Bootstrapping Security in the Wild: A Ground Up Guide for Remote-First Teams
Show original YouTube description
Show transcript [en]
Hello everyone and thank you all for joining. I'm Adita Dave. I also go by Addi. The title of my talk is bootstrapping security in the wild. It is a groundup guide to help remote startups with kickstarting their security operations. So let's get started. Here's a bit about my background. I've been in the cyber security space for close to 9 years. I started off as a software developer in various security teams. Currently I'm a senior security engineer at the lead me. I was the first security hire there. Uh apart from my CISO of course uh where I work on building the IT and security operations, implementing security measures and managing our GRC related tasks. Welcome to the company. We are excited
to have you join our team. You are our first security hire. We do not have a formal security or IT team. So let us know if you need anything. Judging by the laugh, judging by the laughters, I'm sure some of you might have been on either side of the situation. So the question is where do you begin? I often like presenting the scenario in interviews as an exercise to potential candidates because there's no right answer in real life. The fun part about such a scenario is now you get to define the blueprints of processes. However, before you start standardizing processes as security professionals, it is important to understand why you need to do something and what
falls within the security bubble you intend to build for your company, your end goal and your assets. Sorry for the lag. Okay, so let's start with the why. The end goal of security is to ensure legal compliance. Therefore, the result of breaking security measures is always a legal consequence. Have you ever heard of how locks are simply meant to keep an honest person honest? You can have the best, most secure door and a theoretically unbreakable lock, but nothing prevents a thief from throwing a stone at the window to break in. So there needs to be a consequence that deters such behavior. Meaning there needs to be a law that allows us to enforce an acceptable behavior. And now
the job of security becomes much more defined to ensure that the law is upheld. With that in mind, ensure that your company has legal counsel. Understand company policies, especially the ones that apply to you. and know if your company is compliant with all the necessary regulatory standards. So let's start with the what. It's important to understand the assets you're trying to protect and the ways in which it can be manipulated. What are you trying to protect? How does it flow in and out? When it comes to mapping out company assets broadly, I like to think of them as pertaining to money or data. Money is of course the balance in the bank accounts, the cost of resources used by
a company, the cost of services needed by a company. Now data is where we usually come in. We meaning security folks and you know internal operations. It is primarily PII pertaining to customers and personnel. It can also include other info like product source code and of course we have credentials that are used to access sensitive systems and infrastructures. So let's dig a bit deeper into data. The ins and outs of data usually involve personnel trying to get the job done. Now let's consider three facets of an employes day-to-day job. They use their device, use the assigned softwares and of course they face some issues from time to time. Our job as security professionals then become to
