Are Hacktivist Operations Placing Operational Technology At Risk?
Show transcript [en]
thanks for all of you for being here first of all just a quick introduction I'm Daniel I work with the attorney intelligence team with mandiant particularly we work in everything related to operational technology or industrial control systems um most people here already are super familiar with that with the term but in case not because you say we're having some discussions about that General General speaking everything that corresponds with physical processes powered by engineering and computers basically um so first of all I know that it sounds weird and actually I I love like the response that I was getting when mentioning activism and some people were like why activism why are you even going to talk about that right so it sounds kind
of old in general because when we mentioned the topic of activism most often it comes at the image from probably 10 years ago when when we started seeing this type of like actor that was trying to generate some political change he was trying to show uh you know I can go and hack you I can go and have some power with myself make movements something whatever right and then from there we had this terrible image that still if you go and search right now that's you might as well know you go and look for an image of like a hacktivist particularly and sometimes also hacker and you either find just the black hoodie or you find this guy
um however you know as interesting as it sounds as as this nice looking you know I'm mad and terrible to be honest the impact from activists historically was not really large right I mean it was maybe maybe they will DDO as a site maybe they will leave a message saying like look we're terrible and we're after you they will leave a video but to be honest the impact wasn't that large however the reason to bring it back right now is actually related with something we are unfortunately all familiar with which is the current political landscape right in the court I mean as this as a conflict uh the invasion in Ukraine started happening recently uh we started
seeing an optic in again in activists trying to you know like push something in favor saying like you know I think this time I want to get involved in this in this conflict I want to do something I want to show that that I have you know like this this Powers so to speak and then uh we started seeing more activity however there are two different types on the one side you have things like hacknet kill net some some big groups that are actually dubious in like affiliation and whatnot and then on the other side you had this this forgotten Group which was the the people attacking operational technology industrial Control Systems trying to find exposed
systems and trying to say and claim hey I went and I blew up this or looked this uh facility is not gonna work anymore or your systems are going to go down in this paper mill those are the ones that we started looking into and we started collecting it as part of our trading so team and that's how we came up with with this research however the big question in here and then that's also like by the beginning of the talk and whatever like like the idea of the shredding Iraq it's terrible but I just find it very fun um that is the fact that you know similar to The Experiment where there's a cat in the box and you you don't know
if it's alive or dead until you actually have visibility uh it's the same in here basically we it is difficult to know what what the actors actually did if they actually did something how bad it is where is this coming from if the actor is even who they claim they are and when you start getting together all this uncertainty it becomes a very interesting puzzle to solve and that is basically what we're going to be discussing right now I'm not unfortunately I tell you right now I'm not going to come up with a solution I'm not gonna tell you it's the most relevant or it's not but I'm gonna give you enough um how to say
enough information so that you can decide by yourselves if this is the most relevant if it's not if I should worry about it if it's a joke whichever but uh I'm gonna do it with many anecdotes so that it has also some some uh some value in your lives so first of all the the claim that that happened from last year 2022 we actually well early this year we published this this uh research that was saying activists increasingly claim to Target OT this however was not the first time we saw it it is the evolution of something that we started that that started growing since probably a couple years ago there was another piece of research
we pushed in 2021 where we released this timeline where we're discussing uh something that we call low sophistication attacks laws investigation attacks for OT means this case where the actor normally goes find a internet exposed OT goes modify some parameter tries to make a change in system uh oftentimes well I'll talk a bit more about like techniques they use and whatnot but um basically yeah we started seeing an optic in that but most often back back then it was cases that had to do with um opportunistic actors basically I just did it because I can because it's fun uh we saw others that were kind of like we do it because we want to sell it I don't know if someone
