Memory Corruption is for Wussies!
Show transcript [en]
hold on okay I have a start so welcome sir time on bides it's a pleasure to be here it's uh very interesting to see the conference growing up more people are coming the conference is has better better place to to be I hope one of these days it's not besides anymore and it's whatever uh conference name and the B conference because Portugal is a nice place and I will help them as much as I can they know this I will not help them with the logistics because that's a pain in ass but I will speak and I will do whatever I can I will put the the contacts and and everything to to help them so it's let's start this which is a
fun presentation who am I so as Bruno said I'm a besides lisban resident speaker non paa so this year I just spoke once at sisan in Singapore and I was thinking about stopping speaking for a while sometimes you get tired and then they told me oh yeah you are speaking at be light so okay I have to speak I have to get something to to speak but it's still uh it's my pleasure to to be here two months ago Forbes uh launched an article with a list of what they were calling Apple security rock stars I was in that list because allegedly I was called to the Mother Ship meaning California for kickstarting the security
bubany I cannot tell you if it's true or not H I didn't say any NDA so I'm telling you that I was there uh if you ever have any any bug in iOS Mac OS and you want to disclose to Apple uh you can contact them uh feel free then they will be open to to you or if you want if you have something really interesting I can help you directing to the right guys inside I will not take a fee or or anything I will just tell you this guy is is there and there uh there's a guy from Microsoft Jason which is a very nice guy he just moved to to Microsoft uh to Apple from Microsoft and he's
managing the the bugbounty program there so I know the guys that that get this stuff I work for this company Sentinal one uh which is the next Generation AV what is called Next Generation AV helped to create the Mac products the first version I created with another colleague uh right now I I don't have anything to do with development I just break stuff I don't develop so I'm not a good engineer since I'm I am an economist by by by training for those who who know me but if you are looking for uh Next Generation Solutions AV uh we have an interesting product sorry for the product pitch but it's very quick so there are more competitors this
interesting technology have a look at it at least know it it's it's uh some interesting stuff that might help to to fight problems on your companies what's today subject uh I want to present uh some zero days uh or dead zero days because they were zero days uh some months ago it's a very interesting bug I used to love this bug it's a a Pity that I had to kill it um but I will show you uh this bug I will talk about the internal some internals about Mac uh and this is all the everything all the topics usually I have very long presentations is is the as usual uh lots of interesting information I hope you
learn something uh probably we'll have no time for questions but feel free to nag me if you want to understand some other details about about this presentation so our Target is system Integrity protection if you use a Mac uh this was introduced uh last year with El Capitan what it's happens with this with this feature is that the power of root user is reduced meaning that even as root you cannot do the same kind of operations that you could do before for example there are some protected folders if you try to update them or write a file even as roots you cannot for me I see it as a systemwide Sandbox basically your whole system your whole Max since
El Capitan is on a Sandbox on a system sandbox There are rules that say this program this application can write to this folder or most applications cannot write to to the folders or do certain certain operations so it's a very interesting feature there was a lot of confusion when Apple was introducing this because Apple introduces everything as a secret they didn't talk public about about this thing and people didn't really understand everyone saying ah they are killing the root user more or less as the iOS with a with a phone with the the Jack the audio jack people don't apple is not good to explaining what they want to do and this is one of the
problems of of Apple I've been talking to them okay let's change put in information it doesn't kill you to put a white paper telling this is our goal for this feature and this is what we want to achieve and so on because hey if it's binary we can reverse it you saw in the morning the machines can can be used to automate all this stuff it's probably the future or if you give me I and the binary I will reverse it given uh enough time I will know what it what is doing this protection is based on this on on the on the macf thrusted B frame framework uh this came mostly from FreeBSD it's a very interesting uh
technology I love this technology Apple says it's a closed technology it's not supported but they have been saying this like for three or four releases it's still there you can still work with it you get a warning but you can do a lot of interesting stuff on on top of this because you have many hooks on the system that for example you say I want to this process doesn't uh access a file or this process cannot fork and so on this is the Bas technology for for iOS for one of the features of security features of iOS this is where iOS sandbox is implemented on top of system Integrity protection uses code signatures uh makes sense it guarantees
you something about the minory and what they call entitlements entitlements is basically uh an entitlement that says okay you can do this operation or you can do that that operation one of the problems is that uh they sign too many binaries so they have a system where they create a feature that the system wasn't designed for that feature so you are putting something on on top and you need the binaries to to to do to continue to do operations else you need to reengineer the whole operating system Apple didn't add time for that so they put uh created an entitlement system if you are old or if you come from from Unix world this is basically
the the same thing as ID binaries what they are saying okay you have more more uh how do you say uh you have different entitlements so SD is basically one bit that you to you you put on the binary and the binary can do whatever root operations uh you you want this you have a bit more control over what the binary uh can do but still there are too many binaries you can consult this database from Jonathan Lev which is a maest researcher uh and also wrote some very interesting books if you look at this database you can see like 100 binaries with entitlements so there's many targets many targets to if you want to
