Cyber Zoology: Protecting Your Network from New Breeds of Attacks with a Raspberry Pi
Show original YouTube description
Show transcript [en]
we are things are moving along here and I hope you are enjoying yourselves please be sure to give us feedback at info at besides tota so we know how we're doing both positive and negatives are good because otherwise we can't grow all right the next talk is called cyber zoology protecting your network from new breeds of attacks with a Raspberry Pi would you please put your hands together and welcome to the stage Patrick Kelly good afternoon can everyone hear me OK to loud to quiet be quiet go home go back to America gotcha ok so really excited to be up here really excited to be in Toronto Kem sektor a couple years ago director around this area I'll be honest
with you 2 years ago it would never have even crossed my mind that I'd have the opportunity to speak to any of you today and to say that I'm humbled as would really be understating it so we're going to talk about some things I've been looking into the last couple years and we're gonna scope this down on the Raspberry Pi so that you can take this home and/or take it to your lab or wherever you can to try some of these concepts out I will be releasing all of the code that you'll see in here the detection x' on a github repo you can grab it also the production image for the PI 3 that I use for the things I'm
gonna showing these slides will be available as well so you can image it and just do whatever you want to do it so
all right so Who am I to be honest with you I kind of get bored of myself so in short I'll skip to the most important part last night I got to see the first Leafs game go Leafs got really exciting time again if you're gonna kick off in Toronto on something you never dreamed you're gonna get to do starting out with the Leafs game winning is a pretty great way to go so let's rock and roll okay why are we here logs lie if you've ever set up a sim if you've ever done ir if you've ever reached into a Windows machine Linux box if you've ever tailed syslog after an incident you'll understand that logs lie even if
they don't lie you're stuck to the technology and the fidelity of when not logging concept and that mechanism was created in fairness it's a good effort but it's never going to be good enough so you know intrusion intentions on the board are only tail portion of story and this is something that I learned working for years with Sourcefire and with Cisco and Dell SecureWorks we would be able to pull some of the traffic down and we would be able to see north to south but we really didn't have any context around that what did it mean what did it do when it got through passing through that thing bless you I but you know we can't go around
dropping $20,000 Sourcefire sensors every we want them to go it's just too expensive in even setting up 1u you know super micros may be outside a bunch of your organization so probably we're having is that the visibility was not multi-dimensional it wasn't contextual and without qualification of threats too much time was spent chasing things around does anyone in a room ever walked into work and had 7,000 indicators come out of your sin their IDs and you find out that only seven of them meant anything it's a long day right probably didn't get through this so here's why I wanted to solve you know first what is this traditional is north-to-south your signature-based they look for isolated
atomic indicators there's very little correlation it takes place for instance if it's store traffic you may not care if that's coming off your guest Wi-Fi network you would really care if you're doing IRC private messaging between your to Vienna or ESXi servers that would be something that would probably perk your ears unfortunately this past year we worked with a client gave them packets of that happening and they hugged it welcome to my world so we're trying to do here is correlating those atomic indicators with full bra IDs proto analyzation so that you have a better idea of what that attack traffic looks like and what's really going on then you can do some enrichment on those locks from disparate
sources that way you can add a little more color in context to it so again kind of beating this to death because even when I look at machine learning even when I look at AI concepts we're still leaning back on those old principles that we'd already determined are broken such as machine learning off of a signature art fellow shown to artificial intelligence off of a signature we keep looking for that one atomic indicator hoping that we get to see it again and chances are you're probably not going to so another problem that I wanted to solve right is when you're working in industrial control environments and things have been engineered to have a shelf life of 20 or
