Jason Maynard - Security Knows Viruses but the Pandemic Introduces New Challenges to Security Teams

Show transcript [en]
okay we are live uh hello everyone uh the next i would like to next presenter uh jason maynard um first of all i want to say he is like speaking like you know consecutive third year in the row and uh that's like you know kind of an achievement like you know in itself uh so thank you jason uh for like you know speaking so i would uh like you know kind of go through the jason's uh introduction so jason maynard has been architecting designing and deploying security technologies that secure the most complex computing environments for almost two decades his understanding of technologies people and process enable him to deliver effective comprehensive security solutions that align to an organization's security
goals and strategic imperative json is adapt at addressing a range of risk profile across industry vertical skills he cultivated as an end user security practitioner partner integrator and now manufacturer as senior technical solution architect cyber security for cisco system json is also active in direct community speaking at bc aware privacy and security conference and as i mentioned before he delivered sessions uh all like you know all all the be like you know most of the b side i think in canada uh jason also hold like over 75 plus designations that's a lot man across a variety of product and technology including cci designations so uh just gonna talk about uh as you can as you can see on the screen security
no viruses but the pandemic introduces new challenges to the security team so over to you jason awesome thanks harv and thanks everyone um that's uh that's organized b-sides you guys do an amazing job and uh kudos to the entire team um yeah so this session should be interesting if you saw my session uh last year um you would have seen about taking a step back and looking at it from a different perspective when it comes to securing your organization we're going to do a little bit of that again we're going to build on that initial session uh but we're gonna talk about some of the things that we've seen during the pandemic um i know i don't have video i'm actually
in the rockies i got a thousand millisecond latency link so video's probably only gonna uh hurt me uh at this time but if you want to have a visual think of me dressed up in a suit um you know uh all cleaned up i'm not shaving the beard has only gotten longer um but in reality i'm still in my pajamas right but that's the way it is with uh covet 19 and and 2020 right all right so let's talk about the initial focus so you know during the pandemic you know every one of us that uh drives any type of security component within any organization it was all hands on deck right and and so we were focused on
increasing vpn capacity right and and that was probably the the core of most uh if you're a networking engineer security practitioner didn't really matter it was really trying to keep businesses alive right people had to work from home and we needed to start leveraging and adopting you know some of the traditional methods that we use today and uh vpn was a big part of that and a lot of it was centered around vpn licensing and increased capacity so we work on that head end and we'd ensure that we've had enough capacity required to satisfy the need problem was is that after we did that other supporting infrastructure started to fail right and um and that
could connections per second on on switch infrastructure uh firewalls etc but we've never built uh the vpn to to be able to run the entire business on right it wasn't at the forefront it was always there just in case for a pandemic but it was really meant to augment certain users that that needed the capacity to work away from the office not to run the entire business on and so we struggled and that over subscription could have been internet circuits could have been like i said switching infrastructure and then and then what we did was we in order to satisfy this and again this sets the framework of why we want to take a step back is
that we started saying well wait a minute maybe we need to offload some capacity and and so this is where we start introducing things like split tunneling right we start saying you know what things like sas based services if we have office 365 in the cloud should we back all that through a vpn connection just to go back out to the internet um what about things like netflix can we control users accessing those resources and again the burden that it would put on our infrastructure if we were to pass it through that vpn tunnel and so we started shifting some of those applications um to go direct or not even come through that internet or that vpn connectivity
obviously there's challenges when we start doing that and then what we did was we started adding web services right so we said well wait a minute some users don't even need vpn connectivity what they need is access to this specific application and so we may have introduced that to the internet and use native tls as a security wrapper to give access to certain individuals to these services and then we extend that beyond that right we we start looking at um sas right uh we may have already had some things in in in the cloud already um the other thing is this may have forced you to move things faster so you might have had a hybrid
exchange environment right with uh office 365 in the cloud and and so it may have pushed you to move faster to adopt that full cloud-based capability or sas based capability and then what we've done is we've increased you know the amount of users that aren't really used to working from home right i mean i've been working from home i think over a decade now um but um you know there's a lot of people that don't outside of i.t right i.t may have had more of that flexibility but the the average user used to go into a brick and mortar type facility and and do their day-to-day uh job um and now we've said here's a