attack because this system uh I'm pretty sure you can already see vulnerabilities it's the same vulnerability as a SV if there's if the binary has some authorization and if you can run arbitrary code on that binary then you can do whatever operation the binary is authorized uh to so what you get is this you get everyone gets a b everybody gets a binary an entitlement there are entitlements everywhere on the system so it's interesting but the design is not yet the the correct design for this what you need is a total re-engineer re-engineering of the system this is for example uh a sample of entitlement sample you have this entitlement called com. apple. rootless do install on this
binary this is the binary that I will attack to control to bypass uh system Integrity protection and write uh files on the f file system where I shouldn't be writing this binary is used on on updates because okay there's a there's a protection protecting your system uh but if you have an update you need to update files so you need something to that needs to update those files and in this case is this binary one of the binaries with this permission install so this binary can write anywhere to the system so if you control this binary you can do bypass the whole protections because you can write anywhere in the file in the file system so you have
these guys very surprised with with this you'll apologize me this most of this as I told you I only did this presentation at ccan in Singapore and so these pictures are all from csan and most are inside jokes but I like them I my idea was to change them but I like them so much thata okay I will not change them and I'll probably explain you the jokes so sip for example you cannot debug any more processes you have a system process you want to debug you cannot because it's protected because if you have if you could attach a debugger to a process you could modify because that's that's one of the purposes of a
debugger you can control it the memory of the process so you can modify the process and and control in this case I'm trying to create a process inside the debugger I want to run a new process and it doesn't it lets you cannot attach to process to system intergrative protection oh this one is running and this one is attaching to a process you want to debug a process that is already running you try to attach to the PID same thing cannot attach to the process and as I told you you cannot modify delete update protected files there's tons of system files that doesn't let you update even if you try there there were some bypasses they fix it for example you you
could mount a file file system and now write to the Mount point and bypass they fix that stuff and you have this utility that tells you the status of the protection in this case the system is enabled so it's magic this system the first time people were looking at it hey this is Magic how this works I cannot do anything with my system lots of people were complaining but as everything in in this in this area we can bypass it nothing is protected forever one easy bypass that surprised me I was not paying attention sometimes you are doing soft P don't pay don't pay attention so this is GDB my favorite debugger I don't like lldb because of
the syntax is weird but if you do GDB to for example a protected binary KX load is the binary that loads kernel extensions that allows you to run kernel code if you run kernel code everything is the game is over so I run the that biner inside the debugger I put a break point and you would expect that if I try to run the program I will get the same message cannot cannot run the program because system integrated protection is running but what you see the program is running uh if you see here I put on this address a58 and the debugger is running on breakpoints on the address so basically GDB can bypass sip you just need to run the process
under under GDB and that's it zp is gone so here I'm making fun of myself oops there goes system Integrity Protection One one small Tri trick you can attach to the processes if you try to GDB with a given process you can attach to to the process so it's a nice bug I had this bug for while I I was researching on this one and then there were some guys in New York I think it was New York presenting and I see this slide and they got the same thing and I see okay that zero day these guys just accidentally disclosed a zero day one of my zero days and okay I got I got sad uh I talked to
them and they knew more or less uh what was happening they didn't knew the the the the full implications of this bug but hey bugs Collision happens and it's very annoying uh what you can see here is the same thing uh I'm trying to touch file file AA on U on the system folder which is protected and uh system Integrity protection it's enabled so no no problems there same thing again the system show the the the binary data I use to exploit so same thing GDB breako on on that function uh okay I can run the program I'm okay I'm running codes you just write some some stupid some dumb shell codes that gets you a shell so here is
the one that that I use you write everything manually also I'm writing on the program counter I'm writing all the shell manually on on GDB so we keep running the process it will break this is the the Linker so it it gets some some internal stuff to to link uh and then I get a shell uh I touch the file you can see the file is created and you see the protection enabled so GTB is a zero day on this case or was a zero day against system Integrity protection so you can see this is my friend Jacob Tori talking about system Integrity protection he was was at the at the Pentagon and told me hey do you want a
picture there yes with the commas with the flying commas and he got me this nice picture so it's system Integrity protection so I was trolling if you know me I'm trolling all the time with GDB you can home can get the whole system it's yours uh of course you have to have a LP to root or RC because we are talking about root protections as I told you CP is about protecting the system from Roots so it it does doesn't matter uh if you don't have an LP okay people say yeah but you need root access yeah but that's what CP is protection so at the time I was trolling will GDB fall under what SAR control because it was a
zero day effectively GDB let's talk about some of the sep design weaknesses as I told you if you find a bug in a in one of the entitled binaries it's game over you can do the operation that binary is authorized to so what your target is binaries that allow you to to load the kernel extensions because you you want to run kernel code it's the best place to be even if apple has a document saying no don't go to the kernel uh if you find a way to inject for example a liary into that process it's game over because you are running arbitrary code in the same process if you find some linking bugs there were
