For Crying Out Cloud - Stu Hirst and Tash Norris

Show transcript [en]
thank you very much it's an honor to be here actually this is the first time myself and Tash have spoke together but we speak separately at events in the UK so to be part of these sites here is awesome - to whose task we are the cloud security team a company in the UK called photo box but there's actually five brands that are part of that that group one of which is here in Munich called poster XXL we have a better split presentation here around some of the experiences I've had not just in in photo box group but in my in my career and some of the learnings that I've had and I think Tosh is gonna
expand on some of the the things that she's been she's been part of so hopefully there's a lot to learn and we can share some of our our failures as well as well as our successes and so a little bit of background about me I've been an IT for about 20 years but I've only been in security about 7 or so so I'm not an expert and I'm actually not convinced that there anybody is in security who's an expert because it's such a difficult field and I say it's there's so much to learn I do public speaking I guess some of this this kind of thing I run a meet-up in Scotland which which we get a great amount of people at I'm
one half of a thing called cyber Scotland Connect which is around building communities and bringing organizations together in Scotland which is where I live and I think that's really important I think the keynote today made some great points about community and events and how important that is to spread the message within security and our wider industries and personal lives I also run an AWS security slack forum or I'm not sure I run it I facilitate it there's a QR code towards the end of this presentation you're welcome to join I think there's about a thousand people on there now sharing all sorts of great information and - hi yes sir I'm - um I am Kohli for
their OS women at sec London chapter which is launching in April which is really exciting I'm also on the board for dev second which is a developer security and operations kind of combi conference that runs around the world I know there's a threat modeling staff that's my passion so I work at photo box which Jing and I'm in his class security team but we are in a really small security team which I imagine quite a few of you might be able to relate to and having come from a big kind of corporate enterprise as previously a financial services moving to a really small team has been quite an eye-opener for me and it means that I don't just do kind of my segment
of security I also cover anything else that kind of comes in I might be able to touch them so threat modeling is something I'm going to talk about a little bit more later and it's been a real way for me to engage with a lot of different areas within the business and how to support them and being more secure so do some clouds tree stuff I also speak a lot Arnon blue teaming and cloud security so I'm really excited to share with you and a little bit later in this presentation some of the kind of my favorite blue team tools and techniques and that I use with the groups I went with so I'm gonna have Matt sister who's
gonna kick us off cool so as I said we have five brands in the photo box group so I like memes by the way so that might be some silly pictures and things because we don't take ourselves too seriously so we have five brands for those brands or in AWS and I'll explain a little bit more about that so joining one company can be daunting but generally it's one text back it's one one serve code we've effectively joined four companies at once myself and - because group security sits over these these brands and as I said four of the 500 in AWS so it comes with a stack of complexity beyond perhaps what I've been
personally used to and some of those things are not unique to covering lots of brands this could be within your organization so differing tech stacks different program languages use a number of different program programming languages across the the group and cultures you can have different cultures within different teams within your business let alone across different brands different levels of maturity so again some of our brands are new to AWS or newer through AWS and some have been in AWS for a number of a number of years business structures different sets of executives to speak to different boards to have to go and fight for money at different levels of knowledge and so these are things across our group that
we that we have to try and them neat neat the challenge for and from an AWS point of view we have a number of accounts spread across those four brands one brand uses tariffs warm weather uses cloud formation makes our lives a little bit more tricky to try and strategize cloud security and I'll try and explain a little bit more about what I've tried to do in the short time I've been in this in this role so my initial journey I actually joined as the head of security engineer engineering at the photo box group and realized there was a gap potentially to do something in AWS from a security side so I created a role
the role didn't exist I decided to go and do it and then try and recruit to build that team and as etosha mentioned were just a small team of two at the moment and moon pick shifted their height we're a high transactional e-commerce website and shifting into AWS the initial work that I did there was not the sexy you know tooling tech based side of things it was sitting in well architected reviews with AWS it was manually auditing accounts and setups but it was the first time really a security individual had been at the company at that point in terms of that the the maturity and the the movement so it's really really important so if any