bought it but possibly um and then yeah we started seeing that the actors started not only getting access like in the past but also interacting with the process and in this beginning we started seeing also like the activists started playing a role it was before the conflict and whatever but just there were a couple incidents where where activists would claim I I went and I exploited something right and there's actually this is just one of the anecdotes for fun there's a very known case that was um and specifically against Israel and basically the actors were saying you know we hate you you're terrible so what we're gonna do is we are going to destroy your energy systems here you go
here's an image this is what we did um first of all energy systems don't really mean anything uh so second when we started looking at the panels that they were sharing we corroborated that it was actually a kitchen uh it was a like an intelligence HVAC for a kitchen and we were able to track where in Israel that was and everything and you know it was a very fun case not for the kitchen but for us um and yeah I'm like oh everything was fixed notified and whatever but yeah you know like like that's the point we started seeing there this idea of activists also some other activists that were sharing tutorials that were saying
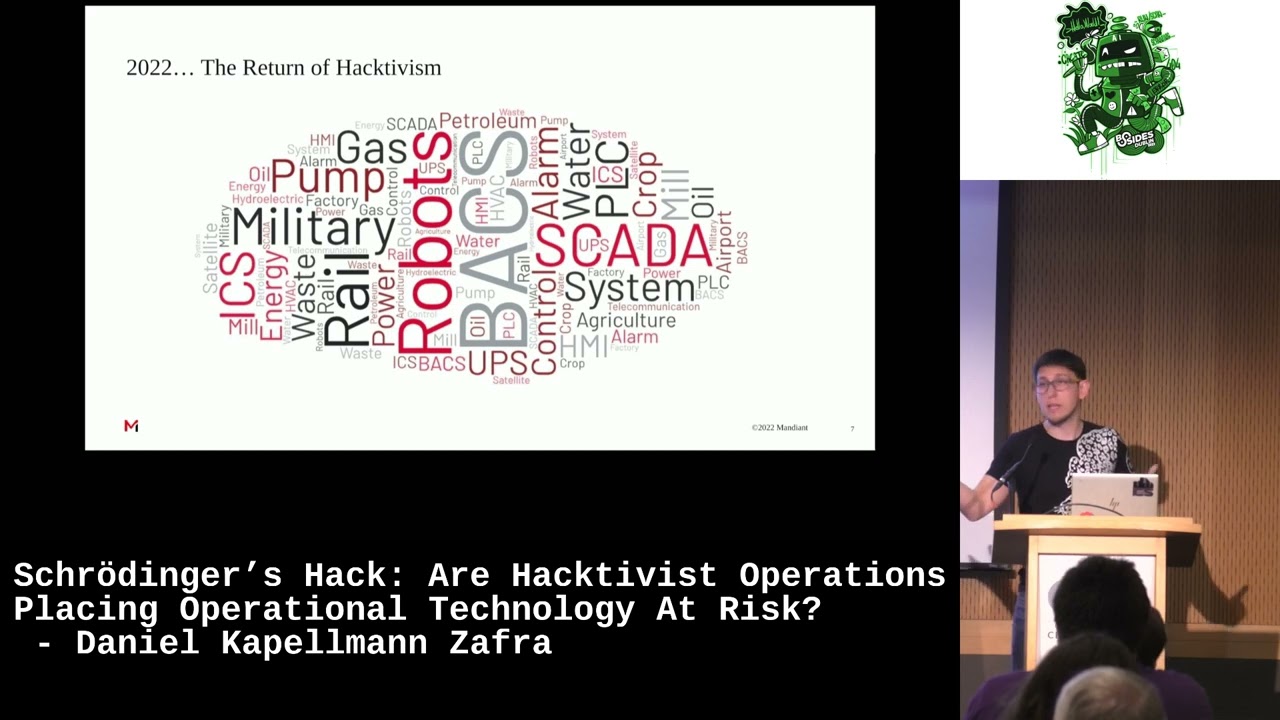
you know this is what you have to do these are the ports you look for this is a type of Technology you look for these are the vendors you look for and this is what you can do so there was this intentionality but there wasn't yet that drive to start doing something more and instead in 2022. that's with the with this research interactivism we started seeing more cases and then there was this intentionality and then there was this Spike right um here just to give some some additional information about in general like our sample so just to be entirely clear and what you're gonna get and where it comes from basically this this is uh This Cloud is made by type of word
warning that we would find in their messages that indicated the interest for OT uh for those familiar with OT you're going to recognize a ton of these ones uh for those not then now you will um and basically well yeah we started looking for this type of keyword in their messaging we started looking at what type of of things they were doing and also the other thing to clarify is of course this is information that's very difficult to get access to because it can be just posted whatever sometimes online forums sometimes it's social even social media publicly but it's all over the place uh sometimes it's very complicated to get access in some cases so the point is uh
since we have that uni capability it was very interesting to put it together and try to share a bit into how this looks like one final note um is that before talking more about this activity more and more in detail is uh what do I mean when I mention activist claims uh active claims these are two real examples actually they were posted in public social media this is one of one of the actors that is super yeah very openly uh this one is actually Pro Ukraine uh it was it's been trying to do compromises in in Russia in general and as you can tell here for example this is the type of OT uh compromise that we see where what they
did they go they find panels uh of different types of processes trying to interpret what the process is and and these people particularly have been very good at at showing that they know they're doing that they are doing the research that they're understanding from there to an impact there's still more to discuss but at least you know you can see that there's the interest and they are finding it as something something valuable oh sorry and just for the name team one fist is a name it's already there but in case you're curious you're going to find more more publicly available information and also an alert that that is basically that when you're going to see some of these
claims oftentimes like you you never know sometimes there there's some reality and then you have to go and do pretty much a ton of research into that mostly ozent but sometimes also it's it's seems like it smells fairly inaccurate this is for example a real case uh one of those prolific activist actors that said you know we went we did this explosion but then when we when you start looking more into those explosions actually there is some attribution not to an actor but to an accident that happened in a different location or you know like when you we also have to look at the real incident where it take place and if there is anything anything any way to know
however from an OT perspective even if it was real validating such an incident would be super hard because you need to involve uh basically a ton of Engineers and then you have to involve the Computing side basically analyze how the process worked what was the problem with the process if there had anything to do with the computer and most likely your equipment is damaged so it's not going to be easy so having this this context of like like the activism and and OT and whatnot I'm gonna try to bring a bit more now of The Facts of what we're actually seeing and and to to discuss and determine if this is you know something we should be
