Deductive Reasoning: File Analysis Techniques

Show original YouTube description
Show transcript [en]
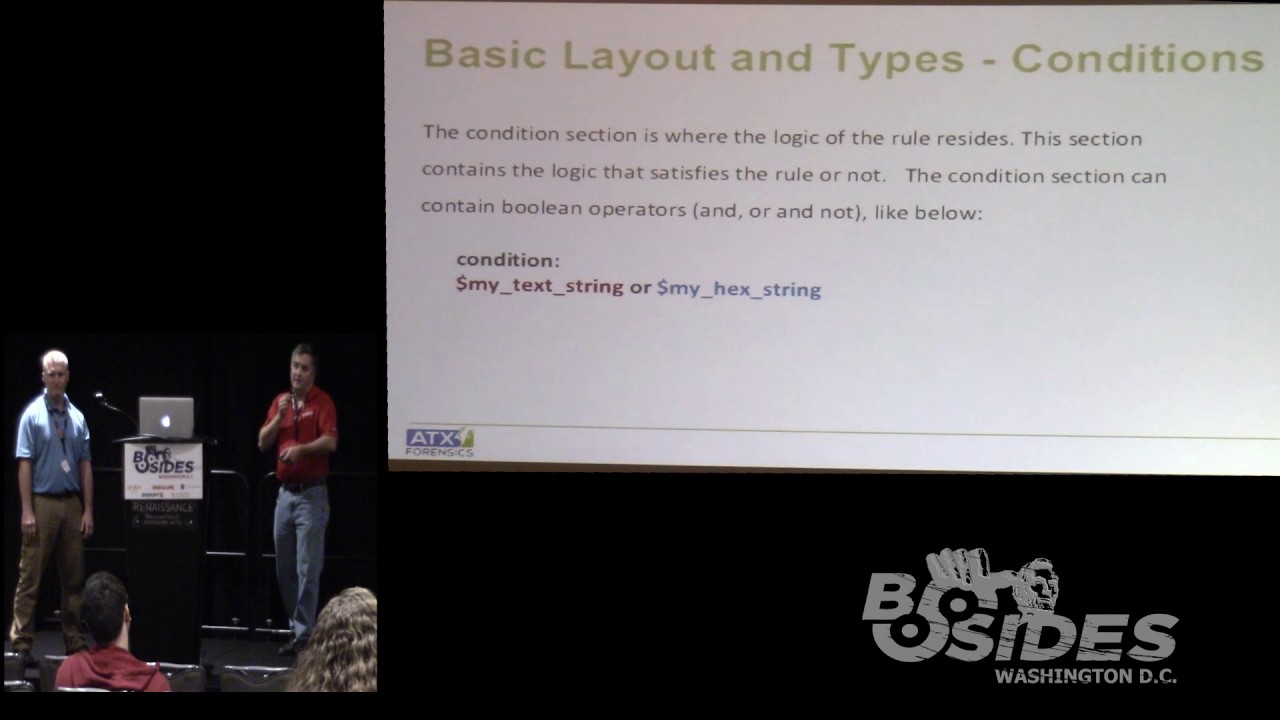
a vibroblade up for the I'm partner to brother we're here today about sex right so my name is Tom make up my partner Chris Rogers you were here day talking about stop breathing I'll announce technique we're going to start with a green card with a product demo so please go ahead lot worse time I be comical the next two hours I'm going to take you through great detail browsing the current apt landscape diagram kill chain optimization of your current infrastructure for synergy and most important pricing and availability I took it I don't know you want to acknowledge that so again playing time I talk I've been involved various out there currently I work for the Dallas Times appearing on our prep
research team i work in Citizen Kane and Chris often have a very background well yeah mostly government contacts now I didn't work without the bank American purple Goodfellas senior allies for research now or so use the mic say guess our mellor okay bye forget it out of the river up or kind of work one microsoft you can actually pick up and hold the mic it's okay alright so this actually started sherlock holmes pan and stir Arthur Conan Doyle through Sherlock Holmes broaching the sign for about the doctor bruising and so he said that you know if you see a thousand you know crime scenes and pieces of it you know what's going on the following first
shouldn't be a surprise we can actually apply the exact same logic to mallar analysis and if you've seen you know thousands of malicious files and the behavior know the symptoms you can relatively easily pick it up and find Amell or without actually going into and every time
so just a little bit of a disclaimer here for for this talk I don't really have a feel a lot of people to various go up and background this is really heavy media introductory type or talk a lot of things i'm going to show you when necessary to prefer anything sound these are things that you have a look at it yeah here's something I figure out I don't need the feedback very well got better so basically if you've got a system on a file on and computer the looks a little bit suspicious we're going to give you some tools capabilities of how to take a look at it and kind of critically analyze it and
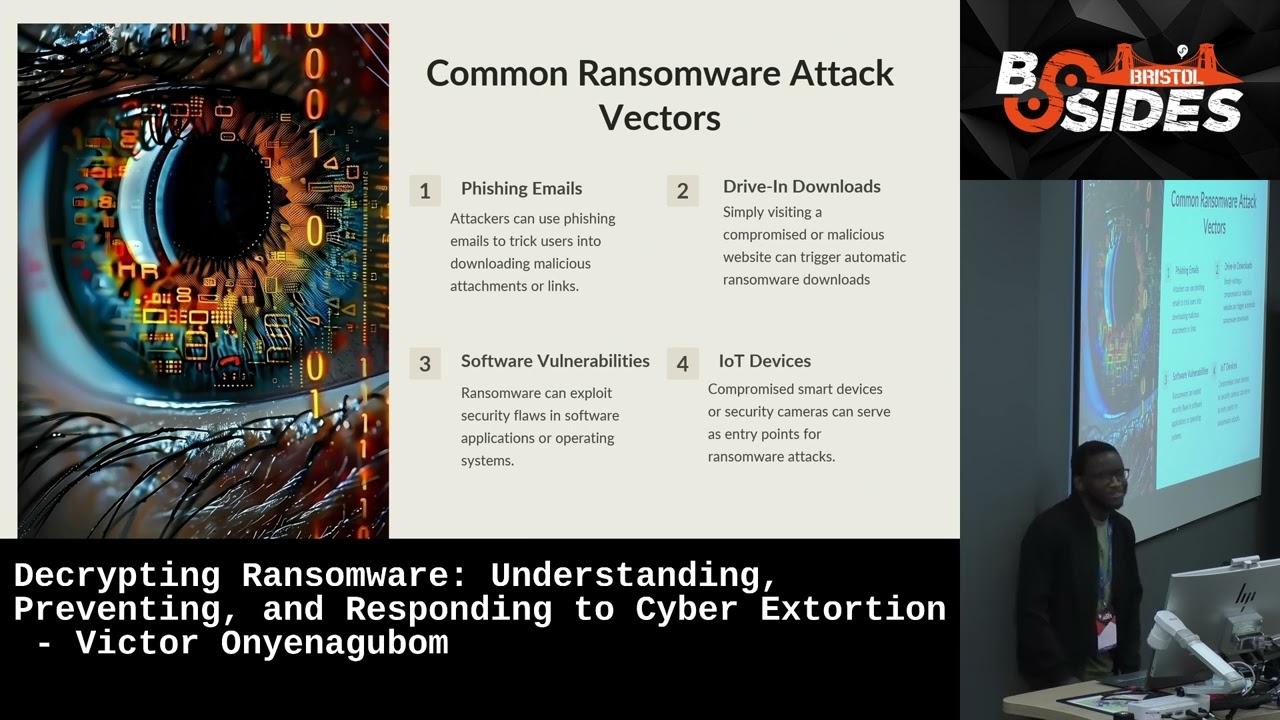
eternal mother not texting malicious so this is to basically we know this it's a very deep topic and we know that a lot of techniques many days for some of yer so keep that in mind we go along yeah you're not in ir that you're probably doing it for your family oh so what is network it's really just writing a logic you know what is it it's not magic it's simply a series of instructions with computers like the basic level are just tools that just translate by our instructions dimock at pictures or you know lover dead and you know better guy shade marketers because of user friendly nature they take a full advantage of it
and get there get there little flexion if it's system so talk about backers email web you know you see them knew Stephen everywhere you know it's common it's something that everyone knows it ha stop it say it's in through the wire comes in through the internet so how was it still a bit I mean it's been 20 plus years and the same same methodology still getting it well a lot of it has to do with user-friendly itís the user experience is paramount in especially the corporate setting you have to you know go to the user go and give them whatever they want there's a lot of latency stuff backwards compatibility and really it's it's kind
of purply so I mean we're in 64-bit architecture and we're still getting 32 good now we're pulling employment systems everybody has experienced I'm sure you know you go to network and you're the server they're running ng for you know that's that's what I only don't have with the server you know every server happen basically it's running from lengthy application it works don't mess with it leave in place but that oftentimes it took one of the biggest vulnerability that you have network it's old patch just don't ever leave along so those are all things that work against us we're looking at a networking the security posture yeah the end result is always the same tacker gets in system is