some linking bugs stefaner presented at the same conference some some bugs there if you have linking bugs when the program is linking a library or something uh you get same arbitrary code execution so game over if you find some kernel bugs some zero days on the Kernel you can attack the protection on the Kernel because the protection is is running on the Kernel Microsoft is better than this in in Windows 10 because they are running stuff at the hypervisor level so they are one one layer lower which is even better if you are running code at the same level in in this case where the protection is it's just a matter of racing or finding where where the the
feature is implemented and Patch it and game over or you can find dumb developers which is fun so you have this program dock mode it's a sexy dock customization app don't use it it's not well coded so the guy was hey publicity free publicity no don't use it so what you have here we have a signed kernel extension uh um if you were here last year I was presenting about bypassing code signatures in in the kernel so every kernel extension in your Mac needs to be signed but the thing it it has a bug so you can use that that kernel extension to load any library that you want into any process that you want so game over I
can put arbitrary codes into any process your obstacles against doing this kind of stuff is basically $99 which is the cost of uh code certificate on on Apple it's just give them a [ __ ] excuse basically if you want to get a certificate from Apple the easiest way is tell them you are building a security product if you say I'm doing this and this and that very specific many people have a bad experience and they're they just reject so just tell them I'm building a security product and that's it I told Apple about this to my friends there okay this app is is getting used to by or can be used to bypass everything so
just revoke the certificate I told the guy because this I don't like this guy because he stole my code and didn't gave me credits and I told him okay just give credits my license is permissive if my code is public I don't care because it's public but the guy didn't even care because I put the kernel extension and I look at the code okay this is my code I know this code from somewhere uh but the guy told me oh this is not a problem I already have like a bunch of certificates that I ordered so he was already expecting Apple to see this or this is being used to do something nasty but the signature shouldn't be allowed
for that and so we cash he got a cash of certificates so you can see uh code signatures with just $99 it's not a big obstacle against people doing this kind of stuff so let's get some uh infrastructure in terms of Technology of Mac technology to understand uh how the bug how can you exploit the bug and what it's bug about so Mac is the core of the OSX kernel is the micro kernel where OSX is is built BSD if you know maos as a BSD layer people look at is as as uh Unix but the thing is the design is mac and then they put the BSD uh on top of that if you are into kernel
design and so on the Mac kernel the the pure Mac kernel has some problems the most famous is the the her that is being promised to be launched for like since like 20 years or something and it will never be ready what happens is everything is implemented as objects a task or a process or it can be the most similar arbit most similar um structure or logical structure for Linux it's the task you can you can say it's a process then you have th virtual M everything is an object inside inside the kernel the representation and this is one of the problems of the the Mac design everything is communicated via VIA messages so for example uh you have a
lot of overhead on on on the Kernel with the messages if you want to do an operation you need to send a message so this is creating overhead and this is one of the reasons for the performance problems of of uh of Mac of pure Mac of a p mark kernel you have here uh a design of uh a layer design of of maos of the kernel ofnow you can see the the kernel here you can see the firmware that that is here if I my my favorite one of my favorite places I didn't present here but this is a super interesting uh presentation and you have here Mac and then you have other layers on on on on
top implemented on top of Mac this is an easier design so you have the hardware you have mac I kit is the the system or is a C++ restricted C++ environment to develop drivers to make drivers development easy and then you have everything on top on top of of that stack so ma is is very interesting uh because you can send two types of of messages simple messages and complex messages we are going to use the complex ones to exploit uh these vulnerability the simple message is as the name says and they have a fixed this you always need this header because it contains some information for the Mac to communicate inside and then you add some
data in this case I want to transmit to integers data and data and data to so they are encapsulated in in in the message so there's no outof bound out of bonds data and and so on it's very simple it's basically a structure being passed between the kernel internally in the kernel or between the kernel and and user L complex messages are more interesting they have a fixed header then they have a descriptor account to say there's X data on following the message they are serial serialized and then you can put out ofline data and Port writes I will explain you port writes what what they are so this is a picture uh you have the fixed header
with some information and the remote port and local Port is more or less about TCP which is the target uh of the message and who we sending the message then you have the N the number of descriptors and then you have the information the data that is that the message will be sending so there are three interesting Mac ports in in your system as I told you these are objects the task which represents the process uh it's basically a container uh in in Mac terms it's it's a container that contains information about about the process not there's a onetoone mapping between a task and the BSD process but in theory you don't need to have uh this one toone mapping so a
task is basically a container for information then you have a thread a process can have one thread or many threads running so this is basically a bunch of objects and there is the host the host represents the machine so it's the most valuable Port if you have access to Ports you can write anywhere in the machine meaning kernel uh processes and and so on the Kernel itself is a is is a task in as a task Port because as I told you this is built on top of mac and the kernel what is represented as traditionally the kernel is another task it has a task Port meaning that if you get some process with this task Port if you
control this task Port you can control the kernel there was a vulnerability presented to year uh last year at ccan uh which is basically you could get the the the kernel port and then you can do you could do anything that that you wanted if you want to retrieve the task Port from another task meaning for example a debugger a debugger needs to control the process uh to control some process meaning that the debugger is implemented in in Mac OS as a task it gets the task Port of that task and then you can control oops I can cannot leave uh so if you have that task Port of any task you can do whatever you want to the task
