COSMICENERGY: The Renaissance Of Threats To Operational Technology - Daniel Kapellmann Zafra

Show transcript [en]
going to be unhappy um hello everyone thanks for being here very glad to talk to you uh today I'm going to bring a topic I'm particular passionate about uh it's I don't know are you is anyone here particularly into OT security I think there is 1% there at least two people okay then ah three people so it's going to be even more interesting because it's is going to be something fairly fairly new for for those that haven't heard a ton about the topic and basically this dog is is meant to present sort of the evolution of the field based on one of our most recent findings um well actually the most recent finding of Tim
malware I'll get a bit more into why that's relevant but first of all to clarify um has anyone seen this image ever this painting it's great because it's not famous it's just AI generated I I just thought that it would be very funny to generate something Renaissance style but like industrial for for the OT um and basically the reason why I bring this and and it goes that aligned with the the title of the of the of the conversation is because that is precisely what we have seen in the field of OT something like a Renaissance uh normally when we think of Renaissance we go back to paintings we go something more historical but actually in general
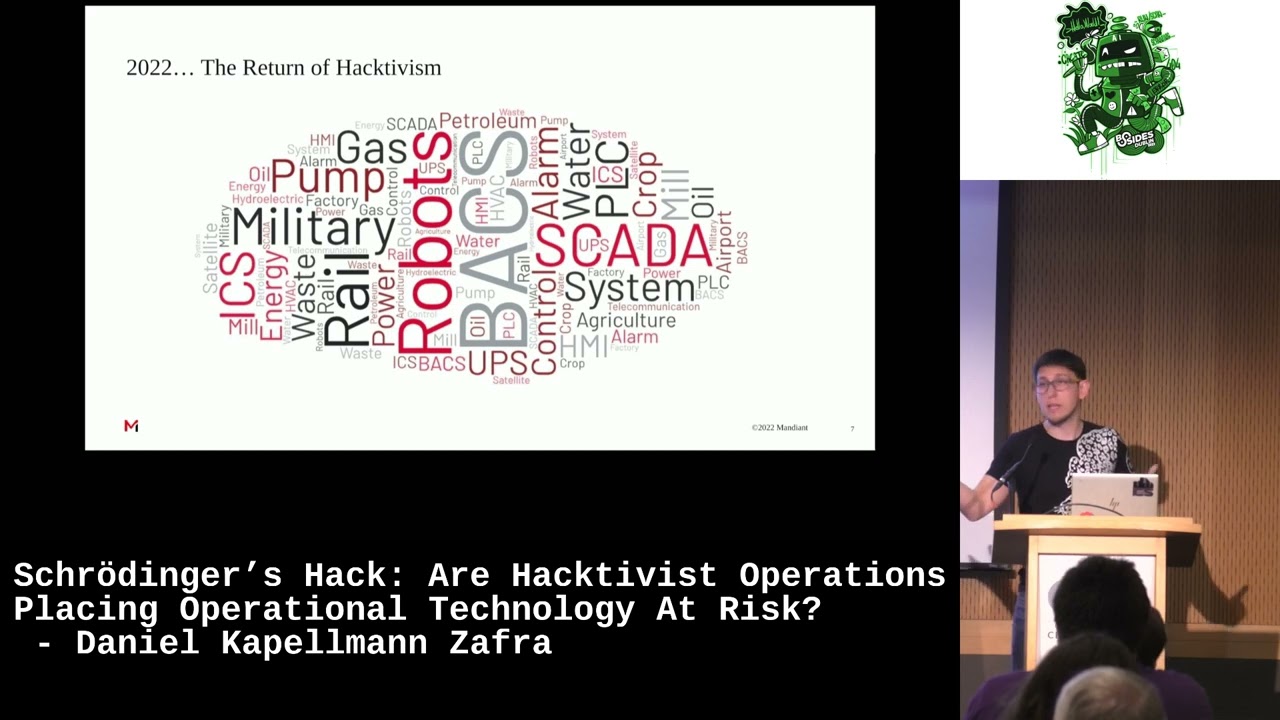
it can refer to any type of uh period of time when there is some Innovation something different is is happening a paradigm is broken and that is particularly what we have seen in the OT security field for last two years to get everyone in line before getting into explaining more of this uh what do I mean by OT industrial Control Systems operational technology some people know it as scada but all of those have different um different nuances but I'm just going to refer to it as OT um and basically refers to any type of of computing devices that interact with engineering devices so you can have a physical process running so it's going to refer to anything about production of
energy water factories what not uh the intersection let's say with the physical world and yeah so you're going to see very different devices you're going to be very different um very different equipment very different software a ton of different things and and you'll be able to see a bit of that those that already know it just please bear with me I'm sorry just wanted to get everyone on the same line so now I get a bit to the meat like finally okay yeah too much introduction let's just uh start describing a bit of of the field so do you understand why this is so new and so relevant in the field of OT security we have only been
investigating things let's say for around slightly over 10 years so the first thing that happened with stet 2010 most of you have heard about it attack against Iranian um nuclear centrifuges uh basically when that happened researcher started figuring out there was something going on governments picked up on it as well unfortunately and then we had a period of development for like 6 years when there was some some instances we see some research we see some minor attacks um it starts becoming a thing it starts becoming a field but but really it doesn't really pick up like there's not so much activity that that that you can identify then between 2016 2017 we see two big
attacks two large attacks in Destroyer is something in Ukraine turn of the power uh around Christmas time very very unfortunate and then 2017 Triton big attack uh again it's basically malware extremely specialized uh an attack that lasts four years specifically for a very um specific type of device uh from from um electric the that basically is what what's called a safety instrumented system that is the last line of defense when when when you can say okay there is an intentionality to generate something physical gladly it was identified and nothing ever happened probably it wasn't even the intention but but the test was covered and and you know like that that's how it became something public after that couple years we're us
we we saw more like on the ransomware compromise we saw actors poking OT devices industrial controllers around an internet trying to figure out what it is very low impact uh but ransomware has impact on production but not really from an OT perspective from a physical perspective um and then something happened and we all know probably what happened 2022 that has brought a ton of development in in in this type of unfortunate field basically the com the invasion in Ukraine begun right with the events happening in Ukraine we started seeing an optic basically whereas before we were looking for information we were looking for attacks we're looking for data all of a sudden the data starts