you're in that journey into the cloud and you have the ability as security professionals to embed yourself in that at the the very early stages and it's super important but what do you focus on how do you know what to go after that was the challenge I found myself having um if anybody's this is an opinion as opposed to a fact so if anybody would like to share this out and this to me is the most important thing that I've done in this company it's the most important thing that I will do in my security career what's the most important aspect of securing the cloud anybody brave enough to shout an idea out that's super
important that's crazily important it's not it's not what's on the next slide but so for me it's recruitment it's getting the right people in to do the job because if you don't have the people with the talent and the skills or able to learn those skills you're not going to do all that great work that needs to be done so for many greats that work alongside - incredibly skillful skillful person in the AWS space so for me recruitments probably been the most important part of the roles that I've been a part of in security and the other stuff is super important as well obviously it just need to say no so that that's can it but that's a challenge and we
know that's a challenge in security the diversity thing was talked about this morning as well we continue to try and work hard to make that better but yeah recruiting talented people into your teams is it super key that's what I try to do was define cloud risk risk is not a sexy word I'm afraid it's but it's what will give you this strategy or the ability to build strategies around what you go after first you don't need to do this yourself because there's a whole stack of benchmarking out there or other organizations that can help you with it I found the CIS benchmarking for AWS incredibly useful and what I tried to do was really define around 50 to 60 major
areas that any business could be concerned with from a pure AWS point of view and this is - it touches great help as well and we really split it into these eight different areas of which this won't be an unusual to anybody in the AWS and it's really given me an opportunity to focus on where our particular sets of brands might want to strategize and you can see that this those eight different areas there now I've put these into a document on github you're welcome to have a look at it it's just industry based it's not it's not company specific but it gives you an understanding of some of the areas you might want to think about if you're an
AWS it's given me personally the the ability to really think about what to go after now I also want to talk about how we how we work as a team because that's really important and we're actually really I think we're really agile small team within our business we're an agile organization anyway and that means different things to different people but with very heavy users of JIRA anybody who follows my my boss Dennis Cruz will know how passionate he is about mapping things in JIRA so what I did was I took those 50 or 60 potential you know business industry-wide AWS risks and link them in JIRA to our cloud infrastructure higher level risk which any business would have if they're in an
AWS we allocate management and technical owners to those things well within jira so that we can quickly see who's responsible for what and then we link our okay ours which has objectives and key results for anybody who doesn't you use those which are innocence projects there they're the pieces of work that we define to reduce those risks and we link them to many vulnerabilities were then find within the business and track progress on those pieces of work and that allows us to to see the work that we're doing to visualize it and to be able to track it and see whether we're reducing reducing these risks now we work in two-week sprints which there's only two of us but
it works really well this is not our Kanban board by the way it's just the generic combine both bars it's got far more in it so we split our chaos into manageable chunks we break those down and we do sprint planning but we've also started bringing lots of other things into our Kanban board mass sprints so business as usual work work we know we need to do team meetings perhaps things where we do dedicate quite a lot of time we've been our incident work in if things happen training and then we have a service desk where other teams can create work for us which which all comes into this that these Kanban boards and allows us to
make decisions on what's more important and I think it was better reporting to the the people that need to see see what we're doing I think security can be very difficult to visualize what you've achieved over a period of time and I'm not saying sprint is a perfect way to do it but it's working for us I think so what I really learned over the last six months been incredible learning curve particularly because I don't perceive myself to be an expert in some of these areas your journey has to start somewhere if you don't have a security team dealing with AWS or cloud use you should maybe try and consider how you you make that happen especially if
you've got lots of data in there changing businesses takes real time and graft it's just painful it can take years to change the culture of one business let alone four or five own people repeat mistakes I'm certainly guilty of that as I'm sure anybody is but we need to find a way to make that better how do we either water make procedures or processes to to prevent people making same mistakes cloud is hard and complex as is all of security I think and recruitment for for me is key so what's helped other training platforms are available I find these things super useful or invest a lot personal time in in these thin cloud guru for me of lei has been
