Red and Blue Teaming and the Powers Gained! Adversarial Emulation: Jason Maynard

Show transcript [en]
you guys still up excited all right okay so this is all about red and blue teaming I just out of curiosity how many people are 100% dedicated to Security in the room okay and how many of those are blue team versus red team so the offensive side versus the defensive side so blue team and then red team yeah see look that's a bad number right we should have a mix of both um but anyways this is all about elevating our capabilities I I'm a big believer that we've been stuck with commodity based controls and what I mean by commodity based controls I'm talking about IP Shaws domains URLs right we buy a product we defend a bit against them
using those types of capabilities but they're easily uh evaded by the adversary and I I really do believe that we need to climb that ladder and this is really where we're going in this discussion today so first and foremost doesn't matter matter the vendor you're with all protections fail they will fail at some point you'll never get 100% efficacy 100% of the time period end of State we'll talk a little bit about the teams for those that may not be as familiar with some of the teams we'll talk about what is breach attack simulation and tools and then I'll go through a couple of examples so the disclaimer is this I have access to stuff um and so I've used Caldera which
is an open source technology for one example of breach attack simulation the other is a commercial product called the TAC IQ I have nothing to do with the TAC IQ but it gives you a perspective of both on how that tool Works um and then I've got um how do I test it well I got to test it against some type of control and I am at Cisco so I happen to use Cisco but you use every any technology that you have this is not a Cisco thing this is really about a defensive thing right really truly understanding it so all protections fail this is where we kind of land right everybody does this we've
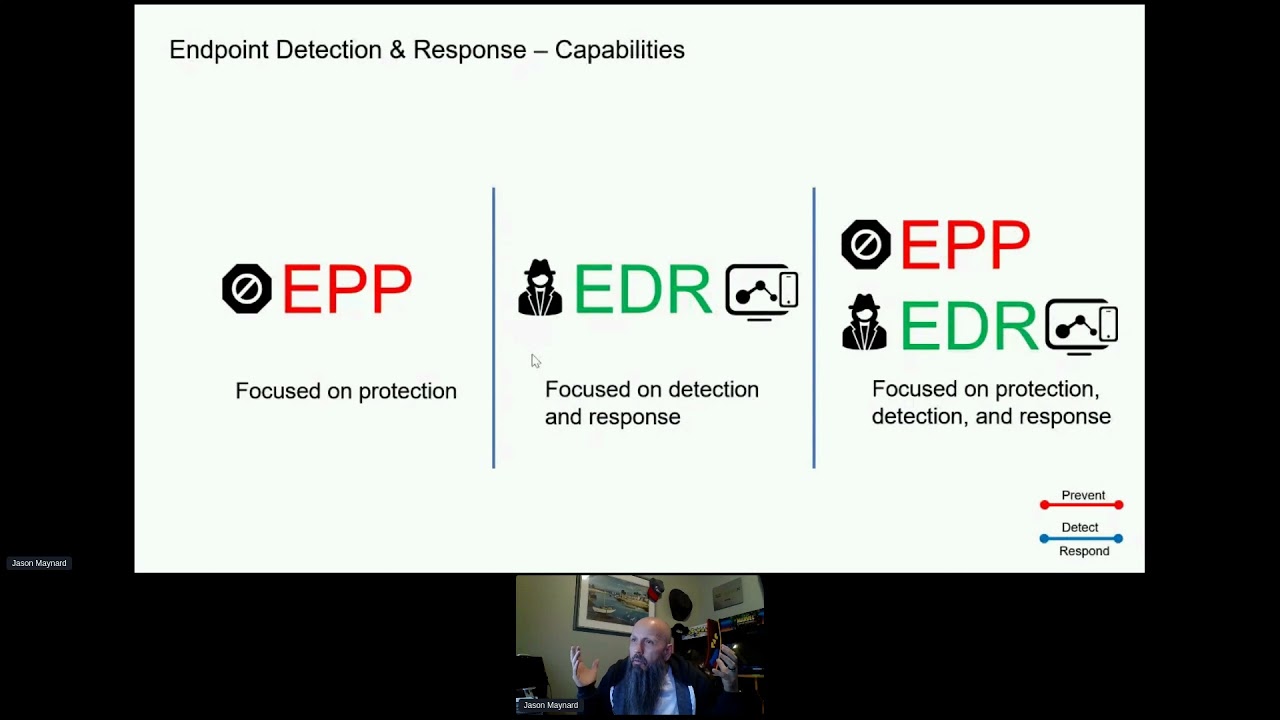
got you know workstations or endpoints that we've got some type of agent installed on them right EP at the the least right endpoint protection and then you move to endpoint detection response uh maybe some Advanced capabilities hopefully that that you're there today but there's other things on the network that you can't install an agent on so you can't depend on that control 100% of the time for everything and nor can you depend on it because it will fail so you have to assume that it will fail at some point in time and if you're lucky enough you might have things within the network that provide visibility so for example Billy's talking like this today and all
of a sudden he starts going like this he does that a lot if you know him right but he's starting to scan the whole layer 2 Network and um can you detect that well you might say yes I have an endpoint product that can maybe catch that but if that fails you might say yes I have a networking component but it is all about those layers and then you've got workloads right or servers those servers are going to have control points put on them as well maybe endpoint protection maybe some type of application layer control um doesn't matter right it could be cloud or on premise but you're going to have some controls there but what happens is the
adversary gets in we see this time and time again right and you might think you know what I've got lots of pieces maybe they operate and integrate well but we still seem to fail and we read it not even weekly like every two days there is a big one right um and so what happens is they get on one asset and they continue to move within the organization and then eventually you know it's game over right we we end up failing but in order for the adversary to do all of these things there's stuff that has to happen in their favor right there's certain things that they have to do and maybe if we focus on those layers
I'm not saying dismiss the commodity based controls but maybe if we TR truly understand how the adversary may act within our organization maybe then we can identify the areas of opportunity to mitigate risk and so there's some things around miter attack framework that we can certainly Elevate our capabilities and understand the tactics the techniques and the procedures that the adversary is going to uh leverage in order to be successful so we don't want this none of us want this and it's interesting recently I think a casino paid $15 million not for the keys to unlock the ransomware but I think it was just solely so the data wouldn't get released to the public right pretty good
paycheck so my point is is that we can look for areas if they're moving laterally within the environment and we're scared that we might get compromised maybe we should understand that and maybe prevent the ability for the adversary to move laterally within the organization or put a lot of detection and prevention capabilities in place to to minimize our our risk and there's Nuance when you start talking about miter attack right there's there's Nuance in the way that you have uh the ability either to prevent or detect some things you may not be able to prevent 100% of the time for example if they leverage Powershell within the organization and you need Powershell for other things and you can't restrict its