owned and they get whatever they want there's information or money or just control so we're going to fight your account and break down a little bit of the process and stuff you can do an essay response I'm gonna take it with a little bit of what you might seem to be game your so called instant response type of situation basically if it looks like how it smells like now probably mount rack system okay probably wasn't that catch that funny cat screensaver that you thought your download so what important things that I'm going to talk about our map times those of you not familiar with that time back and for modified access control and look at the
time stamps that are on a different files and doesn't one of the things that Allah will try to play with your kind of time and you'll see the different ways but basically I'm getting a couple things you can take a look out to some to do to look after your particular file to my hat on compute so what is it one more problem operating system maybe you encounter any of them probably one more common process is about their the waiting list there the final structure between the map quality and if you have never woken to back to top and essentially what we're looking for in here there's tea sets of timestamps the standard information than the finally
that's embedded within the master positive now when we talk about those two different time scales the one that you interact with this user is the standard remain tight mp4 file property for this be here and what we have yes I Jon and in this case here we've got created a modified number 2005 when you see that cloud access in November 2014 now those bottoms I already will be allowed just put was like on a service so he was either this is going to see now the one that I did a little bit deeper tomorrow we want to look a little bit deeper thank you anything but one game with it further detail out there all this going on we can actually use
control to comment available as I go through some of the slides and his Chris goes through a number of length of the back of the slide deck will happen so much slideshow thing wrong number links just teaching reference files or programs first let's draw a clock out of deputy manager uses a lot of instant response which is the nice eh tool to having a controlled up the case opportunities program basic usage we're just going to grab and have to file table take a look at these have to go through your whole system and create a rank amateurs the cable is an export house key gamma team right and what would actually heck supported that out there is a really
nice and I'm cool that I've used in the past called MFG dome and what this does it take the contents of America quality and dumps it out to you cscs when you take a closer look and in this cave and I spoke about the standard formation of the bombing times before we can see that they don't match up so is great for went on really quickly we keep hundred times of my job makes yourself a filter it shows where SI or the attend involved on match and that deference that should raise a red flag which is followed by peppered with whom I take a closer look at this some one thing that first point talk about will help
one of the other places we can book are on the ankle classes himself the storms are poking around you know you'd be pretty simple most of you know where offers to it so we put a file and location and we can go through and finding that works as the complexities increased a lot more location victim operating system version windows are coming into play and so there could be potentially stuff a different directory word for I have against Winky and it's like that here in the reference section they can go through and look out to the twentieth place the local sufficient five but essentially we're really looking for think that's just both long and one of these things is not like you
all right in this case here we're looking at windows system32 whose duty I are equally oir people about exe file please stick out like a sore thumb not only did you get money from you know certain cases ontology hypocrisy Chinese characters and rural character a 15 to 30 blanket stitch with in that direction here to get our edge of the list i put together three guys with his life just some convocation again one place did you book these our economy people we talked to her for now another thing that will look through we're trying to figure out the potentially got some curve actually on a computer ravages and we can use regex jalabiya background offering you project your
