Passive and Active Defense by Jason Maynard

Show transcript [en]
okay so Jason Maynard from Cisco it's gonna do a talk on active and passive defense we also understand that there are some Nate's students who are coming into this so it's just a show of hands are those Nate's students here welcome great good okay so let's get this up alright everyone can hear me yeah awesome all right so I'm Jason Maynard I'm focused on the technical aspects of Cisco cyber security portfolio but really focused in general around security not product specific great so anyways when I was thinking about what I want kind of present some of the challenge I see when I'm out and talking to customers was that there's a big focus on passive defense right and we'll
talk a little bit of what what passive defense is there's not a huge focus on active defense so today there's gonna be a little bit of everything for everyone right so if you're in leadership there's some things that you might want to take back to the team if you're you know more on the geeky side we'll talk a bit about net flow and maybe DNS analysis and and how that might help you determine what may be an adversary you might be doing in your environment obviously that's only one of many techniques that you can leverage but it's a good it's a good way of capturing some Intel in your environment right so if you know if we
have lots of people in here that manage environments I would love to see and I'm not sure if you guys are willing to say but how many people actually ingest NetFlow or IP fix or s flow or J flow and actually use that not from a network perspective but use it for security right so we're building these defenses or traditional defenses to mitigate risk but yet you don't know what your networks doing right day in and day out so we'll talk a little bit about that today as well as what DNS can do and provide you so real quick and you talk about operational and informational technologies right there's a big focus obviously on IT a lot of the times but
operational environments are now being the supposed businesses want data right today you can go and order food right and watch the driver come to your house right the best I had as a kid was 20 minutes Domino's it's free right that but you never knew where they were you were just hoping they'd be here right today you guys are seeing things real-time people know when you know consumption for power is high or low so we'll talk about each of those because they're both important and they both require security both both passive defenses but also active defenses as well we'll talk about a hard exterior soft interior I've seen that still a lot ooh with all of my customers that I talk
to you day in and day out right we've got this hard cross but we got this really gooey chewy middle right we'll talk about passive and active defense very high-level the differences between the two and then we're really going to focus on active defense itself so that's where we're gonna look at threat intelligence right asset identification network security monitoring Incident Response and then finally threat environment and manipulation right so what do we take from the things that we learn about the environment and then use that to feed back into our passive defenses right so we take that knowledge and then we feed it back into passive defenses to start mitigating that risk so when you look at operational and
informational technologies they're both important right so if they might be treated a little bit differently so ot you know it's got engineers right and you know real engineers with the ring right and then I t's got engineers without the ring right hey a lot of times not to say you don't have a ring somebody might have a ring but they're very much the same and they can learn from each other right IT can learn about the operational requirements right and why it's important to make sure availability is core right integrity is second and confidentiality is third if you were going to rank them you could talk to people that will argue all day long that that confidentiality and
integrity is just as important but without availability the operational environment and will suffer right where IT you've got CIA right confidentiality integrity and availability right if you were to rank them again you could talk to someone in IT and say availability is just as important as confidentiality but if you were to rank them that's typically how it goes so now we've gotten some controls between ot and IT but how many organizations are actually doing active defense in the operational environment and I'm gonna say very few right I talk to a lot of customers and the problem with this is Oh T is now it used to be an island right all by itself but now we've got bridges into that
Island right they're not segregated anymore so we'll talk a little bit about those challenges as we go along hard exterior and soft interior right so you got DNS layer protection you got firewalls you have IPS is right you might have some sandboxing technologies right but at the end of the day you've got this nice hard crust but in IT for example that crust or that perimeter is still required but we have challenges because now we've got cloud right we've got mobility so if you're securing an organization you're putting millions of dollars in defenses on the perimeter and you let an asset go home and plug in to the network and come back in are you