has been great these are the must pay them product cyber e is a free learning tool there's lots of good videos on there too to help you learning and part of our roles is continuous improvement in continuous learning I spend a lot of time on YouTube and SlideShare watching presentations from other people who fix the problems that I'm trying to fix because I can't spend all day trying to make up ideas is to is it's too difficult other people have generally solved those problems so I'm going to pass over to Tash who's gonna give her version of the story so I'm sure you did a great job when he joined of kind of setting up
this the team this past routine that didn't previously exist at all and then defining some of the kind of security in the risk areas and then I came along about eight or nine months later and the thing that I really wanted to talk about with you guys today was based on that kind of underpinning structure that she's laid out how do we actually start to really make a difference with those teams and how do we guide them and the first thing I learned was that I had this preconceived idea that for our engineers and moving to the cloud was easy is just picking something up and running with it and brought it actually was like where's software engineers that
were previously just software engineers that did their one thing became infrastructure engineers database admins back in engineers and you all of a sudden become full-stack without really being given the support and the guidance to be able to help them so being a very very small team I wanted to think about the things that I could do to make an impact in the quickest way possible with our teams and without stretching myself too thinly without filling up that Kanban board too much which I'm still incredibly guilty of and I wanted to share my favorite things so the first thing is my cloud security pyramid scheme this is my my Ponzi scheme as it were for security this is how I scale so
it's actually security champions but I recognize that I am I am one and with students just two of us by the top and we work incredibly hard to be able to kind of scale out and to expand that team so I figured as I would just use tougher engineers to do that for me and when they're not included in the security team budget which makes IC so be happy um but - they're already embedded within the teams they already know what they're building best they know way better than I could so we created this cue champions program which to its credit and to our Caesars credit did already exist but wasn't very well attended and became this way of security
teams just telling the engineers what they've done wrong that week or telling them the biggest vulnerabilities and risks that were present that week for our teams and what we actually did is start to turn that around to become a forum where we could share things we were working on where we would encourage our engineers to share things that they were working on and even better we use it to crowdsource problems and solutions so we mentioned we have all these different brands and they're all using different tech specs that means different CI CD pipelines we've got um a huge spread of tools just tools and languages that are being used which means things it might be repeatable
within one company all of a sudden aren't repeatable anymore but the problems are still the same right the problems of key management of certificate rotation all of these things are still there of encryption so what we did is we would get teams to present a problem that they've been facing and we would crowdsource that solution within the room to a point where we would get where each of the brands had pulled something from it they were happy with and then they were gonna go away and talk to their wider teams about what that solution look like no longer did I have to have the same conversation four or five times but it was happening for
me it at one point and then spreading out through our teams we doing some interesting stuff with this gamification and we've been looking at kind of how we embed it within our engineering teams ok ours the idea is empowering security teams or engineering teams to become your security SMEs within their environments so that when they do come to you it's for those bigger things is for those niche problems there's really interesting questions but the rest of the time they are your eyes and ears within those teams and empowering them themselves so it really well so far anyway the other thing I've been doing is threat modeling and hands up anyone who knows what a threat modeling is
awesome say I'm busy don't know and I'm gonna be guilty this there's a whole load of different frameworks and ways to threat model I tend to introduce it is quite a simple process and I'll cover that in the next slide but my favorite thing about it is that everyone already does it and for those of you that have a question earlier about how you get more women in your teams let me tell you the women that are looking join your company are threat modeling you so they're looking at where your office is what your team is like the things that you do and they're doing a risk based decision on whether or not they should go enjoying
