Elicitation Weaponization of SE for Covert Access Operations
Show transcript [en]
Let's move on to the next talk with who's going to be speaking about uh social engineering. So, welcome. Thank you. >> Just before I start, I wanted to say that I left some uh goodies on the the floor. There's a back door and bridges, card game, uh stickies, uh some reading material. So, welcome everyone to my uh talk. I'm going to talk about social engineering uh but more precisely about weaponization of social engineering for physical pentesting and you can if you want then you can follow me on LinkedIn. Uh I also have a a podcast on Twitch which I also share on YouTube so if you're interested in that you can go ahead and like uh figure like yeah check
it out. And like more about me, I'm a penetration tester and social engineer at Black Hills Information Security. I'm also called the woman uh in red. I'm not wearing red today because it was raining a lot, but so uh but uh yeah, you can believe me. That's like me on the picture. And uh so I already mentioned that I have that podcast. Uh I'm also certified as coffer access specialist, physical auditor, and elicitation specialist. And I I received a woman of hope award uh from Celsius in 2023 in Paris for my activity on link in because I'm trying to uh inspire people especially women to enter cyber security and like sharing that it's possible if
you want to change your life if you're interested in something like this just go ahead send your CV start learning and yeah everything is possible if you just apply yourself because I before was a government official and I I'm completely in a different like uh yeah barrel per to say with my like skills right now. So every you can if you just want to learn something it's al it's possible and so yeah I I was terrified of heights before and I believe that if you have like big fear of something it's limit it's a limiting thing in your life so I didn't want to be afraid of heights I don't want to be afraid of anything uh
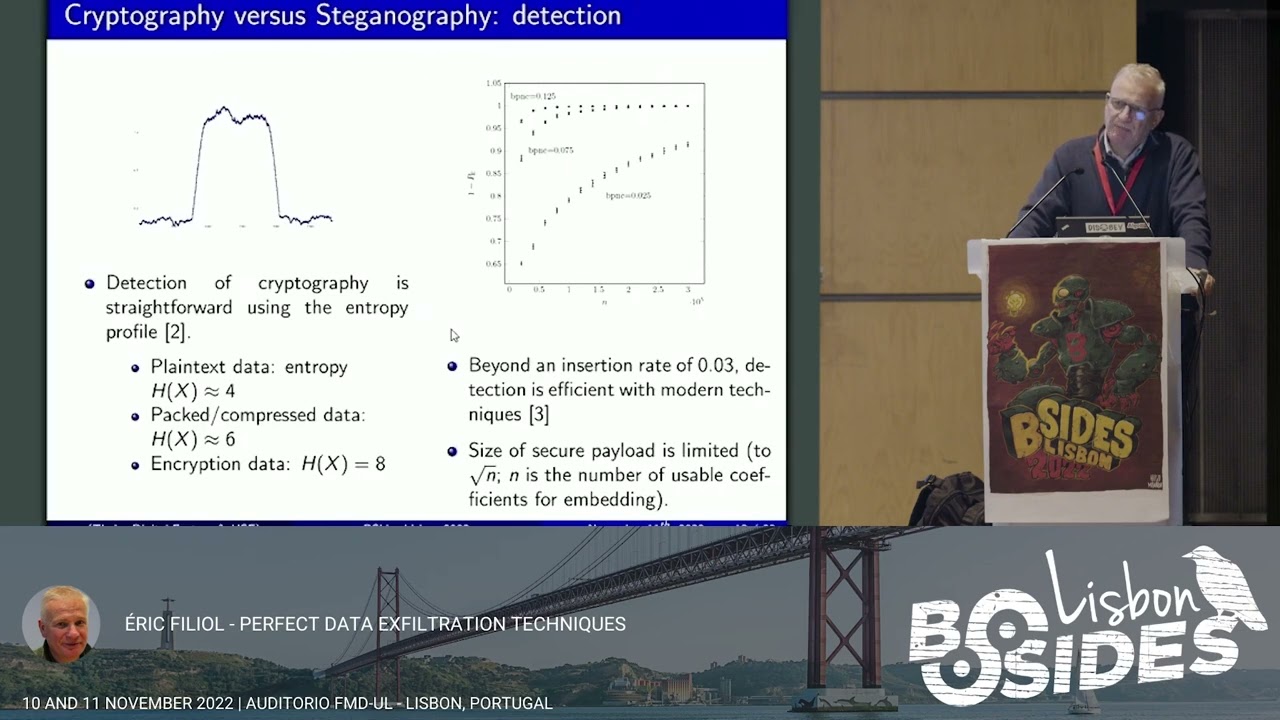
to be honest but sometimes it's like a bit of fear is healthy but uh I jumped out of the plane with a parachute to conquer my fear. I was scared [ __ ] less. But now I'm less scared. So, uh I guess it's worked and I love cycling. But let's go and talk about uh social engineering for a moment. Here's the agenda. Yeah, look what you can expect. But I will just uh I have a lot of slides so I maybe will be flying through some of them but uh just bear with me. I'm trying to share as much knowledge as I can because it's my like obsession interest. Uh so yeah I really care so
someone learns something new today and uh a disclaimer for this is yeah please use it all of the knowledge in an ethical way uh and business ethical purpose only uh don't try to uh yeah plan the highest and low or something like that just yeah be ethical and uh yeah and so what is the purpose of physical p testing uh physical penetration testing is a it's something it's like engagement that simulates a real world threat scenario where a malicious actor attempts to compromise a business physical barriers to gain access to infrastructure building building systems and employees exposing weaknesses and vulnerabilities in physical controls such as logs barriers cameras or sensors so that flaws can be
quickly addressed. So the point of uh doing the physical pentesting engagement is to find all the holes which doors are valu vulnerable where like a problem uh moments uh in the building and addressing them like writing the report and so the client could address uh afterwards and uh but a very important document before I start talking about anything is the get out of the jail free card. So you need a document from your employer that will uh detail why are you here that you're on an engagement that you're auditor uh contact numbers to co or like someone that hired you preferably two or three phone numbers and uh inform the person that like gave you the phone number to you before you
go on an engagement so in case there's like some problems happening uh they call the police on you you're like in big trouble. So they someone can call them and like conf like yeah make sure that you're like the real deal and not like someone uh a malicious and yeah uh so yeah just uh and what I uh wanted to add as well so uh put a letter folded and uh would be best if you not put it like behind somewhere here but like in your back pocket. So if you have to have your hands raised in the air then you can tell them oh please like can you grab uh my document here uh because if
you do sudden movements that's like that's a problematic so things so yeah be be aware of that before you go anywhere and so I wanted to uh uh ask how many of you watched the matrix the first part and do you remember the scene with the woman in the red So uh that's for me that's a perfect example. I used to have it in the presentation where like the scene is displayed with sound but everyone watched it so I thought yeah I by just explaining what I mean for me that's a perfect example of uh the art of destruction. So she's dressed in a totally different way than the rest of the people surrounding her. And so she's