30 years even if you want to log things you can't there isn't a space to do it if you wanted to back haul logs there isn't a mechanism there to do it with you've got some significant issues here just getting the data to a place where we can figure out what's going on so in my ID after working with Sourcefire through the conversion to Cisco and they are acquired working with SecureWorks working internally these are some things that I look for when I'm making an effective security platform blended IDs it's not good enough to have sericata and then another signature base we have to have the ability to drive deep down in packets done in protocol flows and
bring that stuff out the other part that I'm finding out is okay you find something now what do you do with it most environments isolate you and silo you to their environment that's not an environment that you're spending the rest of your time in so you're having to make a concerted effort to go back and forth that's why I really like being an import and export and Stix models is anyone here familiar with sticks thank God I thought I'd be the only one okay so short version of it just so we can move along is that the idea behind sticks is when you would export your indicators of a compromise you would have a little more fidelity and
construct in context around it see how better understanding what was going on at the time that that took place again I talked about logging a beat on that pretty hard when I said you know even your logs are going to lie to you but the fact is is Jason's going to be better than syslog I know that there are other things that are coming out that are a little less overhead but JSON works I was gonna show here in a minute that you've got to have some portability because everywhere you go is not always gonna have a nice 42 you rack in there for you to shine you know push your shiny blinky light box into you right so
API is to pull things back extensive the extended connectivity connectability pardon me to windows logs pass a total virus total so I started working on trains that's called in by DHS as culling some vendors or something that are up here and they said we have a problem we're doing positive train control but we're finding problems we have trains we're putting Wi-Fi ended in but we don't really know how to get our heads around it we think that there's something to happen on our train network but we don't really know because we don't have any logs because we wanted to do logging but there's no space in the ACC or the recs to actually do that what
are we gonna do so well great I'll tell you what I'll build an appliance will come out little rack it will take the data back out of it we'll take a look at it sorry sorry sorry sorry when we and when we engineered this 30 years ago there's no special slots there's nothing open for you to use by the way you're probably gonna have a problem getting power for what you want to do as well awesome so I started looking at these things differently right you have OTN you have IT I t's a little bit easier you know we can drop sensors in between VLANs we can profile those sensors if you're going to put it in a
VM and the thing that you're wanting to look at is V motion traffic then we don't really need to load up protocol detection and deep packet inspection for everything else you can lower that profile and that usage down additionally what if the places that you need to backhaul traffic from don't have a dedicated hunter mag drop or a gigabit drop what if they'd only have the cable coming into it at all we haven't had a problem so the things considering going through this is consider remote sites consider executives personal networks I know that they hate to violate privacy but if anyone's done IR they understand that insider threats and layer 8 is the worst so here we go
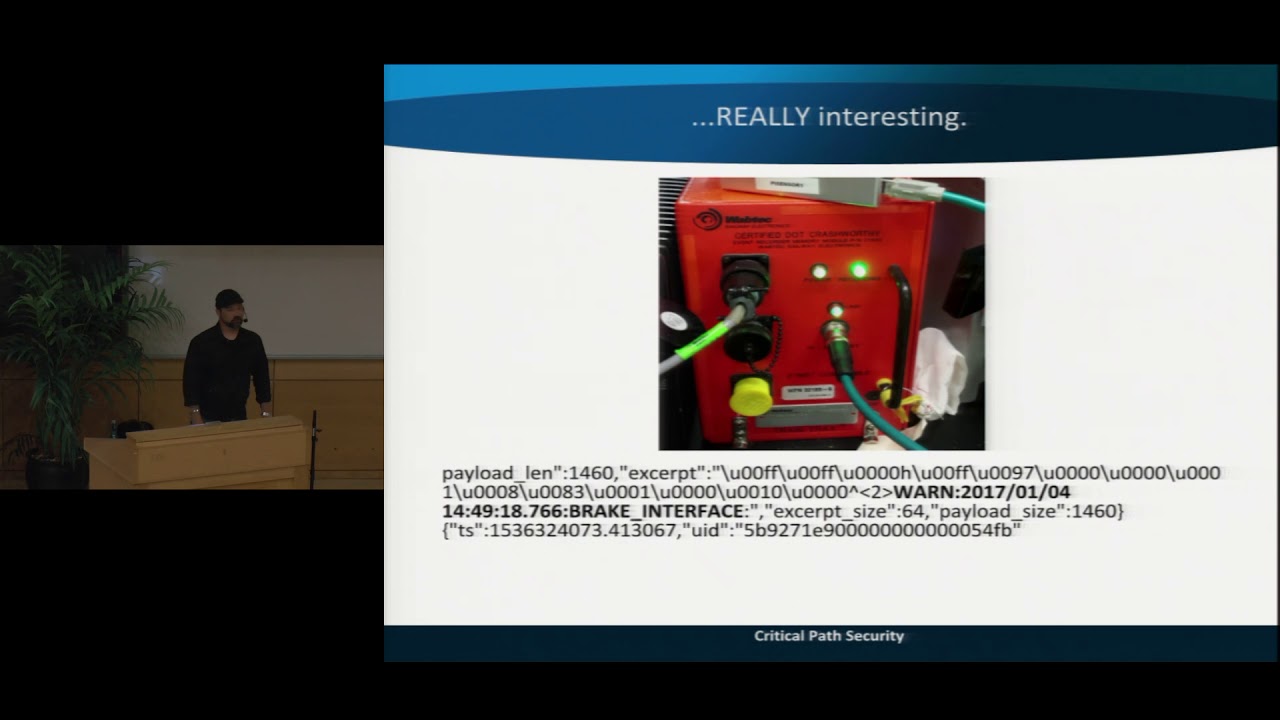
let's move in the in in whatever you can make fit on a train this is a real-world Jam right here you don't always have Rackspace they wanted to understand what was going on inside their traffic Wireshark isn't going to do I can't stick a laptop or a Dell powered server in this environment you have to think and do something different it's a great let's build a Raspberry Pi I can power it our batteries I can do something with it and then I can do a proprietary which are really hard to find and make cable to plug to the j5 so we can get all that monitor traffic off but here's a set of problem security is
a narrative right it's based on a fixed construct of time if you don't have time and you don't have context then you can't really determine exactly when things happen in the order and if you should carry you shouldn't care but when you're dealing with trains you know reader doing Wi-Fi between white side boxes and if you're driving down the highway and you see the big metal boxes by the road those are way sites to connect back to the back office for the carrier or if you don't have that we can do cellular cellular is very expensive and then we move to the third option which is a just horrible for us they're trying to solve security problems which is 220
megahertz radio so imagine if you need positive train control to work in the back office must have enough bandwidth to say you're running into a flood zone and they can't get that across because we're blasting the wire with JSON full fidelity bro packet logs we didn't reduce the threat service we just increased the threat surface and this is a serious thing I like my french fries I like my orange juice and unfortunately we carry nuclear waste on trains too so we have to think of how do we do back pressure and properly store and forward messages to the point that even when they come out of an area and we can get these logs that do we get to fidelity