laptop go home and don't come back right and and connect and and so we've exposed them to an environment that they weren't they were not used to right and and they're always used to you know when they connect in inside the organization there's some security controls that are in place and so they probably don't realize it but there there's things to make sure that they're safe that may not be in play when you work from home and so security right what about security in all of this right is there an issue is is there a concern we've done a good job of giving people access quite honestly it's the biggest proof of concept i believe in it
ever right ever we've forced the entire world almost to say get out of the office and work from home and use technologies uh that you know some users haven't used before at a capacity that we've never seen so it's been a a tremendous trial and i think it has tremendous impact on how we move forward right and you've got to think about this what about covet 2 like phase 2 what happens in the fall right do we users have to be sent home again right do we have the capacity and and that right if if it has to increase but not only that many organizations i believe are going to realize that this work from
home model actually works and if it works then do i need to to have brick and mortar right or as much of it right and i think the commercial space could be in trouble um uh you know moving forward right because of this so don't believe me um security is is a real problem especially from work from home so what i've done is i've went to you know cyber security infrastructure security agency like cisa and and i i just looked for you know elements around covid and work from home um and i found there's no shortage of threats out there actually we we're seeing an increase in in threads and so again here's one that talks about
covet 19 loan relief web page and phishing emails right so the threat actor is is using covid19 to get people to bite right you've got you know hopefully this doesn't happen today um but uh you've got uh you know all this video conferencing type technology um and and you've got to consider you know if somebody jumps into a meeting that shouldn't be in a meeting is it secure and encrypted these are all things that we may not have thought about originally when we started onboarding some of our capabilities right we were so much in a rush to get the capability in play that we haven't actually taken a step back and really looked at the threat
landscape right and what it means from work from home malicious activity targeting covid19 research vaccine development so there's a big push to be first right and so you've got to think any of these organizations that are doing research around vaccine development development are certainly at higher risk at this point in time right whether it be state sponsored or other doesn't really matter the threat is real right people want to be first or countries want to be first with vaccine development so either they're going to steal intellectual data or what they're going to do is compromise the data that you have so the outcomes may not be the outcomes that that you would have seen because there was some
compromise somewhere ddos attacks are have increased by 500 percent uh again because of covet one of the elements we've got to think about is is that i don't now have to worry about just disrupting your internet as an adversary disrupting your internet would cause issues right normally it would anything going to the internet would be at risk right but usually when you're in a brick and mortar type facility all of your resources are usually accessible still right it's usually not going over that same internet circuit it's either back hauled internally or through a dedicated circuit of some some sort and so internally i have full operations my teams continue to function yes there might be some
disruption but it's not massive now i have to target all i have to do is target vpn head ends as an example or some web-based service that that you're having your users leverage to continue operations i just have to target that so it could be a volumetric attack right which means i could you know shift traffic to the internet and scrub it or it could be more service impacting focusing on you know a certain service that you're offering and try to impact that service and not worry about trying to saturate your your uplinks but it becomes a tremendous problem with vpn and here's another alert around enterprise vpn security and again it just talks a little bit
about um you know some of the elements here right as organizations use vpn right more vulnerabilities exist the adversary has adjusted its tactics it's um it gets a little bit more difficult around patching right because vpn becomes you know 100 reliable or and so you know when do you keep the patch updates now for your vpn you've got phishing emails that are targeting teleworkers again stealing usernames and passwords if i can get your vpn username and password there's likelihood that i i'll have full access into the organization right and so you might say well not my organization you'd still be restricted based on that that user identity um but many organizations may not right again it depends on how fast you move to
get these users uh onboarded uh so they can work from home and then we've got things like you know multi-factor authentication if we're not using it we're more susceptible to phishing attacks right and um obviously i mentioned this one already around you know the vpn head end becomes a very critical service to keep operations up business operations up that is and then another one here again it just kind of walks through a little bit and using covid now as the theme as the lure right so now you've got fishing that's got coven 19 elements wrapped around it you've got malware distribution points uh domains obviously have coronavirus or kova 19 names in them now um and again