gathering all of the uh yeah uh uh all the attention. Yeah. Uh thank you all the eyes are on her. So that's uh what I wanted to start with and teleport you all into a bank lobby. And so you enter the bank lobby. Usually there is a place where you drink coffee or for free you can like take a cup of coffee and so you go in take the coffee start drinking it casually and you look around. So where's the camera placed? What is the security guard doing? How the entrance gate looks like? What is happening? like you're like checking uh around the surroundings casually and you're drinking that coffee and then after a while and as you can
see in the lobby everyone is dressed uh business casual so black white beige gray colors you know like very taunt and then your friend comes in and she's wearing a red dress and so everyone is looking at her like oh that's a beautiful lady she's wearing a nice dress so what is happening because no one is dressed in red really uh uh or eyes on her already, but then she drops a pile of documents in the middle of the corridor and starts to pick them up uh pretty chaotically. So uh people rush to her and try to help her. But then uh that's like a perfect moment because you already were assessing what is the situation that the security guard
is not really watching the monitors. So it's a perfect moment to jump the turn style because uh our eyes are on your friend. So it's a good uh like example that if you go on an engagement like that, it's a good idea to bring a friend with you. It can be someone uh like a burner person. So uh that person makes a commotion, creates chaos and then that person is burned. So you can have to leave the building but you are in. So it's a good idea to bring a friend and uh social engineering. What's that? So that's the art of and science of manipulating human psychology uh to extract information influence decision and provoke actions. So uh before I
follow uh I wanted to say that usually when you probably hear social engineering first thing you think it's fishing or like an email that you should be worried about or like uh training from HR that you received. But my whole presentation is about physical pentesting in and manipulating people and to extract information through uh yeah like mind game social engineering that say like dark psychology of social engineering not sending uh emails to someone with link. So uh and to give you an example uh imagine you like you hear a phone call uh like a two people talking with each other. So uh there's here it goes the example. Hi this is Michael from IT. We detected unusual
activity on your account. Uh need to verify your login credentials so we can secure it. Can you confirm your usern username and password? So the voice on the other uh end was calm, confident and friendly. The exact tone you'd expect from a helpful colleague in a crisis. There was no reason to doubt that person. You already felt like you trust trust him. The employee complied thinking uh they were preventing a hack, but they were wrong. They were the hack. So what I wanted to give you an example of is the real bridge uh often takes place between the victim's ears. So what the person uh believes in uh how uh easily that person trust the other person uh the character
traits even like the trauma that that person went through all all of that is a button you can uh press and elicit information from them. But uh yeah uh but here also I wanted uh go back to being ethical because uh to give you an example if you see someone that is a very easy target uh for example you see uh a surgeon in front of the operation room and he's like totally devastated he looks like a easy target right very vulnerable in a very easy to manipulate uh state but uh please don't uh you like be ethical be like a kind human and don't follow the the easiest path because that person might be
on the edge and you don't want to push anyone over the edge, right? So, just wanted to make sure that everyone understands to this is might be easy to uh divulge information from someone but not always advisable and like you be be a kind person. So real world examples for example uh cult who are human intelligence uh from United States uh used uh uh elicitation charm and stage encounters in bars, cafes, cultural clubs to recruit insiders or extract security details. So the lessons from this is long-term relationship building and trust are more effective that uh technology and Frank a big nail I'm sure you all watched the movie catch me if you can't. So uh he