because you control it you have the object authorization on on that Port under normal circum circumstances you what you get is an authorization request meaning okay you have this process that wants to write to that process it wasn't like this on older Mac versions it just the process just needed to be on a special group but now you need to authorize the process one thing you need to be aware is that you just need for example if you are doing a debugging session and you authorize the debugger you don't need to Riz the debugger anymore or at least until you reboot your computer meaning for example if there's a malware what a malware could do
is get into your system and try to run programs that might have this authorization so if you are a developer you might want to reboot your machine once in a while because if you are D debuging there's a process that has authorization to control other processes of course you are not if you are not running the the process the debugger as root it only has authorization to to to attack processes that are running as your user but even that is very powerful you can do a lot of nasty stuff with that so be careful with this take take this in mind if you are debugging on micos one interesting detail is that a task doesn't need any privileges to get
its own port so a task can say give me my own port that's that's okay okay operation there is a function for this Mac task self which B basically you say give me my my own port give me a right an authorization to talk to my own port this is interesting because as I told you in complex messages you can pass Port writs between between applications or or in a message so you can say my application get my my own port and now give my ports to some other application and now that application that receives the port can control uh my own application so this is very interesting uh as you can see you can pass portraits you can also uh this
is something like file descriptors that you can pass in in normal Unix IPC so it's a very powerful design and very interesting to to to exploit as I told you you can pass the the port to to other applications normally what what applications do is task for p which is uh the the argument is a PID for the process that you want to control and you want to the system give me the the task object for that process this is what launches that request and you say Okay I want to authorize this process to control and and so on so this doesn't happen in normal situations you don't have applications giving task ports to others
because that would be a security a security problem you could do some tricks if you are creative enough you can do some tricks with passing ports but you can some something that you you see in some Linux smallware which is basically creating a parent process and a child process and they talk to each other you see also these on Windows is a way to to attack reverse engineering because you have to to to block on on both processes the problem is that the parent is debugging the child so if you try to attach a debugger you can't because there's already the parent process uh controlling the debugger you can work around this and so on but basically it's
more work if you are trying to reverse enger the the malware one trick for example you can put one process controlling the other you put you create for example an exception a divide by zero the the parent process will get that that because it's debugging the the process and then you now run codes uh there for examp this is what you do for example on Windows on struct structured exception handlers you put an Handler and then you trigger an exception and then the code runs there so if you are not aware or the first time when this was used I don't know 10 15 years ago it would fool the reverse Engineers because they would they wouldn't see where the
codes would be executing because the the debugger would say Okay I I see an exception I I stop at the exception and then the other code would not be run because the code was inside the the exception andler of the of the process so we would miscode or the process would crash and so on so this is a very nice trick to to anti-reverse engineering so let me explain you how to send Mac messages your uh you have the messages the format now how can we send messages between the processes we need to define the the format of the messages uh you need to to Define two two structures one is the one to send we sending the message sends in
a format and there's another body another message format for the one that receives that can receive further information you can add for example trailer that tells you some some things about the message usually you don't need you don't need to add that stuff so you re register a server you need to do some some games with ports and basically what you are saying is you will locate a port on the application and you give it rights because uh Mac has Port rights basic basically which which are uh I have a right to send a message I have a right to receive a message so you need to authorize processes to receive or send messages else it if you send if you could send
arbitrary messages to processes there will be no no security and then you do this bootstrap register which is basically saying registering with with a server there's a server the process one on on Mac is launchd which is a server you tell okay tell everyone that is interested that I'm listening for messages I'm D services come.put do macra uh my famous name uh uh and then you register and you say I'm a server I'm listening if anyone look ups for this service I'm the server for for this Services I forgot to put a joke damn uh so basically you Loop and you are a server you Loop and you are waiting for for for messages uh you have
to set some options saying that you are a server I'm a server and I'm waiting for messages and then one important thing is that mac message blocks so it's waiting messages if no messages uh arrive it's simply block waiting waiting for for them so you basically put a a server Loop in infinite Loop uh you set the options in this case you you say you are receiving messages you are a server Mark receive message the options and the large is saying you are expecting large messages you start the server and then you are just waiting for for a message when a message arrives uh the code continues until then it's blocked the client you have to talk to launchd
which controls the ports knows where the servers are you allocate once again a port to receive messages you want to say I'm a client I want to receive messages so here you are looking up the server the other server you locate the message and then you continue you prepare the message uh you say sets a bunch of options we are sending these are the ports the server Port that we look up here uh here so this is locating the the server so I'm telling where is the server and then if the function worked I got the server you set a bunch of things and the trick is here we are putting the data as I told you Ma T self which is
