New Era in Telecom Hacking
Show original YouTube description
Show transcript [en]
all right here we are to conclude besides 2020. we've got ali abdullahi who's going to be presenting the new era of telecom hacking for us so thank you very much for closing this off i'm very excited as i mentioned to you telecom hacking is very uh near and dear to my heart when i was growing up i used to be doing some equipment without further ado i'm gonna get out of your way and let you do the presentation then we'll be back for closing remarks thank you hello thank you very much max and uh all attendees here uh i'm so happy to be here at besides toronto 2020 this year virtually and i hope you to see you soon
next year and uh welcome to my session new era and telecom hacking and uh in this session actually we're going to talk about uh the dark side of telecommunication and actually you may hear more and more about uh telecom insecurity and flaws uh inside the mobile network infrastructure and protocols however in this section we are going to talk about always and all possible techniques and methods to bypass security mechanisms and uh security features um were in place inside a mobile operator to reduce the insecurity and telecommunication and we are going to review all the security how we can detect those security mechanism and features and how we can bypass those uh security features and devices
uh anything else to perform other malicious uh scenarios and attacks so first of all i want to introduce myself i'm ali cyber security enthusiasts with over eight years of uh experience uh in variety of uh information security fields um author of some oracles and um an active instructor attacking nine magazine and uh absolutely uh an active bot hunter uh well known uh websites and firms and uh actually i'm a regular speaker and trainer at industrial conferences like besides uh defcon uh osp and so on so if you already can uh start at the main session and uh here we have some news regarding to telecom hacking and uh incidents during past several years and uh as you
can see here at the top top left corner you can see an incident uh pointing to some kind of injecting atm malware to attack bank and financial institution by exploiting ss7 protocol so as you know ss7 protocol is the most uh important vital part of telecommunication and mobile networking which provides uh capability of connectivity between national and international warming partners and uh however you may heard many vulnerabilities and security flaws on seven protocol which uh provide an attacker to perform many many uh attacks against both subscribers and network elements so in this case uh we can see that uh some attackers try to abuse ss7 protocol to attack banking accounts and financial sectors and on behalf of uh this uh news
we can see other news like a cyber attack and incidents against uh uk's metro bank and uh again in this scenario uh hackers try to uh still credential of uh information credential of uh actually account informations and uh other for more important information from the account holders by using ss7 protocol because uh the attacker by using this uh vulnerabilities inside ss7 protocol stack uh can steal um two-factor authentication for example and still your two factor passwords and anything related to that account and uh it is a way to hijack your banking account or any other account that you are using to factor authentication based on sms so and uh other news pointing to that uh
uh actually um requirements are fixing ss7 vulnerabilities inside the united states to bring more secure mobile infrastructure and this is one of the important uh imp factor when we are talking about telecommunication because uh many students and uh experts asking me that if um using 5g or beyond technologies uh is it possible to perform any kind of malicious scenarios or attacking on mobile subscribers or network elements and i'm answering that this is it is possible so because whenever we are talking about 5g technologies uh we are talking about ip backbone infrastructure we are talking about ip which is a well-known protocol to all hackers all around the world and whenever we are talking about 5g and