putting the organization at risk I would say you are and why wouldn't the same controls you have on-prem exist off brown why are we taking this approach that once you go off brown those controls don't matter anymore right those controls should follow you at least to whatever the technology will allow you to do so when you look at soft and interior there's things like localized malware right something that gets plugged in a USB key for example right gets plugged in starts to propagate you have network behavior how many people here baseline their network right some right but a lot of people don't even know what the communication channels are between their devices you are a hundred percent reliant on your
defense of technologies to tell you that something bad is happening in the environment the one thing I'll tell you doesn't matter what vendor you leverage nobody's going to give you a hundred percent security you will be breached right and you want to have tools in place that are gonna help you during that time so you got supply chain a lot of people don't even think about it so we've seen the adversary go and compromise the website manipulate the firmware upload it and then the customer goes to the website downloads the firmware installs it on their asset and they're compromised right so you want trust throughout that whole lifecycle from a supply chain perspective vulnerabilities right how many people
patch liars okay we all want to patch right everybody in there throughout my entire career we've talked about patching but we're still seeing compromises of vulnerabilities that have patches that are available that haven't actually been pushed out why because the business doesn't want to shut it down it's not that you guys don't say patch it's important of course you are right but at the end of the day the business is driving when when when I first started someone say can I do this no I was god it was awesome like you guys missed out some of the younger folks right you know what I'm talking about can we do this no you're never gonna be
able to do that right that's no longer right the business comes in and says this is what I want you to do make it happen so it's changed so you got things like sanction devices unsanctioned devices how do you know a printers plugged in Michael and and Zoey Freight they've talked about printers but do you know what printers are plugged into your network do you know when the phone's plugged into the network do you have a dynamic understanding of what the environment is doing at any given time if you're only a hundred percent reliant on those action mechanisms you better have them everywhere right and now you've got a costing issue so anyways the stand and
we see this a lot we still see this a nighty but you see this a lot more and ot right if you talk to engineer and say why do we need to do this right we've got this crust this crust his heart right you can't break first off the crust is never hard 100% right we already know that never mind the challenges with internal if I wanted to compromise an operational environment what do you think I'm gonna do well maybe what I'll do is go run to a field location get a one gig USB key put some good stuff on it and drop it at the gate and drive away field engineer comes up and goes oh my gig you've got a
ski try this is fantastic it's my lucky day right goes in plugs into the operational environment plugs in that USB key and back right and I know most people are focused on security here and you probably all sit here and say I would never do that yeah you would I just need to change the size of the drive right one terabyte oh I know what I'm doing I got this right so there's some challenges there that you got to think about so passive defense is focusing on deploying and maintaining the the controls that you put in place right ultimately reducing risk active defense is now monitoring the environment right for which you're responsible for and a lot of people
don't really understand what the environment is that they're responsible for you know what has switches and firewalls and routers and you know printers and phones but you don't truly understand the extent of all the devices that are connected to it so you're probably taking a precautionary approach to this so once you understand the environment then you're gonna respond to incidents right and hopefully with some level of accuracy right so you're not chasing the rabbit down all kinds of different holes and then what you're gonna do is learn from that and then manipulate the environment right so you're gonna take that information you're gonna feed it back into those passive defenses to start mitigating risk right
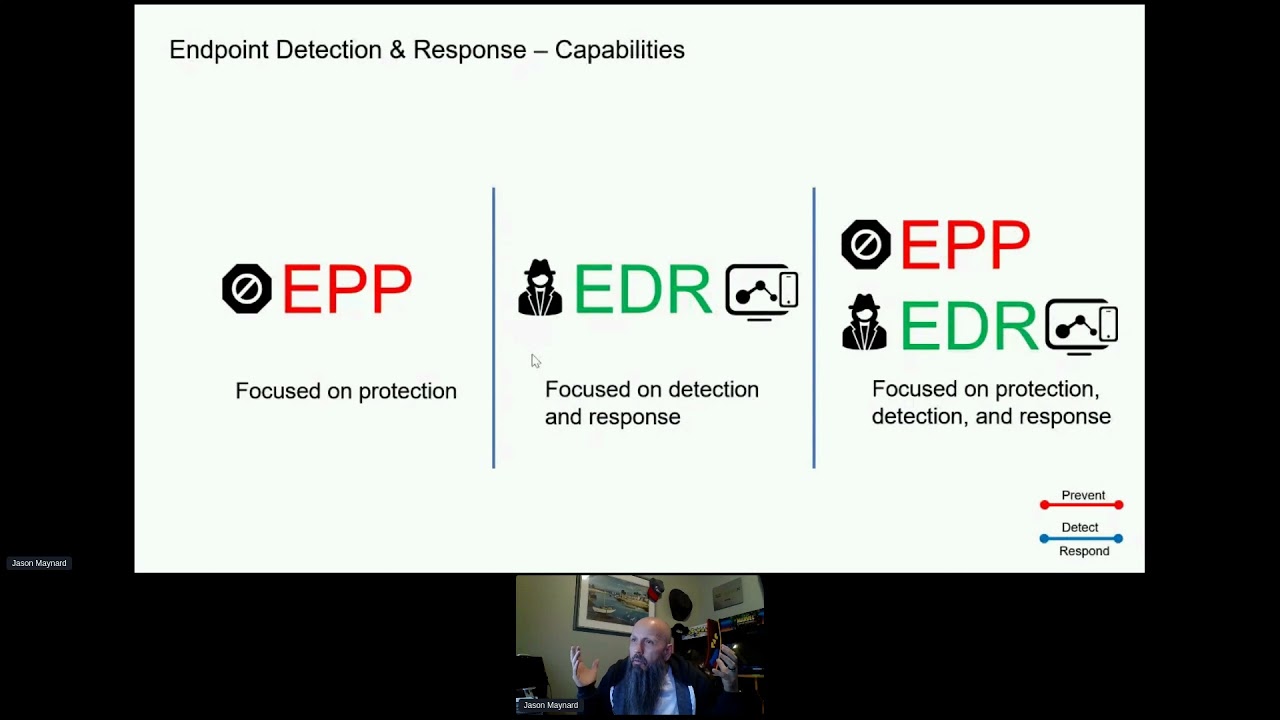
and of course you know it's a cycle right so you're gonna learn every time you're gonna evolve right as you go along so when you look at passive defenses right we've got next-generation IPS is next-gen firewalls right next-gen endpoint I have to use the word next-gen I apologize right but that's what people use to understand is that when I go in and I say oh yeah we've got IPS or they've got IPS they go oh it's not next-gen it is next-gen the problem with the next-gen label and everybody in this room should challenge it is it never expires so if I was an 8 year old company that developed an or was innovated and created a next-gen
