Kevin Breen: RATs and IOC's - The Easy Way
Show original YouTube description
Show transcript [en]
i apologies for those who didn't want to come see me nobody voted for me so unlucky someone is covering I'm going to talk about some remarks s Trojans and IOC's I am son satisfies reverse India malware and I'm independent researcher blogger so my views on my own and not of the employer i work for I'm not going to tell you it is so that's what my friends think I do that's what my wife thinks I do that's what work think I do and that's pretty much what I really do if I was told who needs malware engineers when you got BTW so what I'm going to talk about is what I write is who uses
them what's in them why am I so interested in them grubbing the useful stuff out of them we're going to make it easy and then we'll look at how we can share all this information with the community so where's a rap map is a remote access trojan or at all depending on whether you the good guy the bad guy here's a client server configuration that's slightly backward so how will normal enterprise client server is the server sent out to all the end users the client is sat on my box is the attacker so it is really backwards and they're typically reverse connection so when you run the file you will connect to me rather than me attempting to connect to
you so I said the server side sits the insecticide and if you get one of these on your machine it gives me full and federated access your machine not only to the machine that I'm on blows to the wider network anything you can do i can quite literally do better if i get a a right and planted on your box so black shades are up black shades is a publicly available remote access tool for sale I appreciate that's a bit difficult for you to read black shade is mainly an IT surveillance and security based organization directed at making your PC experience easier our main goal is to offer affordable software solutions and so on and so forth so they make
themselves seem legitimate how many legitimate pieces of software would include ransomware as a option so this option is by de facto in black shades and will allow you to encrypt any file on your box and then display a message to the user saying I have encrypted your files give me something in return so yes they mark you they tried to market then they sell them there's actually a really big market for these things black shades is about forty dollars you have to pay for this and then the bank i thought you know a lot of people are buying this and they're infected lots of machines and this is being used everywhere I want more for my money so the author of black
shades actually put a backdoor into every single server that goes out so when the bad guys are out infecting all their slaves they're actually infecting their slaves with a backdoor server so they've got access black shades of good access whatever the black shade sell it to good access so it's a massive massive thing so who uses them script kiddies use them that's a twelve-year-old boy in his basement ecran groups your big Russian II crimes they use these and apt use them script kiddies they like to do that these are taken straight from some hacking forums so he started this thread so you can share his best moments with all his female slaves this guy he was
told he was lying so we had his proof youtube video he streamed of her as he was hacking a webcam on a facebook this guy's really happy he currently has 126 slaves on lines aiming for 200 this guy's not so happy though he was listening in on her mic he alder calling the police and he didn't have his VPN turned on sir he's being traced and this guy his slave got his mummy to call the police say salt gives you the level of people where we're talking about we're really not talking about you know addled Caesar these are kids who managed to get all this publicly available software and they're just sending it out there these
people the way they typically tend to distribute is there look at whatever the favor One Direction song is they'll rename their server to be One Direction dat mp3 sends out as a torrent or uploaded as a youtube video and waiting for somebody to come and click on it somebody clicks on it they get the right installed then on the wiser a crime syndicates so semantic push the report out last month then the last month detailing the this is a sorry this is a publicly available rap that's out there in the world it's been actively used by equal critique round groups and this is this is massive apt anywhere you look in the news over the
loss over the last year and you'll see the apt is using rats terminator they're all over the place so what the apt groups tend to do is they'll throw this this rat at you and use this as a first day Jim plan this for a couple of reasons one it's a nice simple piece of malware they haven't had to expose their their big the subjects vent fortunes building privately and also is low attribution these are all publicly available the whole world uses them so if you were to get one of these infected on your box how can you turn around and say that's state-sponsored attacks and not say that some kid in his basement who's accidentally affected you so it's
