is looking like uh the domains masc creating as mailer demon uh so in the first example and it
will show you that actually how ap42 works really in a targeted manner because in the first URL you can see that uh there are you cannot actually see because reducted but they are targeting a a nuclear engineering professor in a major Israeli University by having hardcoded URI values in the URLs um they use the university acronym in the URI and also the username of the specific professor in the URI to in the account ID parameter and in the second example they use mailer demon. us um that domain is registered by using Israeli location data and using an Israeli persona wellknown persona and in the URL you will see uh a file containing a name Henry Kissinger
which is a um us geopolitical figure so they're also using lures with legit personas really targeting attacks and try to BU again all this activities around like trying to build a trust build the trust between the targets so they try to use again uh personal legit personas or legit uh registration information another subclass of this group where ap42 uh uses domain that are masquerading as URL shortening services and in this subcluster they also uh use um lead writing so in the first one uh possibly it's the it's Tamir Paro which is an Israeli um the head of former head of Israeli mosad so probably they were encoding Tamir Paro in lead writing and in the second URL you'll see uh they
were encoding Jo payer and with that Jo payer in a similar way we can pivote to another domain um in different domain where they possibly using a l lure with ICT 2023 which is possibly uh International Counter Intelligence Summit that was held in 2023 in Israel one of the most interesting operations that we have seen are uh ap42 uh characteristics on ttps when they are breaching CL environments we have seen in the initial phase which we can name as cren harvesting and bypass a lot of overlaps with activity that as they just mentioned they will rely a lot on thake personas or they will impersonate real people that have a certain degree of Authority or
competence in a relevant field that is compatible or aligned with the with the Target and after building a relationship which normally takes days uh it's it's a really well crafted social engineer at some point uh the ab42 actors are going to drop a link that redirects normally once but not only once sometimes it's even more uh to uh a login page uh in order to capture AC directory or domain credentials to access the network but they don't only capture the username and the password they will also capture the multiactor authentication token and then once they have these credentials uh the infiltration and data collection stage is quite fast the attackers jump into the network using uh
the connecting to the to the main gateway or they will connect relying on R desktop and after uh launching uh what I would call A A Ste reconnaissance phase they will gather and look for the information that they looking for and they will exfiltrated as soon as they can the access as I mentioned before is very similar they will uh impersonate again sometimes creating fig personas but sometimes they will use a relevant figure within the think tanks or the Academia uh someone that is related to uh International relationships or or that has relevancy in the geopolitical sphere and they will establish a relationship one of the most interesting things I would say is that we have seen
ap42 targeting first uh the personal email address of the Target and then shifting that conversation and relationship to the uh corporate or Enterprise Email continue with the conversation they will this social engineering uh stage is normally really well crafted and they will not share malicious links or files or anything of that sort they are going to build this relationship build made of uh uh exchanging information that is related normally to conferences talks topics that are either related to the very specific Target and its interest or to the organization uh and in terms of files uh we have Serv ap42 at least in two cases uh dropping links to attacker control SharePoint uh containing uh files that
are related to again these topics but these files tend to be completely benign these are made uh by the third actor just to to build this relationship and to gain credibility uh just to know these files are legit we are just uh blocking or uh not showing the the file names because they're are Rel to the Vic in terms of ttps for this access we have serve repeatedly t they will replace characters they will uh hide they will really mimic how the the original side Works um in some cases they might change the the the top level domain or or tldd um after dropping the the malicious think that will redirect this this victim towards a login panel that could
be either social social media with single sign on as I see in the picture or uh to all file logins or even to multi multiactor authentication sites uh the is going to gain control of these credentials in this picture you can see that we were able to find a fake LinkedIn um panel in order to to log in and it's asking you for for your corporate credentials but we decided to block the image and the name of of the individual here because this was a tar what this is telling us is that the threat actors are targeting a relatively small number of individuals in a single organization and uh based on on our Cent understanding or
or observations uh with DET joury that this targeting is normally made based on the perceived ease of access to the documents that might be relevant [Music] um the next stage is the hidden run once the the theor is able to collect the multiactor authentication token and the ad credentials ap42 uh connects to the network and it starts um it starts the Recon phase on a on a note we have not observed ap42 using malware at all it has been mostly using benign commands or commands that blend within the environment they might use Powershell modules or Powershell commands CMD commands for Reon that such as B nature host name they are not revealing anything that they are really hard to
detect in terms of uh from a Defender standpoint in at least one occasion we observe them using um an open source tool from GitHub called Power hun shares but it doesn't contain any malicious of component it's just a power sh script to numerate shares um in terms of infastructure we have we have observed uh a Divergence in tdps we have oberved at least one occasion um ap42 using or relying on Commercial bpn noes in order to access this network and execute the whole operation while in the other uh we have been uh observing ap42 using uh residential proxies or temporary infrastructure that is only up when they are uh loging into this network and that
is immediately down after operation has concluded the last stage is the collection of dat cration and from my uh uh s point is one of the most interesting and you will Now understand why um we have OB served ap42 browsing uh ring files that are the or are of perceived interest uh to from an Iranian standpoint but the the most interesting part is that uh while we were analyzing the the cloud logs or uh the windows re we were able to see what was the tractor typing and what the thre actor was typing is usually one two or three names the thre actors were they knew what they were looking for they were not spamming