auditors in this case what we're looking for the bad guys they want their our Kela so to reboot the tube there's no persistence necessarily South persistence is what we call when now our internet trench on sir the reboot okay the road or review system and again we have a positive rotation that's going to look through and this isn't family bir people's IDs you follow a decision on remote software Microsoft Windows version and grumpy is actually an entry the dentist on to the files of the senior you'll see the dough reader the product and we all use who want to start up as we you know use our computer on database we don't want that I reveal so
but we won think when you do a little bit work nation may be about to happen in there you can take out the echo registry key so again just using read Genesis 4 300 system you just go bottle x1 save it out of text file and doing here in this case I'm protecting you open up he is realizing to the actual the last time that key derivative we see that remember second 2014 date again okay one of the things we do as investigators if we try to go through all these lots of family time but what time something thing is so important for the throwing you know things they can play kind of protracted so again this
lists common refugees idiot not one of moms but he doesn't communication that you see get wings of that was like that show anyone of government is Jesus who doesn t need to do to you if you wanna get kogi on Roger I thought this approach number of high school all around they told will be more than just recipe itself test Network some other application for the election your sister and contraction through by pritha another table mommy duty to do this particular topic basically Freddie's windows XP Bernie windows XP princess loud for treating the basically just to help you speed up to start off along the applications on game days total do it up and thrown up cash and so the recreation
is a good educational closet and run on system so in this case here who does the windows prefetch directory and we will be in there the great time in that file itself giving indication when i bought my first and run on the system now that's impartial a lion diesel gas remains my date time it was worked on that kind of educational I product all embedded within the profession outside one laughing I'll talk about here the task Edward and basically you know another method precision and see without his schd you got txt file to pay what version when you're trying to be located ecology replaces underway to try three minutes pass and nice blog column gives us
information about Hitler Casper job at their schedule offices this case here we see his iron eagle job was started on another stop again seeing the day together second 114 in this case here is positive 1 thought that he's a lot of reasons just to be in net framework on computer or business random panettiere maybe this is a mitigation of the time starters follow miss Kay to meet our next success now that is tha that's kept a lot of text file is it the water there that can top job positive created and set up cats so he indicated the entire agreement optional we actually open that up and the past 11 so into the report immediately proposed
a little bit and i'ma turn over to prison you can kind of walking through just some other things with pools are ultimately 5 i'm struggling with something medals alright so you're actually equity going off nanosystems he's got something I on three locations and you're not sure about what you do well it has a detective clues you need a needle in some way to get the information so you can process it and make a determination so the first thing you want to happen it will get is the internet it is definitely living information age and for every you know cute cat picture or funny video there's two or three you know malware blockers talking about something on your NC just