that level of deniability that makes it a really useful first-aid implant that and they are ridiculously powerful so that's what they are us who uses them so let's have a look and see what we can get of them so because a rat is reverse collecting all the information is already contained inside the XE file so it lands on your machine that has all the information that needs to talk back so domains and IP addresses passwords anything they use if they're encrypting the link the passwords are in there the ports are in there when this thing goes to install on your box file names file paths registry keys mutexes all this information is natively stored inside
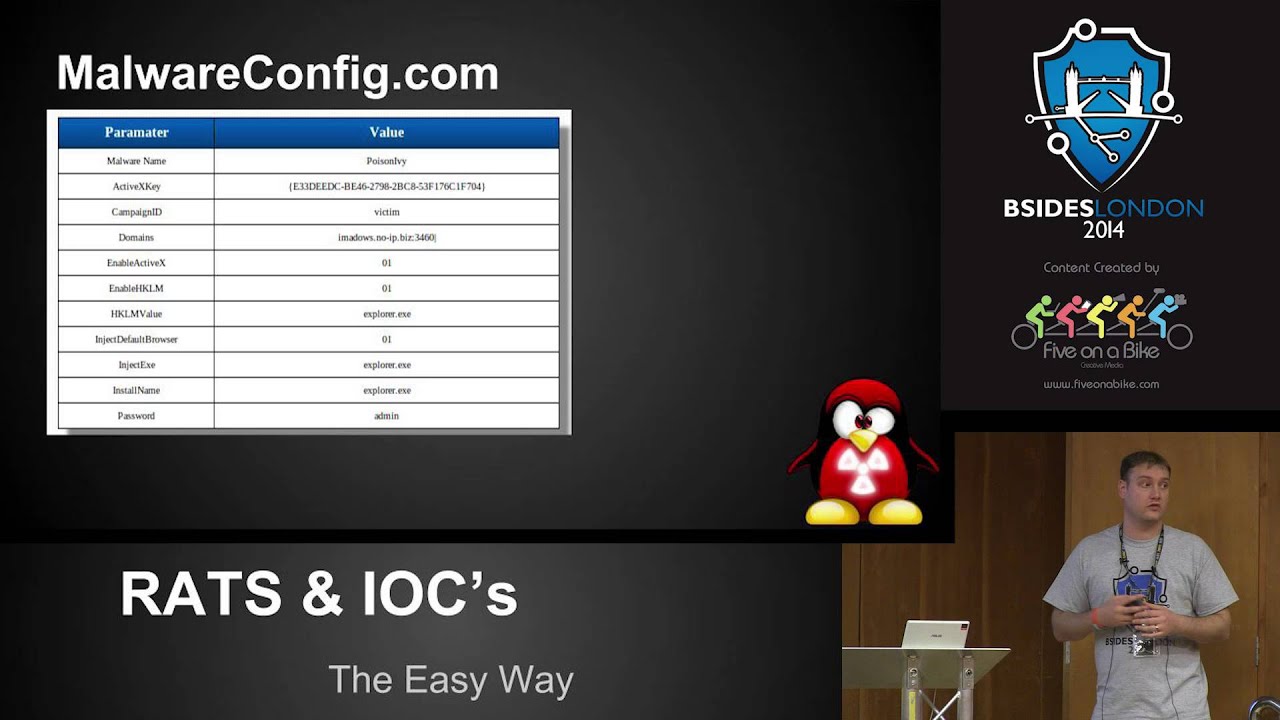
that file you've just got on your box so basically the bad guys just said here have every and single piece of information you want to defend yourself against me to find me and to locate me there it all to you so grabbing the config so we know all this stuff's in there and this is the more technical bits o budgeted the workshop which took you through some of the states we go to do this so a lot of these conflicts a lot of these routes of poison ivy was massively used the conflicts in clear beacon domains port numbers insulation names all in clear text so simply opening up in Santa like strings or in a
hex editor and you're going to see all this information immediately in front of you sometimes we encrypt it with the encrypted stuff we still need to find the password apologies that that's not very clear in the bomb when they encrypt it the method of encryption has to be included in the next file so the encryption keys there the encryption scheme is there everything you need is sat inside it so what we can do is when we start to analyze this we look for the encryption key we take the encryption key out and decode it most the time this this comes in a couple places either sat in a resource section or it's just depended on the end of the file and
depending on how we go for time by over couple of demos we can go through the end and show you how simple it is just to pop these bits of information out
so now we know what we're looking for let's make it easy so I've spent the last two three months looking at rats and I've done all that hard work for you so I've released 23 scripts all hosts on my github and this will do all the work for you so you put any rat in there as long as it recognizes it and understands it then they'll just extract that conflict for you and give it in a nice easy way for you to view and then secondary it's what the main project designed run is my web.config calm so what I've done is I've taken a massive repository of malware over 16 million samples publicly available malware of
that I've indexing it I've sorted i filtered it and I've extracted about 45,000 remote access Trojans from those they're all currently being indexed in to the site and I'll show you the site little bit later on so you've got the config so how can we use this so defensively it's nice and simple firewall rules port filters looking through logs snort rules and IOC files these are all things we can do very quickly to start providing defense against you state now this doesn't really apply for those script kitty kind of attacks because you nobody in their corporate vamps really going to give affected with those but as we've seen this is massive used by apt Andy crow so
if we get a sample we get a spear fish sampling we've got that X file we we decode it we take all that information out I can now write firewall rules or snort rules to explicitly block and stop that or depending on what my infrastructure is like that I can allow those connections and limit them coming in and then to see what they're doing so there's a lot of intelligence to be gained and again this is all sent directly to you they give you everything you need to figure this out
for those of you that way inclined you can also go offensive with this now i'll leave the morality of offensive security up to the individuals i'm not saying go and do this by any means but again you've got all their information you've got their domain name that gives your IP address you have the port number that gives you a socket and you have their password so i now have everything i need to create a legitimate connection back to you with the attacker so what can i do with that i can dodge the attacker i know you're up here just in your port so what can i do i will fake 3000 remote connections to your box make your make
your client unusable you are now either forced to switch passwords switch IP addresses switch ports switch your whole infrastructure which now means that whole campaign you've just done completely useless to you anybody else you've wanted to affect if you haven't just targeted me you've targeted to other people on the same infrastructure there now useless to you as well because you can no longer figure out what are the real connections from the thousands of connections i'm sending you every second that's one way of doing it the other way is to exploit the attacker so a couple of big ones poison ivy and dark comet they're well-known they're well used and they've been used by apt groups