basically the client the client is is getting the port itself putting the port on a message and is going to send the message to to to the server so basically I'm transmitting a port right over a mac message and finally you send the the message once again with mac message this is on the clients mac message is the function that you normally use for this you send the message and now we are waiting for for for a server you can you can put the server saying okay I received the message and send another message confirming that that you receive the message this is good because it allows you to sync the client and the server you already know okay the the the
server finally has the port rights tell the client and the client knows okay the server received everything everything is okay I can do whatever I want now as I told you the server will receive the message if everything went okay Ma is pretty is pretty reliable sometimes slow but pretty reliable extracts the port right receives the message says I have this message there is a port right I extract and now you can control the other process process in this case the client process as I told you it can it can send you a reply okay I'm ready everything went okay I can we can now start talking so this is basically sending uh a message uh the message is empty
there's nothing no content it's basically it's just a sync message I'm just saying okay I Reed everything is okay there's no interest in this case in in sending in sending the data so when I was looking at this my original goal was to exploit the SD binaries I wasn't looking at sip itself this was at the time there was a vulnerability rootless that could exploit uh binaries so ID binaries and and do whatever they want because they add root access and as I told you the same technique will also work for entitled binaries because the vulnerability allows you to execute remote code on on on on the target binary let let's go to the next step for
those of you that don't know what is ISAC fee this is the part where it's very easy to spot to spot the vulnerability so this you have a bunch of exact functions ISL Isle e bunch of ISAC V ISAC V that allow you to start to start a process this is the flow on Mac this is one of the reasons why AFL is slow fuzzing on micos because there's a lot of casses there's a lot of stuff happening so it's slower starting more processes and for fuzzing you want to cut all the overhead so you start a process it goes a bunch of things this is the core image that detect the core function that
detects what kind of thing you want to execute because you can execute a script or a binary to main things it then reads the file if it's a binary a Macco binary then it will load the file and then there is this function that will test if the binary is a SD and do some operations on that binary this is a a code snippet from the from the kernel source you can see here the code that loads the Mac the the file it's a binary file and it will parse the file and load the file into memory and then continue the to start the the process this is basically telling you the the two main functions load Mac file is the
function that loads the binary and puts in memory most of the there's another function inside load ma file which is Parm file which is the function that does the Dirty Work of parsing and understanding which commands which data is inside uh the binary remember if you control the task part of an of an application you control the whole process because the task is the the the most powerful abstraction on on the process there was an obvious bug patched in Panter pter I think it's 10.0 10.1 or something or 10.0 or no 10.1 or 10.2 yes the bug was patched in 10.3 so if you have a su process what they do is they have to
reset the task Port because what we could do how could you attack this you would put a SD bin inside the debugger start debugging the process and because the debugger controls the the the the task Port you get the SV privileges so you can change the code in the task that that you control and you are still running with with suid privileges without this you can do that what they need to do is when you start a suid process one of the things they need to do is to reset the task Port if there was a process controlling the task port then you don't get control anymore because the task was reset so the debugger lost the right uh to that
Port so this is more recent code that they do some operations now they reset the task port and they also reset the threads because the threads also have um rights so if you had you can have rights on the task and the threats independently they are independent ports or independent abstractions in terms of Port rights so if you control a thread and you didn't reset the thread you could still attack the thread and not the task which is the same thing as long the thread runs some code you can do whatever you want on that space so hopefully the you understood that it's not very complicated the Kel is respon the kernel is responsible to
loads and map any executable to that you want to to run and it will try try to to guarantee the Integrity of a new process in this case in the in the case of suid processes because the suid processes are the most powerful or were the most powerful uh Pro binaries that you have in a system because they allow you a normal user to execute as as as root in this case once again it tries to protect the binary so let's go into what was a zero day so this is the function to execute the binary just part of it the binary is loaded it's passed then this function the one that resets the ports to assure the security of the
binary it's here and then here the the two ones that that I show you the problem and it's very easy to to look to to find the bug there is a race condition between here when the file is being loaded into memory and when the port is being reset because there if there's a race condition there's a timing here where the file is already in memory but the port is still not reset so if you have some if you give the port to some other application in this case the server and this is the reason why the client server model that I presented you you that server can do something here in this space in this time space and if you can
do something here basically you put a Shell Code that gives you a shell in this space when the program when the kernel arrives here the binary that was loaded already has different code in memory but it doesn't care because it didn't detect this race condition and when you arrive here you already got root codes running into the process this is a more complex version because now you have the MAF uh framework trying to check trying there's the hook on MAF sending to mfi which is one of the processes that attack that protects your iOS phone uh from jailbreaks this is one of the most attacked processes so it tries to check do some verifications but