coming to us and then well I mean it's happy time for the team researching interesting things but it's also very unfortunate time when we see that there is this int intentionality and this development is is is actually becoming something where we're basically using this type of malware that is going to impact the physical world that is becoming more simple that is becoming more available more affordable let's say and we start seeing all of these different cases Unfortunately today I won't talk to 2022 but if you're curious in controller and Destroyer 2 are extremely interesting we have put out blogs for both of those uh let me know and I'm glad to chat more about that but
right now I'm going to focus particularly on what happened on 20 particularly cosmic energy and then I will put the other the other events a bit in in context so cosmic energy okay first of all that's that's a name that we picked up it was just based on some of the strengths that we're in there I don't know if anyone here is from France or any French speaking location but actually there there's apparently a meme that talks about cosmic energy so I've heard a couple jokes about that it wasn't planned I promise um but yeah so Cosmic ener how did we run into this specific piece of malware as as you can tell in the
timeline before we've only seen like seven eight pieces of Mal that that fall under this category uh so you can tell it's something very unique and normally we only find it once there is an actual an actual event an actual attack but this time actually one of our threat Hunters was just looking for some very specific technique that I'm going to discuss later and he just happened to run into this uploaded into a public um malware analysis utility uh it was up uploaded from a specific location in Russia nothing to say you know it could be different but that's that's just like like the the metadata that it contained and he just realized that this sample
seem to do something interesting it contained a specific protocol that is called IEC 104 that is commonly used particularly for energy distribution and transmission and basically from there he began the investigation so what is cosmic energy cosmic energy is this uh piece of Mal particularly for operational technology uh the let's say disruption of energy um transmission and distribution um particularly as I mentioned IC 104 what it does is basically it's from a nature of an attack it's not extremely complex it basically just allow the attacker to get access to you're going to see in a second but get get access to to the to the Target environment and from there interact with a remote terminal unit a specific device that
allows you to control field engineering devices and basically it communicates with this specific protocol um that you know it has different um considerations for how to interact with it but I'm I'm going to get more a bit in depth into that and what's very interesting about this is that even though like like this m has capability similar to other other type of Tim modware that it's basically fairly usable in that sense the interesting thing in here is that it's we believe it's a red team Tool uh I'll explain a bit more why we believe that and still what are the implications so that you can choose whether that makes it more relevant or less relevant so cosmic energy this is based
on the Reconstruction of of the malware once we pick it up we try to run it we start figuring out how it looks like and basically this is the image that we put on how what what the actor wanted the process to look like it basically contains two different pieces the first piece pyop uh BAS basically it's going to it's going to Target an MSS SQL server and it's just going to go and try to get access so that then from there it can deploy light work lightw work is the one that's going to have encoded the communications with rtu so it's going to have for example I mean like yeah the the IP address it's going to have the
protocol it's going to use and it's going to have a list of um what we call IAS basically a specific type of of data embedded in the io 104 protocol that allows you to communicate with this remote ter terminal units and what it's going to do is it's going to tell that that rtu that then communicates with these field devices that that basically turn on and off the power it's going to tell it to go turn on turn off or basically change the the the situation for for circuits and Breakers and then after that the m is basically going to erase itself and try to avoid the the target from knowing that something happens that modify these
parameters um in summary I know that I mean like it can tell a lot of what the malware can do but besides from the malware the big idea that you can get from something like cosmic energy is that what it can do is basically turn off the power um turn off your light that sounds very easy though right I mean it it's if you can just drop a piece of malware and turn off the lights then you know probably it would have happened many more times and it has only happened a couple times at least you know well well known and documented and this is because there there there is a bit more difficulty into that like even