um they they continue to target and here's a couple of examples right where malicious android app um provides real-time coronavirus outbreak tracker right that sounds usable usable right that's something that i might want but instead it downloads uh you know it and gives the uh administrative access to install covet lock on on this particular device so it's ransomware for the device but as a normal user you know i'm thinking that this application is going to help me right especially during the pandemic and and and to be quite honest many users including myself this is where we're going to get our information we're going out to the internet and trying to understand what covid19 and coronavirus what it looks
like in our neighborhoods what we can do to minimize you know our risk and this one here it was it definitely hits home right this is in canada where um you know we've seen a shift where the adversary is so clever right is that wait a minute what about if i tell the user that their account has been breached and i'm here to help them right so now they're using the the aftermath of a breach as a way to entice you to maybe click on something or provide some information and this one here actually hits home for me specifically because i i know somebody very close to me that actually had this happen and this is where you know august 15th
the canadian government announced that 5500 uh cra accounts were compromised and they used the credential stuffing attack so basically what they did was they went and logged or they breached and got credentials through other breaches and used those those credentials to log into cra they logged into cra they changed the direct deposit information of the accounts and then they applied for covet 19 whatever relief uh you know things that are available to canadians and had that money deposited into that account uh and then got out of there right so so it's real right um work from home and the pandemic has definitely increased our overall uh risk profile so we're gonna take a step back as i
mentioned right we're going to look at this based on a a use case and we're going to look at it from what security wrappers do we think are required this isn't vendor technology this is capabilities right so we'll look at the internet use case don't look as when you see the flows don't look the the cloud is just meaning that this is the flow that we're looking at but uh the internet use case will include users going directly to internet or split tunneling um oh went the wrong way here sorry the next one will be sas use case right include users going directly to sas based services using native tls typically and then you've got vpn use
cases right and now this is where you're terminating to a vpn headed as an example and so we want to think about things like phishing and malware but also you know prevention's awesome the reality is no matter what technologies you have how well you cobble them together the adversary is going to win at times and so you've got to think about the other side of the equation right do i have the data do i have the information i need to be able to determine what actually took place and ultimately build in mechanisms to defeat the adversary moving forward system hygiene right ddos direct internet social engineering dns outage right split tunneling now dns outage is interesting right because you
don't think of how critical dns becomes when you start using sas based services right if i can't resolve can i still get to office 365 so who you use or what you use for dns now becomes something that you want to consider obviously inside you would do that you most likely have your own infrastructure that supports this but now they're working from home it may not even be vpned in directly into the organization credential theft and we can go on right we've talked about many of them and so this is where i build this out right so now we look at an endpoint and we we we we have a user and they're going to connect and and we're going to build
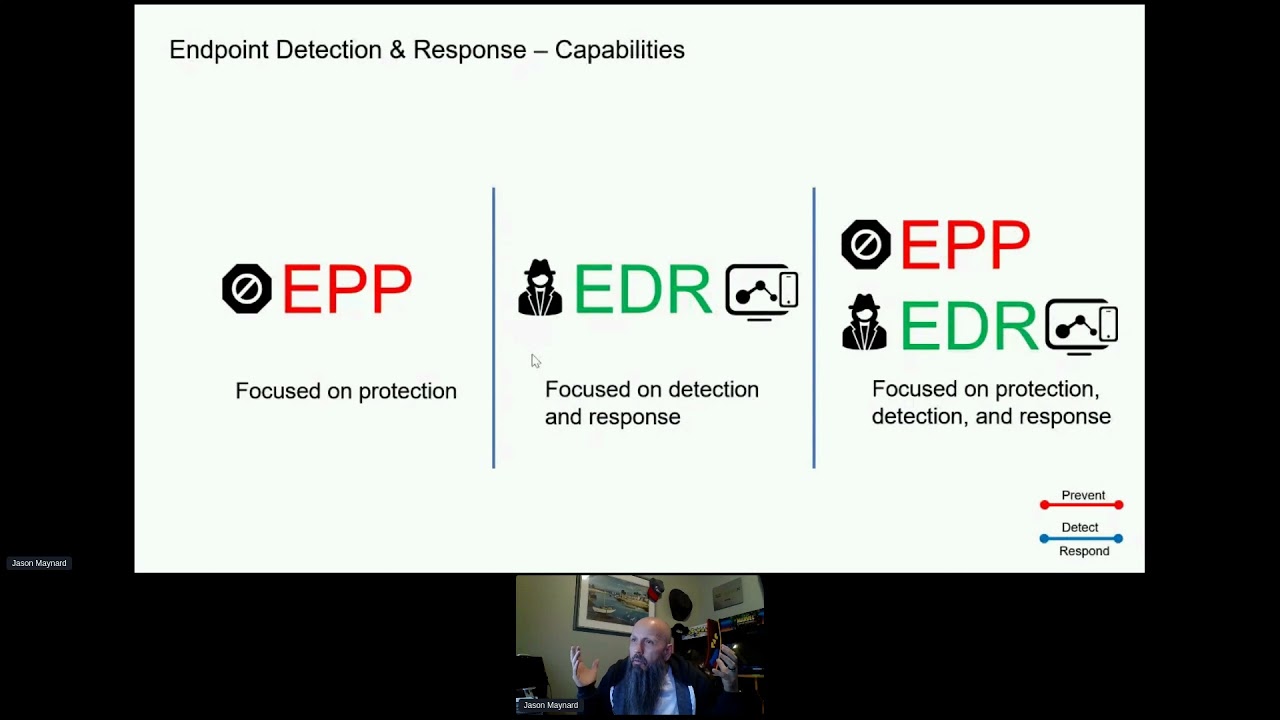
out these flows together well it's really going to be me you're going to be listening hopefully um but um we'll look at it from two lenses right i thought about this at first and i thought you know what i would break these up because you've got a prevention capability and then you have a detect and respond capability and and so what i've done is you know if you can prevent something that's great right detection well you've already prevented it so you had to attack and response well you blocked it right so there is already somewhat of an inherent response there because you prevented the attack um but i break them up and we'll walk through this together
we've got uh patching right system hygiene it's still a big thing right if we can patch 100 of everything we'd be in really good shape but you got to think about that work from home user right how are you patching those systems right how are you keeping them updated right are you using some management platform internally using some type of tls mechanism to secure it are you doing it through a vpn connection when they connect but what happens if they don't connect what if it's 10 days that they don't connect because they used a sas based service and there wasn't a need to connect to the vpn right so these are things that we want to think about