go out there google it hopefully from thank you had a story yeah one example I have is my uncle actually confirm i'll add a female right so this bark echo you're gonna and the little cat thing you got any now and so he's like a tiny bit of water so i took a closer by both get a bargain by horse crap northern at every time I try to use common AFRICOM so shut it down so you know brighton rough so they know they are trying to cover the tracks with this stuff so you where you want a clean system are we doing here resources like that yeah and we are going to make the internets
that's nice and easy do this I'll second thing you're going to use a hesitant I will you the hex editor it based I think that takes the binary little bits and with SP heads and that SQ excellency here actually translates it a little human readable text over here and all of this is searchable as a bottom enter you've taken first few bikes there plug it into google and you should come back I think Barry tester has the largest batch of plastic matures today so HD here we have a funny bad game bang but the first two 45-8 is actually an executable pop so it's not what it says it and so when they hear you no reason
it's going to read it based on the based on this information and not the extension neck stated menus tends to be analyzer I don't know how many of us would be so just bear with me what you're looking at here is two files this one's on depressed and this one's using a freshman of some sort and entropy is the measurement of you know order disorder in a bottle Wayne information it's actually what is it the natural order as well yeah so what were what we're looking at here is the same file aggressively congrats the first one leave intelligence you know a bunch of patterns and data clusters if you get kinky mm and the Petrified fairly low and this file over
here is pretty much scattered it's very random and I XP like high stuffing press files you want each people can see and what's inside oh and this is shannon corner plot channel in 1948 thing those you trivedi bucks so the next item one is a hatch people use hash cab there's another player pipeline there's pee bottle and so but why passions are essentially fingerprints of applies the way to file instead of typing in you know services that exe and coming up with a thousand different things you type in the md5 and you're going to get a whole different thing is this actually what a file is and as great thumb the caches from sears either can do down to the Shahs you can
see the number of characters increases md5 and sha-1 are pretty much banister standard you're going to hear your hash collisions a lot of math needs together and they try to basically break the algorithms it doesn't invalidate them I get to see a heavy fog bleeding a lot and I've been doing this for a while Shah line and that's even more us you know 40 characters as opposed to the 32 so it's even more active and there's a variety of shots too many sixes start to pick up a little bit but there's also for a bottle oh yeah which is 120 characters that is a lot of show how the other equals here that is action
that is pretty fuzzy matching it's a wonderful way to competitive out I get the black count and two different hashes and those will be able to tie those two other clouds and great family resemblances it's good to amongst its really good on X file some of the compression algorithms will scroll that up and so you relation the authentic ashes to their widows Africa you guys have seen that right click on a five that's what that is it's just another hatch they use to authenticate the integrity of the executable club and the in cash in cash has been in popularity when I compiler works and compile the executable file it takes all the imports and holds them in
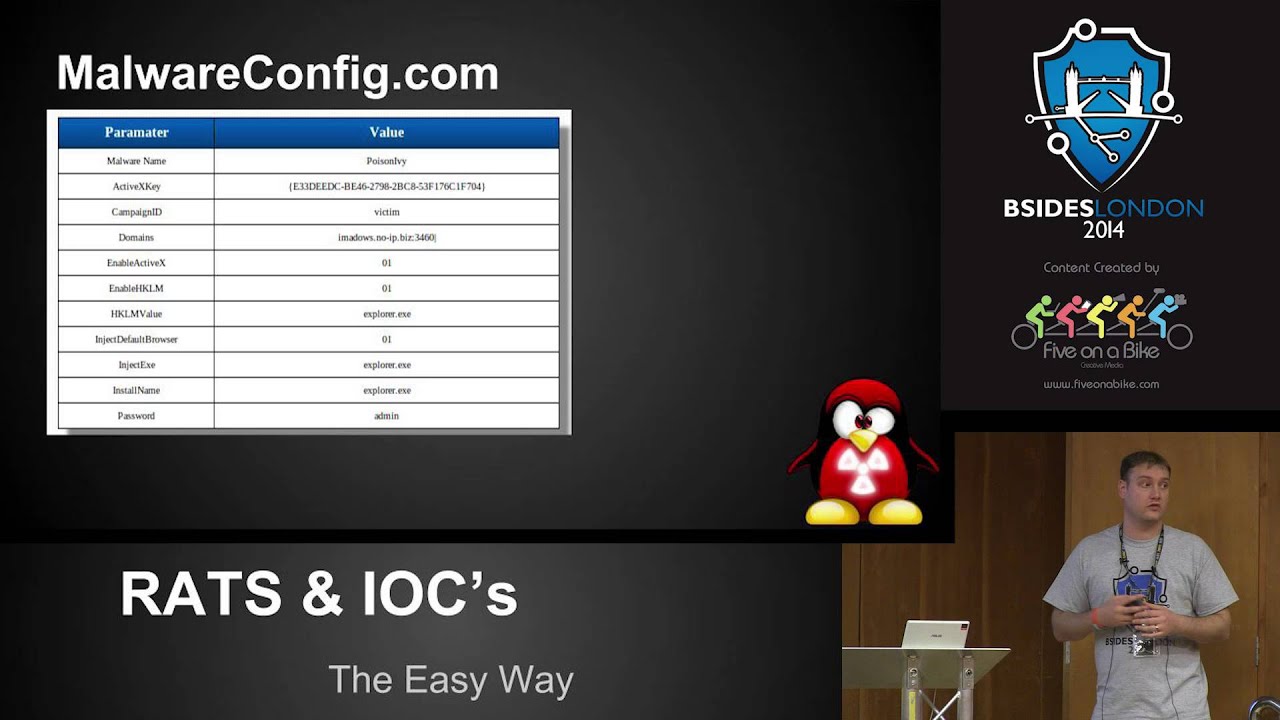
a certain order the impact goes through and says okay well here's the order you know and it ashes you know that series and then you compare that with other stuff but that tells you is that it's the same high so it's not going to tell you it's the same same mail or family but the same product so you can actually equate it to actors or such accuracy in that if you go out there and look at individual ski you know after sharing sets and there's a variety of stuff on there now that works with that an analyzer or information sure there are a dozen or more out there they apply signatures mr. on this one's probably my