things like your job descriptions a threat modeling that and I'm looking at all of those things you've gotten there in your required section which you know that you're not gonna hire but you put it in your required section a knife threat model that and I think well I'm not gonna meet all of those things in is required section so I might not apply if you think about when you go on a flight somewhere where you park your ass at your car somewhere you threat model that situation and you think about what are the things that could go wrong or what are the things that could happen if I if I do that thing what might not happen if
I do that thing so threat modeling is something that is very real I'm very natural to a lot of people and what I do in teams is I just add a framework and a structure around that and what it does it allows those teams to get up skilled in security it allows me as a by-product to learn a lot more about what they're doing like for me it's been a really great way to kind of expand the relationship and the way that teams reacts in behave with each other so how do I do it so I just use for questions I use a really simple methodology and then I partner that with something called stride so my four
questions what am i doing what can go wrong what can I do about it and did I go do a good job and I say I a lot here but I get this stuff for engineers to answer this question so I get a whole team a whole squad in a room and I get them to sit and I I ask them why are you building joy up for me show me the architecture or a data flow diagram whatever it might be and then I think what can go wrong most software engineers will have in their head these niggling oh okay as long as I don't get too many requests their API and pointed be fine as long as no one
works out that really complex URL will be fine or whatever it might be and this is a great way of pulling out and actually walking through okay what are the problems with that things I've seen previously with public s3 buckets or public objects in a three buckets is teens saying things like well it's a really obscure URL and he'll not find it and we know there are sites like grey hat warfare where it will enumerate and scan for public objects they've got crazy complex URLs there's stuff that's it's just not safe and threat models is a great way to pull that out we always make sure that we go through mitigation options the final bit
is the did I do a good job it's a really great way to get that team together and understand is this working for you is threat modeling a useful exercise what tools can we use to make it better and there are some tools that I use with teams that helped you make us find to help make finding threats much easier and much more straightforward and I'll cover those off but if I could recommend you take one thing away if you're not doing this already threat modeling is a great way to scale that security piece and it is also a great way to build relationships with your teams so does anyone actually read your security policies anyway and this is the biggest
thing when I was doing the threat modeling where's seams we pull things out like a lack of encryption or public objects or whatever it might be in a guy this is simple stuff and across the companies that I work for I kind of realized that all of our security policies are these huge bloated documents that actually have the security team haven't even read and someone from a policy team I've put together or it might be something pulled directly from a policy pack online and it's actually unreadable or unmanageable so I figured when I'm doing these threat models and we're finding these bags I can't really rely on our security policies just to support that so I
thought well how do I they're still useful and I still need them from an audit requirement piece how do I actually make them consumable so one of the things that I'm working on at the moment is writing tests so this is an example of a BDD test from that I was cloud security projects but effectively rather than encouraging engineers to read these huge policy documents are incredibly boring how do I write automated tests in a language it's already familiar with our engineering teams whether that's tdd whether I'm doing Ruby Python whatever and how do I kind of automate that findings and the great thing about cloud is we've now got infrastructure is code so previously where my test might
have just been up to it an application layer I can run these tests against terraform or CloudFormation and we have to write because we know with all these friends that we've got all this fragmentation i hands out to automate finally security vulnerabilities but i can also rewrite some of our security policies into a way that's much easier to read because the other thing about these standards is the language is so formal and complex that it's not even really consumable so this is something that's been really powerful for helping those teams the other thing is gamifying security these are elevation of privilege cards by Microsoft these are free so you can get these from and from
github from Microsoft website and I'll share a list of all the resources at the end and these follow the categories I've stride which is spoofing tampering so on so when I'm in a threat model am I thinking what can go wrong and I do in step 2 of that model and teams of struggling to think of security issues because they're they're not security experts these are a great resource for helping them to think of different and attack vectors or different threat vectors and they're really just prompts some of the language in them is a little bit and I want to say archaic but they were they were built quite a while ago and but they're great problems they help
