Defenders Struggle as the Adversary Continues to Break Away by Jason Maynard
Show transcript [en]
[Music] All right. Excited. >> No. Yeah. Woohoo. Uh, you know what? This this is going to be an interesting conversation. So, I did have the Oilers logo on this. I guess this will go on the recording, but I decided to take it off just because I had a couple of comments um that maybe I don't have the copyright for the Oilers logo, but um the point is that this is going to be really focus on where we should be going. So, you know, Wayne Gretzky had always said, you know, you got to go where the puck is going, not where it's been. And I think defenders have to start thinking like that as well. And so
if you look at a lot of the different organizations, there's a lot of similarities, right? There's some nuance, right? So healthcare, you know, they care about patient care, right? Being able to provide patient care. They um, you know, they they don't want malware in their organization that could jeopardize that patient care and potentially death. And I think we've started seeing some of that. Uh, unfortunately, they have personal health information that they want to protect. And, um, you know, industrial environments very similar, right? they've got they don't care about patients but they care about safety and not having to send somebody as a patient to uh a healthcare organization. Um so human risk becomes a big factor. You've
got financial institutions that um you know care about payment processing. So any cyber event that impacts even milliseconds right or nanconds could jeopardize their ability to make money. And so that's obviously something that is top of mind for them as well as personal identifiable information and things like that. And I'm coming to a point here, right? Higher education. So again, um you know, they might care about compromised research data, right? They're they're working on research. They don't want it compromised and leaked. Obviously, um PII, uh intellectual property is something of interest to them as well to protect. And then government, right? You might have critical services, classified data. Um, again, you get into PII and intellectual
property and things like that. But you know what? When I did a bunch of research, so I I probably spent about two weeks, two and a half weeks trying to figure out what are the real threat vectors that customers are facing today. Um, and then I analyzed that, cross referenced it, looked at a bunch of data points, came out, and these are like the top 10 or I use chat GPT. So right I said tell me the top. So yeah, I didn't spend any time but we don't tell our employers that right we say exactly what I did is the effort involved. Uh but anyways, advanced fishing, ransomware, social engineering, like these haven't changed that maybe the new
one is around AI threats, right? People are starting to build models in their organization and so there's a new threat vector, a lot of the same controls, but there is some new things and we'll talk a little bit about that. Uh vulnerabilities are being exploited, right? Supply chain attacks, these are all things that happen. The problem is that no matter how much effort you put in, you're never going to get 100% security effectiveness. 100% of the time. I hate to tell you, right? You're going to get popped. And when you get popped, um, obviously there's things the adversary is going to do. And that's really what the focus is, right? So, we've got preventative capabilities. And
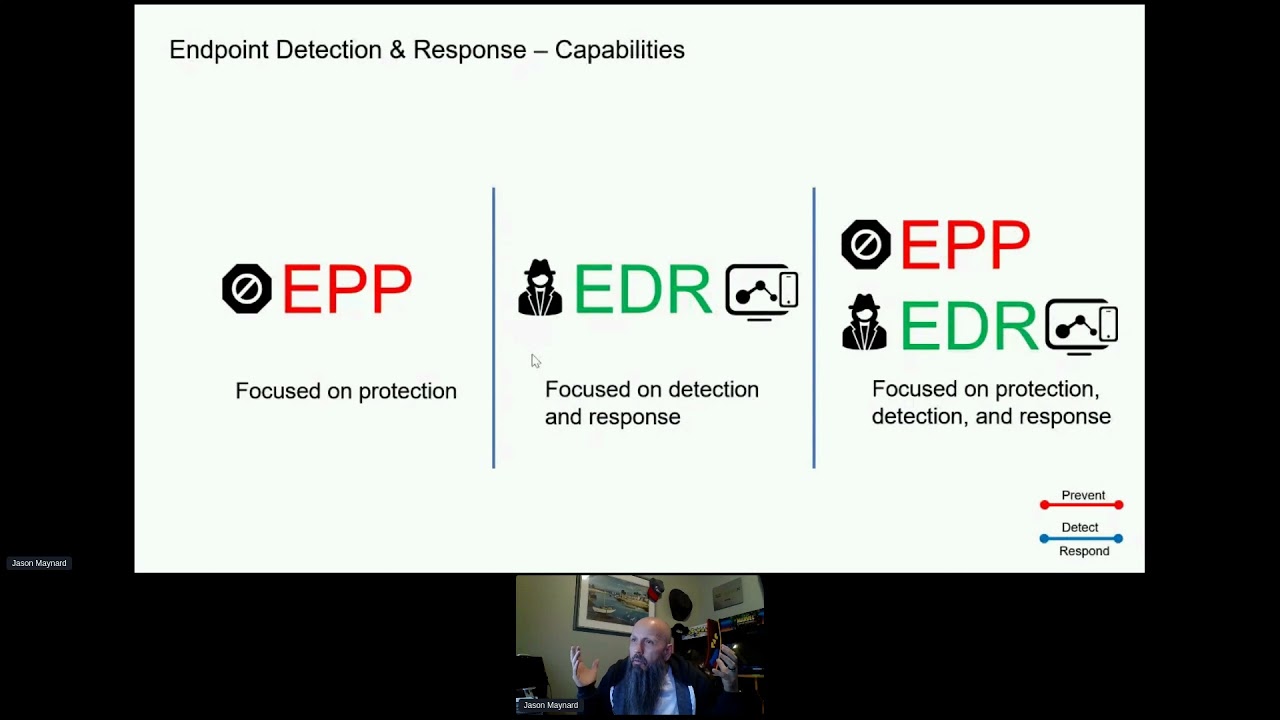
if you look at just ransomware, there's tremendous opportunity as a defender to mitigate against that, right? You can do DNS layer protection, web proxy, next generation firewall, email, endpoint protection, right? And some people might say, well, wait, we've got really good endpoint protection. Do I need all these other controls? And absolutely you do, right? And these are the basics. Everybody has these or should have these. The point of relying on one control is is that if at any point in time that control fails, right? You you better hope that you have something in place to mitigate, especially on the endpoint, right? That's your last opportunity to fend. And then as you go along, there might be things that you need to do from
ransomware specifically like sandboxing, right? detonate that in a malware environment or in an environment where we can look for behaviors to identify risk because it's unknown and then you get a disposition. But also there's other things that you can do that may not prevent but identify threats in the organization like ransomware, right? You got network detection response, right? Baselining an environment. That's this is one of the the defenders greatest opportunity is to baseline your environment truly understand what normal looks like. So if there's deviations of that environment at any point in time obviously with some logic you can identify something in the environment and most times when you're identifying it here is a good indicator your