firewall yeah there's core components that make up what they call next-gen but if I did that eight years ago and did nothing didn't change anything and eight years later next-gen firewall right it's still a next-gen it never expires so next-gen doesn't always mean next-gen right because then is it next-gen next-gen or is it next-gen 2.0 right there's some challenges with that term in my mind anyway you got DNS email security web content again just gives you an idea of some of the passive capabilities when you look at act at the threat of Defense there's four components and this is from sans right so you got threat intelligence consumption how many people take in threat feeds probably a lot right even
if you don't even know you take it in most of your security technologies is pulling in threat data right you're gonna have the next step would be things like network identification right and this one's critical this is the advantage you have over the adversary you know your environment they don't know your environment they can assume but they don't know your environment so the more you know the better that you could defend against the adversary right because they've got to come in and learn incident response rate obviously is a part of it and then threat environment or threat and environment manipulation so we'll talk about one of those so anybody know Locard's exchange principle anybody so basically
if you're a criminal or an adversary so if I'm an adversary and I enter an environment and I do nothing or if I enter an environment and take something there's evidence left period right so it could be a fingerprint it could be blood stain it could be a hair follicle right when it comes to things like information technology right there could be a CPU rise there could be increased network traffic there could be interesting DNS calls right so there's evidence left you can't get in and oh without somebody having some traits now the issue is do you have the mechanisms to capture that and then make sense of that right so threat intelligence so there is a life
cycle right so planning indirection you just don't consume intelligence for the sake of intelligence right you want to have a plan what are you doing determine those requirements oops collection where do you collect now what's interesting here is if you know your network you're gonna know where the best parts are in your environment to collect that data right but if you don't know it it's gonna be difficult right and everybody does perimeter yes you have IPS but how many people have security from the campus network into the data center well there'll be some some bigger organizations here I know have it right but there's a lot of organizations that don't have it what about what happens when you go to the
cloud it was interesting we were talking to students today or just before this and they were talking about what about AWS what what do I need to secure my instance the same thing you need to secure your stuff on Prem nothing changes right it's just a branch office if anything right you still need the same controls so you want to know where you're gonna place this where you gonna get that IP fixed data or flow data right where are you gonna put your IDs or IPs cross processing and exploitation so taking binary data and making it into something usable for humans right and that would be asking so that's what you're gonna do in that phase and then
you're gonna analyze and then productionize it right so that this one's important because there's two components this this relies heavily on analysts analysts are never gonna go away for a long time from a security perspective yes we've got really cool tools that does a lot of stuff but you still need an analyst to really truly understand the threat and what it means to the business that you're protecting right you need an analyst to do that that's not going to go away so don't worry about the technologies it's just gonna allow you to focus better but these also have to map back to that planning and direction phase and then you have output right so dissemination
and integration so the the actual output of that data that data then is gonna be potentially share how you share that data we're gonna talk to about that in a minute but again it's got to be something meaningful right it's got to come back and this is where evaluation and feedback comes back it's got to come back to that planning and Direction phase right why was I doing this in the first place so once you get that established then we start looking at intelligence so open source information can anybody tell me how you defend against that anybody want to take a crack come on somebody be aware that it's out there right but you can't stop
it you could put some controls in place to minimize the amount of data but if I was gonna compromise an organization I would want to research it would I research it by doing an nmap scan against their servers no right I go to job boards I'd read about the company a little bit I'd find out oh wait a minute they're hiring they're hiring oh and they need skill sets X Y & Z that's interesting so what do I get from that two things either they're growing the team or they're short-handed so not only now do I know the technologies that they use they don't have enough people potentially monitoring those logs right good information I can scan I can have as if
