Creating A Resilient Red Team Infrastructure Using Terraform
Show transcript [en]
that it's still here at close to 6 o' I know it's been probably a long day for you I've been here like only like from 12:00 and it's been like a full day of uh presentation uh I would have hoped that more people would attend this uh this uh talk because I think one of the the speakers mentioned about the uh the fact that red teers do create like a lot of resilience infrastructures and they do like this whole stuff where they keep destroying and recreating stuff and it's very hard for blue team site to blog them and uh make sure that we have like an upto-date known uh domain list or IP list so this
is what the talk that I'm going to show you is going to be about and it's going to be focused on um this is like a very short content just so you take a look and know what this talk is going to be about I'm not going to go through each of the lines um very few words about myself uh I'm a senior penetration tester at 12 sec maybe you've heard of them they are Greek based so yeah I'm working for a Greek client but I'm not from Greece um even though I like once three month I go there and stay for one week uh I have like a lot of certification most of them
are focused on red teing and offensive stuff uh on my time uh on my time off I like traveling for poker uh also listening to uh a lot of different songs trying to find like the best high-fi system and uh things like this and I also like to travel also like uh for example I came here by car from Romania so it's been like a very long trip and this is the last stop um so just a few words about what you should expect about this stock and what you should not expect about it so we are going to talk about how to create the infrastructure that I'm that I said before and what resources you're going to need and also
creating is not the only only important aspect but also protecting infrastructure because that's how we defend against the blue teamers that continuously try to find us block us and you know create tickets to like domain providers and say okay this is Malian take him down um also we're going to talk about like the financial aspect so how I mean what's the financial cost for this infrastructure if it's worth having it or not and also a couple of things that are still yet to be manually done even with if even with this uh automatic approach so you should not expect about me going into and talking about how terraform works or like exact line by line analysis of what I wrote but we are
mostly going to focus on like infrastructure key aspects how you should approach and what technologies we used to do this um also this is not like a state-of-the-art or like some sci-fi research that has never been done before there are some people that have done this I think even like ram house has provided like a some sort of resilient wam infrastructure in the past that I actually have my research on his but the problem is that his is like 3 years old uh most of the things are not working anymore there's a lot of new things that are implemented so but that is like a very good uh Baseline also this infrastructure is not bullet proof but
from what I've seen I have actually used this with my client to like doing like not red teing in general but also like even fishing so I have used this to spawn and Destroy stuff very fast and they are not able to like block me or Mark me as malicious and also this is not about an open source project yet but we'll see that in the future um so I'll start with like some simple aspects of what R team engagement uh requires or like a fishing in like shorter uh terms so in a r teaming we usually need for for sure a host where we have like a public IP and it's actually a C2 like
Cobalt strik and or other Frameworks um we also need a host with a PL IP to deploy like a fishing framework I think goish is the most known one but you might also have like custom proprietary tools um we also need like a lot of multiple domains and a lot of custom DNS entries like subdomains uh change C names or other stuff and uh you also need like a lot of redirectors because as I think most of you know uh everything that we have like the most important host with database and other stuff are like hidden and what we actually see like as a normal user is the front facing infrastructure that it's usually like they they replicate
something legitimate or they look like there's a legitimate business and there's nothing malicious in there so we do that by having a lot of red director R directors we can either uh manually deploy them or we can use like domain fronting or other stuff um so in order to have all of the the the things that I've just said before in general we would use something like for C2 we would lose like metas sploit SLE or Cobalt strike or Brut uh if we need a fishing framework we probably go for goish um if I mean we use goish to send emails and you know manage the whole fishing scenarios but we would need to use uh some fishing
templates too we can either manually have like a Apache with like our custom HTML which is good like 5 years ago but the problem is that nowadays we need to have like a actual framework which provides like fishing templates that can um you know provide like real time feedback on on incorrect usernames uh help providing like OTP bypasses and so things like this so this this is why we would use something like a like a proxy framework that would redirect everything from the legitimate I mean the user would see our domain which is malicious but the actual uh I would say the whole design and everything looks like the legitimate uh uh software or service
that he wants to log in um we will also need like a go dead in name chip or whatever platform to buy domains to look legitimate um and this is like something I I've added because I haven't seen anywhere we actually need like a WordPress that looks like legitimate so when we actually go to our domain the first thing you see is like a WordPress blog or like a presentation website so something that looks legitimate and would help like scanners to um categorize our domain as I don't know we want to be a Blog we want to be like a bank okay so we have like a presentation website that says we are a bank in