the race is still here on this space it even improves the race because there's code more code running on this PA so you have more time to win to win this race uh which is very beautiful it's a very beautiful logical uh vulnerability so the ports are only reset after the code is mapped so this is the problem you need to First reset the PS and then you need to map um map the process so this is the reason why I told you the about sending Port rights between a client and a server so so for example you have a binary you pass the port to to some to a server and now you can use the the e
exac v function to execute some other binary still in the same process but since the server is controlling the task Port you can write some code so if you if you if you put if you exact for Sid binary the server can do something uh to the mapping of that binary and it can run code uh with with root privileges so if we win this race we can write anything into the new process so this means game over uh to any protection that that depends on on on the binary so the trick is how to get the task Port of another task right now you already know you just put a server in the client and you transmit
the ports between them I told you task for p uh puts that that uh that box maybe that works fishing still works and there are some users that would put the the password without any problem there but we want to be sophisticated so we we want to work around this we don't want that promp so what we put it we have a client that says okay take my port Port server receives the port then we exact the binary that we want to attack on the client and the server starts when the server syncs with the client this is the reason why you have to sync the client and the server because if you start executing this
before the server receives the message you will lose the race it will be very difficult to sync the race but sending the message when the client says okay I receiv received the message the server is finally in sync so I will I can start executing and the server will basically try to root Force try to to to to win the race so let's put everything together uh how to hack this this is the whiskey con at ccan basically you have to drink two shots of whiskey for talking five minutes I used to have the record of of this there's a very very uh bad video of me very getting very drunk talking about hacking team because of this I was
supposed to talk five minutes and I think I did six shots so I talk like 15 minutes it didn't went very well it's very dangerous don't do it so how to exploit this I already told you all the tricks you have the client oops you have the client that gets its own port sends via a mac message to to the server the server acknowledg acknowledges that it has received the message the client is waiting for for receiving the message as soon it receives the message it executes the target binary that you want to to exploit and the server is already in a loop in an infinite Loop trying to write to the process trying to in this case
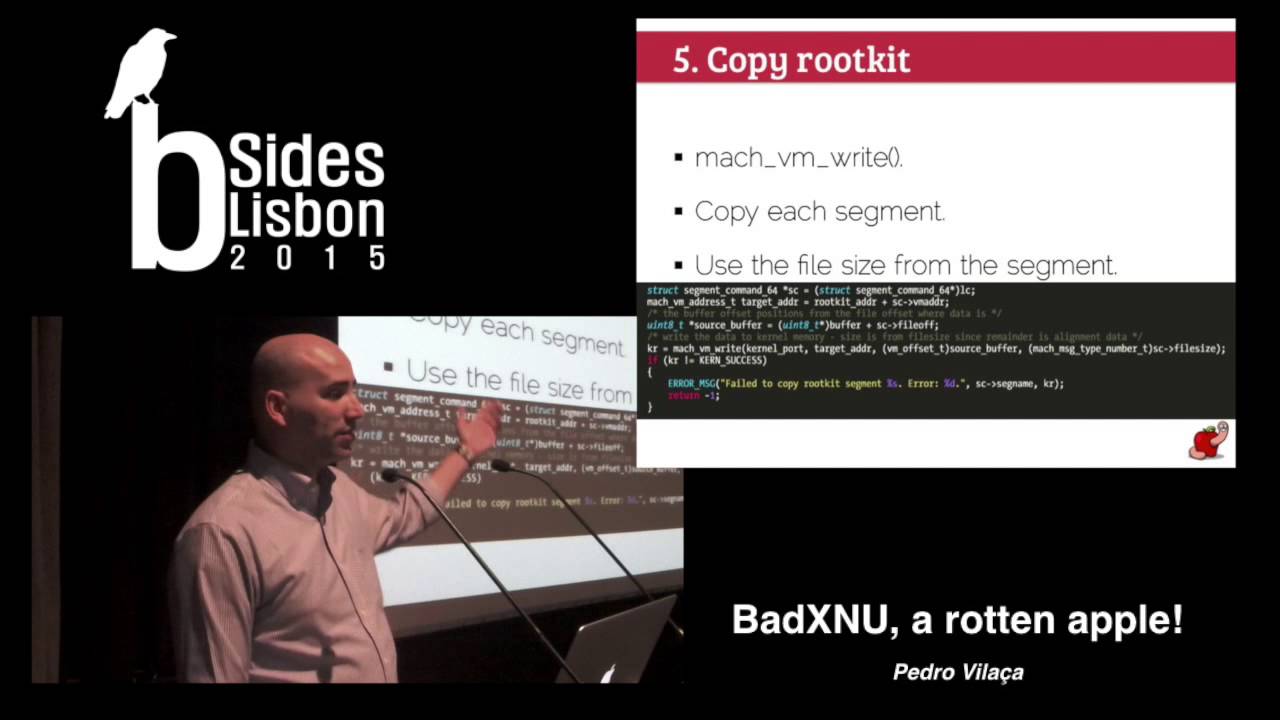
some Shell Code that gives you a bash prompt you could write anything that that you want you want to keep as as short as possible so to improve your uh your chances of winning the the race Shell Code to execute the shell is very small so the trick for for writing to another process is that function Mac VM writes which the first argument is a task Port so it tells you I want to write to whatever task uh I have rights to it's [Music] okay okay so the SD task is already marked when we are writing this the process is mapped so we are changing the the the memory of the target process and if we win the race we got a root shell
on the target process so we can write anything to the new process we need to to to find the memory usually the entry point is the the easiest way because you know in theory it's going to be the first code to be executed you can have some C++ Constructors which is one trick of running code before but okay let's assume attack the entry point and if we win this race we our code will be executed game over we took control of the binary but there's another obstacle before final Victory aslr if you run this against a non aslr binary you always know where the binary is going to start executing so you just start code an address and say modify the
entry point and that's it gu 32 bits binaries it's also deadly because the entropy the SLR entropy on that is very small so you just put force that stuff and that's it and if you know SL SLR in theory we don't know where the binary is in memory because it's randomized on on each starts I'm not an exploiter and sometimes you don't see the problem and I I talked to a friend uh Trio and he told me he was already testing some data about aslr the distribution of aslr in theory should be random but it told me okay just brute force with a selected value it's one of the tricks funny enough zero there's there are sometimes the the function
that that gets that generates the SLR slide gets you zero okay it's one value which one possible for me I would probably take the zero out of there lose one bit of of entropy there and but it's okay if you try with zero and if you run the program thousands of times there will be a probability I can I don't know the probability but there will be a probability that you will hit zero and if you get zero and you won the race then it's game over so this means that if you TR if you do this the exploit will be super noisy you'll get a spike on CPUs 100% of CPU because you are EX think thousands of
times I I had I tested sometimes I would get like three or four executions I would get lucky and get root shell the the normal thing was like 10 to 20K uh executions which is a lot if you are trying to be silent in terms of exploiting a a Target so this was at the time or at this point it was a great vulnerability but the execution wasn't perfect H I wanted to improve uh this as B Nagi is saying here is not impressed can you do better of course we can that's why we are here so we need a known address uh zero uh is is a known address but or aslr zero gives you a nonn address but it's
not good we have the Linker uh deil which is also under aslr and a different offset so we have two two addresses that that we could attack but we don't know where they are because they SLR but there's a small interesting detail you have a a library cache to improve the the speed of your machine and there's a library cache that is on memory and the small detail is that it is randomized as I told you here aslr is under uh dld is under aslr but it's randomized on each reboot so every time you reboot your computer the the the cach is randomized so another good reason to reboot your machine frequently is this one reboot so