controls have failed right and they will so again it's just an opportunity and then you look at workload protection knack on the campus uh infrastructure wired wireless and VPN again these are things that I can stop maybe potentially some of the the things the adversary has to do in order to get successful I can get one user to open up an attachment potentially and click on it, right? That's easy. But spreading it and causing harm in the organization, that's harder, right? Um, and then obviously you'd overlay and we're just talking ransomware. So go through the top 10. These are things that you're thinking about, right? Like what can I put in place to mitigate that threat?
So as we go along when we look at it, an adversary might start with ransomware. And there's a common theme here, and we're going to come to that in a second. But if you look at an anatomy of an attack, they have to get initial access somehow, right? Get you to click or or pop a vulnerability or something, right? That has to happen. And then once they land, right, they're going to do a bunch of things around the the techniques that they need in order to, you know, make their presence known in the organizing
intellectual property. they're not looking necessarily to cause harm harm. So if you look at MITER, the attack framework, you got things like tactics and techniques, right? Tactics is the highle bucket of what I'm trying to achieve and the technique is the thing that I need to do in order to achieve that tactic, right? And so you got execution persistence privilege escalation, defense evasion. All of these are uh, you know, opportunities for defenders. credential access, discovery, lateral movement, collections, command and control. I'm a big believer of the MITER attack framework, right? We have NIST, we have all these other frameworks you're g you're going to follow. But tell me tell me one organizations that followed any
one of those frameworks that have not been compromised. You can't, right? Same thing. If you you've got 50 different technologies and you've done a really good job integrating it and you've matured the platform, tell me one organization that hasn't been compromised. You can't, right? Eventually, they will. But if you take an adversarial view of it, you have an opportunity to do things a little bit differently. You don't need to be right 100% of the time in every step. What you need to be right is in certain aspects of the attack. Now, obviously earlier on the better, right? If I don't if I know it's going to a bad domain and I can block it right out of the gate, that's
probably pretty good. The reality is is that the adversary is going to get past that control. And when they do, what is their next step? So if I understand the vertical that I'm in and how adversaries maybe target that vertical and map that out to their capabilities, now I start building assuming breach. So assuming compromise is inevitable. And now I can start overlaying the opportunity for defenders or protection, right? Or defenders, but prevention and detection. Not everything's going to be prevented 100% of the time. And detection you need in order to prevent, but you don't always have an ability to prevent. That's a reality. And so I'm just mapping this out. I'm not going to go
into this in detail, but again, I'm just talking about capabilities aligned to the tactic and in this case the technique that the adversary is using. And I'm saying these are things I can do like EDR technology, right? A lot of these first pieces, execution, persistence privilege defensive well maybe. But credential access, there's a lot of endpoint stuff, right? So you can do a lot of endpoint based controls there, but I'd probably want to stop it earlier. And then you get into things like discovery. Well, guess what? You need a network to discover, right? You need that transport to be able to use that. So things like network detection response, that's an opportunity to detect things. Lateral movement,
collections, command and control, exfiltration, and then finally impact, right? Ransomware is landed, right? It's encrypted the drive and now you're making a payment or maybe not, right? What do you think's common here that we continue to miss as defenders? What do you think is the number one area of opportunity we still are really crappy at doing? Anyone? >> Yeah, I don't know that we're going to get better at that to be honest, right? We there's programs in place. Sure, some organizations are in different journeys of that to do better. Um, but it is a good point, but I don't know that we're going to get more effective there. I just don't think that's going to happen,
but you have to do it. It's like endpoint protection. You just got to do it.