teams to kind of really quantify denial-of-service problem and when we think about services like lambda and AWS where if you've got a lot of lambda invitations happening once you can hit a throttling problem which can be quite serious it's something that Netflix came across through at the very beginning and then expanded this whole architecture idea of having many many AWS accounts for one application on one service and but these are a great way to kind of build that out and bring those threats out during the design process you don't even have to wait until they've built something and that was the thing that I found with the test is I had to wait until they don't already start to build
the code and now I'm bringing it into the design process I thought about this a little bit more and I thought these are great but I'm still relying a lot on the language and I still they're not cloud specific so I'm gonna introduce you something that I've been working on I've not yet released it so you have to be patient if you like it um but I wanted to show you something that I thought might take this to the next level um and I'd love to invite you to contribute as well so I've been working on cloud security elevation of privileged cards so this is a way of taking that gamification a level Fair there and the same with the original
elevation of privileged cards you can almost play it like a car game you can get points but the language wasn't really that great so I've been working on a Tobias specific threats and I've also been talking to someone from from Asia and luckily from Google I felt really guilty about being here at Google and speaking a lot about Amazon but I've been looking at how do I create a BBS specific threat vectors that will prompt engineers to think of okay what would happen if this happen in my environment am I asking for authentication authorization every layer my inherently trusting and what's coming am I using VP cm points and have I got public objects rather than you know I've checked it on
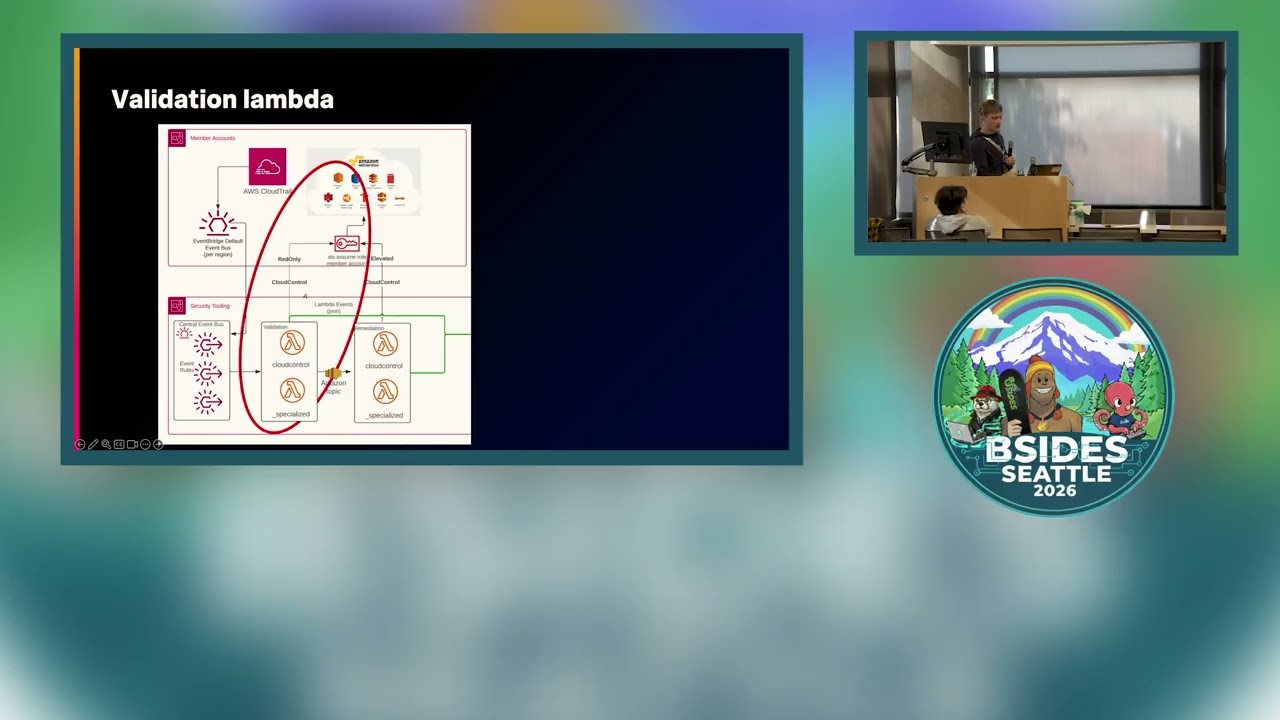
my buckets on public and that's fine but can anyone release any objects anywhere so we created these cards and which will hopefully be really soon open source and I'm looking for contributors to them so if there's something that interests you and you're going across this let me know and you can absolutely contribute to it but already kind of doing quick trials with teams there's been really positive way for them to identify and come up with threads that can help make us more secure so these are my favorite resources and things I've not mentioned and POW custodian which is in the top one there when I talked about writing my tests at the beginning of the abeer DD
what this does is I then implemented they are lambda function within the AWS account itself so if I've missed it in a test phase I can have a lambda function that continually scans for public objects in s3 or unencrypted EBS volumes or overly permissive ion rules is really customizable so whatever you can think of you can you can alert on it you can also make it preventative so rather than just sending off an SNS net earmuff you've got an unencrypted object you can get it to just kill the ec2 instance and terminate the violet volume which is a little bit intense and but I found it really useful for those high-risk environments you can get it to
be really preventative on that side just make sure your engineers are super happy for you to do that before you do it and the only other thing I want to call out on there is security monkey this is a Netflix tool for security has anyone ever configured Netflix security tools before yeah it's awful so no documentation is really awful scream on key especially realize one of the dependencies they have they rely on a very specific older version it's not version pinned and it took me a really long time to work that out when I was trying to get it to work and however it is pretty cool once you get it up and running in AWS it's really cool and I
would just if you're ever looking it can forget a Netflix tool there's loads of complementary blogs by people that have got really pissed at Netflix and then rewritten their own deployment stuff but it is really cool once you get it running these are my favorite resources I think that's it from us and anything else I'm do come and chat to us is where we have an office it poster in Munich and we work for these other brands as well and them if you've got any questions about the stuff we do in AWS let us know you'd be more than welcome to join our slack forum and it's gerunds there's a representative some of those different companies in there and they
cover a lot of different topics and just news about Kyle and there's some Azure and Google forums I believe on there as well nothing more for me that was awesome thank you very much I think thank you thank you - see
probably actually have time for three or four questions so your hands up please if you have questions by them sorry I have a question what's your go-to tool about visualizing architecture in AWS how how do you go about this yeah is a saccade mapper and cloud craft which you've been quite good for putting out the architecture I must admit when I do a threat model I make people draw it and that's because about five or six years ago I had the case of the missing firewall which is a box that made it so away somehow from an original draft design to a design that was a proof but never actually built and no one could
answer about me so I get people to draw it in every threat model anyway and the cloud mapper especially has been been really good I think that's as a small team that's a really important thing because it improves our learning but it improves the the engineering teams learning as well we're in a sort of tricky position about what tooling to add at any point in time with it as a small team because it takes effort to to be on top of it okay so I see a question here are there other questions in the room that I even made me missing you're welcome together afterwards we'll be here all day hi so I've got a question about the