worried about concerned what is actually happening so the first thing in in fact I I prefer placing the boring packs first so the most boring one which is the techniques they use actually um this is this is a mapping based on miter attack for ICS the specific Matrix that they have and like like with similar parallel techniques and basically what we analyze like what you can see in here is is a summary of the most common ones we're observing from activists uh definitely very different from what we see from for big hardcore OT cyber physical attacks um but basically what you see here is a pattern in general initial access is going to be by exposed exposed
basically anything exposed to the internet uh most often it can be with platforms such as Showdown senses whatever if you want to talk earlier they mentioned something like that oftentimes it could also be just you know like basically whichever type of tooling you can use um the second thing is normally the exploit there are two types there are a couple that have started doing a bit more complex cases where are in a complex like using modules from from I'm not going to say open source but basically like publicly available tools such as you know meta split modules for OT protocols and things like that those are a few but most often it is a graphical interface so most often they
just go and find what we name you know see the HMI human machine interface and then basically once you have access you can go and click it doesn't mean that the system is going to respond it depends on many things and it doesn't mean that there is no safety mechanism maybe there is normally there is but you know there that's as much as we can tell based on the on the evidence they show then from there it's very often that they're using valid accounts there's normally not a lot of complexity in these type of compromises which makes it also on the one hand better because it sounds less concerning on the one hand on the other hand it's worse because if
they're happening and happening it means that you know we still find those type of loopholes which is very common for OT and then yeah finally um I think the interesting thing on the impact what you're going to see here mostly sounds actually pretty mild when you just say it like manipulation of control loss of availability but when you actually think about what that means from an OT perspective from a safety perspective manipulation of controls mean you have a physical process that is operated by these machines you modify a parameter and then the the organization that has control over this process has to modify and go and figure out what happened with the process this process
could be anything from production of uh in a manufacturing facility but it could be also energy it could be water water facilities especially are normally very weak in security because they don't have a ton of money to bring like like security people basically so that is the reason that is one of the reasons that make it kind of like like concerning uh even though the compromises are not per se complex um to exemplify some of these uh big uh let's say big techniques the first thing is this is an alert reel from from from CSA from in the US basically it is very what I found the most fun about this alert is they just
said uh actors are targeting UPS um basically it's like power backups so we recommend you to disconnect them from the internet and that was all like a line so like okay well thank you um but yeah what's interesting in here is that they put out this advisory shortly around the time span when the other team that I showed you second a couple of minutes ago team one fist they actually claim to be compromising UPS whether it's related or not who knows but it shows that you know some actor finds something they start sharing it others realize that it's a thing that is a concept that they probably weren't familiar with or a query that they can
do and then you you start seeing this kind of like transfer of knowledge to show the graphical interface portion which normally is much more attractive than just the the the command line I don't know if you're familiar with this this type of images this is what we call the human machine interface and it basically it can be processes as complex and weird or as simple and non-relevant uh it depends we see a ton of these ones uh put out by by low sophistication actors uh some of the panels that you see here don't even say that much because it's actually a logic a programmable controller basically engineering equipment to go and fulfill a physical process
um and yeah so so part of part of the job we do is also it's like whenever we see these claims we go and try to validate what actually happened if there is any concern or if it if it wasn't in some I insist it could be super concerning in some others not really like for example another another phone case that we had well actually was an actor saying we compromise a rail systems basically trains um and then they showed the image from from the control and then after doing some research some due diligence we realized it was it was a train it was just like a model train so probably you know it was it was kind of like Ant-Man