that we need to make good decisions so this is hard to do but if you can and you can get the logs coming into a Raspberry Pi using bro and sericata here's a lat long the next flow I try to keep big words because I know these it can be hard to read but in that one next one is introducing the great this is train going up is it going down what is the speed that it's moving in we can plot this across time and as we do this we look at how to determine a behavioral model around this so did a train normally go 52 miles an hour up this grade or down that's great is there a
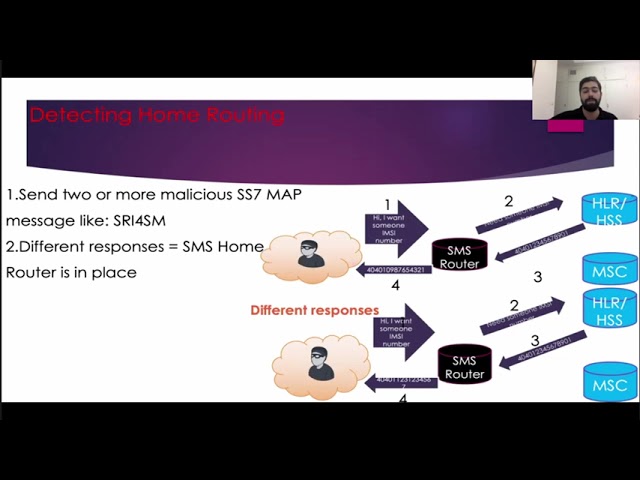
problem in the cabin that caused there to be a change did we lose consciousness consciousness of the engineer can PTC take control so you start getting some very interesting data when you start tearing down a protocol it's stuff you're not going to get out of sericata and you can't run a laptop with Wireshark in these environments all the time but it gets really interesting here's the brake interface here's a warning so we talked about new breed's for us talk about old ones before we get to the new ones when you're dealing with trains we're dealing with airplanes when you're dealing with cars still with canvas most of that traffic is still using protocols that were cutting-edge
25 years ago they're subject to replay attacks they're subject to you just tell netting in using web tech web tech or admin admin an unfortunate thing is that most trains can be driven with a lockpick kit and admin admin and if you can't use that just alter the GPS that's being fed to the PC PTC on the train and it'll be glad to do what you want that way in case you just don't want to pick locks so here's where I started solving this problem with Breyer that you can't really get out of that our IDs solutions D mp3 you're gonna be concerned with reset commands that they're coming from places that shouldn't be sending reset
comments if I jump onto network and I want to alter an environment or I want to stop a job where I want to make a change I can drop in pull the tape pull that traffic in plain text because dnp3 and Modbus both are an indie replay attacks or do resets or do any number of things so one thing we can do it bro and I'm sorry if this is a little hard to read they go ahead and define what you want to look for in there that would be suspicious to you such as a function code reset I'm really sorry about this I really am I tried to get the leanest bro script I could find so that you could
see it in this room and it may make sense and not be trivial but new attacks and what I started finding when doing with sericata and other things is that we are looking for a foul hash or looking for one piece of code that was in a Wireshark in a packet or we were looking for some single atomic indicator the problem is we're having to write signatures for every single thing that gets really that does the same thing 29,000 some odd individual roles in sericata is heavy it's heavy and snort too I mean I try to point this out if I can but the idea behind doing this what bro is that if you're using Empire if I'm using
Metasploit if I'm using any a number of things I use one our red team to get control of you know local admin and then escalate up I'm gonna want to get the hashes off the domain controller now pulling in CC or NC changes between two domain controllers is not a big deal that's normal behavior it's called replication it's been a new hotness since 1999 right for it came out but if you're a workstation that's not a DC and you're not and not list that's defined above as 192 168 0 2 then you're gonna want to know about this this may not fire sericata in fact it probably won't this is normal behavior there's nothing for it to tell you that there's wrong
with URIs in PowerShell PowerShell is generally allowed in every environment on every workstation so having the ability to contextualize what that DRS in C changed and that replication looks like to someone who isn't and a main controller is going to be valuable I didn't find an easy way to do this in sericata I found a very easy way to do this with bro no this is just looking for one indicator to contextualize this the only thing that's making a difference in here is that we've got a domain controller defined but we could do this differently like you can some start this yes I'm not really worried about doing one time I'm worried about doing nine times and or
let's say we're looking for a brute-forcing and I'm not so much worried about you know the nine ones that failed because I'm used to my networking getting skinned I'm used to the nine ones failing an attempt when succeeding so that's something you can write in bro scripting and you can run on a Raspberry Pi so that regardless of what that malware signature is regardless of where its from it doesn't matter if I'm using me me cats Kiwi Empire bro you know on and on and on you're still gonna see that behavior and you're still gonna be the fire on it so now it's a problem you know how to ingest probably transport data I've seen a lot of people in