though the malare has that capability it can make those changes of course from an engineering perspective you do have other types of of um of logs different types of types of of of um counter measures but also one interesting thing here is that for the actor to to be able to deploy one of these tools most often they actually need to do some prior reconnaissance they need to know what are the different parameters internally they need to know where the asset is they need to know the information of the asset they need to know what ports you're using they need to know often times even the models in this case it's more model agnostic but in other Tim
malware it wants very specific models and particularly here the most interesting part is in the end the ASU type whatever um because basically what it what it does is the fact that it interacts with this protocol makes it special and the fact that it had already encoded some some specific messages that can be developed by an engineer almost arbitr contrarily like basically some of the parameters in ic 104 that that use this well that you use for communicating with these type of devices are are set up by the vendor or by the engineer or by the plant or by a convention so it's some type of information that you can't just go and Google it around but
actually you know you need to have information on the victim um so yeah this is this something very interesting if you're curious actually you can go on Haun in your favorite uh malware utility whatever for cosmic energy uh you probably will be able to pick up some of the uh of the indicators from from from the blog and basically you can find this and reproduce this this traffic but there is a quick detail that I was missing and it's the fact that the sample wasn't actually just running so we believe it was still in development uh or someone was testing it that that's that's how it got into this utility it actually got like in late 2021 for for
whichever reason we just happen to find it later in the year and basically the trick in here is that when you run it it had a couple issues where sometimes a mod would erase itself before it runs or would try to to call for functions that weren't yet compiled so yeah I mean like it wasn't particularly functioning yet but we also realized that it was very easy to fix uh one of our researchers really with a couple lines of code was pretty much able to to get it running so still something to worry about so now the point and this is where this is my favorite part of the investigation because even though the malware is
already fairly interesting I just love the part where you just like start finding the small pieces and particularly we believe it was a red red teaming tool um and this is this is basically the reason once again I just just because these images are amazing has anyone seen one of this or knows what this is well this is this is not AI generated this is just someone generated for fun apparently but this is how they believed someone in some random repl for images that a solar poly one would look like which again I'm not even going to ask cuz if I ask anyone knows what a solar polygon is most likely the answer is no
because it's not really a term that is actually fairly used I was looking around and apparently it's something like solar irradiation and the volume and whatever but it's just been proposed so it's not even a formal term and that is why this this became so interesting the point is we found this specifically in the Cod that was called for this library from solar polygon and it just sounded something interesting so when looking what it actually was we realized it was fairly specific didn't really make a lot of sense um and then we started looking and we were actually about to publish the the paper just saying you know this is a tool that could be used or not when we run into
something very interesting apparently polygon which I didn't know uh probably some someone here is is actually more familiar with that also refers at least in some some contexts also to kind of like test ranges um ironically a couple days ago I saw that apparently where the policemen go and shoot some called polygon so it makes sense um and basically yeah so after looking for solar polygon we started looking with different characters um and basically eventually looking into realic we run into the Ross Telecom solar polygon and we started looking more into this around the dates around everything and apparently it seems to be cyber security company um well it's a uh to iations provider that acquired solar and then it