convinced people he was a pilot, doctor, lawyer without formal credentials because he was very charismatic, charming, he was also good-looking. So that also helps if you like because it's the halo effect. If we trust more people that are attractive so uh the lesson here is authority symbols, clothing jargon, confidence or powerful trust shortcuts. And Kevin M Kevin Mitnik, I'm sure you all know he's uh social engineering pioneer uh manipulated uh employees to reveal passwords, codes and access numbers. Preferred talking to people over hacking machines because uh we all know a human is the weak link and it's easier to extract information from a human being. So the lesson here uh phone based elicitation vision bypasses
technical defense uh if employees aren't trained to resist. So uh there are four phases of social engineering and first one is reconnaissance. So what we do during reconnaissance we are gathering information. So uh we will find it we already know who the target is probably if we are on an engagement. So we find all the personal information, organizational structural online behavior, uh potential vulnerable, we're looking for vulnerabilities pretty much on that phase. So we know uh how to plan the next phases and how to perform the attack and uh so what is the important part here? We have to understand the environment of the target. We have to identify potential entry points and yeah we are planning the
approach for the attack. So example here is an attacker might scan social media profiles on or LinkedIn to learn on the target's job row uh interest connections and email addresses and then craft more personalized attacks. And so uh protexting and personas is what is pretexting? So it's crafting a believable identity and you have to so uh yeah it's a fabricated scenario uh believable identity of who you are. So this is very important. So you have to practice before have answers uh ready to go if someone asks you who you are, why you're here, what's your name, uh what's your credentials, who sent you, you have to be ready to talk on the fly. And sometimes it's important like uh to have
two disguises. Maybe one day you come in with like a blonde wig wearing like baggy clothes and uh like acting very relaxed as a I don't know a student or something like that. And the next day you're very dressed very professionally. You're the IT uh I don't know uh person that will go into the server to check something for example. So you can prepare to disguises and uh make sure the uh the identity the pretext is like makes sense in the situation. So if you go goal is to go into the server room and plant a flag there on an engagement. So address business casual dress in a way that makes sense for the situation because if
you dress as a UPS delivery person and you're found in the server room that doesn't make sense, right? So uh you have to adjust your uh persona to uh make it more believable because sometimes if you like your clothes uh have like authority behind them that's already like something that people will not question you. So uh think about all of those things before you enter the building. Uh the next phase is uh engagement. So that's actually uh you're establishing communication with the target. So uh maybe you're sending an email, maybe you're creating a situation where the target is willingly providing information or access uh so uh or maybe like sending an email but also vision is
possible. you can uh call call help desk or I don't know uh IT department or uh HR and the purpose here is building trust rapport or set of agency to uh to make the target more susceptible to manipulation in the next stage. An example of engagement is the attacker might send a fishing email to that appears to come from a trusted colleagues or well-known company uh to uh the email uh could ask the target to clinical link download attachment provide credentials under the guise of legitimate request. So if we are doing the reconnaissance and we are doing the research about the target, it's a good idea to also research their uh clients and like the companies they work very
closely with. So we can maybe use uh one of the templates from the company that is trusted as a template for email. So uh yeah, that's a good idea I think. And uh I wanted to talk about building rapport. So what is that? Uh rapport is a mutual trust that makes communication possible or easy. A friendly harmonious relationship. So you can play on the targets interest and emphasize their uh their own personality trait. Uh use oint uh to learn the targets likes and dislikes. And I have an example here with the hobby hotel lobby here. A friend of mine on his engagement uh he had a lot of time obviously. So he spent uh like two or three weeks sitting in