for the last several years and they're still being used now there are two public exploits poison ivy has a metaphoric module so if you know the password the poor and the IP address you can actually get a remote shell on the box well they sent us all that information inside the EXIF file so there we go anybody poison ivy and plant i can now start chopping shells on your box i currently have 13 and a half thousand live poison ivy domains and passwords so there's a whole lot of infrastructure out there you can just start going to take and control of that comment against without comment there's there's no remote code execution but what there is for comet is are with your
file access so if i know a file half on your machine you the attacker i can just go and download that file from your machine back to me this has one really really useful thing the Wade outcome it works is it logs every single connection every connection attempt and all the information that comes back with it is logged and sword in ask you like database that she like databases in one place so using my arbitrary far read I can now go pull that database down that tells me anybody who has ever connected to your machine it gives me all their key logs as well so every piece of information you've just managed to scrape I now also have that as well and
there are a lot more most of the rats that are out there have some sort of vulnerability in them that if you were to take the time when the research to go through you could probably find yourself doing the the more offensive side of this again not advocating that everybody starts hacking script kiddies but it's an option so like I said I have a large data set and I like to share I've spent a lot of time doing the research and rather than just keeping it all to myself I like to share with the community as I said IOC files I know the industry hasn't really settled on an IOC format so for those of you not familiar
with IOC it's an indicator of compromise and these are files you can create that you can share with admins and and other providers and you can use these to identify infections there's lots of them there's open IOC sticks taxi there are plenty of formats out there IOC bucket is the services up and running where you can share these are seized every rap that lands on that gets processed by my box I extract the file path the register Keys the mutex is the domains the ports create an IOC file to that and that gets pushed over to ioc bucket as well so it's a massive repository of known malware when the real useful things about this method it's impossible to
have a false positive you've extracted the config straight out of the sample exactly to this so it's impossible to get a false positive on that virus total they have every sample so any sample is submitted to me take virustotal if virustotal has it i'll link to them and say here's more information on it and then if they don't have it i'll push the sample up to them and then there's a big cross-reference their standalone decoders i mentioned this earlier so I've done 23 so far i have another 26 or two right so head over to my get pull these decoders down and you can just run these they're just piping on pretty much standard Python
about the modules and then Marvel config so I've got links at the end the other thing I've done anybody in fact does reverse engineering in here really is in my crowd is it sorry for those of you on boring so Viper is made by a guy who who wrote cooker with an automated allows his platform he works for rapid seven and it's a framework there's a modular framework for reverse engineering malware so gone are the days where you need geeks like me to sit and stare at the assembly and figure this all out of you there were nice modular frameworks where anybody with a little bit of knowledge can just open up vipre import the XE file and then just run modules
like rat analysis and then it just pops straight out so you don't need to rely on if you're working for small business who still getting targeted by these and you can't afford to either outsource or create your own reverse-engineer miram our team then things like this exist out on the internet where you can go and use these as long as you're not too concerned about publicly broadcast and this is lots of this other
there's a screecher working so more conflict like I said it's a public site that I've setup allows you to submit files up to be analyzed and you can search and there is an API coming soon
these are sort of things that will pull out so there you can see this was a sample of poison ivy this is non interactive analysis so at no point do I run the executable file and allow it to connect out to the into that I don't allow it to connect back to the attack aside it's all run on interactive or static analysis so there's no way the bad guys unless they come and search the site will see these connections coming in so you get all the values in the config file there's a virus total look up will do the domain an IP lookup so if there's a domain name it'll grab you the IP if it's got an IP org of the country