exploit prevention right so now we get into defending your endpoints for from things like memory injection right and these attacks are commonly seen with malware and zero day and they attack unpatched software and then you get into system protection process right so we want to make sure that those system processes are not being attacked by other processes on the system and again this is focused on capability right i'm not saying this is a technology that you need it's just the capability that you've got to consider advanced malware and av right that's obviously commonplace nowadays but you want to make sure that you're using something with multi-engine platform or multi-intelligence platform right that has different insights into the threat
landscape and hopefully different ways of detecting whether or not something malicious is happening malicious activity protection so what happens if as an example something does pass your defensive capabilities right we know that that's a reality it's going to happen and what if it starts encrypting the drive just starts to do it right do you have a mechanism maybe to stop that particular process that's invoking something that you deem as malicious right so these are again things to consider application blocking so again you might want to make sure that certain applications aren't uh able to operate on on a mobile endpoint right no matter where they are um but but the other use case and i've
worked with someone recently on this one is what happens if you have to let somebody go um right and um and they're not coming back to the office necessarily right and so they've got to ship the laptop but from the point of when they ship the laptop to when you receive it you're worried about whether or not there's some localized data on the asset now nobody wants localized data but do you have controls in place to mitigate against that that that would be a question so you can use something like app blocking to do something clever right right so say there was a termination that took place um obviously you shut down all the access internally vpns active directory
all that magical stuff um but i can also maybe build a policy that says block explorer.exe from launching right and so if the user uses the laptop and flips it up it gets the update um they try to log in uh there's no shell right the the asset becomes unusable at that point in time so again being clever with the technologies that you have network blocking so the ability to you know block you know l3 l4 type controls right and again this doesn't always necessarily have to be on the end point this could be anywhere else but the thing the way i you know some people argue defense in depth whether it's dead or alive i do believe
that if you have multiple controls in multiple different layers your success of either defending or making it so um uh so um difficult for the adversary to be successful that they move on right and so you know you want to look at this as a multi-prong approach for sure usb blocking so this becomes another issue right maybe not an issue that we thought was a big deal when they're on premise but now off premise you know we've got students from from home right and so people are scrambling to get their children asked access to laptops and devices and and so maybe you know they're using their work laptop even if policy suggests otherwise you know people tend to you know
again want to help their family members and and they don't suspect anything risky is going to happen because they don't know computers and so a student comes in or the family member that's a student comes in and plugs in the usb device opens up a pdf the pdf has malware on it right and so you might want to have some controls there to force the data to be in a file repository in the cloud maybe or on premise as opposed to coming in through external devices intrusion prevention i think that's commonplace firewalling right so you got network blocking based on l4 l3 l4 based on um maybe you get some security intelligence to suggest something's bad and so you just
don't want to communicate outbound and then you've got you know standard-based firewalling that might be built into the system itself or through a you know an application that you've purchased you get fileless uh malware right so this is where we get into um you know again taking advantage of uh memory and injection and running code and memory and evading and so exploit prevention and system protection process those are some elements that are going to help you here but we've got to consider file lists as well and then you get into you know some more of the buzz buzz terms right uh ai and uh machine learning so machine learning is a subset of ai uh
but machine learning you've got to have a lot of good data and a lot of bad data in order for those algorithms to really mature but it's something you want to consider right on the end point and so that kind of rounds out prevention and somebody might have their hand up saying well wait what about what yes there could be more there could be less right um but you get the idea really taking that step back i haven't even talked about what i'm connecting to yet i'm just talking at the end point at this point these are some of the things that i would consider these are things that i've been talking to people about
over the last you know probably five months uh ever since covid really started and then now we move into detect and respond right so now you you know buzz terms like endpoint detection and response right the ability to understand that a word uh document was opened by windward and it executed a macro the macro then reached into powershell and reached out to a ip address pulled down a dropper file yada yada right the story of what happened um tremendously valuable especially now that you don't have access to these resources as much as you did before when they were on premise forensic snapshot right i need to be able to take a snapshot of that endpoint