you have randomized on the cash because if you don't put an attacker might get lucky get that and then it's game over so assuming your machine uh assuming we have we can find the the the SLR because it's the same address for every process because it's a cache so if you start the process the the the cash will be at the same address and because this this cash is is a copy on right it's not dirty cow but it's it's funny now there's a cow there uh we just need to modify a function on on that cache and we are not attacking every other binary meaning because it's a cache it's shared between other processes but it uses the copy on wres
technique so if we write uh on our Target that we are attacking we are not attacking other processes so this guarantees the stability of the system we can safely write to the cache without attacking other processes because if this wasn't uh with this technique if we modified some memory we would affect every other processes so this is interesting to for this exploitation uh in this case uh for example this is the starting point of uh PS the binary PS it calls very very early this function which is a library function Li a lipy function uh and I will show you why what we can do we can because the the the library the the Library address
is the same for every process the server when it starts says locates the address of that function we can we can do this easily because we can locate where the cache is we locate the cache we know where the function is and we know that function is the same address for every process that that is there so we need to do this once the server finds the address and we now we have a fixed address where we know we can write to safely so this improves our chances because we already know one one value we just need one to five attempts maximum because we are just now trying to win the race we we are not locating trying
to locate an address the address is already known so we are just try to to wining the race and as I told you there's a lot of overhead on that function so we can easily win the race one to five attempts maximum is quite an improvement from 10 to 20K executions so this is a very interesting exploit because it's 100% reliable works all the time um maybe more or less executions but it will always work it's super safe because it doesn't affect any other processes so it will not crash anything at the time every single OSX version was vulnerable to this bug uh so the bug has been there since 10.3 so that makes like 10 years or more you can
abuse any SD binary because I can control any process and as I told you you have the more also powerful entitled binaries you can also abuse uh these binaries I found this vulnerability in early 2015 I was working on that rootless and I was looking at the code and it's like one of those magic moments you look at things like bam this looks obvious it was I was working on that function like many times because uh I do work on on that area for for the product and I didn't notice then on that moment I noticed oh there's the race Condition it's very easy it's super easy ianb found the same bug in late 2015 I hate
Ian beer because of this no he's a good guy but he made a collision because at the time I was trolling with apple uh ELC Capitan was released in September I think and I found this like in April or March and I was trolling on Twitter Apple I'm going to show this on the first day of el capan release I'm going to release and show that your system is broken but I have a very good friend at Apple that asked me very pretty please don't do that because if you know I also released the zero Day in 2015 uh E5 firmware it was an accident but it created a lot of confusion and he pretty please ask don't do that again
because don't don't create more problems to me and H it's not a problem to to to do this so I didn't release and then Ian beer puts put a very interesting blog post where he describes this uh he exploits the vulnerability in a different way it's the same bug uh same same vulnerability same way it just exploits in a different way instead of attacking the cash he attacks other properties so we should look at this at this bug which if you want to further understand this yeah be being a great exploiter continue to keep working on on these issues I'm already finishing he keep working on this and there was uh still more problems with
the with the task structure and he found tons of interesting bugs he posted like two weeks ago or something this very interesting blog post you should if you are interested in into ma stuff go read because it dives into into the more into the internals of of the task structure of of the kernel and we found a lot more vulnerabilities on on this I also posted a very I wanted to talk but since I have no time about this about little snitch which is a firewall for Macos you probably are using so I started looking at it and I found another logical vulnerability on on little snitch the program is is very is very good but it had some logic
vulnerability there's a very long post describing and how to reverse drivers and so on go to my blog and you can you can see you can see that stuff and it's super interesting let me show you quickly a
demo so this is a vulnerable VM here uh ID uh normal user so here I'm running the server you don't need to have two processes you can have the same process that forks and that creates another another server uh I just put this in into into separate processes to make it easier to understand the code so what I'm doing here I'm launching the server I'm attacking the PS command because it's a SD banner and I'm attacking that function that I show you because it executes very early and I want to to try to R the race as early as possible so now what is doing it's finding the symbol this compat mode in the cache it
says that the symbol is at this address so this is the fixed the fixed address registers with the with the launch D so now the server is waiting and also detects where the the entry point of the target is so I know where the binary the target binary will be without aslr and now I just put here uh race I'm trying to execute the client uh uh 10,000 1 million times just a big number but it will not be needed so I execute and it start talking to the server the server is sending the port is executing the command I just W the race so ID I'm root so exploited now let me show you attacking
bypassing sip so this is basically a local priv privilege excal I'm excal a normal user to root now that's by bypass sip or server okay this is the server the server I'm attacking that utility that I told you system sh there's another function system function get U ID very early in the binary to guarantee that I win the race uh let me okay so I'm trying I'm trying to write a file to system which is protected operation not permitted uh so let's run the client once again uh uh this is not going to run because there's a server hold on I didn't run the