access for some reason then that might be acceptable risk there to say we need that in place the advis AR may use it but we want tooling that would detect an adversary taking advantage of it because we can't turn it off so the goal here is really to start moving towards threaten forign defense and I I really do believe this buys us two things as Defenders specifically one is um the first thing that it does is that if we make it difficult for the adversary to be successful um they have to create more noise and if they create more noise that gives my other tooling a chance to detect their their presence in the environment and it also buys what I
believe is time based defense it gives me time if I make it difficult for them to be successful and again that gives me an opportunity to detect them in the environment so everyone hopefully is familiar with the Pyramid of pain and and if you're not uh certainly look it up but the Pyramid of pain kind of the the whole goal around that is to suggest the pain invoked on the adversary if I have these indicators in place uh to make it difficult for the adversary to be successful so the bottom three domains hashes and IP addresses are typically a symptom and they're pretty trivial for the adversary to to overcome for example if you have an IP address
and you have a technology stack that says oh I'm going to block that IP the adversary just needs to change it and guess what they bypass your control same thing with the domain same thing with a file we want to move up higher in the stack and we want to get up to where we think it's very difficult for the adversary to overcome and that's tactics techniques and procedures so TTP and miter is a great tool to allow us to valuate our our organization I talked about this last year I'd be curious to see how many people move forward with it but really do a gap analysis of of what we uh identify as the adversary that
targets our vertical and these are real world examples uh these aren't Pie in the Sky stuff these are things that happen with research paper supporting it so we know how they act and then addressing that with the defensive capabilities where we can and then identifying the gaps that remain so if you're not familiar with miter they've been around for a long time you might be more familiar with common vulnerability exposure database these are the folks right they created the attack framework in 2013 um and it's really focuses on the adversaries perspective The Who their goals the why and the methods the how and ultimately if you understand this you can really truly start building a
defensive posture that makes it difficult do does that mean you're going to be 100% immune to every threat no absolutely not but it's going to buy you the time needed hopefully to prevent bad from happening so I'm not suggesting that those lower what I call commodity based controls are no longer important we still need to do that get short of a lot of noise so we want to make sure that we continue to do that and and then continue to rise up that stack and get to ttps really understand the adversary I'll get more in this in a moment um you need to understand the adversaries right and and like I said there's Nuance in
our ability to not only prevent but also detect right um and then breach attack simulation which we're really more focused on today is again elevating our understanding of how the adversary operates and then testing our controls and seeing what the outcomes look like and maybe we ident identify a gap that we can address you're not going to address every single Gap but maybe we identify a gap that we can address but some of the out out uh the things that you get out of it is the teams actually acted as the adversary and defended against that adversary so they've seen it been there so if it does happen it's not New To You Right you've you've been
living and breathing that and so there's really two teams and I'll go pretty quick here but blue teams the defense side right uh they they're the on that defend the organization against uh Cyber attack right they're the ones that build up that security posture then you leverage certain toolkits from vendors right build it and piece it all together that's a whole other story right but that builds your defensive posture and there's people in process that should be part of this equation as well it's not just technology it's all about risk reduction hopefully you got some orchestration and Automation in place as well they augment all aspects of Defense right machine learning and artificial intelligence again I'm almost thinking it's