Yeah, th those are two good ones. But if they land and you can't prevent that escalation, then what? What's the adversary going to do almost every time once they pop a box? So they they've defeated the control. What is it that they're going to do every single time? >> Yes. Ex Whoever said that. Yeah. lateral movement, right? Almost. And again, it's 60 to 70% of all breaches involve lateral movement. That's the number. I I was surprised by that number. I thought it'd be a lot higher, but maybe if the adversary lands and they weren't able to expand that does. So that 30% was you you had a control in place that didn't allow the adversary to successfully move
forward. But no adversary lands on an asset and says, "I hit the jackpot. Game over. I win." Right? They need to break out of that system every single time, whether it's in the campus infrastructure on an endpoint user, an IoT based device or a workload vulnerability in the data center. It's inevitable. And so the common theme that I see is is in fact lateral movement. Um, and you might say, well, wait a minute. You know, Jason's got a little Cisco thing in the back and you know, they have the network and no, I'm talking about when I talk about lateral movement, I'm I'm talking about lateral movement more holistically. So I'm talking about from the campus whether
you're IoT, uh, HR, IT, whatever, stopping lateral movement within the campus infrastructure, but also mitigating risk in the workload environment. And I'll show you that in a second. So when you look at this, you have a lot of stuff on there. Look at the plug for Cyber Alberta. Meren will be proud. But um, but the campus infrastructure, you've got lots of devices, right? It's pretty messy. A lot of IoT devices connected to the environment. um you can't put an endpoint product on every single asset that you have in the environment. The adversary knows that, right? They know you have IoT based devices and they're targeting them and they're using that to pivot more uh within the organization. And so when you
look at the campus infrastructure, there's a couple core elements that you absolutely require. Doesn't matter what technology that you're buying, it has to do some of these things. One is provide visibility, right? You need to holistically see what the assets are in the organization, right? or else you can't prevent it. So that's the first thing. Then you need to build policy. The policy is going to hopefully drive a zero trust outcome. Meaning that connectivity from this asset to this asset can't happen even in a layer 2 network, right? We're not even going through a router. We're talking even on the layer 2 boundary. So for example, you might have all these users in the same switch on the same layer 2 network.
Well, if ransomware gets on one of them, they have free access typically to spread in that environment. I want to stop that. We should stop that. Little uh a bit of work to make that happen. Um but you want to build policy and the biggest piece of this is because you touch the network um there's a tremendous amount of noise and risk, right? So if you put in a control and it breaks, guess what? Help desk it lights up. And we don't want that. So you want to have an ability to simulate. So find a way to be able to prove policy out and the outcomes and then move to enforcement at that point in time
that helps us drive towards zero trust. But zero trust doesn't mean no access, right? Zero trust means limited access. Now what if this switch here all these people are on the same layer 2 network need a peer-to-peer type application to function. You know it happens. You're not going to shut down the business. They still need to do peer-to-peer stuff. um right collaborate or whatever it might be. Um, so you have to allow that access, right? If not, you just unplug everything and say it's secure. We all know that, right? So you can't do that. So what happens if malware takes advantage of that as an example or an adversary, forget malware, just say an adversary gets on it and starts probing
and starting taking advantage of that port that's open. Well, you can't stop that, right? That's where other controls hopefully come in. But I could proactively build policy that says what happens if I do assume breach and they're able to move within that environment. Could I push a button and send controls into that environment and mitigate that as we kick the adversary out? Right? Once we understand where the adversary is, we secure the environment. Then we open that back up. We should be able to do that. These are things that we should be doing in in the industry but it's been difficult to do this right and it should be based on some level of risk right we want to
identify the asset and when I say an asset or identity identity is more than just a user right it's a machine it's the context of the risk profile associated user it's the context and risk profile associated to the machine and then the the the overall risk profile right all of that matters and then if there's u CVE in the organization we may want to add additional controls, right, and mitigate against it. And the goal here is to stop what I've said earlier, that lateral movement or make it very very difficult. And I'm a big believer of this, right? You do not need defensive capabilities in 100% of the places. You just need to make it sticky, slow it down. And I call
this timebased defense. Um, and the reason why I call it timebased defense is that if there is a port open or the user has access to something and they ride along that access, um, hopefully they try something that they don't have access to. And what's that going to do? It creates noise. If it creates noise, guess what? Any one of your other technologies may pick it up. So, it gives your team more time and your products more time to catch the adversary in the in the environment because think about it, they're in a box and they're just pounding the box trying to figure out how to get out, right? You're making it noisy for them. And