became R Ros Telecom solar and then from there they created a polygon under the sponsorship of the Russian Ministry of Defense they received a ton of money they said we're going to do this test range and then they've been conducting exercises some of those exercises when we started looking into it said that they tried to produce disruption of energy in a like specific fictious City and that's why we believe in the end that this was basically one of those tools used for that um another thing to to highlight is it is definitely possible that we're wrong I mean yeah like maybe there was something else that happens to be sort of polygon that that matches for some
random reason uh we don't believe that's the case based on like like all the context we have um and also based on placing this in in context this timeline that you see in here you're going to realize probably that it's very similar to the first one even though it's a bit more detail some but it's very similar and the point is that most of the high profile attacks and events that have happened in OT have been related to uh Russian um sponsored attacks basically Russian sponsored groups particularly um so it's it's not really a secret there there is like like some development going in there and particularly I bring attention here to industro one and
industro two two of those highest profile attacks both of which match in a great degree what we saw in cosmic energy particularly how does it match we have here a couple of of details first of all both cosmic energy and the IND destroyers both of them uh developed are developed basically for to Target electricity transmission and and distribution both of them follow the same approach of communicating via I 104 and then turning on and off and basically that that kind of like simple process um it's it's it's basically the same that they were doing just a bit more complex in the in in the prior cases and then both at least indust first and and cosmic energy both of them
communicated most likely with the MSS SQL servers and from there reach out to the rtu so this is kind of like something interesting as if you're on the side of the user something you should probably look into and then one final small reference o ik that it just happens to be in the code for for both both cases it is very specific software for OT that it it's it's not um common enough to believe that it was there by con ents and we found it in both pieces of M there can be multiple explanations it could be the same people doing it it could be learning from the same it could be that they got the samples you know
who knows uh but particularly in the story version one samples are difficult to get so I would say that you know there's some probability at least that that there is some overlap um in there so now I mentioned there was a tool oh oh okay there was a tool that was very complicated uh well this is very interesting from OT perspective everything you can do then we say okay but it's a red teaming tool so probably it wasn't meant to attack anyone or we don't know so then the question is does that make it relevant or not some people have said that is not relevant it's not going to be a threat it's not going to attack me they're
going to use something different other people have said it is very relevant because it it has different implications and also if such a simple tool can be available for anyone you know it can be used as as a the same way way that other red teaming tools are used for attacks and we have a stand kind of in the middle like yes it is relevant but also um uh you know also it won't be attack likely it won't be used for an attack likely but still you can learn a ton from what the tool does and how it's being used because this simplification in Tim malware where different actors that didn't used to be able to produce
this are now being able to make this type of simplify tooling that becomes as a very big difference in the paradigm so to decide whether it's relevant or not I bring a second of the cases that happened in 2023 this one is the Vulcan Vulcan Leakes it's that's basically how it's referred to it was um came out it was a group of newspapers were looking into that they collaborated with some organizations including us and then uh basically we put out this research it was a series of leaked papers that from this company and the culcan that basically was compiling requirements from Russian government on uh different tooling that they were going to develop for them uh but I'm
going to get to that in in in in a second after this because I forgot to add some additional details that's my bad um some of different considerations that's one of the consideration basically yeah the last one nation state actors that have leveraged these type of of uh contracts for developing different type of tooling um there's also another thing that lowering the buyers of Entry which is basically what I was saying before the malare was super sophisticated now it's getting a bit more simple still with the same the same type of use case but now more lightweight and you can apply it next to different type of operations uh as I mentioned also the fact that it's red team can be used for