the bank lobby and he was building rapport in that way with the security guard. So after those three weeks he was just working on his laptop acting very like casually like he's just working in this building or something like that. So after three weeks the security guard didn't really uh think of him as a threat anymore. So he started approaching the security guard more and more asking him questions like making friendly uh conversations with the security guard and that's like how he built the rapport with him uh without even like uh coming to him on the first day and like uh starting to uh to talk but uh by just spending more time in the area of the security guard.
So he had like him on like he was looking at him and uh elicitation uh something I wanted to uh focus a bit more on my presentation. So that's the strategic use of conversation to softly extract confidential or sensitive information without the target realizing it. And why does it works? So because it leverages human uh tendencies like help helpful I'm sorry one step back helpfulness desire to be liked trust in authority uh information sharing nurse and what are the psychological foundation of elicitation uh that's reciprocity so people feel compelled to return favors so if you come to someone that you want to extract information and give them some information that they find valuable people on even give them a gift like a
physical one they might feel obliged to return the favor and that's the reposity social proof is if others share I can share but another example of social proof is uh we mostly do in new very new situations for for us as a human being we act uh we look around and look what other people are doing around us so we don't uh act as a fool you know like or like make yeah make a fool of ourselves in a Okay, that's the point. Uh then so social proof, I had an example. There was a a trial uh in like a big city, let's say uh the United States, New York. So people were standing in the
center of the city looking up and or like a lot a lot of them. So uh everyone was looking up. So that's very suspicious like why are they looking there? Is there something happening? So the first instinct is usually you would think oh what is that like some kind of apocalypse? What is on the sky that everyone is looking there right? So you also look to check why they are like staring above. So that's social proof. So we sometimes act in a way that others do around us. Uh another one uh authority and flattery. Uh compliance increases when approached by perceived authority or those who show admiration. Uh so if you are dressed in a way like
uh I I'll give you an example but don't dress as a police uh policeman uh because that's a big big mistake. So if you meet someone uh in a uh in a clothes of a policeman you already feel like uh authority of that person and that you have to act in a certain way to not uh yeah be in trouble or to oblige his request. So that's example of authority. Uh, another one is c curiosity and ego. People love to talk about what they know. So, uh, yeah, if you have like a very niche, uh, hobby, uh, you would probably want to talk about it if you find someone that uh, yeah, knows about uh, so common uh, information targets or
uh, attackers might often use elicitation to uncover internal procedures. So it policies uh HR workflows system access levels so who has access to what maybe that's a person we want to target infrastructure details so what uh VPN they are using software uh names and roles so org chart is uh something very uh like nice to have and work habits uh when and where the employees work to they like help each other to enter the door so maybe you can use it to target in the link. So if you like watch them uh on in the morning then you can see like uh how they are behaving and like take notes of that and uh counter measures and defensive
strategies uh recognizing elicitation attempts in various contexts. So I will talk uh about not only how to perform something but how to defend yourself so you have uh like the knowledge from both sides. I hope that helps. And so uh if someone uh display displays unusual curiosity like asks about procedures, access, personal details, that's suspicious right? If they uh yeah, if there's like excessive flattery, over friendliness from strangers. I'm Polish so I'm overly suspicious maybe like from like my national level but uh there's like a lot of people that are like very friendly because it's a cultural thing like uh from like people from United States for example uh I'm not saying that's a wrong thing
just like cultural differences are also important to uh uh be mindful of uh leading or assumptive questions so you guys use cloud backups right so he like leading the answer in a way uh that's like uh yeah what to be mindful of uh request that bypass normal procedures. Can you just hold the door for me like uh yeah tailgating in the morning uh or for example you're trying to enter the building with one hand uh with like 12 coffees and the box of donuts in the other one. So obviously your both hands are busy right occupied. So, uh, if you try to enter the building, uh, like this way, someone may be kind enough to like