code so if you start plotting all this together you can really start to pull together some some really interesting piece of information and for those of you in an IDs this will automatically generate you a snort rule so you can deploy this straight onto a sensor and you've got immediate media alerts to any time this land on your box yawn rules yarra is I like to yard snort for for malware but again I'm talking to my audience so I'm afraid knowledge you can understand that so Yara's signature-based detection on the host so IDs intrusion detection systems these look at the network analysis and these look at all the ones and zeros crossing the wire and they'll analyze that and
they'll alert you on that yard does the same sort of principle except it works on your box so it's a bit like antivirus except that this is a lot more powerful than you antivirus antivirus is tend to use more heuristic analysis than they do with with string analysis and they rely more on looking at what happens when a file runs so pretty much everybody should know that antivirus is fairly well broken and can be trivially bypassed innovated as far as static analysis goes well it's really hard to trick on taveras is at runtime so DLL injection process injection nobody will be doing these things so av's got really good at detecting that yarra applies these sort
of principles to a static analysis and they're really good at identifying malware families and as we said before you can jump our IRC file so you can Nativity police ioc's so the IOC that's being used in a minute is Mandiant's or monday and fire eyes open IRC format so if you think you've been infected with one of these rats you pushed up tomorrow config you download the IOC file you then deploy Mandiant's IOC agent across your entire estate upload this one file it will instantly tell you every machine that's infected with it so you don't need to pay big instant response teams to come in you don't need to do a lot of this work itself with freely available
tools and freely available resources you can now just upload download scan and get a full indication of if your networks compromised don't know so as I said I'd like to share so as I'm building this database I'm building a massive massive list of known bad malware and what's of most interest to people is this information so that the main names the IP addresses so most about guys what they like to do is they don't like using their own IP address they'll use dynamic dns and the big ones are again this really poor quality on there it's no IP dine dns zap total org all these free dns providers where you just sign up get a domain name and then
associated with your IP address this means you can change IP address you can change the main names very trivially without having to read the euro your whole situ infrastructure what it does winds its way of us to track you though recently I upset a couple of thousand script kiddies so I run several thousand samples through this pulled out two thousand eight hundred no IP dine dns and lots more domain names I reached out to a cup of the security list someone and said you know anybody have any idea what I can do with this data I've got it I can't use it can anybody else use it within hours I had got responses back from godaddy from no IP from dan dns in
give me that information give me those IP addresses and they then canceled all the accounts so it's really funny from my cell so as I'm doing all this research as I'm analyzing these routes I have to go out and get the actual build kit so I have to go into the underground forums and into we're all the script kiddies are where they get their tool so I can get them as well so I've been in there I've got the tools i go i published the paper a couple of weeks ago all those get taken down i go back in to check and see if there any updates and there's lots of entries of kids crying because there's no IP accounts
are being cancelled and I've lost all my slaves and I can't spy on the pretty girls anymore so it's very funny it's really gratifying when you can publish this sort of work and you see that sort response so I'm a superhero I've just saved I have just saved people's internet and that's how I see myself so yeah there's a lot you can get out of this like I said it's all about showing a lot of people that the community used to take this information and they sit on it you know this is mine this is an attack against me I'm not going to lease ended this information and what really kicks off was that was actually in
mandan with the apt one report is anybody not familiar with the apt one report yes sir they were really bigger you know saying you know with enough is enough we're really going to start outing people and that's what this is is hoping to contribute to I have all this information I have all these lists of bad people doing bad things on the internet and they're not just script kiddies then they're not just kids looking at girls cameras there's apt groups there's a crime groups there are people on here making absolute fortunes out of your computers so if I can run this and start sharing that information then safer based on then more than marry for