I scan them by leveraging things like Showdown I think somebody mentioned that earlier today right I can look up exploit the databases for exploits that I might finding with the devices that I just discovered and I've done that right so if you look at the city of security because I thought I'd better not put any real city on here because they might call me afterwards right say hey would you do that but they're building a new facility which is connected to the city of security Network right so we got this brand-new think public sectors really bad or good at this right because the problem with public sector in general is people want to know where their tax
dollars are going so you've got to go oh look at this is what I'm doing right oh sorry you're gonna have to replace that I think it's broken but you pound the chest right like I'm so awesome look what I'm doing 82 million dollars for this section of highway right but if you go there's a bunch of PR documents that would be released right it'll talk about who they partnered with what companies are involved right even people to communicate to so maybe I can start actively taking that open-source information and start actually probing individuals right and we've seen this in the real world product research and around advisories and alerts right once I get an advisory or alert then I go
look for things like vulnerabilities and then I go look up an exploit database and bang I've done I've at this point done all of that without touching the company I've got a plan I know where the weaknesses maybe they're short-handed they're expanding their environment right a lot of great information now again defending against that is tough but knowing is obviously very important right knowing what's out there and you know what me included right when you're on LinkedIn your job description look what I've done right in my career right so it's everywhere oh wait we got to show that one right but that the adversary is getting all that information so as much as you want
to put that information out there for the general community the adversary is also using that information and potentially against you so we look at external threat intelligence there's all kinds of sources right there's ice axe right there's the Canadian cyber exchange right I think that's a paid option but I'm not a hundred percent sand Internet storm center right vendor threat feeds and blogs and you'll get reports etc and this is just an example of some of the intelligence that you might get from a vendor or from a third party whatever right but you're gonna get some IP addresses you're getting it maybe domains files directory hashes in that right so what do you do with this
information who's who's on blue team here la lot so what do you do do you go and look at your firewalls to make sure that those are in there right do you ever use this information to find out whether or not you have systems internally actually making the requests outbound to those destinations or do you go ahead block I'm done right well that's what we see a lot of right they take that information they block you said note we're good we're secure right well in the meantime assets were already compromised there's residual there's communication coming from those devices and yes maybe you blocked it in the firewall but what did we say earlier those devices are mobile
right they just walked outside the environment plugged that in that's coffee shop right any coffee shop connect to the Internet and now there's a CNC channel because they're no longer protected by the same mechanisms that you had at the head office right or in the corporate environment internal threat intelligence how many people generate internal threat intelligence remember this is taking a step beyond passive defenses right so now we're looking at things like endpoint events we're looking at traffic analysis right flow data you've probably got lots of it you just got to go turn it on right you might do full packet analysis right DNS analysis user behavior user information might have honey pots right and maybe you even do
reverse engineering around malware right and again you might be leveraging tools to do that but also the analyst is very important in that equation but a lot of people don't look at that internal side they're always looking for threats and information from from outside but they need to understand those that that information internally as much as and even more than what they they they do externally so it comes to sharing intelligence you may want to classify right so everybody's all about community all about sharing right I've got my own thoughts about that but but we'll leave that to the side I think it's a great thing to do right the more we share the better everyone's protected but you may
not be able to share certain information so you want to classify what you're sharing right so white would be something that's fine I could share it with anybody right they can use this information I can use it to share it with similar companies right and it's good for the community red might mean that you've got some interesting information in there that may expose you right that you may not want to share that information out so you want to classify it and then you may want to use a format to be able to share that data to some of your passive technologies right so sticks is the format taxis that the transport to get that data to other