interesting how this AI there's certain terms out there that become more marketing than than actually like value right one of them zero trust machine learning AI right but AI can provide us a tremendous opportunity right good data set and we can drive specific outcomes but I'm not a big believer in those marketing terms right zero trust is a framework not a product um so so some of their activities user and device monitoring Network Cloud workload application Network detection and response endpoint detection and response vulnerability management and it goes on right patch management incident response forensics and and security operations management and awareness training then you got the red team these are the offensive side and and we've
typically you know they've operated a little bit in silos and that's where purple teams come in and I'll talk about that in a second but they assess the security pock posture right hopefully simulating real world attacks things that the adversary are going to do and they're going to leverage all kinds of techniques um methodologies to identify those weaknesses and then they're going to create a report at the end to say hey look we're able to successfully do X right and hopefully the defensive team the Blue Team takes that and start building the defensive capabilities in the organization and so things like vulnerability scanning pen testing social engineering physical security wireless network testing application security exploit development and breach
attack simulation it's interesting because you got USB keys I don't know if you know right and you know what they know everybody here is not going to plug that in but guess who is anybody with kids right they're going to find it and plug it in for us or or I mean the the the organizers um but anyways um and just a little fun on the USB key but threat intelligence research as well purple teams is not a new team it's actually two teams coming together and there's no secrets here right we're sharing intelligence across both teams you're going to know what I'm going to do and I know the defensive posture that you have
the goal in this is really to start identifying gaps within the organization it aligns to the business collaborate between the two teams improve the overall security posture uh of the organization is the ultimate goal right so understanding the adversaries by leveraging cyber threat intelligence you want to emulate the tactics techniques and procedures you want to identify and remediate those gaps during the emulation process as well anybody do breach attack simulation I'm just curious yeah kind of not now yeah so Kare actually if you haven't played with calare very easy to deploy in your own home lab you can actually certify I don't even think there's any cost to certify you just go through and you kept capture a bunch of flags you
submit it and you get a certification on blue and red I think both sides I think um but anyways uh yeah so it's open source and it's it's actually created by miter so certainly leverage that I'm I'm glad to see that you're even exploring it so this is a good thing and I do believe we all need to get to this level right I'm not saying that you have to build this in house maybe you just once a year twice a year something like that you bring in somebody to do this or work together with somebody but I do think that we need to change the way that we defend our organizations and so the Cyber kill
chain there's certain things that have to take place right reconnaissance right what are the IPS that I'm targeting and some of this I can and can't control right if I can find your public IP block on the internet how do you hide that from me can't right can't do anything if I'm creating an exploit to Target of vulnerability that happens to be on your system how do you stop me you can't I can do that all day every every day well I mean you could patch the system but you're not going to right um weaponization delivery exploitation installation command and control and then actions on objectives now I I've heard people say it the other way but I do believe the
adversary has to be right every step of the way here in order to compromise your environment a Defender only has to be right in one of them now a good adversary might have three or four ways to accomplish a task right but if I can stop say weaponization or delivery right if I can stop the delivery then how do you move forward as an adversary right if I'm not going to click something nobody's going to click anything right and nobody's using USB's handed out at a conference how do how do I get that payload into the organization now stopping it 100% of the time is a whole other ball game right but there's mechanisms or tactics and
Techni or sorry techniques that they're going to do to deliver that payload if I can prevent that then they're not going to do exploitation installation command and controls and actions on objectives right they need those other pieces to fall in line so I do believe Defenders have the greatest opportunity It's just tough so a little bit about breach attack simulation right it provides a testing methodology to simulate attacks against the organization it helps identify any weaknesses uh and vulnerabilities across the entire attack vectors that may exist and exploited by the adversary we want to determine the security Effectiveness and the opportunities to close those gaps in people and process and Technology not just the technology side