it so the future I said I've created about 23 so far I have 26 more which I'm in the process of writing so releasing those soon expanded to other malware families so for the last few months will for the last eight months I've been researching only rats only with my taxes Trojans but as I've been grabbing build kits there's a lot of time over between things like keyloggers Zeus SpyEye they all use very similar tactics they've all got a configuration file this included in the malware they send to you they're giving us everything we need so I'm expanding out to those forms as well using the same techniques and principles that I apply to rats applying it to
those as well reverse engineering to the masses you don't need a reverse engineering degrees to run this stuff it's a little bit of logic run my script and away you go volatility plugins again really focusing this to the wrong audience if you do an instant response it's one thing having the EXIF file then you can pull this con figure out most of time if you're going into instant response you're arriving after the fact so the sexy father was on those probably gone now to replace with other stages of malware but everything's in memory so though I'm currently writing volatility plugins that do exactly the same thing they'll take a memory sample they'll look for those indicators they look for
those things that mark this is piece of malware i extracted out I mean exactly the same thing give you all that information and then I said they'll be coming to a get near you soon ish as soon as I finish writing them it's really hard right in all this widely w data as well again apology sir I didn't anticipate the slides these are I like to stand on the shoulders of giants if somebody else has done the hard work for me then I will happily take their research and then build on that but I won't seal it for myself I'll actually um give them credit which I've hidden see nobody can read it so the guys at marbar lu one of the
first pieces of malware oversight to research was extreme the guys at Marvel you they were really nice writeup fire right man diem they're constantly releasing more information out to the public who else is on the motsognir so there are a couple of guys they wrote a paper looking at offensively targeting rats it's a really good paper they didn't look at the static decode side of stuff but as part of their research they figured out all the encryption schemes which means when I always put in my work together it was three less steps i had to do so they saved me a lot of work are there any questions yes
so there are you can't really have a remote choice that doesn't carry its own configures there by native their reverse connection so the only way you do that is if you have a listener so I drop something on your box and then I have to actively connect to you and then I connect to you when I'm telling you so you're only listening so all you have to know is a port number and possibly a password to authenticate my connection they don't really do that the way rats were designed is they because of the way reverse connections work these things sales straight through firewalls because we implicitly trust the inside to turn that all the way through rather than
blocking walking to the way so you could I've researched 132 rats I have yet to see one that doesn't do that with one exception there is a family of rats that are PHP based so they launch a web interface web shell on your box rather than a a remote connection basically it's the same sort of principle it still has to contain all that's all the sort of information
yes so Zeus does this so Zeus isn't a remote access Trojan it's a botnet although it has the same kind of fun counting what that does is it has a single look up and what it does actually goes and collects its config file from out on the internet so it knows that my config file is one two three dot which is sat on this URL so it just doesn't get requests for that pulls it down then will decrypt it in real time on the box but again when we start to analyze this we can pull that first request down it's got to go out somewhere it's going to pull something down now I can check my
logs see if that files ever been pulled down I can look at the box see if that file exists on the box and then that can tell that way so there are ways of doing that erm there are a couple of go strap ghostwriters of fluid flows Randerson they're very similar the the actual config file is just a single base64 encoded line at the end which is just a URL and he goes out to the URL pulls down the config file and parks it and then it stores into memory the good thing about that is it uses something very similar so it saves that that config file on the disk now so if I go
in as an interest bonds handler I can i can grab that config and again it it's always got to interact it has to do something so as long as I can figure out what it's doing in the first place then it gives me something to pivot on so I can start blocking if I've got IDs or IPs I can block those if I've got fire warlike say suck i can stop implicit bucking those as well the more how am i doing for time as this is not my audience I won't bore you going through a technical demonstration unless anybody really wants to see a talent for demonstration I didn't think so apologies that you got me instead of who
you were really hit see but thank you very much