server I have to kill a server because that server is using the same name so uh I didn't code it to clean up but okay server okay the server is running again test process so it's trying to exploit once again same method same same exploit okay it's
here B sites and that's it as you can see I just by bestp I can write uh to the protection [Music] CSR so the system still detect integ system Integrity protection is still enabled but I can bypass and this shell until I leave this shell I can do whatever I want to to the system so let's finish this uh so this was cute but last as I told you I like the kernel can I load and signed kernel code of course I can uh in this case I'm attacking uh I'm using GDB to bypass this I attack the binary it will tell you okay the this the the extension that I want to to load doesn't have a uh as an
invalid signature in this case it it's not signed and of course I can use this because what I do I patch the binary I patch the protections and I can load and signed codes so meow be here was very happy success let me just go very quick over this you can use the same vulnerabilities because this is the program that loads the the Kel extensions you do the same trick you attack the program you patch some shs that are there for code signature and then that's it you you win that you can load any binary you want to the kernel and then you do whatever you want to the kernel let me bypass this else they will kill me with time and you
can see this uh ah let me use this let me troll a bit this was a vulnerability in in Linux because there was a kernel kernel code signatures in the kernel kernel processing x509 basically and this was my point last year and I still believe on this point you cannot load codes into ring zero also known as the kernel usually when you are checking this that same code on user land because if you control the process you can do whatever and then you just load to the kernel so this doesn't make any sense for me you need to check the code at the kernel and that thing from x509 was there because if we are not if we are unable to do this if
you unable to build a secure code f509 code signing feature in the kernels I have no idea what we are doing in this industry we we should be able to do this create some reasonably secure code on the Kernel that can guarantee that the code signatry is okay in the right in the right place so at the time Thomas Lim Mr Thomas Lim was asking if I can AP this stuff so how do you AP this stuff you bypass sip in this or other vulnerability you install AP on the protected folder you enable sip again and then the user cannot delete the the the AP he needs to reboot the machine and do a bunch of steps so it's a very
nice sip protection racket sip will protect your malware from from the user and from AVS and so on so it's quite interesting in this case the user needs to to to intervene he needs to boot the machine in recovery mode open the common line you don't see most users doing this so get the [ __ ] out you can have the special special Apple entitled shell or application for me this will be the way if you go to the Apple Genius they will put something like this and and fix it maybe the FBI would be interested into this because they would be able to do anything you can use the AVS to bypass or disable
uh sip josa was like here last year or to or on the first edition and he was attacking aies he has tons of interesting work a there's I think it's D Vel that made this quote AV tends to be a different kind of root kit because they have tons of vulnerabilities and they run on the Kernel so good Target conclusions H so this is why the slide get the [ __ ] off the stage because I'm already going overtime see doesn't fail it's designing I hope I conf okay this is ATT attacking Apple but at the same time protecting Apple because I'm doing the same thing I'm trying to design Protection Systems designing security systems is very difficult most of the
time I'm breaking my own systems uh all the time so which which is good as long I can I can break my own system means I'm still under control when I when I finish and I say I I don't know more maybe someone knows so this is very difficult it's a very difficult task if you want to say to to test it move to defense side I have been on the offense side I have been now I am now on the defense side and I see many people on the offense offensive side saying ah we have bugs it's easy and then just move to defense and and I want to put your money where your mouse is and try
and try to defend and try to create code without bugs it's not that difficult it's not very easy and then you have customers saying oh I want an exception and so on and the exceptions are are the problem as I told you secrecy doesn't buy you much okay you might have proprietary information that you don't want but for example the design the where they implemented is was on top of macf so it's known technology so they should and most companies should publish information or at least invite researchers for a private thing okay hey we have this new feature do you want to take a look I will give you a paper okay sign an da or something and
you start to understand you can help uh companies uh on this process release a white paper so we researchers can can understand you hopefully I convinced you that logic and race vulnerabilities are great vulnerabilities or the best vulnerabilities because everyone is after memory corruption Dan was showing you that machines are going to kill your memory corruption bugs sooner or later hopefully these bugs can live for many many many many years uh this one was like 10 or or 20 years there are more bugs like this logic logic bugs are really nice bugs and people are still not attacking them everyone is chasing memory corruption and so on and the logic bugs are there they imply more
work they imply you to understand the system but when you find them they are really great and bugs to to have patches are out for L Capitan for 10 11.4 is already patched iOS is also patched there are no patches for all other versions so if you are running those versions you are vulnerable to this kind of stuff and you saw it works so it's great vulnerabilities I posted the code and so you can use it for pentests or something if you have a shop with a running Gold Max you can use it at the time I I didn't know why basically it needs some re-engineering on on the Kernel so Apple doesn't support the older versions they didn't
want to reverse engineer and so I after the latest tnb bugs Sierra the latest version is the only safe OSX version to to use so never forget Dave you can have firewalls encryption antivirus but you always have Dave the human error on your corner and that's the weakest element and this is why we are not going to have these race these arms race against bugs we are not going to win it in in a in a in a time period uh great to besid steam thank you for doing this and a few other friends if you need to contact me you know where the blog is feel free uh email me and so on I will try to help
you and and as much as I can so that's it not bad five minutes