at any point if there's an incident can i do that what if they're not connected to a vpn what if they have direct connection to an internet can i can i get the data i need again this could be a very big breach right and i need some additional insight and maybe it all started here um and so i need some insight from that endpoint host isolation right the ability to be able to minimize the overall risk of that endpoint if it was compromised right so once you determine it has been compromised what do you do right okay so maybe you have edr maybe you can take a forensic snapshot but can i isolate the house and still um
you know do my investigation let it have limited access right so these are things that we want to consider because vpn isn't going to always be there cloud-based ioc so again enhancing the technol or the intelligent stack that you have and again based on certain activities and patterns you might have to flag indications of compromise now this doesn't necessarily have to be cloud but i see the trend moving towards more of that big data you know uh data uh intelligence you know that that typically comes from the cloud uh because it's too big to build on premise command line capture again if if power shell's going to be invoked i i don't only want to know that
power shell was invoked i want to know that it was power cat minus c [Music] 4.4.4.4 minus you know p444 right i want to know the exact command line that was or you're using powershell to download a file and start the process i need to know what that command line um that was passed within that that application that was used or processed that was used you've got sandboxing and file analysis now i didn't put this as a prevention capability because i feel that sandboxing takes a bit of time to do and in order to do that um you can't stop an http connection mid-stream and say give me seven to you know five minutes or five to seven
minutes to execute this payload in the sandbox environment come out with a disposition and update you late right before you can you just can't do that it's impossible um and so um i see this more of an after uh thought so it may have been sandboxed right then you've got to think about okay now you know the disposition is bad how does it tell the end point about the disposition and what does it do with it but also i need this to be able to do my own analysis right if i need to submit a file or review a file that was submitted i want to know what registry entries network connections i want you know p caps i want um you know
what behavioral indicators were triggered i need to know all of that right to help understand the full context of the threat that i'm dealing with and then we move into vulnerable software right you can't be successful at patching unless you identify the vulnerable uh software sure you can do it regular every tuesday right patch tuesday but there's other software that might be on the system that needs to be patched as well and and i want to be able to tie vulnerable software to any breach that might have happened that's key to me right because if if i can mitigate the vulnerability i essentially break the the adversary's ability to be successful but if i can't tie the threat to the
vulnerability um or the breach to the vulnerability then it's just going to continue to to happen ipfix or or network flow data right from from an endpoint where it ties in the process to the network connectivity that it's making and so some of you might be sitting on the edge of your chair say well wait a minute isn't that what endpoint detection response does kinda right it does but it's usually limited to the number of flows per application that it that it actually tracks what i'm talking about here is every single application or process that makes a network connection regardless of any threat is actually being monitored and tracked all right now we've got the end point
right some people might be saying well the endpoint would never run if it had all this stuff on it right but you certainly can do that in today's world right agents are becoming uh thinner and and streamlined um there's some things here you can use uh you know a couple of products with some are inherently built into the operating system just have to expose it and then others might be you know based on vendors that you that you might deal with right but you want to look at that both from a prevention and detection and response perspective so cool but before we even connect any services there's some other things that we want to consider
like dns security right again i told you earlier that now your vpn head end or your sas based services all of these dns records that you leverage have to resolve and if they don't resolve then that service will be down disrupting your users so dns security becomes not only the an ability to make sure that you can resolve services but also a mechanism to prevent threats right dns is a first-line capability when it comes to breaches right dns has to happen before i make a connection and so it gives me an opportunity to cut it off sooner in the attack chain web proxy right you might want to have proxy why well now you want to run additional
inspections against that payload if you're waiting for the end point to catch it because you might be saying well wait a minute you know you could say dlp tls decryption and advanced malware wait a minute i have that here right like so why do i need it here right it's going to see it here i'm a big believer that if you wait for the end point to solve the problem right just to solve the breach it's always too late in my mind that's not where you want to defend right now you have to defend there that's a reality because you can't trust the other controls that you have elsewhere are going to be a hundred percent every