beyond we are talking about software defined networking we are talking about network function virtualized devices and segments inside the core networks of our uh telecom provider and these technologies these segments open new doors to hackers to perform malicious scenarios more attacks against subscribers and network nodes inside our core network and uh also we have another topic and that is when we are uh providing 5g services to our subscribers or lte or even 6g to our subscribers actually uh whenever a traditional mobile phone which is working in gsm or 3g can work inside our territory or inside our network so all these ss7 vulnerabilities and the possible tags are still present inside our 5d networks and this
is uh one of the uh impact bad impact on new technologies because whenever we want to migrate to new technology like lt address like 5g or even 6g we must uh actually restrict uh the subscriber who want to get traditional services like gsm or 3g so uh that's it and the final news uh pointing to users won't be able to it via sms and this is very important that twitter disabled tweeting using sms because uh one of the most used usage of sf7 vulnerabilities is sms spoofing and sms interception so an attacker can intercept your tweet uh whenever you are using uh sms services to tweet um on twitter or even an attacker could uh actually spoof
uh an sms on behalf of you as a weak theme and uh to eat whatever he wants or she wants so this is very very dangerous and uh in this good news uh teacher disabled this feature recently so here uh we have all possible attacks uh the first one is subscriber data leakage um an attacker always looking for a weak team if he or she didn't target anyone or even a hacker will try to set up a wide range of active subscribers to perform malicious scenarios by abusing uh telecom protocol stacks and features so in this case uh one of the most uh valuable information and value in telecommunication uh is imsi or emc number
emc number is a unique value uh for each subscriber all around the world so each of you has right now has a unique number called emzy uh which is unique to you and uh it's some kind and somehow um identifier when we are going to talk or sending sms or even activating uh our mobile phone inside um new uh territory or as a roaming uh subscriber so emc number is very very important because it is uh unique for you all around the world uh whenever an attacker receive your emc number so uh the attacker can set up a further exploitation and malicious scenarios so the second one is network data leakage which pointing to uh internal
information like uh global titles which uh is something uh like ip address in telecommunication gt's is something like ip address uh of each telecom or mobile network infrastructure elements and uh other uh network data would be for example ssn um or uh actually some internal ip addresses etc uh so from an attacker perspective uh it is very important to actually extract network data like a network data like gt numbers like uh ssn numbers like uh internal ip addresses and so the third item is um invasion of privacy or location tracking which is very important to all uh vendors and uh mobile service opera operator because uh uh attackers and intruders could using ss7 protocol inside
telecommunication infrastructure to retrieve your uh cell location identifiers and any other information related to your location like uh mobile country code mobile network code and uh cell id and the location area code and to actually locating your uh locating you and also they can locating you whenever you are going to go in in each country they can locate thank you by using uh cid or cell id or location area code and mobile accounts record mcc and mnc mobile network code so location tracking is the other actually possible attacks which is very very dangerous only subscribers you know the next one is sniffing uh which is possible for both voice and sms and an attacker can take advantage from the