efficiently secure the device, solve their problems and provide access to the apps required by them to do their job. And this brings us to our main topics for today's sessions. A prop a proposed methodology for each of the three requirements here. Let's start with zero trust device enrollment and focus on two of the most popular operating systems in use by companies Windows and Apple. A laptop either Windows or Apple is purchased from a vendor. This laptop is then delivered to a warehouse or an office location for further setup. after which it is delivered to an employee for their use at their work desk, at their home, where have you. And presumably the same supply chain works
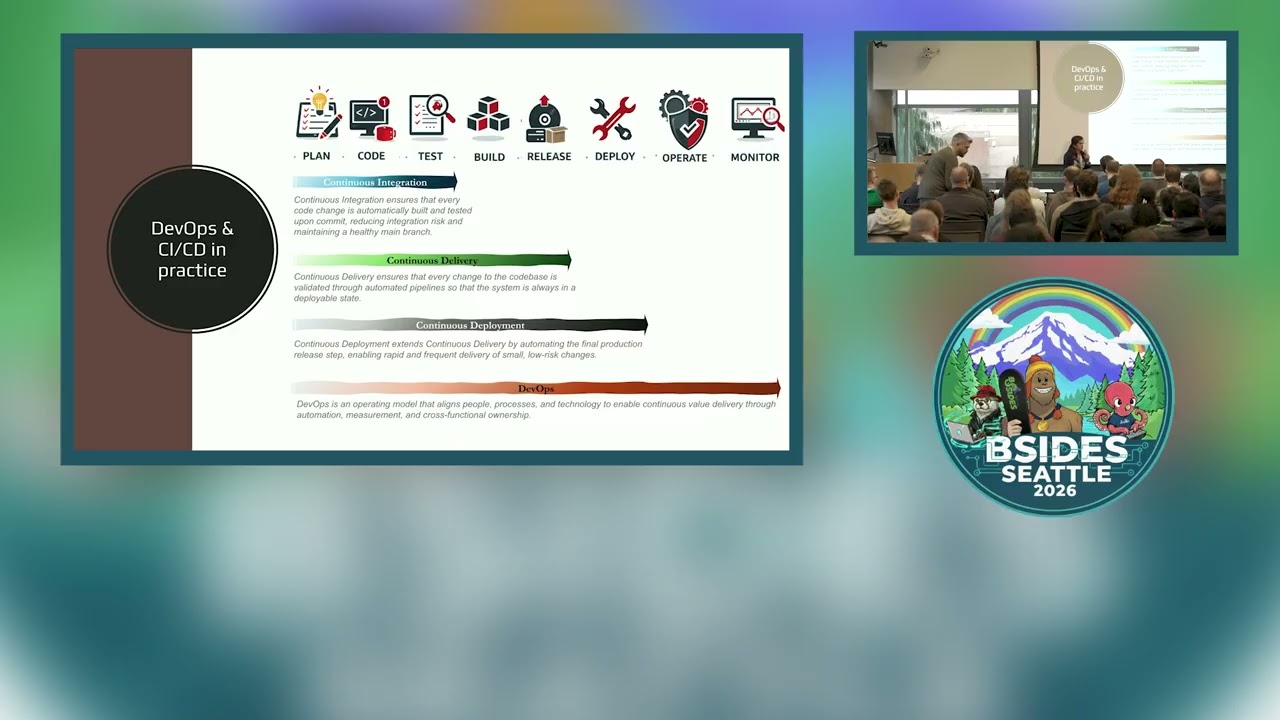
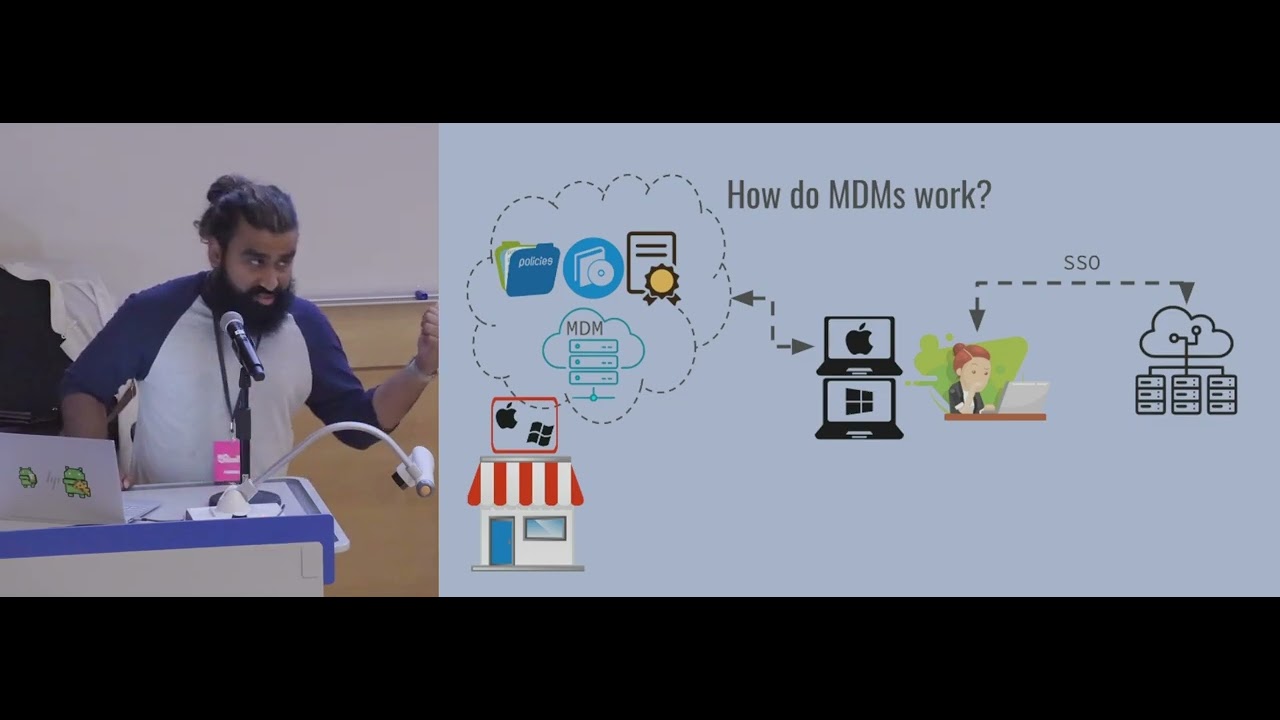
in reverse in case of replacing, repairing or returning a laptop. However, not all companies have the budget to operate teams, store inventory, and account for the operational overhead, especially at a very nent stage. Not to mention the security implications of missing any employee data that has not been set up or erased correctly before or after it leaves the corporate bubble of security for any reason. With that in mind, let's look at how MDMs work. For those of you who are not familiar with MDMs, it stands for mobile device management. Think of MDMs as a server that remember which devices belong to which organization. There's a bit of a lag there. Okay. Uh so MDMs allow you to configure
policies such as your laptop password strength, your screen saver time or autoinstall software such as Chrome, Slack, Zoom, etc. to all the employees or a group of employees based on the role or you can deploy certificates needed for identity verification onto devices without once touching any of the devices. So this aderes to the core principles of zero trust. By employing zero touch enrollment of devices, the devices, softwares, and accesses are only for the assigned person's eyes and no one else. Employees can then use their secured device to verify their identity and use SSO to log into their accounts and access data. and MDMs where they come into picture is that they're often independent third party
vendors that can get information from authorized computer vendors. So the device registration happens automatically at the point of purchase. Not a lot of companies or folks know this. So that's pretty cool, right? Coming to some more acronyms. EMS stands for endpoint management solution. The concepts kind of go hand in hand. For the MDM registrations to occur automatically and correctly at the time of purchase, you can follow these guidelines. The QR code show. Okay. Uh for the MDM registrations to occur automatically and correctly at the time of purchase, follow these guides to configure MDM on your Apple Business Manager and Microsoft Entra respectively for your organizations. And here are some of the popular endpoint management solutions
offering mobile device management capabilities for your corporate needs. Just an FYI, I'm not affiliated with any of them. I've only used or read about them. So, please feel free to use your judgment. And at the end of the day, most MDMs offer similar functionalities. Now, let's go back to our employee now trying to get their job done on their fancy secure zero-ouch enrolled MDM enabled device. They are now facing access issues. They need softwares to get their job done. They are unable to follow the steps in the guide to configure the VPN correctly. Wait, I clearly uh okay, stuck my own nerve. So, what do we do here? We ask them to go to some place, submit a ticket. Bureaucracy