noise is a benefit to us as defenders. Now, what about the data center? Now, I'll go on record saying this. This is the greatest opportunity I think defenders have, but we ignore it because of the complexity. I'm not saying EDR and XDR and you know your email security and nextG fire aren't important. I'm I'm not saying that. What I'm saying is if you can focus on one area that provides the greatest amount of risk reduction, this is the area because again the campus tremendously valuable, right? If I can stop lateral movement, but they're going to pop a user. We know that. Is that where they want to stay? Probably not, right? They want to get here. They
want to get in the data center environment. And so what we want to make sure that we're doing is is again very same thing. These workloads could be containers. How many people have protection mechanisms in their container environment, right? There's a whole virtual when you talk about virtual networks, containers have a whole other world of virtualization inside of that. And most of those micro apps have access to each other and there's no additional controls in that environment at least by default. Um, you've got Linux, you've got Windows, you've got AIX, you got Solaris, you got security groups in Azure, NSG groups well and Azure security groups in AWS, right? They all have a different nomenclature. Their API
works a little bit differently. Um, but they all have a control in that environment and and up to now this has been very difficult. Like anybody that's managed firewalls know this, right? App team or a business group has said, "Listen, new service coming online. we need to turn on this service. These are the ports and protocols we are doing a change request for. And then you go in and do that heavy lift, you know, type it all in and then make the change. You do your internal testing. You pass it to their UAT team and they come back and say it kind of works but doesn't work. And that's at the edge of the data
center, right? Or an internet firewall as an example, right? And then you go, well, tell me what the app needs. I can make the change. That part's easy. And they don't know the app. And then you do a little bit of conversation, come back, you guys make additional changes again, it kind of works better than it did before, but not fully works. And you're like, now you're doing packet captures, right? You're trying to figure out what does this application need and so people don't touch that workload environment. It's too complicated, right? You break stuff here, things go bad. So you want to be able to do very much the same thing. You want to be able to take the
information from the systems in the organization, whether it's container, security group, network, operating system, take that data, ingest it, run AI against it, and build policy automatically for you. That's a reality. And not only do you want to build policy, but you want to simulate it before you make the change of enforcement because if you don't, that's where you're going to get calls. And most likely in this case, like you can block out a user, but you start blocking the workload itself. that's and workload just because sometimes the the terminal workload equals server, right? Whatever service that you're providing. Um obviously then you're probably going to look for a new job, right? Um so if
you are looking, this is a good way to f accelerate that if if you want. Um and then and then there's some really interesting stuff that we're starting to see in the industry like exploit protection. I'm going to talk a little bit about this, but imagine being able to say, "Listen, here's a high-risk ex uh vulnerability that I can't patch because we're in the high seasons of transaction for whatever. Maybe it's, you know, uh Boxing Day, right, in your retail. You don't want to go in and but if there's a vulnerability, high risk, right? Maybe you can do rolling updates, but maybe you can't. Can I mitigate against that?" And this is where the industry is kind of evolving. We're
going to talk about that in a second. And risk profiles. And then you know it goes on right like again if we talk about accessing private applications. Well again when you access a p uh an application you want visibility. You got to build policy. You got to do enforcement right only allow them access to the things they access and nothing more. You want to drive towards zero trust. Again some level of risk maybe around identity and machine all coming together. And then maybe if something does change you want to step up authentication. So, for example, if you're a healthcare organization, you're a big organization. You have, you know, a Tim Hortons. Tim Hortons has their own
Wi-Fi in their organization. Well, you're a doctor. You go down for a Timmy's, right? You have access to patient care data. You walk into Timmy's, it automatically connects to the Wi-Fi. Well, should you lose access to that app, maybe, right? And if you don't, because the condition of the environment changes, then you might want to step up authentication. Right now, we're going to add friction to the environment. The goal as as as practitioners is to remove the friction, add the security. You know, when you go in an airport, how much friction is that, right? You go to up to the tail, you show them a ticket, you show them your ID, you know, they get say, "Go
ahead." Then you put the bag on because you're going to you're checking it in. It's going through a whole bunch of security controls that you don't see. Then you go up to security and you're taking everything off. Then they're, if you're lucky enough, they say, "Come over here, right?" And they do additional validation, right? wipe your laptop, check it for whatever they're checking it for. And then if if you're going to the US and you know you're in customs here in Canada, guess what? You get to go up and then they're asking you probably even more questions. Where you going? Where you staying? How long you going to be? Are you leaving? Right? And then if you if you're lucky, I guess