vulnerabilities inside telecommunication infrastructure to sniff your voice data or even redirect your voice data to any other place and um as i told you before sniff and intercept your sms message and an attacker can read all those texts and sms that you sensed before the next one is spoofing uh it is the same as sn spoofing is uh same as sniffing and it is possible for both voice and uh actually sms text message because uh an attacker can spoof your phone number or even a spoof any other phone number to call you uh like 119 or even 000 or any other uh character that he wants and also by um using this kind of vulnerabilities
an attacker can send you uh sms uh from any uh mobile uh phone number and this is very very important because uh attackers uh can take advantage from this vulnerability to perform fishing scenarios and the last one is fraud tax and by up using uh those vulnerabilities inside uh telecom infrastructure and ss7 protocol attackers can perform fraud scenarios for example by exploiting uss infrastructure and any other uh techniques and methods like uh force uh victims to uh actually click or tap on a phishing sms or any other similar malicious scenarios so as you can see here uh this is the whole mobile network architecture and as you can see we have uh the first section we have bts
node b and enodb which uh indicating uh all three uh primary uh mobile architecture 2g gsm 3g and 4g lte um cell tower in 2g called bts or base station base transition station and node b in 3g and e node b in 4g and as you can see here we have a telephony network which indicating um circuit switch network uh with handling old calls and sms and everything related to those procedures and a cloud which indicating internet uh which handling or data and internet data that we are going to use so we have two main area here uh circuit sewage uh including mobile switching center or msc and uh sgs nmg gsn in packet switch which is responsible for
our uh internet data traffic and in at the bottom of the page you can see the whole uh epc which is the lte or 4g core net fork including all those cs and ps elements centralized we have mme uh which handling all mobility management uh procedures and serving gateway and pgw acting is like as ggs and in traditional uh mobile network architecture so here we have a whole architecture of 5g which is a little similar to lte however we have gnb as our base station and we have other function like policy control function or pcf we have a authentication server function or unified data function here but um consider that the main uh actually the main topics in 5g is using
software defined networking and nfv technologies and as i told you before 5g is not more secure than lt or 2g or 3g because attacking and app using 2g 3g and 4g networks need a knowledge of a complex uh mobile telephony networks which indicate that both circuit suiting and packet switching and radio access network as the most accessible sub network of each [Music] mobile network architecture and however in 5g we have more ip function ip based function we have uh many many um network nodes and elements which access a bill using ip addresses ipv4 and ipv6 and uh software defined networking core elements needs a centralized controller to control all those uh elements inside our 5g network and
these uh topics open new doors to hackers because uh this network 5g and beyond will open new doors to them by using ip address and ip sorry ip infrastructure and the sdn and nfv technologies because they know uh ip procedures ip backbone how they can scan perform massive scan against uh ip infrastructure and also they can perform uh as many as they can uh exploitation and attacking scenarios against uh management uh web application for management managing these uh sdn and uh nfv uh and network elements inside 5g core networks so here we have three main hacking scenarios have three separated uh segments mobile radio access network or ran signaling network as i told you like cs