to the rescue, right? So the ticket gets filed on Jira or Zenesk or service now some kind of a ticketing system and then they get a standard we'll get back to you in 24 hours email except requests are triage based on priority and importance and those people are stuck not because it doesn't want to help or security doesn't care because everyone is overburdened and then we have solutions getting developed in silos we have shadow IT to the rescue For those of you who don't know, this is a phenomenon that refers to the practice of signing up for unapproved softwares and using solutions without really getting it approved or telling anyone just to get the job done. Commit the
crime and then ask for forgiveness kind of thing. Well, it gets results and we are living in a result oriented world. So why not? The problem here is that a security or data breach in such an unapproved software or solution goes unnoticed by the security team that is actually liable to protect the company from such issues and that is why it is crucial for security to champion the availability of ubiquitous IT support throughout the company. The solution? Well, look no further than the communication services used popularly in most places. In fact, I challenge you to find an app that does not provide an automation feature which integrates seamlessly with any kind of a ticketing service out
there. Just a forward slash, a button, or tagging a bot. Pick an option. Make it simple for anyone and everyone in your company to file an IT ticket and get quick responses. I like to think of the acronym flow. If there's friction, it won't work. If it doesn't work, there's friction. So, keep it simple for you to build and manage and for everyone to use. Let's move on to decentralizing GRC uh governance, risk, and compliance, which is in and of itself a vast area for those of you have worked with GRC. So, I'll do my best to stick to the parts that are relevant to our discussion so far. So as you can imagine there isn't a
single comprehensive list of compliance standards from around the world. They vary in various factors such as the level of stringency, the coverage scope and of course the geographical jurisdiction. So for example we have ISO and NIST which are widely recognized global standards whereas you have GDPR that applies to companies operating in or serving jurisdictions in the European Union and then again we have sock pipeda fed ramp which are largely applicable at a national level in countries such as US and Canada as well as standards such as CCPA um text ramp if you have heard of it which operate at a state level in the states US states of California and Texas. Um we also have more domain
specific standards such as PCIDSS which involve the payment industry and HIPPA that dictates the standards for healthcare data in US. As a security professional, it is important to understand which of these may or may not be applicable to you and your company as you begin to define your company's security baseline. And an important point to factor in while doing a costbenefit analysis is the frequency of audits and semiannual audits needed to maintain your compliance with the given standard. So for example, u the text ramp level two certification requires you to provide vulnerability sorry uh vulnerability reports every quarter as opposed to something like sock 2 or ISO 27,0001 which can be certified by annual risk assessments.