again you get to go into secondary and then they say, "Are you sure?" And you're like, "I was running from the airport. That's why I'm d like I was trying to catch my flight. I'm dripping sweat. I might have looked nervous, but it's I'm not nervous, right? Like I'm I'm just trying to catch my flight." That's all friction based, right? It's a garbage experience for users. >> Huh? >> That's a good point. But I don't mind the attention. Anyways, um but the point on our side is defend. We don't want any of that. We want the same level of scrutiny, right? We want all those same things. We want to scan packets. We want to look for malware. We
want to do all those things, but we don't want the friction, right? That's not a good thing. And then the operational environment very much the same thing right I'm not changing anything visibility policy simulation enforcement zero trust right and now we start to take these off in sections and we start building more of a holistic zero trust outcome you're not going to have a single product or technology that drives the outcome it's going to be a collection of capabilities that drives towards the framework not the products that drive the outcome right but we want to make it operationally as simple as possible wherever we can. So you're going to start hearing this theme around hybrid
mesh firewall, right? That's an industry Gartner created it and this is now focusing more on that data center workload, the biggest opportunity for defenders, right? Go where the puck is going. That's where the adversary is going to go, right? They're going to your workloads. That's what they're going to compromise. So maybe we need to get there first, right? Uh and intercept it. And so applications are highly distributed. We talked a little bit about that. nothing we we don't trust anything period. Even when we do trust it, then we're running intrusion prevention against the packets we do trust, right? Um and then vulnerabilities are coming faster and faster. And so the goal is to leverage that ecosystem of capabilities. So you
might have a firewall. That firewall could be deployed in an organization. There's a bunch of capabilities that come with it. That's going to move remove some risk, right? And so think about every dot here. These these dots represent where controls could be put in place. And again, I'm not talking about a vendor specific outcome here. I'm talking about a capabilitydriven outcome. Same thing with secure services edge or SSE or Sassy, right? There's a whole firewall as a service within that service. So now I've got a my nextG firewall. I've also got this firewall as a service. I might also have security groups in the data center or in Azure, GCP AWS. Um, I might want to transition that to
be more full-fledged security appliance, right? So, probably paz device that can grow with the environment and build in advanced inspection like intrusion, malware, TLS, decrypt, quick proxy, things like that. And that's going to be in places. And then you've got workloads, Linux, AIX, Windows, um, uh, you know, all these containers, right? Docker, Kubernetes, all of these have controls in it. Most people in this room, nobody touches this piece, right? Like how many pe and I won't ask this because you don't need to put up your hands, but I suspect, unless you just yell and say you're wrong. I'm okay with that. But most of us aren't running firewall services on Microsoft Windows in the Windows environment or firewall
services in Linux in a workload environment or data center environment. You're just not because it's hard to determine what the application requires to function. So you don't do it. So this could be, you know, um 100 workloads. I've got a customer in my real job that has 30,000 40,000 workloads. Like massive. Imagine trying to do that there, never mind 100. But the scope of this is it could be this big, right? It's very very hard to do. And then you've got containers. So this is Docker, um, Kubernetes as I mentioned or Open Shift like all of those technologies now have that whole world inside them again delivering a control. And are you the thing that us as defenders got to start
to think about how many how much skill set do I have to bring in? Like now you're saying I need a Windows firewall admin. I need a Linux firewall admin. Maybe they're the same people, but containers and platform engineering, that's a different group. And then I've got my cloud team over here that does the security groups. I've got my nextg firewall team back here that manages, you know, Apollo, a checkpoint, Cisco, whatever it might be, right? Um, and you think it's well, it can't get much more complicated than that. Well, what about ebpf, right? open- source capability, right? Every anybody everybody familiar with ebpf kind of no not really. So ebpf is uh really a sandboxed in in
environment that's in the kernel by default on Linux and containers. So what it allows us to do is see every system function call that takes place at the kernel level with full visibility without ever breaking the kernel and blue screening the box. So everything goes through this sandboxed environment and now I can see every process, every function call, everything and I can do some really interesting stuff with that. And eBPF is open source um and um and it's coming to Windows. So today it's in Linux and it's in uh all all the container platforms and it's coming to uh Windows as well. So a tremendous opportunity here to understand um security and networking and observability at the kernel level