circuit switch network and data network which is handling or uh internet's traffic and uh in the first segment the attacker will perform all those attack from a radio field which is uh the most accessible segment here uh right here we are in a radio access network because uh our phone is contacting uh by mobile station and the signaling network responsible for our voice and this is the vital part of our scenarios for both detection and bypassing and the data network in data network attacker start attacking from the internet and internal signaling points so radio security in uh radio access network segments we have three main uh security features and mechanism the first one is a mobile
device registration using imei which is a unique id like mc number for our hardware so each uh mobile hardware has its unique imei value so the second one is using ciphering algorithm to avoid interception and man in the middle and the third one is using advanced mobile technologies like lte advance etc so here's a radio access network architecture as you can see uh this uh this is a radio access network of uh lte network which called eu tran or evolve your trend uh we have uh some you know to be here you know these here and they are uh connecting to mme and sgw inside our core network and they are also connected to each other using x2
interfaces and also they are connected to uh cs and actually uh epc or lte core network using s1 interfaces so it's straightforward and simple so why mobile operators and law enforcement using mobile device registration using imei or or imei restriction because the first one is uh mobile phone uh smuggling countermeasure in many countries uh there are a large number of uh mobile phone um which they are not uh imported legally inside the country so using imei's restriction they can control phone smuggling the second one is monitoring suspicious activities and also it's similar to tracking criminal actors uh by having imei of a specific hardware uh police or lawful interception uh can they can uh track a hardware or stolen hardware or
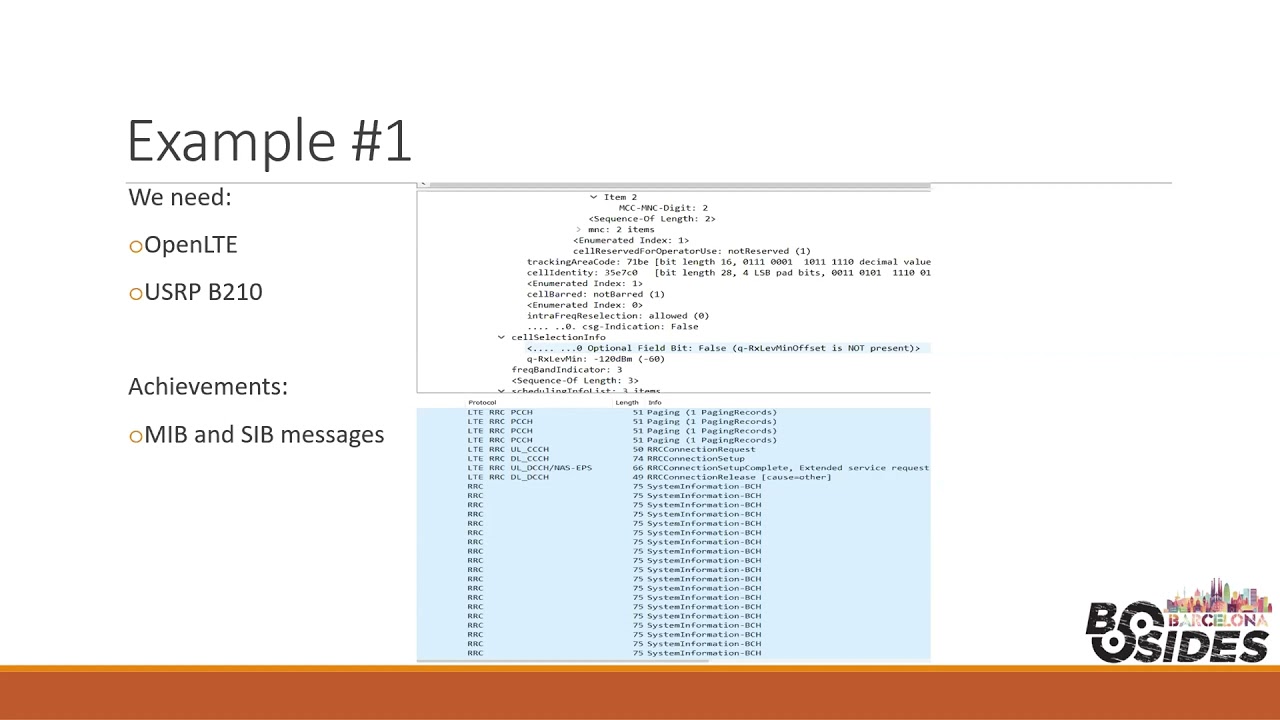
stellar devices locating criminal actors and monitoring suspicious activities to avoid any further incidents so in this section uh we are going to bypass uh imei policy and restrictions so uh actually to perform this uh bypassing methods we need um osmocambie software and also we need a motorola c118 cd118 and c115 well to perform uh this bypassed uh technique and by uh using uh osmocom and uh motorola uh mobile phone we can change uh valid valid imei to invalid or even uh fake imei and also we can set up a call and test next network behavior to or check all those parameters and even our changing imei is working well or not as you can see uh
in this wireshark screenshot uh the network actually the cell tower uh sent a identity request to my phone which is uh motorola and i'm using osmocon bb as i mentioned in previous slide and the type of identity is set to imei and in this slide you can see i replied to the network with an invalid mei set to all zero so uh be careful that also an attacker can set imei to an event to a valid imei which is uh used previously by an active user or a subscriber inside uh radioaccess network so in this case we just uh and only tests uh invalid imei so you can also test uh whenever you want to test if
your radio access network or telecom provider can respond then accept uh using a fake imei or spoofed imei so at the final stage as you can see ciphering mode completed and my invalid imei accepted from network side and after that i can communicate actually my user equipment my mobile phone can communicate with the cell tower and i can make a call or send sms so the next one is using ciphering keys to avoid interception or man in the middle so we have some uh kind of ciphering algorithms like kc race and random mobile operators and vendors using them to avoid active or passive sniffing inside radioaccess network and those ciphering algorithms uh stored in hlr hss which is a database