both good M basically can be used within an attack and finally um yeah the remote chance that it could be used for for malicious purposes sorry I'll get back to the more interesting part so in the volan l site um what we found in here in these documents was very interesting there were three different modules and and what it tell tell us about it is first of all how well there's the investment I'm trying to develop this tooling um but also the combination of different types of operations so Within These modules it wasn't everything OT it was actually some part of it was OT some part of it was trying to compile data from different sources like even social
media vulnerabilities expose devices uh basically all types of scans all types of data um and then they were to put it all together in a single platform and then try to they were also requesting for for support on developing different types of exercises particularly related to OT te so what we see here is the simplification of Tim malware into smaller modules that you can then go and deploy next to bigger operations so that then you can have a bigger impact as in this case in the event of a conflict to be precise when I mean impact for OT there were two cases in these documents that explicitly called for this uh list of requirements for
particularly targeting real systems uh pipelight systems I'm saying super generic because it's translation and because this was requirements Gathering we do not know how they accomplish or if they accomplish if there's any tooling coming out from this uh if it's still working but what we do know is that was the requirement that they wanted to have malware that could be used for these purposes um and then that matches with what we were seeing cosmic energy where uh basically it might be a contractor working on that or it might be directly a government might be a separate organization might be any type of case might might also be private and nonrelated but and the last thing in terms of the
development again in terms of this discussing this perspective of red teaming tools and whatnot is uh the other case that we saw in 2023 which was two particular vulnerabilities uh for those that are into vulnerabilities in here you will know that there are thousands and thousands and thousands so probably it's going to sound like why would you focus on two of them when there are so much and probably others that that can impact that a much larger scale but what was relevant of these two wasn't the vulnerability itself what they allow you is to um interact with control logic equipment again like industrial very specific General uh General Communications devices but what was very relevant in
here was how it was disclosed and actually the vendor collaborated with the US government and then collaborate with different organizations including ourselves and different places to put this out at the same time because in some way somewhere it was H connected to a specific AP so the reason in this case is this is similar to in controller the case from last year where an AP develops a specific capabilities for a specific type of OT devices and then in this case gladly it come to the vendor first before anything is disclosed before anything is used the vendor puts out these vulnerabilities you can avoid the development of such tool but then it shows again like how the development
just keeps on going it's like differently from the past we're just seeing more and more and more and so lastly in terms of red teaming I just thought that it was good to do an analogy and also I needed a c in my presentation of course so red team Tooling in this case is going to be like cat PA right like like on the one hand it's uh it's fluffy it's pretty the cat can walk they can eat they can do whatever but then on the other hand if they want to scratch your face you're definitely going to regret it right so it's kind of like that in this this type of red teing tooling when you're
discussing it it's like it can be something that is pretty beneficial pretty useful but it depends more on the intentionality of the use of the of the specific [Music] tool so it's for you to decide if this was very concerning or not being a ring tool but beyond that and I just don't like leaving everything on on kind of like a note of let's see what you think but I also wanted to give some recommendations uh into what we learned and I thought this is this is some good practical stuff um into how do we hunt for that type of activity what was it that our our researcher did to find it and what could you do in case you're
interested in being the next person to identify some ultim malware um and basically there there are three three main things that that we have been highlighting recently the first one is that ultim modware in general like when you go and analyze H has this consistency of abuse of insecure by Design protocols so in this case it was I 104 but most of the protocols used in OT are not extremely secure so if you look into known protocol like modb like or like in this case I 104 and whatnot it is um most often the Mal is going to try to use it to communicate it's it doesn't even have to have so to be so