you know it's like Falls around for those who watch watch the the movie but yeah so um anyway so so it depends it can be very concerning or it can just not and the most interesting for like like for this year and like the most relevant sorry recent cases that we hadn't we didn't used to see this before we used to see the the exposed uh systems but we didn't we were not used to seeing these actors using anything more more interesting and in this case they had two things one of them is they were using some meta spot modules uh if you're familiar those three are specific protocols that you use in OT um they're they're very common and and
most often fairly insecure IEC 104 might sound even like probably not give you a lot of information but if you're familiar with with the big OT malware cases which there are only like eight in history um like at least well known uh in destroyer in Destroyer version two both of them deployed in Ukraine to turn up power lights um one of them successful the other one uh possibly possibly not and then cosmic energy the last OT malware that we actually our team just just published I think like two days ago a Blog about that all of those were basically using IEC 104 because it's really used mainly in in European facilities for energy um and Kill Boss there was also like
like a specific tool that they did for themselves um this was also modbus uh modbus is also a very common one of the most common OT protocols and again what we were saying here is uh they were just like searching for devices trying to go trying to do these modifications and the most interesting thing is here there was not even like like a panel or an image that would tell you what happened you which you simply don't know they just like found devices and maybe they just tripped some devices around and that's it I mean there should be some way to verify but it's going to be very tricky um so yeah we saw that and the other
interesting here is we didn't see it from just one group after one group did it we started seeing other groups using the same tool and the same tool and same tool the same with vulnerabilities for example there's this um there was this device uh fairly used in Israel uh that was basically for HVAC and [Music] um basically like yeah building Automation and then one actor found that there was a vulnerability from 2016 in that device they started exploring remotely so he started finding more and then you saw one two three four many actors starting to reproduce that same vulnerability against all the devices from this company so and you know even though it was fairly old so
that was something very interesting that we're seeing basically actors starting to use more of this tooling um and moving away from only the the poking what's what's online and so what's what's the impact security serious and also I really apologize for these cats I promise it was a normal horizontal cut but then I had to move the pronunciation a couple times and I just couldn't fix it anymore and that's what you see that thing uh but anyway so what's the impact you know like because I I believe in and I'm aware that painting this picture it's a bit difficult because on the one hand I say it's very concerning on the one on the other I say ah you know really it's
not that bad so I think that it makes a bit of sense to describe uh what the impact could be how it could be how it could look like and for that I decided to bring three cases just like discuss um 33 cases we had researched that are fairly interesting the last one is my favorite I will gets there um but so let's let's debunk some of the some OT hacking claims um first of all the first one goesick I don't know did did anyone hear about this it was like earlier this year around January February did you ever care about ghostec ransomware rtu does it ring a bell for anyone then great because then it's even more
interesting so um basically around we have actually January this year there was this uh case we made it made it big to news mainly for for OT people and whatnot and it was super discussed and what happened is just an actor ghostek uh posted on social media saying you know we just deployed ransomware in a remote terminal unit okay what does that mean remote terminal unit is an automation device basically it's mainly used in energy and then you use uc2 control interaction with other different devices this is something that that's basically for well it can work in different automation Industries but for example a lot in energy and it is basically the score to have a physical
process works and how you're going to receive the service um but it's also fairly specific normally when you're talking about an rtu it runs on something in sometimes called rtos real-time operating system so it's not something that you can just go on ransomware like Microsoft or Linux or whatever oftentimes they are proprietary they might be even made by their own vendor they're fairly obscure um so by by claiming by getting an activist claiming that they had done these ransomware on an rtu was something fairly fairly new it was like okay if you did that you would be the first one it wouldn't be a researcher it wouldn't be a security it would it would be a