of all subscribers inside circuit switch core network so to bypass this uh security mechanism actually uh we are going to choose a different attack vector so in this case we are not going to perform an attack from radioaccess network uh because it is very uh expensive and uh it's not very good choice to start your attack from radio radioaccess network we selected a circuit switch network to start our attack and we targeted authentication center which is a vital component inside hlr hss and those algorithms stored in auc inside hlr hss hlr is that database in 2g and hss it's a different name but the functionality is the same in 3g lte and beyond so to perform this uh bypassing method
uh we will uh start or uh attacking from the signaling network ss7 network and uh we you we are going to abuse send authentication info which is a normal ss7 map or mobile application part message and by sending this message to hlr hs test of any mobile operator we can retrieve as you can see in this screenshot random number stress and kc in clear text and those parameters um representing uh ciphering algorithm of a specific victim or subscriber so as you can see we have all those algorithms in clear text
the third item was using advanced mobile technologies um mobile operators usually use advanced technologies like lte advanced like 5g like uh nb iot or or any other technologies like voiceover lte uh to have uh highest quality and performance uh to have a more secure channel more secure technologies and actually you can see they're hard to gain access from radio segment or in this case eu training lte network and to bypass uh advanced mobile technologies whenever we're dealing with uh for example a mobile operator as our victim or even a penetration testing project and to bypass it we can downgrade all subscribers in a specific area of a test to older and traditional technologies by jamming all those active signals
as you can see here and we can see the attacker here in this example downgrade all subscribers and victims in a specific area to older technology using a signal jammer so there are many uh commercial signal jammer uh on the internet you can see um many models of signal jammer into g3g4g or even there you can put the signal jammer in your pocket or even we have bigger signal jammers so they're uh there are variety of signal jammers and even you can also uh build your own signal jammer using open lt and open bts by using software defined radio uh tools like usrp or blade rf or hack rf so the other uh bypassing methods is stay
taking advantage of rand sharing feature in many uh regions all around the world uh many mobile operators exist and they are using other mobile operator infrastructure radio infrastructure uh they are using uh other mobile operator cell towers because they are a smaller company there may be uh mvnos um or maybe they have less customers so it's not uh fair enough to set up many basis stations and sites uh all around a whole region so they will take advantage of uh those cell towers and they will establish a rant sharing so whenever a mobile operator using rand sharing feature you can take advantage from this feature and whenever you find a vulnerability inside the that specific area you can also
attack and trigger your malicious scenario against other mobile operator that they are using that uh specific cell tower in that radio access network so also there is another bypass uh particularly on volte or over lte which is uh released recently and it will exploit a volte call by uh recovering the content of encrypted watercolor and the attacker can intercept and uh actually uh decrypt all those contents inside a secure channel of volte when you're talking with your friends uh based on walter technology so if you want to learn more about this attack you can check this website for more information so now we are going to have more talk and details about coordinate for security which is
very hot for us and there are two main uh security features and uh hardening maybe the first one is enabling home routine feature inside mobile core network and the second one is using signaling firewalls okay so home routing what is home routine actually home routine acting as a proxy inside uh telco uh infrastructure and uh mobile operators and telecom service providers using home routine because they want to hide their real subscriber information and maybe networking information from attackers as you can see and also i talked about mc number and uh internally network information before and uh home router or sms home router risk will respond with random or fake numbers for example fake value and it will hide in signaling coin