hold the door for you and then give them, oh, sorry, uh, give them one of the donuts or like something like that. So, be friendly uh, and answer of someone is being friendly to you, but you can also use their friendliness to your own advantage. So, you didn't have your batch cloned, so you're like using the donuts example. Uh, yeah. So another one is inconsistent and vague pretext. So I'm with all the audit team like if you are not confident, you're not sure of your pretext, that's a big red flag. So prepare. Uh very quickly I will not maybe go through all of it so you can scan it with your eyes. Uh so a best
conversational uh triggers and openers for example innocent inquiry. I am new here. How do things usually run during on boarding? And so uh that person appears harmless uh invites exploitation uh explanation. Sorry. Uh and also like another example could be for example flattery. Uh you seem like someone who knows their way around this place or cur curiosity. There's an interesting badge design. What uh is the colors mean? So you can like ask about uh details about access roles for example if you know is red means something else that yellow for example uh and another uh tactic that you could use is uh sub challenges and also false information testing. So uh subful challenges is powerfulation tool
used to verify details provoke correction and extract data without direct directly asking for us for it. And uh for example uh I I I thought remote users uh don't need MFI anymore. So the target likely in response is actually they do. Everyone uses duo. So you already have your some information without like innocent uh question and false information testing that's very fun to do on stack overflow or like forms like credit. So uh you for example ask a question and no one answers. So in the next hour you create account as someone else and answer in a totally wrong way. So then people will uh rush toward uh answering and correcting you to give you the
correct answer. So uh you can confirm assumptions that way and target uh test the target knowledge uh yeah prompt uh corrective disclosures uh yeah that's a fun uh way to go about it and uh subal challenges false information testing now I wanted to talk about red flags and defensive defense tips so uh if someone is repeating mild errors without uh about procedures he's probing uh for policy details uh via correction. Uh if someone shares incorrect assumptions followed followed by or reading. Uh he's testing knowledge or misinformation. Uh naming internal uh roles with wrong info. He's uh legitimizing falsehoods to elicit clarification. If someone is playing confused uh and like vague too often, he's trying to
pull details through help helplessness and sympathy. Uh and defense tactics. Uh yeah, don't correct procedural or access details. If someone doesn't know, refer, don't educate them. Uh beware of anyone testing you their knowledge casually. Treat incorrect technical talk as bait. And another phase of social engineering is exploitation. Is pretty much when the attacker leverages the information and access gained during the engagement phase to carry out the attack. Uh manipulating and manipul to manipulate the target to devote uh divulge sensitive information around access uh to systems and perform actions uh that compromise security. So the purpose in here is to gain access to systems maybe data theft or facilitating a further attack. Um before you enter
the building what is very important is that you know uh you map the target. So you know what is the overlay of the building what are like the camera's placements uh where if there any blind spots uh of the camera placement so maybe you can use it as a path to go in the place that you want to go. Maybe that's a server room. Maybe that's a board a room or maybe like uh you have to go somewhere uh to plant a device. Uh so yeah, you have to know where that room is and how to get there. So that's very important. And while you are in the building, you can also uh try to uh leverage insider
conversations. Uh and so you can use protecting as a contractor new employee and asking for help. You can uh use flattery curiosity. Wow. You must have a high clearance to get back there. How do you manage that? shared identity building using companies lang events or insider references uh to appear trustworthy procedural exploitation steering conversation toward patch policies shift uh changes or visitors uh visitor rules or maybe ex escorted access manipulation gaining someone to hold the door on walk uh walk or walk there past a checkpoint. Uh so it's It's really more less about hacking doors and more about hacking people who use them u corporations. So sometimes you can use techniques to influence uh employees and