activist now the problem is uh that they also shared evidence because they want the credibility and they they're really trying hard you know what they're doing is is for real and the problem is they were searching for itu and there was a knowledge and there was intentionality but basically once they started sharing the evidence and we were able to go and verify what had actually happened the picture was slightly different this one I do believe it was an honest mistake so at least it wasn't like in other cases where they are kind of exaggerating this one what you see here is basically the evidence from from the actor what what they offered and then I
don't know if you see down there it is a build for rtu blah blah blah it says rtu but it does not mean it's a remote terminal here it's just a name of a different product that's called rtu and then so actually this was a router so we started looking it was a router it's more like similar to um to a Raspberry Pi in this case it would say kind of like in capabilities um in their defense it is used sometimes allegedly by the vendor for OT but you know it's not really like like a big deal and as you can tell if you recognize some of the of the commands in their base well not commands basically
the the names in there it is um it is in Linux so basically what they found was via an rtu but an rtu that meant something entirely different had nothing to do with OT was much less concerning uh and yet it caught a lot of attention and one week it was look activists are going to destroy the world the next week it was like look okay maybe not maybe it wasn't real you know like yes but no um anyway I mean of course you can see here like like also they showed that at least they did encrypt something with a you know very interesting uh file extensions but um anyway that that was the first one and
and I think that was fairly relevant from an OT standpoint because he would have been like really something big if that happens the the second case uh this this is one actually not one single case but it's actually multiple and it's more like something we we have absurd fairly often that is when the activist claims that one of their attacks resulted in physical damage somewhere else so sometimes it is difficult to know if they're taking advantage of that and you're saying it's some it's difficult to know if they believe it maybe it's just to call attention because in the end from a active standpoint what you want is to call Media attention people's attention to your cause right so you
know the attack is being effective in that sense it just goes out and it's something we see um and yeah these three cases for example they all claimed they said yes there was this explosion and it was me is it true is it not most likely it's not based on the complexity that you need to make one of those things happen it is possible and we've seen nation states doing those type of attacks um but not specifically like like as a single activist group that normally would not have those capabilities um and interestingly here for example like in the third case here the one from team one face that case we were able actually to validate there was public
information claiming that the explosion had resulted from uh basically a technical error in a different facility in a very different location and then eventually you know just basically just uh it was entirely unrelated to the hackers but in other cases it's difficult to tell was it them was it not most likely not but you know it's up for someone to validate um the third one is my favorite though this is the case that actually I I'm gonna ask again just for the fun but is any one of you familiar with with predatory Spyro it was I think late last year then again I'm very happy because then I'll bring it up um so Predator Express is a very
interesting case it was it was an actor that that appeared um basically be already like like last last year uh a bit earlier and what they did actually in the beginning it was a ton of compromises against Iran basically like things in Iran it was a television channel it was uh gas pumps uh this one uh basically that's still manufacturing uh and I'm missing one but anyway they were like like four critical infrastructure cases um one of them was actually very fun because like in the gas pumps what they did was they switched the message and they added there a hotline from from the supreme leader let's say so like if you see that you couldn't go and pay for
your gas you would be flooding their their their hotline so it that was a fun thing they they added but anyway the point in here is um these guys they have something particular because they do claim to be activists they behave like activists everything seems activist but actually they have some things that no other activities has or not really common like basically complex malware families that they create for themselves uh we call them meteor and meteorite both of them used in these these surrounding cases and sort of related to this event that I that I'm gonna discuss right now what they claimed was that they generated basically they were able to damage still physically damage uh still