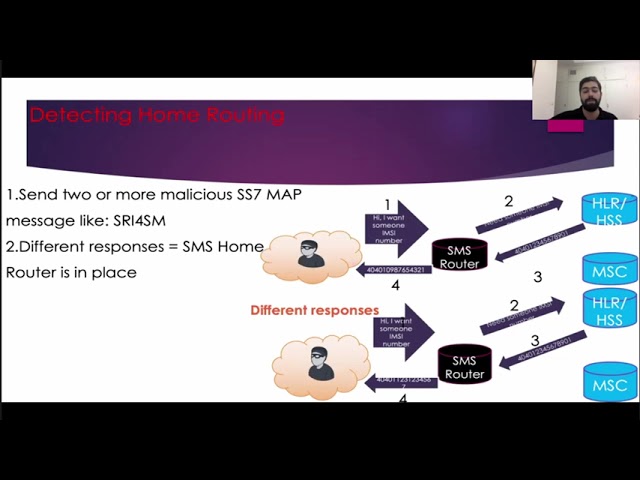
formation as you can see in this specific uh scenario attacker tried to uh retrieve subscriber mc number and uh actually hlr hss or even uh specific core elements uh respond with the real mc number but uh sms from rotor uh respond with a fake number so it is not real so uh as a result the attack cannot perform any further exploitation against that mc number because it is not a valid one okay first of all to perform bypassing against this uh feature is to detect or whenever a home rotor is in place or not so detecting home routing is very important and it is started forward because we need just to send uh two or more malicious ss7 map message
like sri or sri for sm and whenever we receive different responses so it means that a home rotor or something else is in place as you can see the attacker received two different responses as a inc of a specific victim or subscriber okay now we detected that the home router or samsung routing feature is enabled and now we are going to bypass it so first thing is that we have three types of gt or global title that i mentioned before the first one is msisdn or e.164 which consists of mobile country code or mcc uh network destination called an sn and nc number as i told you consists of mobile country code mobile network code and sin
or msin which is the unique number of uh your sim card or using and the third one is mgtg or e 214 uh consists of uh mcc and dc and msin so to perform this bypassing technique uh we will use ngt um while we are guessing a random mz located in the targeted hlr hss and also if you don't know any emc or you cannot guess any mc because you know if you for example for one example that i can explain uh this situation to you uh for example if you want to perform this attack uh you may buy uh three or four or maybe more sim cards mobile sim cards of your targeted uh mobile network operator
and you will check it out uh what uh emc number you receive and you can also uh actually guess a random mc number or even if you cannot buy any uh sim card uh you can uh actually perform brute force attack or dictionary attack or something like that uh so uh it is simple to guess a random valid mz number which is located inside uh the core network so by having this uh valley dmz located in uh the core network and using mgt the attacker will lure and trick sms home router here and receive the actual uh emc number and also other information like mobile switching center address or gt numbers and ssn number any other internal
information so signaling fireball uh the next uh security feature mechanism is signaling fireball signaling firewalls are as same as uh layer seven and layer three firewalls uh we're using inside our network or even uh perform or even use uh web application firewall to protect our web-based assets and properties and uh this is kind of signaling firewall designed to protect our signaling infrastructure and properties and they will inspect signaling messages and they can perform white list or blacklist uh actually rules and also they can filter all signaling messages based on uh best practices or uh predefined rules or anything like that as you can see it is very simple an attacker sent a malicious sf7 message
to the core network and a signaling firewall here blocked his or her request so now we are going to bypass uh the signaling firewall however we need to learn something about tcap because uh we are going to playing with tcap which is a ss7 sub protocol it is similar uh to tcp and uh tcap enables um signaling elements and core networks to have a connectivity based on sccp protocols and as you can see here in wireshark screenshots uh tcap uh we have a tcap begin and keycap end and which is indicated used by a transaction id here an oid here and a dialog request and components so to bypass signaling firewall we need to removing application context