platforms asset ID network security monitoring I think this one's the big one right not to say any are less important but this this section I focus on a little bit more and then at the end I talked a little bit about what you can do from a manipulation perspective so how many operations rooms look like that for security lie and lying like it you know it hurt didn't it I know it hurt the reality is is that this is you guys do a phenomenal job it's very hard to do it there's all kinds of reasons why you might be blind in somewhere that's right the bottom line is is the end-to-end is very difficult and I
talked about this earlier how many people could tell me what servers are in their in their data center how many people could say I know it's Windows its Linux its its patch level right application it gets hard right but even just knowing the systems on your networks valuable for datacenter depending on the size of the organization some of you guys might say yep 192 168 1 dot 0 slash 24 those are my servers we're all the windows shop we know what's going on ok all right well what about the campus don't say you don't care right because you do because that's probably where the attack is gonna come from right hopefully you fortified the data center but again
nothing's 100% so anyways how many people can tell me what's on the campus probably very little right some people might write depending on the technology and some people might have a static list to be able to provide that again that's really not good it's like a pen test or a pen test is only as good at the moment that you do the pen test right it struts today it's stretched version to tomorrow right oh and then it struts version 3 and it's stripe right so it's only as good as the time it's valuable information you need to do it but it's it's a little bit static right same with asset inventory of your environment right it might be a little bit static
what about this how many people allow this on their network honestly how many networks can I plug these into and you wouldn't even know it was there right that's probably the bigger question because the reality is you might think that you're ot environment secured go to the lunchroom because somebody brought in their Smart TV plugged it into a network jack that happens to be there that is tied into ot maybe he didn't stop outbound communication from ot it's got its way into the business that I'm saying this is not right and now they're watching Netflix during the day right during their lunch time right you don't know so how do you protect that turn on all the signatures
yeah well now you have a box it doesn't run right so it's got to be dynamic you got to know what's going on what if you have CT scanners Oh we'll just throw a a VE agent on it or malware oh wait the vendor void warranty you can't do that right do you know how many of those are plugged on are their mobile are they moving around in the environment being plugged in right there's all kinds of challenges with trying to secure that and then if you look at a SCADA environment no I I would say out of every environment this environment you should have locked down and know exactly what's going on right they're fairly static right they don't
change as much as you see IT changes but these are all challenges and if you miss one of these right game over right because that's all the adversary has to define is one see as security practitioners you can be batting down hundreds of thousands of threats right you guys are awesome your team is you're awesome nobody else gives a right they don't they don't care how many times that someone said oh my God look at all the stuff you've blocked this is phenomenal no never you'll never be remembered for it you know you'll be remembered for how you handled the breach right well how'd they get in well I don't know there's the stupid TV right it's gonna be hard right
to be able to talk intelligently it's gonna take you a lot of time to figure out what's going on and you might figure out what's going on but that's what you're gonna be remembered for and who are you gonna hire the one that was compromised that made mainstream media as the seaso or somebody that may have handled a breach because nobody not everybody's gonna have to handle one of these at some point or do you handle something or you hire somebody that handled the breach well right still go compromise there was still impact to the organization but it was done in a timely manner they had processes and versus maybe somebody else that's from compromise and again it doesn't matter
you go for an interview and you say uh-uh I told them everything nobody listened to me listen the other person that didn't have that who do you who do you hire you probably take the site of caution right because if you hire the individual that got breached and and maybe they did do all the right things if you get breached again what do people say well would you hire them right so you'll never be remember for how many threats you block or attacks that you block so network security monitoring so you got to start you're gonna want to collect information right this is why then understanding the network's important because that's where you're gonna put your choke points or