favorite piece video it's a beautiful thing we actually has so many signatures that are augmented so you just drop the file in and it will go through and it will look at all the signatures that it knows about and it'll tell you hey I think this is the dishes because X Y or Z and you can use your custom new Jarrah for those of you who they r & P explore there's nothing there's a dozen elevators will break down the aisle with the information game you see the hatches and there's a variety of available women for comm mark oh yeah I agree the P information why is this important because all eyes people have effort and
the header is not human readable for you that but it pulls out stuff like a creation time and time again how late I which like John sake love with the time something it's it's kind of easy to month too much this but most Iraqis don't if you can you said the system time to something will you can compile it and it will be and you know most of most of the compilers you know when they running through with everyone thousands of files through in order to get via the now we're out there it will have a more so now you have a tool set what do you do well you go off to the file system
birthday might look at it will get the bottoms I like down on the same if you see you know Cyrillic or Russian characters on nano system there's something that's a big clue right there service those it's misspelled you guys in the spellings or something that's close the windows would not play that's another clue and then there's the total random character you know I created this you know with a piece of code the feeling things simpler than finding something like this is finding pfft XD or word that EAC the hash we just talked about the hashes so what do you do you go out the google aquifers football control Nash you know see what's out there they'll give you options I'll
cotabato just know that if you're uploading file you're losing control you no longer have you know what I was inside so if it's a key log you know this up about an hour now Nana's recipe and all the bank account informations on the internet which is just never good filetype we're talking about the heck side is where the heck's that is really awesome so here you see creative involvement freedom about legs are live and this is the old office on d0 cm11 easy row here's the new office which is XML in a compressed file or if you did and then down here you have the SP OMG header this is you know really word as a human looking at the binary with a
hex editor you can actually pick out some of the stuff and you can go down through and pull up strings and stuff if there's nothing blocking you are compressing the file the size they lata cisely possess play a part of anything well it's pretty relevant you know if you got to pee dee up and it's incredibly small or if you got word docs or powerpoints and they're really large and there's one like one day or two slicing them that's a key in it that there's something that might be like up here and so you want to take a closer look how do you do that we break the files now now this is actually pretty
cool because those office files and you know the PK header it's just straight brushing so you can actually take 7-zip which way did in this case and in this one I took an executable file and I just said Kate well they can extract as executable Bob and this is what you come up with you got the text section on our date of the data and this resource section well what you're going to find more often than not is in that resource section that the camera offers you're going to stop other things like will say is an icon file but it's another rescue so you can dig through that you know repeat leatherby go through process and
it all worked with a about determination on validity this is what a power level is like when you break it down using zip format again become their breaks down into all these wonderful little directories and you see here these are the slides in XML format and look there's a exe right there in his life so they've got their efforts in there it's never going to be that easy but you can you can go through and find something that's suspicious or you know do this with an office document below through the VBA code it'll break up with one player there is a CBE 2015 4 14 that we just will report on and that was exact