around that they were not browsing a lot of files on the network looking for information that could be relevant or not they were just targeting or introducing a specific names that that likely indicating that the threat actors knew that the victim includ even these uh targeted individual had access uh to these files in terms of uh of the topics that are related to the files that they are browsing or looking for we have observe uh repeatedly the use of keywords that are related to the Middle East we have certain browsing files not only in um window shares we have certain browsing uh connector share Tripes in the cloud with topics related to Iraq to Syria of
course the war in Ukraine and as well as documents that are related to a foreign policy or related to International uh disputes that relate to Iran in a certain way the last stage for them once they have Scan and grab these documents what we have served is that ap42 has been just grabbing them through RTP back to the network or they have or they have collected uh pruit files that are identified the victim they zip them with a with password protection and they might exped it again back to their uh command control infrastructure or to public CL services such as one drive so in this part I'm going to mention that um as I said ap42 mostly
relies on their spare fishing or social engineering activities or operations and they generally as Adrian said in the previous operation they don't use any Uh custom Weare but mostly um tools that is um uh difficult to identify but we also track like they we also have the cases where they use custom malware and I'm going to mention about like in a short way what their Mal based operations so recently we've seen these are the recent ones the first two are the recent ones actually uh we've seen nice Cur and T cat vectors that are used by customer vectors that are used by ap42 uh to like that are downloaded uh by together by decor decor document uh
probably uh or possibly um letting ap42 operators to have an initial access with the target so uh in um I think in in in March um sorry in January 2024 we identified an lnk lnk file that is downloading both nice Cur dropper back and with a together with a lure document named interview feedback form and in the intervie feedback form there was mentioned uh an intervie name as Daniel uh server and forign um um sorry for that I need to check uh the notes I'm always forgetting um a foreign policy researcher actually uh in Middle Eastern Institute um I will also mention here uh another custom dropper net dropper that's used by Bacha uh by
ap42 um it's not the recent one recent sample it was used um this campaign was active in between 2022 end of 2022 and 2023 actually as I said it's not recent one but it will show you I will explain in the later slides uh it shows actually how ap42 operates in a highly targeted [Applause] manner so Bacha was highly targeted campaign uh because it was using um ap42 was using a bachow samples that are unique to each Target so let's say if they had like they were targeting like 50 organizations they had 50 different samples that are each and unique to the each Target and even if like they're targeting the same organization twice they even had like two different samples
so for each operation they had different samples um that are unique to the Target they had hardcoded IP addresses they had hardcoded um like they had pdb pads containing information about the uh about the targets and they have subdomains that's also unique to the Target so here you can see some examples of the uh samples that has the PD pads containing the country codes of the um targets the Austria Israel so it's not also only Middle Eastern U uh organizations but also there were targeted organizations that's from Austria Italy and turkey so you'll see here actually it's reducted but in the reducted part that there exist also the domain and the organization ation name so as I said
they all the samples were unique to the Target and also subdomains here are two different screenshots actually they're both using the same CNC they are from the uh they're actually different two different samples but they use the same CNC uh but they differ in the part of the subdomain where one is using the austrialia possibly a Target that is located in austrialia and the second one is coil which is a TLD for co. and Israeli possibly targeting an Israeli organization so bachow is I will just briefly explain how it is or its attack life cycle so bicha um we we identify two different variants basically but in both variants they were B samples were first starting with sending a DNS
request uh to a DNS server controlled by AP pt42 operators and they were resolving a subdomain which I explained in a previous slide that is unique to the Target they're um requesting a resolution for that subdomain specific subdomain to that DNS server and based on the resolution bachow is performing different operations so it either does nothing or it removes all the artifacts or it drops additional payloads and these payloads are contained um as a basics for data in the pach samples so in the first variant we see the p is dropping an ASX webshell that we call shile and shile to operate in a proper way it expects uh a specific user user agent string and then once it gets that
uh specific string it is capable of file uploading downloading and command execution and in the second variant Bacha is dropping peeling tool together with a power shell Vector that's named blink power and blink power is using peeling tool to uh make reverse proxy connection to the CNC um uh to interact with the power sh web server by using by by making that reverse proxy connection they use hardcoded values again that is unique to each Target so they use the usernames and passwords hardcoded passwords and usernames that is unique to the each Target and that Powershell web server is uh capable of file uploading file downloading command execution and script execution so I explained here in a super
brief way the Bacha sample if you want more information more detailed analysis actually uh bit theunder has a really nice blog public blog about this so you can go and read that it's really nice uh blog and Analysis
we have not observed uh the attacks conducted by ap42 but we have observed a shift in Iran sa operations after the October 7th attack of Hamas to Israel uh or corent understanding of ab42 uh likely suggest that ab42 are is going to continue uh is going to continue to support um current collection efforts it might change depending on some political geopolitical events but based on ouring observations most likely any geopolitical events that or Internal Affairs that can be of relevance especially those in the Middle East tend to be used by ap42 as lurs or as topics of conversations to Target again either uh this Iran diaspora or think tanks or any organization that is deemed to be a Target by the Iran regime
and one of our um to close one of our observation is that the actor continues to evolve we normally uh assume that Iran uh doesn't have the the the power or the control in terms of sever capabilities as other countries such as Russia or China but the truth is that uh ap42 continues to evolve it's a highly sophisticated thre actor and uh he has been proving as well to be quite comfortable operating in Cloud environments they don't rely on tools and they don't need almost anything it's an in and out really fast and it it's is quite uh it's quite hard to catch in a sense but talking about blogs we also have one and it's pretty cool uh we
wrote it a couple of weeks ago and it has more comprehensive information on ap2 operations thank you