right there's an opportunity to say how would we go and move this through the incident uh response life cycle as an example right and then reconnaissance so if you break this down there's certain things that are going to happen for example reconnaissance right they want to figure out and locate the opportunities within the environment um then you're going to do some scanning of those systems to find out that where those weaknesses exist and then eventually exploit them right so reconnaissance you've got vulnerability scanning and then exploitation that takes place privilege escalation moving from you know maybe a standard-based user into a privileged user that I have full access to the system maybe then dump memory uh to
harvest credentials as an example and then really once I land on a system and get access what do I need to do next is it it did I win the game as the adversary no I've now got to guess what poke and prod and figure out my next move so that life cycle almost starts over again right they're scanning the network they're looking for weaknesses they're trying to find an exploit that they could leverage to take advantage of that vulnerability so they're making a lot of noise they're not doing this stealth they might be uh uh do this um as slow and low as possible but but they're there making noise we just got to figure out where that noise is and
make sense of it and then data exfiltration once I get into an organization and I start harvesting data what do I typically do with that data do I just send it from that machine that machine that machine that machine that machine out to my uh system in the back end or box or wherever I'm dumping that data to do I just do that or do I have a central system with enough capacity slowly move the data into a central system and then slowly leak it out of the organization over time probably and then reporting right you're going to have some reporting at the end of this so think of it this way we got reconnaissance initial access execution
these are all tactics and adversary might leverage and then privilege escalation so we popped a box not a big deal because if I can scope or minimize the overall scope of that uh that attack then the adversary has very limited options to move around in in the organization then lateral movement takes place I need the network in order to drive that outcome I can't do it any other way there's no secret way of doing it the Network's going to get some activity can I detect it that's a whole other ball game and then you have uh maybe data exfiltration privilege escalation out of their system so again they're just making noise all along that path and these are all based on
identifiers I I like to call them T identifiers I don't know if that's formally what they're called um but they're T identifiers and they also have uh the software identifier so s identifier or mitigations so M identifiers um and so that means that we're all talking the same language there's no confusion when I say ta 0043 whether you know it's reconnaissance or not when you look it up you're going to know it's reconnaissance so there's no mistake here so some of the tooling as I mentioned right there's a variety of tooling out there's commercial again I have no skin in this game whatso ever attack IQ Metasploit Cobalt strike as examples of some and then there's some
open source stuff like Calera oasp uh and others uh available as well so again if you're dabbling you might as well dabble with Caldera and try it out and and and and see some of the results now it's interesting because when you go through some of this testing if you prevent and you do your test you may you may prevent it earlier on because a variety of things and never see the exact attack path like you don't see the details and so you may want to run in audit mode so you can see the execution in the full path and track it to see whether or not you are able to detect it and you may also find that you detect it
in different ways than what suggested by the tool that you're leveraging right so what are some of the benefits well you identify vulnerabilities so simulating attacks uh against your networks and systems again to identify those vulnerabilities and weakness nesses in that security posture overall highlights what controls detect and prevent and those that fail failure is a good thing here right because now you know um and you'd rather have this happen now versus an adversary right uh testing those controls and seeing those fail also helps you prioritize so if you go back to your 20 minutes left you're kidding oh no you you were kidding started late um yeah anyways okay and um no yeah so the