same thing they basically packaged up a new vulnerability it was an iphone or build ethic and PowerPoint and they did it is packaged it up and you know using the slide so there's a big file one slide relatively easy to find ones you extracted it hey look this doesn't look right time job talk about times counting how is very important to us well here you see you know there's this time in 2008 which eight years old so if you go out and look up you know w get you know and look for this specific package you should be able to find some information online so compared to or just download another version check the versioning check out
the rest of the data that's too old or too you then Jacques towns not ball it means it a question upon the metadata metadata is literally just information so you go ahead and look at what was this great advice yeah was it created by a tool that you know should it should record who was the author how many pages you know there's a lot of information you can do to say hey this is this looks suspicious you know and this and with everything else you can make a determination this is a bad bot this is a good Bob yeah you media QPS update when the attackers like use very valid entropy we talked about a little bit
earlier i'm going to break it down for you so try to stay awake here i use crippled pretty cool that is just phenomenal and i downloaded the second board for product boot bird and electra night didn't actually check on it and there you see the entropy it was pretty low then I'm going to have to use the same tool I did the encryption a symmetric encryption using our c4 with the key f00 be pushed encrypt and this is what it looks like so you have a plain text over here and this is the encrypted version on this side any of you tell you know you can easily look read this and you know if you do this in
your head and the other job way any CSP is way high the reason you want to look for I entropy is malware authors won't change and the little repack something just using a crypt or using a different style and this is a way to get it passed 8e but as even you can easily go and just go right feel good and enter each other and say hey this doesn't look up and let's all say boxes so a lot of times sandboxes artwork they're just their dominance put up a almost there's not a lid over and they don't work you know and you know you look at the static affections you can tell it's malware but
I'll doing any sandbox I mean nowadays there's virtual deduction there's some tables will see it's on the now examples are out there are you know love you doin gravity three checks looking for existence of VMware virtual box looking for existence of Wireshark and things like that that's about where to test that will actually change of behavior just shut down deliver different payload with something long coastline so you know it's kind of cat mouse keep going back or if we have get to be cool to try to detect now doing it out what we're doing we go back and forth back and forth even now Kevin we bought a lot of good rat decoders and now we're actually seeing power authors
and use that put you know lovely messages in there about those reporters and some of the breakdowns you aren't checking I'm Chester's ways to basically patty hinder analysis for those of you in about a little more advanced analysis and sometimes their dependencies either you get a file that you don't have the accompanying while that was on the system or the file like Java said earlier yes yeah like stuff that looked first at a keyboard leg and it would install and work only that was present and sometimes you know you're missing a component on United the whole system so you're trying to be something wrong version of word we're peers virtual environment or sandbox you got a variety
of different you know things that could prevent it from detonating properly malware itself could use other techniques that you can go up to a known bug own site to try to pull that guy P address in the duck down then again it fix it ever before I look back to the laterals using the internet and trying to get ever information if you go up you have a file decided to send a hash bar sold our soul comes back 0 56 you know 80 butters attacking it doesn't make it a good file it just means if not most fun and so yeah those are great but you gotta get a better movie but you gotta use a little little