secure champions area and forgive me if I missed it in the presentation so how did you actually approach teams about it hey I've got this cool idea that I want you to start doing you know how did that conversation start say and it's a good question because it can be really hard to get people to invest time in security right am I missing it before I took over the forum people were what I'd like to call voluntold so rather than being volunteered they were voluntold by someone and what happened was there was a conversation with leadership and leadership were really behind it but there wasn't really a conversation in engineering level so people didn't really put themselves forward so they
were voluntold and what I've been starting to do is work on the PR of the security team and that's really how people today I want to have more conversations the most accessible thing I think I've done so far and it's a bit cheeky because it was really recently is I held a lock-picking workshop and so just in our breakout space and I kind of where people eat their lunch I had a message earlier in the week and I got it kind of in their car off this newsletter and did some stuff on slack and I was like I'm just gonna be doing some lock-picking workshops if anyone wants to come along and learn about lock-picking and then
once I got them there I was like are you gonna have to learn about this scheme and but that was really fun because I got people from marketing design our UI UX teams as well as tank and for me for the security champions to be really successful I need people from everywhere in the business including those people that come up with his crazy new products that we should all work on and I wanted them to engage in chat to us as early as possible so I would I obviously have these conversations with leadership to say hey this should be part of your objectives and this is really important and I can help you find bugs earlier
shift and left all of that stuff and but then I would just go on like a marketing rampage and do this stuff like free lunches and all that stuff that shouldn't have to work but you gotta do but honestly the lock-picking stuff I got stuff Amazon for like the equivalent of like 60 euros so load of padlocks the load of pics and I'm home loads of people and that was there I think so far that's been the best way of pulling people in I agree I mean we've got an OK are specifically on with cork we're calling it our PR campaign and that's I was trying to get around all those different brands and all the areas of
the businesses in ways that worked for those parts of the business because as you say some things work for one team's other things you know don't work for others there are different technical levels different levels of ability and I think I've had a similar experience in other companies where during a training course over the fence and hoping that somebody's gonna complete it and be enthused by it doesn't actually really work you've got to find other methods to engage with teams in whatever way that is now it is a big commitment in time they it's a huge part of our of our roles from a time commitment but yeah things like the log picking it just gets
people involved and they realize that actually a lot of what we do is not boring and it's not dull and we're not trying to tell people to not do their jobs so yes just trying to ping people on that journey I'm gonna do a bit of a shameless plug in the lock-picking part I you think we don't have luck they fix to lock to lock thing right now but there are a few logs that need to help the cat escaped from the box that you can do from the online challenges so please check out the CDF afterwards and doing lock-picking worships could be an idea for next year so if there are experts here or maybe you want to visit us again
it was maybe one question here and that'll be the last one I have a question is that you're using Jireh for tracking their phones did you have to like customize it how do you write the phone's first can you talk more how to set up yeah we've heavily customized do we have all sorts of ticket types and labels and tagging and yeah it's quite heavy actually in terms of how we use it with that I saw bosses create a tidge it's called the GS bot so it's a bot that allows you to quickly create tickets and link things together which has been really really clever but yeah that's taken time to do yeah we've Kabir
it's like but they're queries I'm the GAAP I and then we would say like show me threats related to be created IT assets and threat ticket types so I when I do a threat model I have an idea it could be like a particular container cholesterol whatever and then art I'll link my threats to it as your ticket so then teams can link their stories to fix today's so then I can create a slack bot and I can be like showing me all the threats related to this asset and we encourage the business to do that too and then you can see all the threats and the stateís what I've been fixed what stories it's really cool and doesn't get
a lot when I'm like this is all the stuff you do and Dennis is created so I see so who did a lot of the underpinning of that that geo taxonomy and it's got some slides on SlideShare and I'll retweet them today slavish pug from my Twitter and I'll retweet them today and so you can see a little bit more info on how we do that geo taxonomy there I've seen all the linking as well as probably are killing the find or break coming soon thank you very much