the nice thing about this though is when you build it out you can go to your leaders now with something that's informed you say I don't it's not about an xgen firewall it's not about an endpoint detection response tool right I don't need budget for this but you can you can translate this into the gaps that you've identified in the risks to the business it's a much better conversation compliance is also going to help with driving uh or driving towards this against it's with evidence-based testing that you're able to see the adversaries targeting you and the outcomes continuous Improvement overall obviously you've been there done that um it's going to help your overall uh team's capabilities training and
awareness simulation of fishing email social engineering and attacks and I'm going a little bit faster because I want to show you some of the the examples gather threat intelligence so as you're going through the process this is what you're going to do you're going to gather threat intelligence you're going to extract those techniques you're going to analyze and organize and then you're going to develop tools and then emulate the adversary that's the the ultimate goal and and there's certain things that you're going to do within those steps right determine the adversaries of Interest what verticals that they're targeting are they verticals that we fall under um identify post exploitation so do they open a shell or do Brute Force check out the
tools and aliases and campaigns the adversary so there's a little bit of work here that you're going to do and miter attacks a great tool it's not the only tool but a great tool that you can Leverage to get this information and example of that an adversary group uh uh a wizard spider and they use software like emotet as an example then you want to extract the techniques right identify the behaviors collect information um you want to identify the tactics and then move down to the technique and sub technique that they're leveraging it's a team effort we're going to work together on this and that's an example of the miter attack framework there this is Navigator this
is a tool that you can use to identify your adversaries and then map this out you can do it based on rubric scoring and everything else and then you can overlay this with your defensive capabilities and identify the gaps you want to understand their objectives their motivations and this is an example of it so this is Wizard spider as an example everything in green is what they do and if you look initial access says valid accounts persistence says valid accounts privilege escalation says valid accounts guess what I would do there's three opportunities for the adversary to get credentials of your users and use them for nefarious reasons I if I don't have MFA I'm probably going to start
investing in one right because obviously this is a weakness potentially in the organization we want to see if there's open source or commercially off the shelf tooling you'll create payload simulate the attack infrastructure set up C2 the domains um you know drive towards their motivations low and slow as I mentioned and it's a collection of both red and blue teams working together so here's an example so this one's interesting um this one is and and so this is I'm Le again you leverage any tool you want but this is a Tac IQ and what I'm doing here is I'm going through and I'm creating an assessment okay hopefully you guys can see it but it'll
be all up on the thing later too so you can see it but I'm going to create a custom uh scenario I'm going to give it a name as I go through here but it's pretty easy all you do is come in here you can search the scenarios that they have built into the platform just so you know there's an agent on an endpoint that's going to go through a Firepower device as an example and out to the the attack IQ headend okay that's how that it's going to to work and so what I'm going to do is I'm going to pick and I picked this on purpose Cozy Bear CNC and it's looking for a specific URI that
happens to indicate flash okay and so I picked this specifically because there's no signature enabled by default on the default policy within Firepower for this there could be lots of reasons why meaning that things have changed since then or whatever but I picked it because I knew it wasn't available and so I'm in the platform again use any platform you want this is powered by snort which is open source um and so I can search up cozy as an example and I see a couple of uh signatures there and I'm just going to enable them just to for fun right well not for fun but I I if I'm looking at cozy I might say you know what maybe
I want these enabled after I've done some research now you don't want to just enable signatures for the sake of it I'm not suggesting that you want to understand what the threat ve the the the the threat is and understand how it applies to your organization and enable your signatures as required but the point here is is that I'm going to go ahead and enable this and just based on a little bit of timeing I'm just going to fast forward just a bit here so I blocked this out I've enabled it to make sure the rule actually has got that policy as well so that's fine I'm going to go to unified events and then I'm just going to give this a name