networks push things over syslog and just send it to a narcissists lock host please stop doing this I know it's easy the problem with that though is I can see all the traffic in I try and an attacker can see all of your try all of your traffic - additionally in this kind of an aside but if you load a new device in and you move it from HTTP to HTTPS to make it more secure and you turn off telling it and you get a SSH make sure you turn off SNMP while you're at it most your vendors won't tell you that they left version 1 with the default private or public community strings that's kind of a bonus around sorry I
did this pen test last week and you know you know it was like hah man that's to say H an HTTP and man this company's really doing the right thing that's in the MP version one damn so you can do splint with sun certificates that's a super easy to do you can use log stash to bring the data back out if you want you can do ssro ssl curl direct to elasticsearch from bro which is a lot of fun and you can use Kafka no oh speaking of somebody at lunch today and they kind of kind of lifted an eyebrow you know I said you know I'm using Kafka on a Raspberry Pi I know this seems I'd be
strange to somebody to use Kafka every day but a problem that I had what beats Splunk and elastic and logstash was that they're heavy they're really heavy and if you start burning up the processor back hauling logs and you're going to reduce your ability to capture traffic and log that traffic at all so what a feeling that had to do in trains and I had doing other environments when I'm using PI is that there's a Kafka plugin from Apache metrion that works really really well with bra and you can tie some of your sericata traffic back to it as well you can send out in the environment lightweight over to a Kafka server and then you can kind of manage that data
any way that you want the biggest problem that you're having I'm gonna showcase this in a second is though Splunk is easy when you start tearing apart bro network packet logs this is heavy we're not looking for a single indicator we're gonna tear down everything from the Mac all the way up to the authentication so when you're capturing all that data and you're bringing back in a JSON city you can make good decisions with it that means it's very heavy and you're gonna blast ass punk ass punk license pretty fast so that's why we started looking at Cabana we started looking at ways to drive Kafka back in back hauling things over SSL and curl and these things worked
really well once you have it you can visit stuff out in more meaningful ways these are and should be when we verify because I can't see on that screen very well and I'm sure you can't either but most of this thing set for that bottom right-hand corner is all bro locks now I'm extracting protocols if I see a protocol that shouldn't be in my environment salmon on an entirely Windows environment or probably shouldn't see SSH so very simply by tearing down all these protocols we can see those things happening again carrying it further just on network logs and using like je3 we can tear down what software is that in that environment well as well just off network traffic
we're not worried about pulling from the endpoints we're not worried if someone remember to put that brand new shiny server into our asset management and connect the agent to it it doesn't matter when we're working with briar we can see the traffic there we can see the protocols that we're using additionally we're dealing with bro we have entity tables that get created so you know what you've seen before and you have good elements of what you haven't seen before so it's a nice effective way that when DevOps is shoving more machines in your environment and they're playing with live data instead of development data that you're gonna have the ability to pull that apart and see what's really
going on in your name in your network I know you're not gonna be able to see this you know this like slide deck fell one after another here it's okay what you can't see real well is that you can push those logs out and take everything from the size the length of the flow the size of the flow so if you're looking for persistent connections if I'm using me me cats or done persistence through Metasploit I'm probably gonna have a really long running flow here so using bro and using those things you can start picking apart that information for free and you can start looking at what's going on inside of it just make sure before you get started that you go
ahead and allow or basically you mute and hotmail outlook on Gmail those persist forever and they're really going to skew the the size of the other data in the session that you're being and bringing across but again that this is a highly modified but not too terribly a modified version of Kabana so you can pull this down use it at home completely free we've had to do some changes stars to ingest the amount of data that we're bringing in we are working with a huge social media vendor just just couple weeks ago and then they may not may or may not have been in the news lately but when you're ingesting many many gigs of