At the end of the day all the compliance standards have essentially the same core tenants. You need to follow the security principles, best practices, protect privacy, ensure data integrity and maintain confidentiality. And finally, the most important one, can't stress this enough, accountability,
what you can do, what you must do. Uh, invest in a half decent GRC tool. And for the love of everything that's holy, please do not use spreadsheets. um um Google Sheets, Microsoft Excel um like whatever to to track your progress because a GRC tool will allow you to visualize the efforts needed to attest to and maintain compliance to a given standard. Often times it does this by listing the necessary security controls that need timely auditing and evidences and giving you an idea of your audit readiness which will help you stick to your promised deadlines. These security controls often include evidences of change management processes in place as well as security policies applied to devices security personnel.
All of which which we touched upon during the earlier sections. And finally, they may even offer the ability to set up automations to enable you to pull relevant data that allows you to audit different controls more seamlessly. The second thing to be done is to set up your vendor management solution, which is often an offering by most GRC platforms. This is crucial to get done as soon as possible, probably even before your first ever audit. Why, you ask? Well, maintaining a vendor registry allows you to assign an app owner, not just for budgetary purposes, but also from an accountability standpoint. It allows you to engage stakeholders and delegate tasks to them from the very beginning. In most of my experiences,
the humongous task of audit gathering often falls to one or two key stakeholders, which can get stressful during audit time and it's not a scalable process for sure. And finally, since we now live in a world where we are being sold a host of different SAS solutions at all times leading to a SAS pearl, using vendor management solutions as a source of truth for an approved list of vendors only to be used by the company allows us to effectively account for the surface vectors that need to be monitored and um in a way curb the sprawl. So feel free to check out some of the popular GRC tools in the market. Again, I'm not affiliated with any of them.
I've only read about or used some of them. So, please feel free to use your judgment. At the end of the day, most GRC's offer similar functionalities. So, over time, your choice of your GRC becomes a matter of preference for yourself and your auditors. To summarize, let's go back to our employees experience with the security bubble. They are able to
Okay, I promise you it was just text.
Oops. It all came at the same time. I was lying. Um, okay. So to summarize, let's go back to our employees experience within the security bubble. They are now able to use both SAS and desktop apps on their secured endpoints which in most cases is a company provided laptop some cases mobile devices but you know and they use this to download upload and process sensitive information all the while following the basic principles of zero trust and maintaining accountability required by the appropriate compliance standards attested to by your company. Any questions?
Thank you for your time.