uh facility a steel production facility and what they share for evidence was the following on the left on the top what you see is a video of the Furnace it's like um I think like five minutes of video you see it from normal how it starts basically that's when it starts falling eventually there's explosion um it is interesting because on the one hand one can say just like you know it's just a video but obviously we did try to go and validate we did try to find maybe they reuse it from somewhere maybe it was like fate generated maybe we tried all those approaches and it didn't seem like uh it may be that it happened maybe
they're not obviously from from from Iranian authorities they came back and said this is a lie nothing happened to us nothing has ever happened to us but also it's not like we're going to be able to go on validate right uh it's not like just carrying coffee shot or anything um so in in this case for example there's the big belief of like is there a risk is it possible it is possible that this happened they also shared this um again human machine interface that does have the information from from the organization um and yeah I mean so so the trick in here is there seems to be feasibility in the case uh happening but that also brings different questions
right like like for example um when you discuss about hacktivist does that mean that the activist is is like really just an individual trying to operate out of ideology and doing something might it be that it is a government for example there are some theories that say this is a specific government because of the conflicts in there um might it be that that it's not a government but it has the support such as in in recently we've seen a group called uh kilnet and hacknet and both of them for example operate in very close timing proximity to deployment of wipers from from Russia in Ukraine so for example there are we seeing collaboration or are we seeing uh
government saying you know you can do this no one's going to say anything this is it's in public social media then you know maybe we can also do it and then no one's gonna say anything or no one's going to do anything because they can't even validate so actually that is that is this is one of the things that I consider very very relevant and just to finish the case because I mean make sense to give the full story the actor also claimed a responsibility for basically when they saw that that researchers were pushing back and saying like hey I can't really validate they tried to go one step further and do more and say like okay look here are a bunch
of files from the three factories that I compromised this is all their engineering documentation which normally is very relevant for planning an OT attack from our perspective though we analyze those documents they do seem to belong to organizations so probably yeah they compromise at least some file some email servers but didn't it didn't seem like the type of document like for example our red teamers would use to do an OT attack or that we've seen from other actors stealing so was it was it not it's basically a bit tricky so let me see yeah I'm good so um I guess after giving like all this this information on the cases I think the the big points and what I promised was to
respond uh if this is something that actually we should be concerned about or not because like you see the type of Target is very relevant for your life is physical it's one not and yes there is a connection and there is a possibility of doing an attack but the question here is are that is the attack coming from the activists the one that's really we should be really concerned about right and for these I mean as I said I don't have a response yes and no but I'm going to give you the summary for both both arguments so that you can you can make your decision on the year side first of all activists do interact with OT assets
they are finding the exposed assets they are using these different uh modules exploit modules that become increasingly available people are getting more familiar with the protocols with the how it works with what it means and you know that is something that is just simply a fact we are seeing it um the second thing is higher frequency means higher risk so theoretically you know like when we go to through the equation if we're seeing more more cases it is more probable that it's something that can happen to you if you have something exposed most often we expect that will impact smaller organizations rather than the large ones that have a lot of security but still you know like as I said earlier water
facilities play Within those smart organizations for example you know it's there there's a lot like there's a lot to figure out in there from from critical infrastructure perspective uh third one calls me the attention basically the more it is reproduced in media uh how it's seen and whatever it is good because there's awareness but there's always this challenge that also there might be copycats others doing it normalizing the case it's okay you can go and say you hacked something you blew up something but you know no one's going to do anything right because it's you can't prove it the fourth one is a it might help nation-state Selena actions such as the case of hacknet and