hotspots right places that are important for you to to capture data and then you're gonna need tact that right and that detection is gonna be a variety of different technologies they could be open source technologies commercial products doesn't really matter but at the end of the day you're gonna need things like ids/ips right if you want to do some prevention at the same time you want to baseline the environment if you could do that you're gonna want to take flow data maybe you write and then you're gonna analyze that data and then there's going to be two results that come out of that one is going to be you're gonna kick off Incident Response or the other side is it's a false
positive we're gonna keep going back through that loop right so network security monitoring collection and detection you've got spam Mirror Mirror ports taps etc right IP fix mention that but that could be as flow J flow net flow right if you want to talk some brand names firewall event logs window event log sis logs right you may aggravate that data somewhere right but but this is all going to help you on the the collection side and then the detection side we talked a little bit about that already right you're gonna have maybe idea ass you'll have you know maybe ZigBee for some of the wireless stuff that you might have right you can't forget about that right just
because you're capturing data around Wireless right you're gonna miss anything that talks as igby so again it's important to truly understand that environment you might have host ideas flow data we talked about baselines etc so now when you're collected the data you've got some detection capabilities taking place you're gonna start looking at the analysis portion of it this is where skills come in right human skills right not just technology technology will help you maybe get rid of some of the noise but at the end of the day you need skill sets so file analysis you have DNS analysis flow analysis packet analysis right time line about analysis right so we want to understand the timeline of
events that took place to be able to correlate that information so we're gonna focus on flow and DNS right these are two examples of many right and how you can actually start using information to piece together what might be happening so how many people here can pick the bad packet out of that right well I made them read so it makes it easier right but who knows right that's what's on the wire that's encrypted it's even worse right so it's very very difficult there's all kinds of stuff happening on your network all day every day right we talked about the little device earlier that they put in line right the thing I'm starting to think
about how do you mitigate that forget about the the technology that should be mitigated but how can I get that risk from a network perspective potentially right but they're gonna leave potentially evidence right so I want to capture that data and that data could be you know bad Geo's it could be recon it could be compliance things that take place I don't want my business Network directly communicating with the OT environment in lower levels right if if something like that happens I want to know about it you know worm propagation exfiltration all of this you can get from flow right now you might need some technology to help interpret it you might need an analyst to help interpret
it probably get any both right but if we look at it here's a baseline flow right so get a host a tox active directory in DMS my talk to a print server at god forbid write an email right and then it might talk to the internet and there's gonna be deviations in that flow right and you're gonna have some baselines to understand what those deviations look like right but what if there's an unknown threat when I say unknown I'm saying that our technology's not not Cisco's I'm talking our in general as an industry hasn't been able to identify the threat it's unknown I apologize Russia but I'm gonna use you as the example right but if I had some
communication that's taking place that's communicating to Russia I was actually in Vancouver yesterday we had an individual and this wasn't part of the discussion but we did talk about Russia and I said yeah I use it once a while but I sometimes I try not to because you point out a country and somebody gets upset and he's like and he's Russian he's gone oh I've went through this ransomware act experience where I called them up and said I'm Russia they were willing to give him back the crypto keys because he was Russian but he needed to give us passport and picture and prove he was in Moscow right to get the keys right so he didn't get the keys but he
was Russian they sounded Russian but so host they talked to a server that's located in Russia we know proxying all that but forget it was just an example but that the line there is a little bit thicker and and what that represents is there's volume of traffic that that is increased compared to the other communication channels so that's interesting so that took place and now hostei is talking to host B C and D never did before now you might say well we have a technology that does chatting and that communications there yeah based on that protocol right and we baseline that but this might be a different protocol that's being leveraged right maybe they're expanding
and taking advantage of a vulnerability maybe it's okay maybe they lit up a new service and how many security teams get involved in that until it's too late right you get brought in oh yeah we're lighting this up can you secure it yeah I need a million bucks oh no you're not getting any budget we already spent it okay so now you have host B C and D they're all talking to that same server would that be interesting to anybody everybody in the room it would be right now remember nobody's seeing that because you're not capturing flow data so you don't even know what's happening and again it's an unknown threat so it's not like a blacklist at C and C right