of your resource and try to make a decision whether or not that is valuable sometimes matters now our reports will be very high level and won't give you the technical details you need so you know just kind of give it off their go find something that will help you make a determination these the whole thing we were talking about can be related in a couple stories we had from experience there was one time we have a response and we went out to the five had an alert we get down there it was a common location and I'll was just you know there he had a scrambled name I entropy it was obvious so we were able
to pull a file we're through in our sandbox and it didn't work and so then you know what happens and you have to take it to the next level Trevor happened it's a hoodie thing to email or analyst and and we saw some weird system checks going and we're like us as the main jets and we're like well why is it checking system e-check assistant named it would just kind of sit there and spin for a while and then Germany and so we know what was going on following go down through the path well thought if I know when it sells itself onto the original system it queried the original system systems name edited during the melt or
the melting process and then was looking for the system and comparing it to the system thing that was currently on and it didn't match it completely went a different way so once we're able to go ahead and bypass that we're able to get all the deepening information figure out exactly what it was you know based on the behavior okay so another motion area we had with non-network law result who is this Bishop people enjoy how to Chinese efforts now never ratified yes you'll go with what we was we just very randomly and so both down third looking at it and it fighting it so it left a lot of gnashing of teeth we realized that there was a
very critical pendant we need to have this particular piece of melon we had to have web browser open and have a paint file loaded up and browsing itself to actually execute payroll from now so just keep in mind you may have a very suspicious file out there but you don't you can't get drunk you have 30 per year but it's something called it may be time to avoid doing before the xix chiste but yeah like what you're saying the techniques that we you know we showed you guys if they're not named you know but you use them the terms of the that is malware without actually knowing with Mallory's going beyond windows these same tactics could be applied what we
looking at here is is an alt better brought you two mixers out there and literally you can search stuff you use a lot of the same tactics including trying to decompress it out using winzip it'll break it down to the components it's it's just a really really nice way to cheat so in the inclusion and we are breathing steadily well what would I let you guys know in some clues are key entities it's you can get the smoking gun just looking at some of their comment has a specific mutex I think for Sarah Carol put a wonderful their common thing for our blog and some booths you know you can get up massing the flues but you won't
have enough to say to make a final determination you know so even though you have like a weird filing and a known location you know sometimes the glove doesn't fit so you gotta move on try different things I think the final fitting both of them leave you guys would tie this whole thing back together that the more bizarre thing less mysterious it grew to be which you go out and you see and it fits all the criteria you know it's bad but if you got something that looks like a system file is behaving erratically you know those are the ones that are really really hard to find it hard to define good yeah I think that's it I have any
questions there we go vitamins oh no nobody okay yes how do we deal with SLR that is a really good question if you have access to the host and you can do it daily that's probably best that I don't know any good good automation for that long time on network yeah we do a lot of networking national network stuff when you're hooking actually have a physical system it's a a bit more of a sticky wicket anyone's got failing I think we're done thanks