name or acn from tcap and the second technique uh is sending double operation message um toward core network so the first one we are going to remove acn from tcap and as you can see to perform uh this removing procedure we need to remove dialog request as i uh show you before in tcap section and whenever we remove dialog requests second from malicious ss7 message there there will be no acn or application context name to address to malicious map message so whenever dialog request is present acn application context name will be addressed to the specific malicious map message and by removing dialer request there is no acn or application context name to address the our uh ss7 map message which is
malicious because we need to send that message to receive our uh information from the core network so as you can see attacker the attacker here uh send a normal ss7 message without dialog request plus a malicious message because there will be no acn to address to that uh malicious message and signaling firewall will act as a policy uh segment here um probably it's going to police the request and there is no sign of malicious map message because there is nothing to address to that uh specific message and uh the request was uh received by the core network elements and it responds with a normal message response with malicious message response so the attacker have two responses
including normal message response and a malicious message response so the second method is uh using double operation message so most of signaling firewalls uh decide then the block or drop the request based on uh ss7 message type which uh indicates by 3gpp and you can find many information on the internet uh by search 3gpp uh malicious ss7 web message categories uh each ss7 message has an operation code as you can see here in this uh picture uh there is a op code or local value which indicate sri4sm or send routing info for sm which has operation code 45 and you can see the upcode number here is very very important because whenever you want to trigger a malicious
message or even normal message each message has its own operation code or opcode so right now we are going to have use uh this op code and to bypass signaling firewalls so uh actually here as you can see the attacker will use uh acn address and a legitimate ss7 message and embellishes ss7 message and we have acn here and it will address the malicious uh operation code and in second stage uh the attacker put a legitimate s7 message up code first because we have acn to address to the next message uh which is right now which is a legitimate one and after that the attacker puts a malicious ss7 message signaling fireball will check the first
operation which is legitimate so as you can see acn will will point to the ss7 map message which has opcode which has an up code and it is legitimate so signaling firewall decide based on the first section of the whole request however there are uh two requests with one up code which is legitimate and after that uh the request received by uh hlr hss or maybe any other core network elements however the elements cannot understand uh what's going on here because it is receiving two messages with one op code so uh to respond to that request it needs to have two messages with two op codes however in this scenario in this particular scenario uh we have two messages
with one up code so it requests to send the message this request again and this is what the attacker actually wants because the whole session right now is clear for the signaling firewall and the session the signaling firewall will keep the session uh until the attacker uh send the request again and in this case the attacker will only send the malicious ss7 message to the coordinate for and the core network will respond to the malicious map message with subscriber mc number network information location area code and cell id or any other responses and information that the attacker wants to have uh right right now so in this scenario right now the signaling firewall bypassed and the attacker