here and then once I give it a name I'm going to grab the endpoint and the endpoint then is going to go ahead and run this test it's basically going to go out to a head end with that URI attached to it and what's going to happen is that it's going to fail meaning that I didn't prevent the attack okay so there is some integration with the attack IQ but if you want to learn more about that product you C certainly can go to their website but what I'll find very quickly as I start going live here and as this attack continues to move through its process I see that very quickly I know this because I happen to
know the environment pretty well that that flash video is that that actual um attack okay and I didn't identify it why because I don't have a signature for it and I thought I want to do something a little bit fun with this as well and so I thought okay that's fine let me look this up what is the details around this and there's a particular URI that's involved right it looks for this you know four or player. sswf right and there's a full uh URI path there that I can pull or a path uh that's part of the URI right it's command and control so I can grab this and I thought wow what if
I went into chat gbt right because that's the hot new thing today and asked it to create a snort signature for me for that particular Rule now what I can tell you is um using I I I'm a big believer I I've had it try to convert scripts over and it's not been great like converting to python to to Powershell it I mean it's good but it's not it's not perfect um and same thing with this so here I had to say so I had to play with this a bit to get something pretty close but imagine if you come in here and start creating a bunch of defaults that you knew drove the right signature outcome
but only change certain elements of that signature and it's snort so it's on a lot of different platforms so create snort version 3 signature following order in one line alerts TCP home network external network so I know what to ask it give it an a name or a message right CNC server uh security vulnerability detected flow to server so I want a connection made um URI has no value content without brackets I had to tell it that because I did it without the bracket ETS um and um and I didn't get the result I wanted so that's that right down here at the bottom here that's that web script security view player blah blah blah right that's what
I want to create the detection for and I want to run it against that okay so that's the signature and then I dumped it in here and I thought well wait a minute what if I'm new to snort and I don't even know it why don't why don't I just ask it to tell me exactly how it created it and what it what each element is I thought this was pretty neat so I said it explain each line item in detail for me because I'm new I'm learning I want to know more about it right and now I'm starting to get a skill set maybe that I didn't have and and in my opinion maybe even accelerate that skill set and
now I say okay well alert TCP henet versus external net right here's your ports here's the message flow to server so it's teaching me why how or how it created that signature and what each element in that signature means pretty cool at least I thought um anyway so so I went through that and I C I copy it from here and I had to make a small adjustment so it still wasn't perfect and I didn't play with it any longer because I I all I wanted to do was give the point out there that there's lots of tools to drive an outcome uh especially when you're doing a breach uh simulation or attack simulation so I come in and I
import it into the the the the engine and then uh I'm going to set it to block and I'm going to go ahead and test it after after I do a deploy and I'll rerun that test now hopefully it stops it but it won't stop it because I'm actually running an IDs mode in this case so let's see what happens here we'll refresh we're running the test and we should see something here any second now it's a video it should be with oh there we go okay so there it sees it would have dropped so it knows that it's in IDs mode so it's clearly stated that it would have blocked this if you were in prevention
mode but it did alert on it regardless and there's all the parameters that we just created so one quick easy way to test something like CNC pretty basic right but it's part of the attack uh framework and I can evaluate that and again depending on the tooling there might be miter tags that are associated with the alerting yada yada yada right so a good way of start testing the the uh the environment and then you can drill into packets again depending on the the technology stack that you might have in play so the next one I thought well wait a minute why don't I do this one again use any endpoint that you have uh to