complex on on on the the development and finding of workg grounds as long as it can get to communicate with industrial device so this is definitely something to look for just look for know OT protocols and and that still gets you from here to a smaller sample the next thing is uh open source libraries to implement protocol given that these Protocols are fairly specific and you know often times are propietary but also there it's just not something that that you go and and just learning in live how to use unless you have the experience and you play with it and whatnot so basically there's a ton that use open source libraries because make life easy
and allow you to understand the protocol without needing to go super in depth and the last one is uh python from allw development um and packaging that one probably would raise some I me like probably might raise some eyebrows when when you say just like look for python because python can be everywhere right um but actually that's not the case and this I put this because uh the researcher did this is from him he he really wanted me to to put this I while like okay man I I'll just go and include and basically what what he's bringing up is like python is very commonly used yeah in multiple environments and and whatnot you you would assume to find it mostly
everywhere but particularly in industrial environments you do not use any type of of of um of coding you have to choose a specific tooling you have to choose specific coding most often there is no python in there and if there is there's going to be a documented use case so that is actually something that tells you very interestingly that if you have something that interacts with OT and has python probably it comes from a researcher probably it's an attack tool probably it's some different thing but it's unlikely that it comes from from an industrial facility it could happen but again it will be closed and it will have a very specific use case so if you're
sitting back in there you are defin only going to notice and the last one was um yeah in terms of Discovery methods some general recommendations of course uh I think the first one is as I mentioned uh looking for those type of python package executables that in my opinion has is is going to bring pretty pretty good results if you find that combined with some other OT parameters uh and the second thing that I see pretty relevant in here is the MSS SQL Server that normally I mean of course you're not going to look into any of them but if you have any that are connected or close to any type of OT equipment that is
basically where you're going to be hunting for this type of activity um basically there are also some some types of um of things that it was trying to to to use that wouldn't normally be used in in in the environment and so the main takeaways just uh to gra dis ration what are the big things that we we can get from from this particular piece of malware and and this this type of evolution uh first of all buus buus to entry lowering for for offensive volti as I said ultim used to be fairly specific it has to be a very interesting uh proprietary devices and whatnot and right now we are seeing these simplified versions that are easier to deploy and
that you can use next door cyber operations the second things is uh cosmic energy capabilities are not extremely different from other type of ultim malware which makes us believe that even though there definitely is going to be more under development if if you look for activity based on what has already happened it already bring might bring you some of these interesting findings the second thing is uh well it's rare uh takes advantage of insecure protocols it's not something you're going to see every day um so definitely whenever you get these Publications enjoy them because the next one could have could be a couple years from now the same way that it could be in a
month um in terms of red teaming of course there's a leveraging of red teaming tools and contractors so it is a possibility that we are going to see cosmic energy in the future if we don't I wouldn't be surprised but it is definitely possible and then lastly well yeah I mean like definitely this is more like geared towards Ot Ot audience uh last recommendation but obviously if you are in the situation where you work in some uh industri organization definitely worth keeping an eye for this type of activity and the learnings that it comes from from there and that's all from my side thanks for everything uh if you have any questions or anything feel free to to reach out
I don't know what happens or do we have okay cool okay so thank you