without having the risk of a new security update that comes into the platform that happens to touch the kernel that blue screens to death or blue screen. I think they changed the color. Did they? I saw something. >> There's a black screen of death. They didn't think we can change blue from black, right? And it's not even that hard. I mean the first letter is the same. Anyways, um eBPF uh allows us to drive some of that security function. And imagine being able to and this is again this is uh future uh thinking is taking the DPU in a switch or in a network card on a server and being able to drive an L3 L4 based control with low
latency in a data center. And if you wrap it around with some intelligence to tell you what the policy is. If I need to build a policy, do I need to figure it out? Does the application team need to figure it out? who figures it out? Well, why not let the technology determine based on the connectivity that it requires to tell me what the policy is? And listen, why not even do that without the complexity of knowing the nuance of how to operate it on all of those different technologies? And that's the shift. This is where we're starting to see the uh transition in the market to allow us to do things that we could never do, especially in
the data center environment. And this includes or should include third-party. Cisco could be third party. It could be Paulo. It could be forinet, right? The customer determines, right? The user determines what's first party, right? But the bottom line is is that you have one or more security or traditional firewalls in the environment and you're managing them independently and that's comp convoluted and complicated, right? And again, how many people do you need to bring in to drive and support that? Maybe it's the same team, but they're probably going to be overburdened, and I bet money that they're not going to be able to do some of the things that you probably should be doing from a risk uh
reduction perspective, right? Like, yeah, you could take care of all of our firewalls. Maybe there's some switch controls that we can drive, but workloads, Windows, and Linux, no, we're not we're just not going there. Well, again, that's where the adversary is going. So, the point here is if we don't do this time and time again, this is what happens. And it's going to continue to happen. And again, I'm not saying dude give up on your other controls. That's not what I'm saying. I'm saying that we need to go where the puck is going because that's where our enemy is going, right? Um and it doesn't mean that you're going to have 100% immunity either, right? It
doesn't mean that they will not pop a vulnerability. They still might do that, but if you make the box very hard to get out of, well, um you know, there's a good chance that um you have some advantages here. And so with cloud, we're starting to see that cloud control come to fruition, right? Lots of vendors have the ability to drive controls into an ecosystem, but a lot of times it is very vendor specific. The goal is to remove the friction. This is what you guys all should be pushing your customers or your vendors to to start looking at is listen, I want to be able to control outcomes more broadly, right? And and I want to understand the intent.
So if I for example want to deliver a control for a specific service, do I need to know that it's got a Windows firewall, it goes through a security group in Azure, it's got um a container, right? It's a Kubernetes environment and it's got do I have to figure out exactly how many touch points of controls I have to open up to allow that service end to end to open up or do I drive intent to say I want this service to work and it tells me these are the control points that need to change. That's where the industry needs to go. The other thing that we need to to start looking at is leveraging AI to get rid
of some of the noise. So decryption is a heavy cost to everybody. Um but you need it, right? You need it for things that are bad. And so what if you had the ability to do encrypted based visibility without decryting the payload? What? Yeah. And if you buy now, no, I'm just kidding. Um, no, but you have the ability to look at multiple different data points um of that packet to determine its destination, right? That could be anomaly. The TLS ciphers that are being used, that could be a piece, right? And you take each one of those and then you determine whether or not um uh this is at risk. And if it is, then
maybe block it. So some of the things that we're starting to see with AI is 6% of flows are actually at high risk. Again, your environment might be higher, another environment might be lower, right? But generally speaking, 1% of traffic is going to be risky. And so those are flows that I can get out right away. Like optimize, you're not going to do any additional analysis. We're going to get rid of it. Right? That's that's the goal. um low risk roughly 96%. So all the stuff that you're decrypting is very low risk. Again, I'm not saying don't decrypt it. There might be reason to run IPS on some of it, but 96% of flows don't require typically don't
require decryption and your other controls are still going to be in place. That leaves us with less than 4%. That's it. 4% of traffic needs to be decrypted. and decrypted might need me also mean you know TLS proxy but also quick proxy right you need to be able to decrypt both of those uh as well but now what you can do is when you start using technologies like machine learning and AI you can reduce the amount of hardware you require in order to do the decrypt right you can get into a smaller form factor reduce your overall cost but not sacrifice the level of security that you're getting starting to see this as well with snort
as an example another open source technology with intrusion prevention. We've added machine learning capabilities to it that now look for uh anomalies within signatures. So signatures, what you try to do is cast a net. The net's got to be wide enough to catch as much of that um exploit as possible, but it can't be too wide because if it's too wide, then you get false positives and cause disruption. It's bad. So you've got to tune it in a bit, right? The problem with that is is now the adversaries are using AI to find the nuances in that signature as an example and they're looking for the gaps and they're targeting the gaps. Well, fine. We'll do the same thing. We'll an