single time and so you need something at the end point but if i had it in my mind where i wanted to defend i want to defend as far away from the asset i'm protecting as possible and so web proxy allows us now to do dlp we can start thinking about tls decryption it's more specifically around um you know tls 1.3 and some of the implications that are caused there around decryption and then i could do advanced malware inspection and then i transitioned from the prevention side to okay what are the other things that i would would require so thinking about this is dns forensics right that this becomes tremendously valuable again determining not only about what
took place but also maybe understanding the attack infrastructure right that that that is being leveraged so dns forensics becomes highly critical full uri capture so if you are doing proxy or the need for proxy exists again having that full uri is certainly helpful sandbox and file analysis it's a proxy connection and so if you've got a sandbox it's http you can't keep that connection open forever and so uh you know you've got to do the sandbox and file analysis very much the same as what we talked about on the endpoint and now we move into the internet connectivity right and so this internet connectivity might be a little bit more open here right because they're not coming to
a vpn head end or a sas based service now in this case i'm showing email like it would be a sas based service and and i'm not really focused on that side of it um today but you also have to look at that if this is web conferencing as an example you've got to think about is it is it secure is it encrypted where does the data reside like these are all things you got to think about on the services side especially if you're exposing it like you've never done before and i used email as an example here and i'll continue that theme moving forward so we only have to walk through this once but you've got reputation filtering
right spam business email compromise advanced malware protection again right like you might be saying well wait a minute it's already here right well yes but if i can block the attachment from ever the user clicking on it i want to do that right and so here's an opportunity for me to extend that capability here and prevent much sooner in the attack chain gray mail phishing right anybody that's done anything around email security um you know knows these are fairly common capabilities that that would exist today in any mature email security offering and so url protection is another one and so some people and i've heard this this comment uh you know talking with many people across the west
is why do i need url protection here at the email level because when i click it isn't that dns going to do a dns lookup and then i got this web proxy capability you're right it does right but if i can actually defang it in an email so nobody clicks on it i don't have to worry about whether their dns security had intelligence to know it was bad right i was already able to to mitigate that risk or maybe i redirect that that maybe for proxy as an example you've got sandboxing now you notice i didn't say sandboxing and file analysis i've left file analysis both for detect and respond sandboxing i included here is a
prevention capability because the email is never you know instant you have an opportunity here to hold email for a little bit longer and therefore you could run it through a sandbox get the disposition back before um before you ever send it to the user itself dlp right and then you get into some of the forensic pieces right the detect and respond right message tracking i want to know everything about the message file analysis right i want to know behavioral indicators again it's more of the same so that's email right on the services side so we won't do that again although the theme will carry for vpn and sas right but you get the idea of
the process that you want to go through uh when you're building out your overall security posture and you have the opportunity to do this right um now this isn't too late you might say well we've already got things employed great figure out what you need figure out where the gaps are and address them right there is an opportunity still to make the organization more secure so now we get into vpn right again this is not a termination point right so don't say well shouldn't this be here right no it doesn't matter this is the flow right you've got all kinds of different controls wherever so ddos right again now we know it might not be volumetric type attacks
although they still exist and you can use scrubbing stations etc to be able to you know offload that volumetric attack into the cloud as an example but now you've got service focused impacting um ddos capabilities and now they're trying to take down your vpn service why because they know that now you're going to be running you know maybe you're running at 80 um from work from home i could drop that down where it's very difficult for you to operate tls decryption again if i'm doing a network based inspection here right again i need to do tls decryption right or else malware and ips all of that stuff becomes i i'm blind to it right and again i know
some might be sitting there saying well tls here it's open here tls here tls here lots of t yes there is again i want to prevent you know as far away from the the the individual i'm protecting and so if i have an opportunity to block advanced malware here even if this was going to catch it i want it blocked here again if this fails i need this capability to hopefully catch it and again the the green stuff right all this stuff here is key in case you do get breached all right so you got multi-factor authentication you got endpoint posture right geo control you might not think that that's much of a control but it certainly is something that