drive the outcome natively Windows uh Defenders I have to dis disable it I'm in audit mode if you go into audit mode then defender's smart enough to actually turn itself back on after you've disabled it I thought that was pretty cool um but anyway so I'm in Caldera so this might be familiar to you and I'm searching up MIM cats as an example and again this will have an agent deployed on the inside it does have a client that understands uh detection response or EDR capabilities and it's in audit mode as well so it's not going to prevent anything and so I can come in here you can build these based on operations you can build these very elaborate like
everything an adversary is going to do you could have listed here so give it a name I'm going to start that new operation there is no adversary that we're leveraging and we'll go into advanced and there's a bunch of stuff that you can do in here um but I I left all the defa faults I left it and I didn't do any obic or anything like that and I'm going to grab uh the that technique and I'm going to run that technique around uh MIM cats so again I could look for specific tactics or techniques that I want to flag here I'm just going to be lazy and search for it so Mimi cats and then
there's 's a whole bunch down here I'm going to grab one and you know now that I think about it I I picked proc as the default uh I guess shell within um I could have picked Powers shell most likely um especially that it is power but it doesn't matter in this case it detected it but you might have to tweak it as my point and I go ahead and run it okay now if I quickly run to endpoint I can see the policy update that I I just forced and if I hit reload I can start seeing stuff coming in so the first thing I see is command reference remote to Red Team Tools
another uh uh refresh from there and now I can see at the very top MIM cats dump credentials but if I go back through the process I start seeing multiple different tactics actually more than what the test was in itself and why because it looks at the um the attack tool the Ingress tool transfer anything like that is happening outside of that is also being tracked which is now showing me more things that may be my initial test command and control resource development in Ingress tool transfer um and again hopefully the tool whatever you use gives you you know clear understanding of those capabilities of the platform and it also includes the uh the the script that may
have ran in the environment you certainly want that as well and then as I go up a little bit higher it says MIM cats is an open source offensive tool designed for credentials and memory blah blah blah blah blah right and then it says credential access that's the tactic and then you've got two techniques that were discovered here OS credential dumping Elsas memory that's the test that we were I think we were doing um and then also this use Al alternate as well right so pass the hash as an example now the one thing that I did was okay well wait a minute I'm going to do automatic isolation of this asset and again this is understanding not only the
adversaries abilities but what is the defensive outcome of this as well in the equation so I'm going to set this to critical anything that's a critical alert of a certain group this group is going to be um the the group in protect mode so we're going to protect in this case and I'm going to save and so basically what I'm saying is if you see a critical event trigger not only for miter but for anything automatically isolate the machine and um and and um and and hopefully reduce the risk to the organization ultimately right that's that's the goal and so what I'll say to the red teams is I'm doing a ping here to 88.8 and I said red team go ahead and
run your test again let's just see the difference now I see all the tactics and techniques that we would discover with that test which is great but now I want to identify whether or not I had the ability to stop it and what that outcome would look like so here all I'm doing is moving it from audit I'm showing you every step right so there's no smoke and mirrors right I I'm going through and I'm moving this into the protect policy and I'm going to update I'm going to force it it would just update after a few uh uh you know 30 seconds 60 seconds depending when it got the last update and it moved over um the test I'm going
to run here so I'll go ahead and add a potential link a new test all uh brand new so let's go ahead and do that we'll do the search for MIM cats and and we'll scroll down and and here we go we'll grab that one that's the command line We'll add it it's automatically running because it's set in the policy it's automatically running and what's happening here is you can see oh oh no let me go back sorry I'll be quick so what you can see is here it's not isolated right right um and then a few seconds after we did this you can see right here this will turn to see it says isolated so I hit the button the