g gatekeepers and so security training must address both groups and not just to don't collect the fishing emails but also don't be pressured into uh breaking the process. So if you someone is pushing you with questions just don't say don't yeah don't don't answer and and you can use for example authority pressure like dropping names uh claiming urgent executive approval maybe your urgency and stress that's also used sometimes in fishing attempts when someone sends an email with a link and he tells you you have to it's like one in the lifetime offer and we'll finish in 15 minutes so you feel like pressured for like filling out the form, clicking the link uh but also like uh on the slide I have
only five minutes to get this report to the VP and you like stress so the security card might uh let you pass reciprocity uh offering u yeah donuts cow coffee favors so you appealing obligation social proof I already mentioned that sympathy appeal consistency and foot on the door getting someone to agree agree on something very small and then escalating later. For example, boss me in this time. So if someone does that first time, then you ask for a small favor next time and next time and then after a week of doing that, you say, "Okay, you you've did that for a week from now. Now you you now you can ask them for a bigger favor
because they're like already in a big trouble because they let you in seven times." Uh now we have a role play scenario. So, uh, new contractor needs help. That's like a conversation that looks pretty innocent. But if you look what the what Alex is actually asking, you can see that uh what is happening there, he's protecting. So, he's using a fake crow student or like a a trainee on his first day and our new contractor. I just started with the ventor team. So the purpose here is build builds plausible reason to ask questions flattering and helplessness. Oh, you're a lifesaver. I'm uh probably doing something wrong. So you appeal to ego disarm uh septisen if you act in like a very harmful way
and like you don't know anything uh assumptive questions. So the second password uh that's two right. So that leads a target to confirm correct process naming internal uh tools and groups. Uh so any connect VPN contract tool to FA builds a credit credibility encourages uh open response. Echo boosting uh an urgency. I'm starting to feel like I'm uh in trouble on day one. So makes the target want to rescue uh you because you're like so yeah vulnerable in trouble and they want to help you because everyone remembers their first day probably. So yeah that's that's sometimes that hard. Uh another technique that you could use is framing. And what uh framing is uh is define that's defined as information and
experience in life that alter the way one reacts and the way to make decision you make decisions. So for example, grocery store stores use framing uh by putting 70% lin on a package on ground of ground meat to as opposed to 25% fat because that sounds healthier and like more appealing to the buyer. And that's why the stores use 70% lean instead labing the actual fat content. And simply protect presenting the facts in a different way can make uh something normally considered bad uh seem a good thing. Uh a bit a bit examples of framing. So we can uh use praise framing. For example, baiting the target to talk about systems. Example uh you've been
here for a while. Uh you must know all the systems better than anyone. So implied system status. Uh an example here is I heard not everyone knows uh how to how the VPN file over works. Is that true? Uh so uh you encourage someone to prove knowledge. Uh challenge framing I doubt most people even understand how the rooting policies are layered but I bet you do. So you provokes detailed explanation and kind of like creating a challenge for someone to prove their uh like skills and knowledge. Uh next one is framing through curiosity or flattery. Uh you clearly know your stuff. How would you uh do it if you get logged uh during travel? That's expert flattery and
extracting contingency plans. Hypothetical curiosity. that if example here if someone wanted to bypass UFA uh just for testing how would they uh do it so it's framed as curiosity actually proving weaknesses and another one is leading questions so you can lead through sympathy or empathy for example you pretend like using the helpless persona and example there I just keep measuring this up I'm sorry I one step back I just keep messing this tab. Do you mind walking me through uh how you normally lock in security? So you that encourages step-by-step disclosure uh shared burden framing uh bait the target into reviewing shortcuts. For example, they make uh they make uh it's so complicated for contractors now. How do you even
manage all the extra security stuff? So that uh bait the target into revealing shortcuts, victim framing. For example, my access keeps failing. Uh feels like I'm being uh singled out. Uh did you do through that too? So that creates bonding against personal project process info and uh so we can lead through assumption and proposition presupposition. So pressured uh famil familiarity. So the standard process uh is still mailing credentials to the admin queue right. Uh so invites correction or confirmation follows consensus uh normalizes risky behavior. An example here is everyone uh just uses their work email as username, right? Uh third party framing pulls a privilege information under guise of casual talk. For example, someone told me uh you don't even need