layers on the complexity that the adversary has to overcome right they've gotten out proxy and take other methods you've got l7 firewalls right now we're getting into application control and again that might be shifted to an endpoint right or in the cloud um but it could be a network-based device as well that's more traditional you have ips you have advanced malware inspection behavioral based policy like the ability to be able to understand that this is a critical asset it's talking to a critical resource i have this software version on it and there's an indication of compromise right so i may be on all those factors want this to be a certain impact level so i can
actually address it then you get into web application firewalling you got device insight denied authentications right host profiling impact analysis sandbox and file analysis right so impacts analysis and host profiling are key and the reason why they're key is is that if you don't understand the asset you're protecting how do you understand the impact of the threat that's coming in and so those two work together right but these are things that you want to consider whether you use it in the platform that's being offered or you try to figure out a mechanism to do it externally vulnerability insight again if i know the vulnerabilities that are being targeted i can get them patched in the meantime maybe use ips signatures
to minimize my risk here you got flow analytics event packet capture um and then um and then you've got event workflow right so this is the ability to pivot and understand what the threat looks holistically right from end to end ultimately and then you get into the application right and again so sas space there's a couple here i'm going to move because i'm already getting the 10 minute warning so multi-factor authentication right for sas based service right we'd also want multi-factor as i mentioned for vpn right or any other service that we're offering the more critical the service obviously the the more critical multi-factor becomes endpoint posture i want to understand the end point right before it's
connecting to that sas base geocontrol we've already covered that you've got restrict non-sanction applications right so applications that exist for example if you have one drive and that's your file repository what about dropbox box and all the other file repositories the user can still get to remember they're not plugged into the network and they're not going through maybe a next-gen firewall that's doing application control right they might be driving this because they're they're directly connected to the internet and using that sas based service so we want to make sure that those data that data is not being moved over you've got sas based dlp as well and then you get into device insight denied authentications right i want to know if
multi-factor fails then there's a good indication that a credential was stolen right because they got to the second factor and it failed shadow i.t and community trust rating so the ability to understand the applications my users are using in the cloud and figure out whether or not these are should be moved to sanctioned applications user identity behavior analytics if i log in in edmonton to salesforce and then an hour later i log into um uh uh office 365 from maybe the continent of africa or whatever right if i've logged in there i can't be in those two places uh very quickly and so i need something to tie that together to let me know that that actually took
place and there's risk and then you have the service at the end right so whatever it is email web uh some web type platform doesn't really matter salesforce etc right you've got to think about the security wrappers for that application as well not only within the app right as tanya was mentioning right the applications need to be secure but also anything that's supporting around that application right as well and so this is now what you end up with right so this looks a little bit more interesting now i have a better picture of what i need and now i need to figure out what are the controls or what are the technologies that are going to help
satisfy these these needs but it doesn't stop there right i think that's understanding the controls and the the the the ability to detect and respond in case of failure of those controls but then we've got to think about what happens in instant response and threat hunting that that user might be mobile right it's they're not connected they're they're directly connected to the internet and maybe not vpned in so how do i hunt right for threats and so you know lots of people are building data lakes data lakes are very expensive to do and i'm not saying you shouldn't do it but if you're not down that path um what you want to be able to do is
hopefully leverage some api based platform that can actually query the technologies you own and provide you insight and hopefully visuals of what that threat looks end to end right so i should be able to say i know that this is bad this is a an indicator it's a shaw an ip whatever ask the platform questions and it tells me i've saw it in an email attachment with this subject i've seen a dns request go to this domain and i've saw something on the endpoint and i'd like that all tied together and show the relationships between them and then you've got orchestration and automation so the ability to be able to um orchestrate and automate um some of
this right so building out playbooks becomes key right and and and even if you haven't done this and i've got an example here that you guys can see in the um the pdf version that i'll share with b-sides later but it walks through going through in the incident response um consortium and you know you grab fishing and you walk through fishing you build out the playbooks that's meaningful for your organization but you got to think how can i automate some of this stuff like if i see a fishing link come in wouldn't it be cool if i can say okay abstract those observations query the rest of my technologies tell me the results of all of that