wrong button by accident but anyways so now it's isolated but I can still ping 88.8 so you might be saying well wait a minute how are you isol you're still pinging it started isolation well because I have a white list for 88.8 in my policy so with anything you might still want access to certain systems even in the event that you need to isolate an asset that's the point here right um and then I go ahead and show you that I can't ping 1.1.1 I can't even ping the local Gateway on the network that's the 2551 you can see it's so I am isolated and contained but for whatever reason I needed access to 88.8
or a specific system right and so I can grant that access the last one here is interesting I thought well let's use the network we're almost done harf I'm going to get you back on track almost um but anyways I thought well wait a minute why why don't I use chat GPT I'll make make the five minutes to create a Powershell script to scan the network like nmap now yes I could have downloaded anything already I didn't have to do that but it went through and it starts developing it says okay for major ports on your network 192168
255.0.0.0 as I want to also understand and become very proficient at this as well so what is this what is this an example of if I'm using Powershell to scan the network anybody want to throw out what sorry I can't hear you it is end map yeah it's like end map right we're scanning the network it is living off the land right I'm not bringing in any tooling not bringing in anything extra right and I'm an adversary that that's maybe not as skilled on the scripting side so the again this is just to show you how easy it could be so I go ahead and I copy this is this perfect code it's not it's really close though
and so I throw it into Windows Powershell ice and I hit you know uh select all and I hit play and uh failure but you know what it points me to exactly where the failure is I had to add the parenthesis right you know the brackets between IP and Port that's it so I do that and again just trying to be sensitive of time here I do that and then I rerun it okay and I not only rerun it within the ice Pro there's no client on this by the way um enabled at this point so I'm not looking to do this from an endpoint detection response I'm not looking to do this from a NextGen
firewall perspective and I hate the NextGen term but don't get me started on that um uh so I don't started on either one of those so um what I'm leveraging here with a little bit of time is the network can the network detect it and this is my point is that I have the ability to test all of my tooling throughout and so did it test it did it detect it yes it did maybe it didn't cross a Gateway right an N ngfw to detect it maybe it's on a layer two boundary maybe you don't have end maybe it's on a camera that doesn't have an endpoint can I detect it yes I can I see
the discovery it talks a little bit about it I can pivot into the miter attack framework again you Leverage the tools that you have in your organization to do this but the point here is if my other controls failed for them to get to this point I still had another opportunity to detect them in the environment and you might be saying well you didn't prevent it yeah I haven't but now I know they're there so now I can start working on prevention so in summary defense of is is definitely tough business right it is really tough business um and we always feel that we're behind the eightball but um you know colle itively things like
bsides people coming together we start elevating our defensive knowledge and understanding I think we're all going to be better off we want to climb higher in that stack think pyramid of pain let's see how much pain we can invoke on the adversary by making it very difficult or costly for them to be successful we want to understand the adversary right that's targeting legal Health Care you may not care about that they're targeting an operational environment somewhere in Saudi Arabia it might have no relevance to you and you might say well it's still interesting because they might use some of that in my environment yes but you better do the other things first right you better understand who's targeting
your vertical first and then you can go and you know if you're at that level let me know I'd love to see what that environment looks like right but we're not there um identify the tactics the what and the techniques the how right they're driving towards an outcome breach attack simulation helps identify uh your defensive posture and how you stand stand up against those T attacks um insight into preventative and defensive capabilities again I'm going to reiterate you're never going to prevent a 100% of everything even if the tooling has a capability to suggest it can it will never do it 100% of time for the rest of time right so you want to make sure you have detection
capabilities throughout thanks for the auction uh style presentation harf but thanks [Applause] I know it's lunch so I don't want to keep anybody from lunch but anybody want to stick around and chat I'm more than happy uh to have any any questions feel free