analyze it, be able to determine what the the risk factors are and dynamically build in those signatures on the fly when we determine that risk. little bit around AI there and only because this is another hot area that everyone's looking at. AI has two sides of it, right? You've got the user side and then you've got the application side. The user side is um users going to um unsanctioned AI applications like DeepC chat GPT things like that, right? That aren't sanctioned and you're scared about intellectual property and things like that. So, you probably want to start controlling access to those types of applications. And then more importantly, the ones that are sanctioned, you probably want to run DLP
on it to make sure that they're not putting the Oilers logo in their presentation, right? If they don't have the copyright. Um, so anyways, um, that's one side of it. The other side of it is really driving towards securing the models in which you're introducing to the environment. So if you're building out models, we want to make sure that there's no data poisoning, um there's no prompt engineering, um no injection, like all of those things should be tested and validated and you should automate the red teaming of of those as well, right? So for example, um we've done tests specifically around DeepSeek when it initially came out. Um and this is talking from a different
lens but um you know out of all of the security tests against deepseek how many failed at that time almost all of them and it might even have been 100%. Now again I think with a lot of technologies we move really fast for adoption um and then security comes and wraps around it. The good thing is is that everybody now knows that there's a security component to it and they're starting to shore their capabilities around that. So segmentation as I mentioned as we continue to go through we want to get down to this level right so we want to see flow-based is is more high level port you know source destination uh allow it's not great right what you want
to do is be able to get down to identifying the process that is on the workload that needs to communicate with another workload and the specific process and if you want you can add identity to it as well and that's at the workload level and that's where you start driving towards micro segmentation. So you're going to have some workloads that you're going to be able to drive 100% of that and then you're going to have some other workloads where you're not going to be able to do that, right? So if you have an SAP application that communicates 100% uh throughout the year and there's a batch cycle once a year, well that's going to be a little bit harder to get
down to deny all at the bottom. But NTP, DNS, domain controllers, you're probably going to be able to do those really really quick. Not really really quickly but quick quick enough that it identifies those threats. All right. So this is an example of now things starting to come together. Forget the technology name there, right? It could be knack, right? If I can authenticate and authorize things that attach to my campus infrastructure including IoT based devices and then use that in identity now for controls in my environment. That's pretty good. Now I can say this cam from Logitech has access to Logitech app and that's it. And I can actually build that identity into the workload policy that the
Logitech system runs on, right? I can build that logic into it. And then on the campus side, the moment they try to communicate with anything else, instead of going all the way through your controls to block it at the workload level, guess where we block it? We block it as close to the asset that's making the communication that isn't allowed to make that communication. Why do we need to pass that traffic all the way back in just to drop it? The goal would be drop it as soon as possible. Right? This is an example. You got sales front end, sales backend, a database service. Um these are all microservices. You can use ebpf as an example to identify and
map them out and then build prescriptivebased policy to drive the outcome within that Kubernetes environment. So, I have um worked with people specifically trying to reduce risk in an environment where they can't patch specific systems. They just can't. There's um there's no patching of it because the systems unsupported. And to build the application or rebuild it, there's hundreds of thousands to millions of dollars. And so, what they're doing is fortifying them, right? They're making sure that if that they do get compromised that they can't break out of that system and move further in the in in in the environment. And so these are some of the things that you can do. You can start mapping out the
web applications, the front end, the database, the backend, the behavior, the file changes, the network flow. You can use all of that good telemetry to build prescriptivebased policy. When I'm saying prescriptivebased policy, I'm saying I don't need to know how it's applied to Windows firewall. I don't need to know IP tables. I don't need to know ebpf. I don't need to know security groups. I don't care about the API is different in AWS, right? I don't care. I want the same look and feel. Policies always look similar, right? So, I get used to the way it is created, the way I add policy, and then all I do is hit enforce once I've simulated that
traffic, right? And I'll show you that in a second. And then if there's deviations, I want to be able to call that out. If there's a deviation of a communication pattern that I didn't map, I should know about it. Now, could it have caused disruption? Yes. If you map this out and you go to a deny all and back cycle didn't run and now it runs, we're going to see it, right? That's if you don't have technology that helps you see that, we've got a problem, but it will be able to see it and then we'll rectify. Now, we don't want to get there. So, you probably want to run your policy analysis over a period of time to