log data some of the things that you're that you're doing are gonna have to change so 10 gig links require some massaging say the least so lessons learned pies are finicky some of the OSS that are released for them are finicky a been too was working really well for us when we first started this up with trains then they released a version that drops snap into it and everything fell apart we did Cintas for awhile and that was working really well and then there are some changes came out with it and it fell apart who had a lot of success with raspbian we were using the older versions of older binaries of FAL B for
a while that were compiled and built for arm and a run on a PI the unfortunate thing is that they were abandoned so now once again we're increasing the attack service we have known buggy transport software that you can attack right on the wire and there's very little you can really do about that so that's when we started using spunk for a little while then we realized man this is going to kill us we have to do something different again the Apache metrion Kafka plugin works really well in raspy and Umbro the patching is super simple you can with with very few edits you can include that into your cpu into your landscape environments and
ever been to or you can manage a three shuttle but if you're doing about five or six hundred of these PI sensors at one time you really want to have the ability to pitch those patches without the issue log verbosity requires some real consideration here I kind of hit on this earlier but I want to pitch this across if you start playing in industrial controls you start messing around in trains and airplanes if you start occupying and taking up that whole line to get your logs back you're going to cause some operational problems and unfortunately some of those are going to cause some accidents so again bottom line don't das PTC so where am I
going from here what am I going to release in the future for everyone to use sandboxing for file extraction bro will do Fe life you determine what mime type you want you can have it pull that off of the wire drop it into a folder Kaku can pick it up for those familiar with cookies and boxing and you can blow that up and get the analytics I finally have automated an investment from pastebin and tor taking place right now which has been really exciting so what I mean by that is every 20 seconds I've got an engine that's going and scrubbing all the most recent pay so they're coming down in real time and in gluing
that data together with my logs in the enterprise so instead of me waiting for a point in time equifax tripled dark web cafe latte scan whatever the hell that means I can go ahead and get that in about twenty or thirty seconds almost all the data like he talked about in the last slide is going to end up in a former it's going to upon paceman for sale if you can get that information in 20 seconds you know you can fire an alert off of it it's going to save your hide waiting until something blows up to figure out if you can find those pace is not going to be very helpful more proto analyzers Megan verbose I think I have
three minutes left so I'm going to rush through the rest of this but the hard part is we have to do route determination if you're operating in a train we have to determine what route that the traffic's going to go so we can determine the verbosity that we can get from those logs without pushing something over I've solved most of this but this was not easy to solve because sometimes it's very hard to figure out what route something's going to go out once it passes accr the racks but still it's very helpful to still be able to get some of those logs even if you're on a 220 a grading OT is hard if you don't
believe it try upgrading 600 trains at one time and then you know so we want to make that easier and then the other is finding a more efficient way of transferring from there got networks one thing some people in my last 60 seconds my wife she put doubled its trash she brings me food and more dry erase boards Fred Wilmot from Splunk he's helped me out all the time Chris Robert to hack trains and planes with me my team Berkeley for giving up all the webcasts and lectures that they didn't know they're actually doing until someone pointed it out and then God cuz I'm here alright I think do I have time for a question or am I done
okay any questions yes
I don't remember exactly the amount of time but it was not very long I was having to do it daily at the lease and on trains we were still filling up we're still filling up the SD card that was on a PI I'll be glad to give it to you the integration is actually part of and you can actually get it before I have a chance to get online its built-in to Bro right now so if you download the most recent source code the Kafka plug-in is already there for you one more okay thank you very much I appreciate your time thank you