for admin rights to override the lockout. Is that true? And so key takeaway from that is if someone makes it you feel important uh flattered or they are posting your ego pass and think what's happening right here. So because uh that emotional reaction might be exactly what they kind counting on. Uh next example uh I wanted to talk about is mirroring. uh that's a sub im imitiation of person's verbal and non-verbal hearers. So to explain it in an easy to understand way if you look in the mirror your reflection uh looks back at you and moves in the same way. So that's mirroring. So you are acting in the same way using the same uh body
language. Maybe you're adjusting your tone of voice or the speed you're talking in to your to the person you're talking with and that might uh help help you build rapport and make them trust you more because they feel you're like just like them. Uh so uh building active listening that's actually uh something that involves showing genuine attentiveness and responding in ways not uh that encourage uh further sharing. So example minimal encounters like Right. Exactly. Oh go on really and uh clarify and clarify clarification prompts. So uh can you walk me through that again? So why does it work? active listenering tactic because uh people feel heard and understood and this builds comfort and makes them more willing to open up.
And uh if you combine mirroring and active listening in one uh attack uh then uh for example that's an effective social engineering strategy and why because for example on first step you might mirror the language and repeat uh wording complaints. Yeah, on boarding is uh chaos lately and maybe the target will feel understood and then you can show empathy that would stress me out too. Builds emotional bond with the target and ask like prompts. Uh how do you uh usually get around that? Target reveals workarounds. So if you uh yeah use a few tactics in a one attack that could be like even like more effective for you. Red flags or here or repetition of your own phrasing in a conversation
usually good emphasizing early on expressively encouraging someone to keep talking and sub parotting of tone posture and rhythm. So be mindful if someone is like acting as your mirror that could be uh yeah like they are trying something here. So if someone feels too easy to talk to that might be exactly the point. Uh comfort can be manufactured and therefore what you volunteer to share. And the last uh stage of social engineering is execution and that's the uh when the attacker completes their objective. So maybe that's in exfiltrating data, deploying malware and they're covering the trucks. So they're to maybe they're erasing logs or uh yeah to avoid detection and m maintain access. Uh but uh take tips and best
practices when you are on an engagement. Ethics is very important in my opinion. Uh so uh you must ensure the operation adheres to the client's rules on engagement and legal agreements. Uh so you have signed the rules of engagements before the you entering the building. Everyone is written in that document how you should behave. And for example, if the client uh uh allows you to take uh pictures inside of the building, record voice and camera uh feed. So that's all in the documents. So yeah, be mindful of that. Flexibility is important. So sometimes it doesn't go as planned. So we have to adapt on the plan on the fly and because life happens something could
go wrong. Uh that's when a friend comes in handy. So you can use the friend to burn the friend in a way. So he has to leave the building but you can continue. Uh risk awareness if you're questioned or challenged. Have a plausible backstory ready. Uh but know when to abort if things get too risky. Tactical use of situations. That's a example. So for example, uh the goal is to gain VPN and admin console access without triggering help help desk alerts. So you use uh use casual chat with IT support extract VPN software. You guys still using any connect or did they finally switch to foret? Then a conversation with the high HR rep representative
confirms naming conventions access groups. I think I'm in the wrong uh active directory group. My badge doesn't work for remote uh as it usually the VPN admin one uh pink developer. So that narrows down to FA and trust models. I can get my dual page through to go through uh is it sent from your internal uh CA or do you use octa or something and so as you can see there's access path is now partially mapped without uh raising uh big alerts because you called different departments and exit strategy uh there is no uh need to run uh leave as discretely as possible uh leave trace avoid triggering alarms uh causing unnecessary disruptions uh that could raise concerns