based on my environment right and also then take a forensic snapshot move the asset into isolation uh create a conference room with the right incident responders so they can collaborate and potentially take action right additional action on that threat and so maybe that's for some a longer term strategy but that when you're building out these you have to be thinking of these as well and then you've got threat intelligence that's going to support all of this right whether that be third party in-house outsourced doesn't really matter the intelligence comes in and so can i use these platforms to be able to feed that new information into to provide prevention capabilities and then also be able to query that data
as needed for instant response and so i'm coming up to the end here i've included this just to be complete here so i'm not going to walk through it in full but if you're not aware of irc not irc chat right but irc is the incident uh response consortium um check it out right they've got tons and tons of community-based uh playbooks that have been developed and you can grab them download them and modify them right there's no no restrictions that i've seen and i've worked with a lot of organizations that universities as an example that certainly leverage uh this this this site to help build out some of their playbooks and so you got to prepare right you got to get
the right teams together you've got to review a maintain a timeline and you might have some interviews and you're going to have some you know an internal path and your document that an external path then you're going to get into detect right so what is it that we're actually looking for what are the threat indicators right we need to understand those and then kind of develop them right like emails that are non-re uh returnable or non-deliverable right or emails that have been linked to an external or unknown url right and so these are my indicators and i need to categorize those requests maybe packet capture conduct content scans now think about these elements too when
you're doing the playbook are these manual can you automate this right these are things that i would want to do right i don't want my team focused on trying to capture and pull all the data right they're too smart for that i want my team focused on analyzing the having the human element right let the technology do all the weeding out of all the noise but i need my humans to be able to look at it understand the context of the threat based on the business and be able to come to the determination to understand the risk to my organization analyze it right we need to then define the risk factors right log collection evidence collection
data capture etc then we move into contain we want to contain it right so how we gonna do that right servers desktops our credentials stolen right uh what other services are impacted again here's a nice list of elements that you want to consider almost done harv uh eradicate um triage uh and confirm incident uh a report right um and ultimately eradicate the malware that's the goal um and then recover recover those systems incident remediation and this one here post incident handling although the others are very important this one i think is critical right it's at the end everything's been done now you need to go back and revisit right and learn from that um make sure that you're applying those
lessons and and you're adapting your your processes to accommodate the things that you've learned during that incident and so again you've got to think about the use case what you're trying to secure um and build that out with a longer term strategy in mind right you might not be able to get there day one but you want to build towards something and building it out based on flow is going to help you identify what you require in order to be successful and that's it and yes it's anonymous but i i like it oh yeah awesome presentation again you nailed it um thank you for that um so uh i have one question from the audience um the question is
this for work from home during covid 19 times what is the best strategy tips for security awareness training for end users who are already under stress
so so sorry say that again harv i i kind so so users are under stress they're already working from home yeah what's the best strategy for uh security awareness training like you know who's uh already under stress working from home user so that's the question so restraining yeah i'm sorry i'm i'm i'm missing the security awareness strategy security oh sorry i got it gotcha it could be that latency on my side hurt um yeah so i i i think security awareness training is key right that's more than ever um because uh again many of these users aren't used to it so there's lots of different platforms out there that'll actually go through uh and grade them and test them and it's
not they don't feel like they're being um you know uh graded in the sense like in school right it's almost more like playful type uh training exercises that you can go through right um and it's not something like you're bad it's like you're fantastic and we're only getting better but there is a lot of platforms out there that you could leverage for security awareness training okay uh um thank you very much jason uh like you know once again uh you are the one and only person who are like you know here for uh three years in the row you know consecutively so i think we have to plan this to bring you every year so um
yeah so we will be taking break and we will be back at 1pm so i will encourage everyone to please uh visit the uh sponsor booths in expo section there are like new prizes and some draws are like you know kind of brought by the sponsor so please visit them thank you