that it's communicating with we don't even know yet so anyways that's interesting so when you look at flow it's five tupple right source IP source port destination IP destination port and then protocol so host a would be an IP address right the source port would be whatever right you got an IP address you've got the destination port an IP and then the protocol and then now whether you have technology that will help you through this process or whether you start looking up and doing your own analysis I can use that flow data and start building out something important right so that's interesting right now I get start and end time what's that gonna do that's gonna help me know the
timeline right of when the events took place it's valuable right user and device type now this could be stitched into the flow depending on what you're using or you're gonna cross-reference that right because you've got the source IP address now you're going to DHCP you're looking at that time line your cross correlating oh it's that active directory user during that time right a lot of work though right but that flow date is gonna help you move along receive and transmit right so I can get some interesting stuff from that we'll talk about that in a second round-trip time and server response time in this case because it's going to Russia you probably don't care because
your users aren't calling you saying I can't get it taken forever right but if this is an internal flow to a database back-end that return trip time is the network the entire time from sir or client to server and everything in between right server response time is telling you how long it took the server to actually respond to the request how many people are here in network and networking couple right how many times is the network the problem I started on the network's wealth systems in the network right but how many times is it the really the network right very very Sultan right but it's just black box nobody knows about so they always say
why it's the network go back to check no now I can say the server held it for 200 milliseconds I know that right again you might need to other tools to help you get that information I'm just including it to be comprehensive here URI right that's interesting data because again destination IP is one thing but if I have the URI now I could see exactly what they were calling device process so imagine I'm able now to take this information in that time line and correlate it back to the endpoint to find out what the device process that actually made the call out pal right maybe it was SVC host using NP authority subsystem that's interesting
right shut it down okay so now I've got potentially data exfiltration I'm gonna help you along right and then we've got some SMB don't worry about the source port that could be anything great I didn't fix this light but because I don't want to say SMB doesn't work that way right but anyways you've got you've got the same data points right the only thing different is the protocol and then who it's communicating but you have three of those instances right and you could imagine if this was some type of to a mechanism to propagate right does anybody know recently what use four four five anybody come on security somebody's got saying don't be shy yeah right eternal blue right
being able to propagate using SMB so we see an SMB probe we don't know what it is right so potentially exfiltration because we see volumes of data right and potentially an SMB so incident response kicks off right your team now is gonna get involved they're gonna start using this to do their analysis and we're gonna come back to that now when we look at DNS traffic there's some interesting stuff so you've got this you've got this domain right so you might have gotten this information through third party intelligence right and again this might be more of an instant response kick off but it doesn't matter right you're doing analysis and this around DNS so now I know this
domain so what I can do is I can do a who is again you might have tools that help accelerate this process or you might be using you know third party tools open source tools go into Google who is right so I've got a domain name what do I need I've got to go quick here 41 what do I need in order to register to me an email address right and then it's gonna go on top of of some infrastructure so if I'm a criminal organization I probably gonna leverage a lot of the same stuff right I'm not because remember I used maybe fraudulent credit cards to build the infrastructure so I'm not gonna do that
every single time so there might be some commonalities but now I know that that individual has had other domains and in the past they have been back I can now pivot from each one of those and I get what networks they're part of right the the maybe some reputation type information right I can also see the number of queries so I can actually say what does a query look like for a campaign marry that up to what an exploit kick campaign might look like and make a decision right I get IP addresses from that IP address I get more to means that potentially are malicious so you can see where this is going you've taken one data point and