kilnet or such as the case possibly well possibly Hackman killed it or possibly with the predatory Spyro it is basically what we call plausible deniability that the state can do something and then you know just say it wasn't me it was a activist so it provides the tool and lastly the share of knowledge basically that right now we're seeing this this trend grow over the conflict but then the question is what's going to happen hopefully soon when the conflict is done are we going to see these guys still doing something are we still going to see hacktivism becoming a consistent problem or is it going to be like the last time when there was something it
caught attention and then it just went dormant for for a long period of time there's positives for the no on the other side is uh basically the techniques they use are very simple yes I'm definitely not talking about an apt grade type of event I'm not talking about uh not even ransomware that right now can get pretty complicated I'm talking just about the hacktivism the activist attacks that most often could be reproduced by just looking at a couple set of instructions and having some general knowledge the second one a higher frequency does not mean higher impact that is true so even though theoretically the risk is higher it does not mean that they have that they are
normally causing big impacts so in most of the cases it's different it's it's even difficult to tell if they did something or not or what is the implication attacks require more resources to generate impact in general for OT if you really want to go and generate one of those explosions that they said it's not that easy you do need to develop more complex malware you do need to be very familiar with the cases we've seen a lot recently for example from from the in the conflict in Ukraine uh about like like growthing capabilities from nation states uh polish blogs about that and whatnot but you know those are big teams that are working with this uh in conjunction
engineering Computing and and whatnot right um activists can call me attention without a team yeah as long as it's something flashy it does not need to destroy something so probably it's going to be a passing trend and then lastly uh nation states have hacked OT with little to no precautions in the past so it's if you've seen if you follow the past OT cases most of them have never gotten any consequences for for the people conducting them uh there are a couple for example um of indictments in in the US for the case of Triton 2017 Middle East uh there's indictments for you know like like for sandworm team which is one associated with industry or whatever but
in general most of these cases just you know it's difficult as a state to Define what action you're going to take um for multiple reasons so that being said um yeah I think that's that's everything I have my personal opinion is uh we're gonna continue seeing this at least through the time of the conflict given the geopolitical situation most likely it's gonna probably go a bit forward uh the more complex the political situation is the most likely you're going to see this type of attacks and the fact that we see these type of factors using more tools trying to to find different approaches I do think it's concerning and I do think it's something at least worth keeping in
track because otherwise my concern is that if no one's looking at it the day that it they actually achieve something interesting No One's Gonna Know and everyone's gonna say like it's normal you know they've been doing it that's all um but instead if we keep a track on that we might be able to to to to basically respond if we see this type of escalation from actors that are less complicated it's already a big problem with nation states a big problem with criminals I just hope it doesn't get to be a problem with uh with activists as well and yeah that's all on my side uh yeah thanks for everything and I don't know uh yeah I think we have
like a couple minutes so if anyone has that okay yep
well it depends okay yeah thank you yeah sorry uh I'm gonna repeat the question so so he was basically asking like like if if uh the use of nation states of these type of activist operations is basically like like a benefit or a hindrance right like basically [Music] okay does it help cover the operations or does it hinder covered operations so it depends I would say like like I mean this is not the first time that we've seen in uh nation state actually like like cooperating at the the haxies level so it definitely can help if depending on the objective that's the summary if your objective is basically to call attention to something that's happening
to show that there's a capability for example uh for psychological operations if you're trying to for example damage the in Ukraine for example let's get the people the psyche let's get it down let's show that everything that's going on in there that everything we can destroy then probably it's a it's something good uh however it's definitely gonna be gonna hinder it as well if what they're trying to to do is just keep it secret but most likely I I would assume that you just wouldn't use the type this type of technique if you wanted to really do something covered so okay yeah I know any other questions not okay I think then we can just
I think we're good okay cool thank you