like people asking questions what are you doing here and who are you uh if you have a pretext that involves time frame for example 10 10 minutes stick to it and uh avoid suspicion if a question act composed and confident say I must be in the wrong department uh and then leave casually uh so and counter measures defense strategies uh how to defend yourself if you feel that someone is pulling information out of you. So uh deflect redirect politely without giving details uh that's not something I can share but it security can help. So send them to someone uh else that maybe knows more than you but like defend yourself don't share information answer with a question. So
why are you asking? Generalize. Uh give broad nonsensitive answers. Exit gracefully. Excuse yourself or ex escalate politely. Uh report quietly. So capture details of suspicious encounters for the security team. And what are the ethical considerations legal boundaries? I will not go into details here but just you can see that we have computer fraud, the abuse act, GDPR in uh in European Union, wire fraud, telecommunication acts, corporate policy, HR regulations, professional codes on conduct, all of those uh create like a ethical and legal boundaries for those kinds of engagements. and a lot of text here. But to summarize, uh digital and physical elicitation will increasingly intertwine. In my opinion, attackers may use AI chatbots, cloned voices or defy
videos to enhance credibility or in elicitation. Remote work uh social media and IoT device uh devices give attackers more channels to exploit casual conversation and information leaks. uh underground underground markets may provide elicitation as a service scripts playbooks and AIdriven pretext for less skilled attackers. Organizations uh will need uh decisive uh evolution such as uh continuation continuous training not just oneoff sessions. Uh, smarter red teaming, so simulating future style hesitation. Uh, not just like sending fishing emails. Uh, spotting suspicious interacctor interactions. So, train your employees to to pay attention to anyone that uh shouldn't be in the building, maybe give them like a reward. Maybe if they find someone that is trying to sneak into the
building and they shouldn't be there, maybe you can give them like uh three days of vacation for free or something like that. So, everyone will have like eyes around their heads and yeah and be mindful of their surroundings. Uh because elicitation is not going away. It's uh adapting to the new world. uh to human factor remains the more exploitable surface. Uh security resilience depends on awareness, culture and practice and technology evolves but the psychology stays the same. The attacker's toolkit is trust, authority, curiosity and urgency. The effect defensive awareness training must be continuous uh because all tricks adapt uh to new platforms. And if anyone has any questions uh then go ahead. Thank you for listening.
That was all.
If you still want to ask a question and like you're sure to do it now, uh you can catch me afterwards. But uh other than that, thank you for listening coming to my talk. >> Hi uh sorry. >> Um I I would like to to know how do you train uh your teams? the towards the social engineering part. Do you practice any kind of role plays or something like that? >> So, uh how I will answer this question is how to uh prepare yourself for engagement like that. >> Yeah. >> So, a good idea is to go for example to uh Porsche stores because those people that work in those stores, they uh they want commission, right? So, they want to
talk with you. So you can go to stores like I don't know Prada or like a big uh car salesman like uh any any of them will do and ask them question like practice because they will tr they want to uh talk with you. I think that's a good example but also uh before you go uh and do uh physical pentests maybe a step before that could be uh performing a physical audit. Physical audit is something that you don't really have to ask in a cover uh behave in a covered way or like pretend uh like hide yourself back in the background, but you uh they know about you and you go there with like a
card and with the check points, right? So it's like in plain sight. You can play with the doors, look at the cameras, and you can even ask your employer or can I do uh perform a physical audit for you for free just to check my skills. So it's a good uh like example to practice and uh be more confident on an actual engagement where you have to be stealthy. >> Thank you. Great presentation by the way. >> Thank you.
I guess that's it. So, uh, feel free to, uh, grab some of the card games. That's back doors and bridges. And also, I have stickies like I mentioned before. Yeah, feel free.