make sure you catch it. Now, this is interesting distributed e exploit uh protection. So what we're starting to see in the industry is the ability to look at uh vulnerabilities identify true risk. So true risk really means you know just a CVE number 7.5 or 8 to 10 uh that it it should be backed by data science to give you a real uh indicator of of the risk to the organization. So that's a set that aside for a minute, but that's critically important, right? We want to prioritize our our patch management based on real vulnerabilities, not whatif scenarios. Now, what if it is high- risk and it's being exploited? In order for it to be
exploited, guess what? It needs to write a file to disk or it needs to run something in memory and then open up a netcat listener on port 8080, whatever it might be. Well, if you're using eBPF open source, you have the ability to see that. And if you have the ability to see that now, you have the ability to prevent it. So, you can actually go and say the vulnerability requires these things, I don't want you to be able to do that thing. So, when they make a function or system call to open up that port, it's going to deny them. And you can leave that vulnerable application still running until you patch it. It's
not virtual patching. It's a level above that, right? It's looking at the vulnerability and how you expose it and then making sure you can't expose it. You can't take action of it. You still get into memory, right? You execute arbitrary code, but that's it. You can't actually see the results of that. But how do you do that um safely? I'm just going to fast because I know we're going. So, how do you the the biggest thing the biggest problem in the data center is is being able to drive the controls without disruption. So, h how do you do that? Well, with eBPF, I said that at a kernel, you have the sandbox. There's lots of ways to simulate, by the
way. This is just one way, but with eB specifically, you have that sandboxed environment, right, within the kernel itself that allows you to hook into everything and see all the communications and um and it passes through that system, right? And what if I'm able to and so that's where you'll build your controls, but I don't want to do that because I want to simulate it. So there's near real time and then real-time simulation. I'm just going to talk about real time. So what if I take this and create a duplicate? So I have a digital twin of that traffic at all times. Now I can upgrade this. Look for the impact. Do they impact memory, CPU,
latency? Is the same number of packets passing as it once before? And if it does, then I should be able to transition that that uh shadow data plane or digital twin into the production data plane. It just flips, right? Moves traffic over. I feel confident about it, right? I've upgraded the system. I didn't blue screen, black screen, purple screen, I think is what the SXI, but anyways, I didn't do the bad, right? The same thing can be done with policy deployment. So I run policy against that secondary or digital twin and I allow it to run through the analysis and then based on those outcomes I adjust or move right into enforcement. If I need to adjust I make
the change to the policy I let it run again and then I go ahead and move to enforcement. That builds confidence right and it helps with adoption. So these are some of the things that we should be looking and pushing for is you know driving towards uh microbased segmentation not with complexity not with private VLANs right but simplifying the deployment of micro segmentation in the data center specifically I'm not just excusing the campus but if you're going to pick one that's where I would put my money on and then managing it right you need some type of controller that can manage some of this stuff and that's a a conversation because you have different techn technologies, different
stacks. You're going to try to figure out how best to do that and there's ways to do that, of course. So, in conclusion, so I probably got three minutes probably, you know, they're they got big signs like even a stop sign. Um, I'm not kidding like well, it just says stop, but so it says stop sign because it's a anyways lateral movement equals success for the adversary. Period. Uh, zero trust is not a single product. Again, micro segmentation is helping you drive towards zero trust. But I I think we all got to push back on vendors specifically. Zero trust is not a product stop. Right? It's an outcome that your product can deliver on of the
bigger framework, right? Because you got to remember as soon as you know COVID hit like and and this whole thing around zero trust that framework like every product just changed. Zero trust everyone no advancement in the technology they all just found a way to spin. Hey, you want zero trust? Look at my identity. You want zero trust, look at my network. Look. Anyways, end to end segmentation is possible. Uh you definitely want the crawl, walk, run approach to anything that you do, especially in the data center, but even in the campus infrastructure, right? You don't want users upset. Um so visibility policy simulation enforcement, and then finally compliance. That's something that we didn't touch on, but how do you know
when you have deviations in policies? Well, things like network detection response, that tool will tell you, hey, wait a minute. I'm seeing a communication pattern that wasn't there before, and it can let you know. And if you feed that in, then obviously you can find that you you are deviated from what you uh originally thought, and you can make the adjustments as needed. And that's it. That's the power 45minute hour. [Applause]