BadXNU, a rotten apple!
Speakers
About this talk
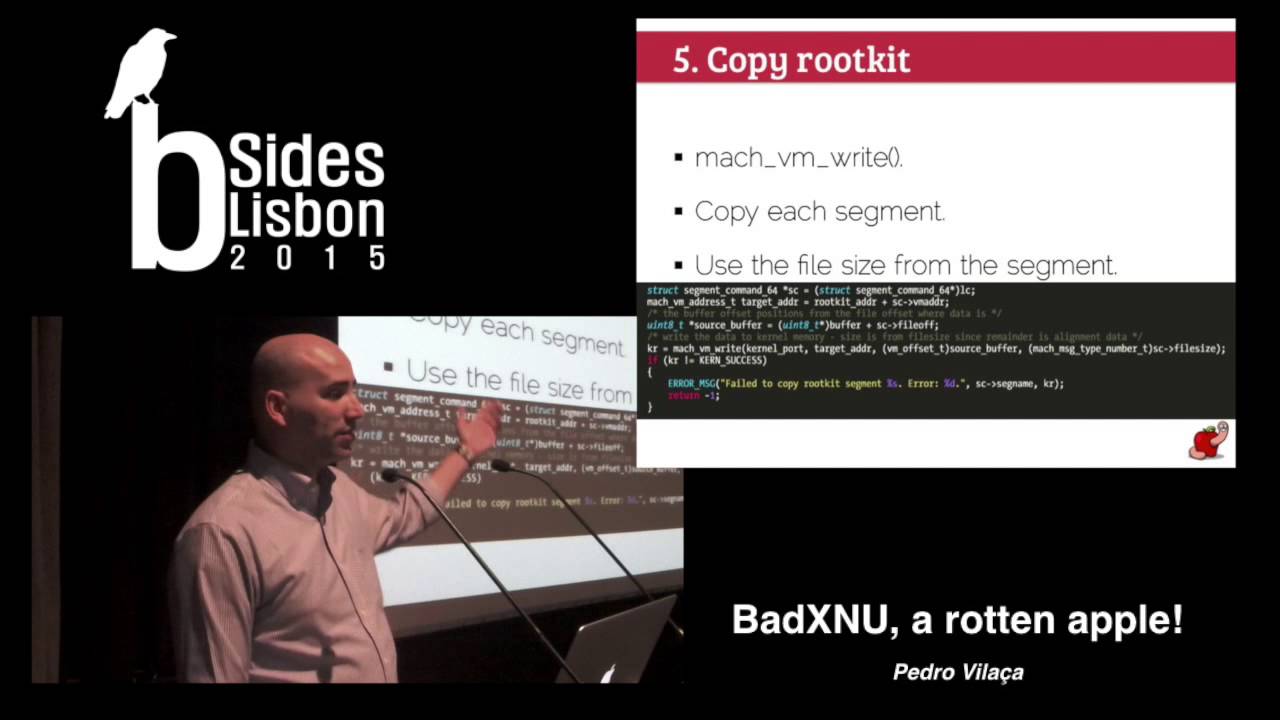
Your latest OS X 0day exploit got you root and now what? Apple (finally) introduced mandatory code signing for kernel extensions in Yosemite so there's a new obstacle to your beautiful kernel rootkit. Are you an OPSEC ninja or too cheap to buy $99 a code signing certificate? You can't or don't want to steal (because it's morally wrong!) someone's else certificate? This presentation is about solving these problems with techniques that allow you to bypass code signing requirements and regular kernel extensions loading interfaces. The goal is to convince you that kernel extensions code signing is a joke because its design is flawed. But this isn't enough, challenging, or even fun. I'll show you how to abuse a public known vulnerability that is still present in all available OS X versions and also a feature available in Mavericks and Yosemite, working around some "protections" in XNU kernel. The full source code for both rootkit loaders will be available so you can poke around and hopefully learn a thing or two. Hopefully this will be more than enough to convince you that there are serious issues in the OS X platform and something must change at Apple. The only requirement for this talk is uid=0(root). Well, the world isn't perfect but there is hope. Google Project Zero has already shown how easy it is.