you've went and blocked it in your passive defense and you've missed all of this right you can actually stay ahead maybe here right but we started with that original domain we've got an IP and now we've got three additional domains so that's interesting so answer response kicks off and I'm just gonna fast-track this okay so you've got preparation I didn't think I had enough I thought I was gonna be done in like 30 minutes you know when you're prepped right there's like wow I'm in trouble I'm not even and then you talk and I like to talk and anyway so preparation for instant response I kind of broke this out for folks that are in
AI IR right so this is the life cycle right so you have preparation and again you guys would get these slides you got detection and analysis you got containment great and and I'll eradicate the threat and then recovery and then you got post activity right lessons learned etc right so that's gonna kick off and then in that you're gonna have chain of command you're gonna have your incident handlers that are gonna report to the lead responder that's gonna give guidance and timelines and stuff like that right they're gonna shield the handlers from management right we all love management but we don't need management to be behind the analyst that's trying to do the work right
doesn't help and then you have the director right the director kind of filters the the entire team from the business in general but also is probably point of contact for communications right and then you've got IR external communication so you might have to go and talk to law enforcement depending on what the the breach might be internal be use et cetera so now when you take that flow now I've got host user insight so now I know the host and potentially user behavior I've got an OS device type so maybe I know some vulnerabilities exist on that asset right again I'm painting a picture here application so now I know I might know it's vulnerable right maybe
it's process hollowing maybe there's additional analysis that has to take place their IP address and geolocation domain and full URI ports and protocols application so maybe we've identified the app itself and then volume of traffic right so those are all things that I could discover from flow when you look at DNS you can see maybe you've got some date domains that were is bad but as you start painting this out you might find that hashes are also assorted associated to that domain right and as you move along you might find the download URL you might have domains that co-occur what that means is when I go to your site I might have came from that
site or this site right I might go there or I might have come from there right but that might help me tie the attack infrastructure together right I get popped by the exploit kit then I go to the CNC get the file go finally to get the corruption keys and get encrypted right so if we look here we got the email address right oh wait I just skipped that part goodnight sorry these domains all share the same infrastructure these three folks in the front here right we've got the email address Rhett registered the infection point the current malware distribution point and then we potentially can start looking at things like DJ's and potential future infrastructure that's gonna be leveraged
against us right so thread emulation of the environment so this is the final pieces right is that I'm gonna take this information and I'm gonna use it now right this team's gonna help use it and and and this is gonna be turned on and on passive defense potentially as well right so segmentation of patching so now I can maybe segment those assets get them segmented right maybe there's still some communications let's get them patched right again this this will be a decision right I'm just giving you an idea of some of the things that you might the outcomes might be the device process maybe I'll blacklist the process if you can if it's SVC host you know you're not
you're gonna have to think about what you're doing you don't want a blacklist Explorer dot exe because because that's not good right you might patch you have geo and IP blacklist right blacklist the domain develop an IPS signature that matches the URI race and I'm taking that information building a signature now mitigating breast blacklist the app rate restrict the app patching right and rate limit now in this case if this was talking to Russia with large volumes you're not gonna reek limit right you're probably gonna cut it off right but there might be another use case where you've done your incident response found out that there's no threat to the organization but there is a business
productivity issue and you want to slow down that access because it's not business enhancing that they're doing SMB probe micro segmentation right both both sides patching blacklist app patching restrict app etc the domain I can block the sender right so I can make sure that if they ever try to send us mail right because you remember they're learning about your environment too right they're looking to expand maybe I blocked the sender blacklist the domains blacklist the IPS I think you guys get it so your network your system they all leave evidence right you just got to figure out a way to capture that and store it in a meaningful manner that you can then query at some point in time and
do run analysis on it that's it [Applause]