has a clear and legitimate session so uh some highlights uh from the this session and talk so as i uh in my previous slides uh mentioned that the most mobile the most of uh mobile operators all around the world uh enable security features they are putting some security devices like signaling firewalls and and any other uh solutions to defeat these kind of vulnerabilities and fighting against uh actually uh ss7 vulnerabilities and security flaws inside mobile code networks and even uh telecom infrastructures and uh in this uh second we talked about the all possible ways to detect them bypass security or not i told you
further exploitation and uh as i told you before uh using 5g technology is not fair enough it's 5g is not more secure than uh the older and traditional technologies they 5g will open new doors to hackers and intruders all around the world because they are fully familiar with ip backbone and ip infrastructure and uh sdn and nfv uh elements so the next item is uh some advice from my site uh from my standpoints uh network hardening uh and putting security devices not fair enough and is they are not a good choice only hardening and putting some security solutions you need to have a periodic uh security assessment against your telecom infrastructure on all uh sub networks and segments
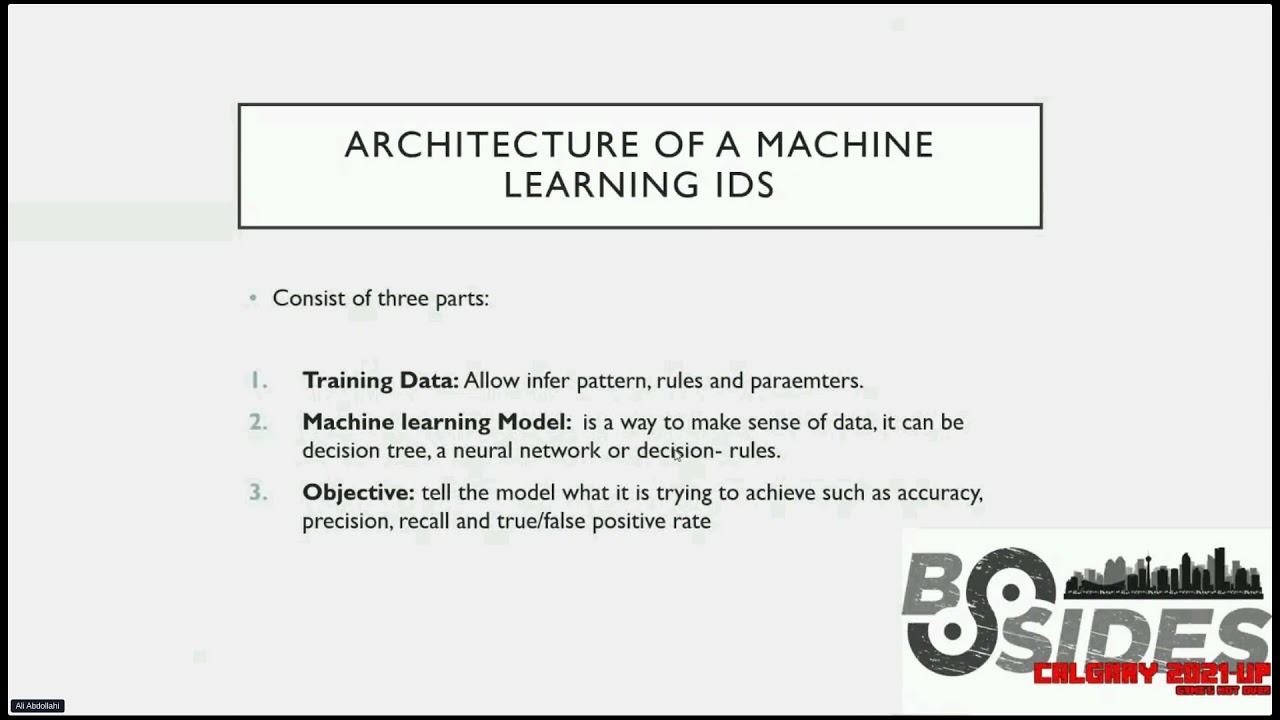
radio access network circuits through cs network and packet switch network uh from uh different points of view from enrollment points of view from the national warm airports of your international points of view and uh also you need the behavior analysis and continuous monitoring like a telecom security operations center or tsock to analyze and all behaviors and monitoring all uh connections and requests requests from uh the telecom partners and mobile partners to have a big picture of everything happening inside your network so these are uh some advice from my side because uh it's not uh only enough you can also set up as a signaling fireball or any kind of intrusion detection system based on telecommunication protocols
uh whenever you are dealing with uh t-stock or some kind of behave monitoring and behavior analysis of uh vulnerabilities and uh security flaws inside telecommunication and a periodic penetration testing against signaling points and ss7 networks and uh also performing red teaming will be a very good uh choice so uh thank you for your attention guys and uh i hope uh to see you soon and if you have any concern or any questions i'm here to answer your question and also you can be in touch with me on twitter linkedin thank you so much hope to see you soon stay safe wonderful thank you ellie um there was one question that came in just wondering if we can
um quickly cover that and that's why can't uh modern phones be used for imei uh spoofing
uh yeah uh
i think there is not a specific question from and uh so yeah you know uh actually whenever we are uh dealing with new phones and traditional phones whenever you uh can turn on your traditional phone inside the a network a mobile network so this is a warning this is a warning because uh it means that the 2g 3g or even 4g whenever we are talking about 5g or 60 and beyond and uh will be still present and those vulnerabilities still present vulnerability ss7 vulnerability is still present uh and also this is just only about the circuit switch and signaling core network uh also we have radio access network and also we have ps or uh packet switch network uh which is
very accessible because uh from the internet side an attacker could scan all those router and see packet switch elements to find uh which devices has gtna build and gtp enable sorry and set up further exploitation and scenarios and uh especially that motorola phones that here it's the c115 or one one sorry one one five this is motorola c115 and c118 you can also buy these kind of motorolas from ebay or amazon or anywhere else okay great thank you very much for uh for doing the last presentation of the day we're going to uh let you go and wrap up so thanks