America and we are doing this because we need to look legitimate so if everyone everybody is looking in the logs and they are trying to see who did send us the fishing scam and they see oh this is a weird domain we go there oh this is a classic B bank I don't know where in America so we need to have something that looks legitimate um and we also need like a lot of tunnels we can you can either choose from like socat SSH or maybe there's other stuff that are useful but I've used mostly SSH and socat so this is like a very simple like basic diagram on on how the infrastructure would look
like based on what I've showed you before so we see that we have two people that are important here we have the victim and the operator the operator is us and us as the operator should have access to everything that we have deployed so we should have access to the goish database which is the the main server we should have access to the C2 framework uh also on the other on the other resources as well but the victim which is just like a simple user with some access to a workstation when he goes to the internet he only he would only be able to visit the goish proxy which doesn't have the goish framework on it it just proxies everything to the
goish which he should also be able to uh access the fishing templates because that that's intended I mean at some point we'll give him a link and he would go to the fishing template we also he also needs to visit the WordPress that's so that's the main the main thing that he will be redirected every time he tries to visit our domain and he also should be able like if we deploy like any sort of malare on his computer his computer will talk to the C2 proxy which is the front-facing part so when let's say they detect in some way they detect they have a malware and they see the traffic to the C2 proxy we just destroy
it build it again and just do like redirect the actual C2 database so we don't actually burn the whole C2 and recreated enter the license import the profiles and other stuff so we just burn the front uh the front domain so now the question is how how do we do that and in general we have two options uh you can use your own server so if you have like servers you can deploy VMR EC XI or other stuff and create like VM VMS and manage them or you can use like a cloud version like user provider such as I prefer digital otion but you know any of them are supported throughout the presentation um and the problem is that
for any of the above uh options that you choose you have to do two stuff you either have to create like a lot of B scripts and try to automate everything uh manually or more via scripts or if you want to be like more I would say like more in an automate thinking you would probably create like some snapshots or like some base images that contain your whole tools and uh uh I would say configurations and when you have like a new engagement you just go and build from there so you can either like pack them and upload to digital ocean as a base image and you spin your custom C Linux or you can do like if you
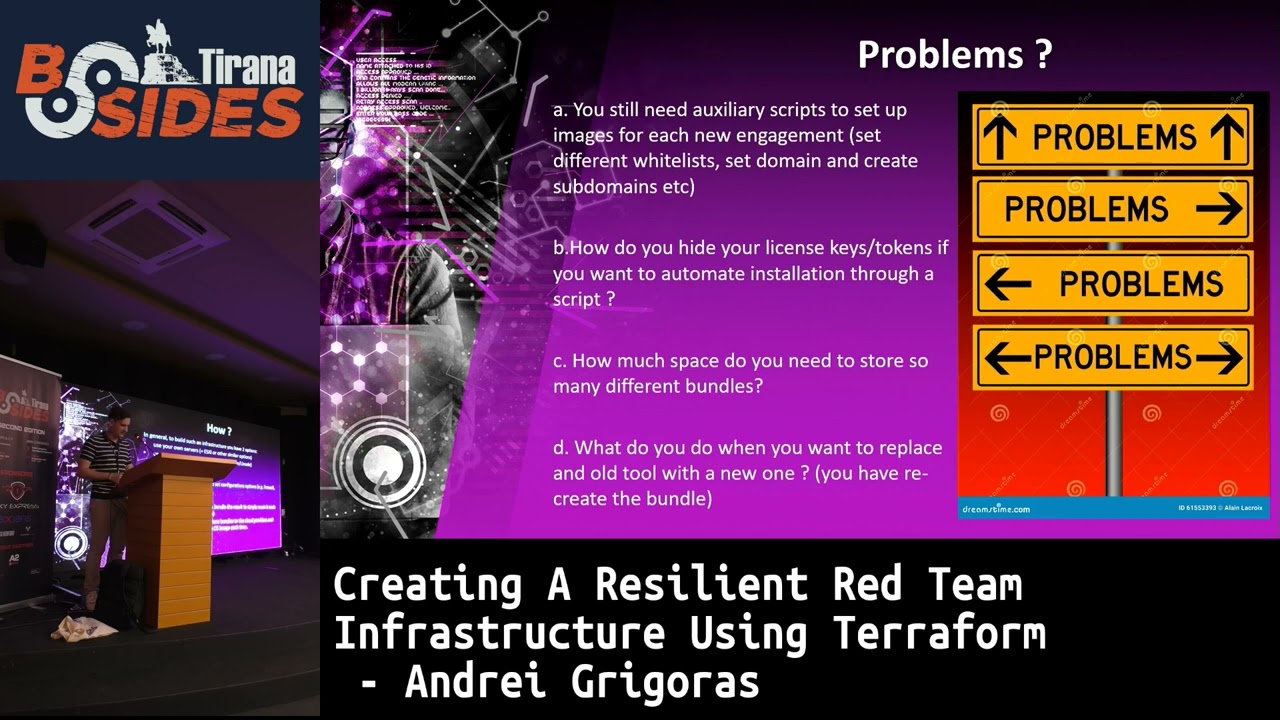
have EMR you can just create like a snapshot or like a base image you can use Packer from hashy cor so there's a lot of things that you can do to like automate um but there are of course I mean this is the I would say the traditional way of doing it so there are a lot of problems with this uh and the thing is that even though if you have like base images configured you still need to configure like custom stuff for your newly purchased domains for your client uh for your WordPress which needs custom stuff so you need you still need like a sort some sort of B script to configure even if you created the VMS
like uh I would say like in five or 10 minutes also the question is you have B scripts and you install everything how do you hide your license keys because once you deploy something on internet nothing is safe so if you have uh on a VMS script that you run and installs your cobal strike and that's like doing in automate weight so you spin up the VM and by default it's copying a script it's installing Cobalt strike it has the password your license and other stuff so the the question is how do you secure that because let's say your C2 has a vulnerability and some exploit it they find your C start license and it's over
so you just wasted everything so you just need to make sure that when you deploy stuff you also are not deploying with like credentials that can be gained by other people um also another question is that if you build custom images or uh snapshots or other stuff you it's going to require like a lot of space so you have to store them like for example let's say you have like 10 different VMS with like different Frameworks or whatever you want everything is going to require like a lot of space because it's not just the the kernel it's the whole image so it's going to take like at least 50 GB every time you want a new a
new screenshot um so you also need like a lot of space and also the question is you have everything set up and there's a new tool that is coming out and is better than all of the before you have to recreate the whole stuff so you have to go back again with the base image install the tools pack it and then upload it again so this you know you have to look every day for if there's a new tool you have to recreate stuff this is like very timec consuming and that's what we are going to try to uh avoid here and the solution probably some of you might have heard about the the theras uh infrastructure as a code so we
basically want to code everything that we are going to build as an infrastructure there are multiple providers for this but basically the the the most important aspect that we want to achieve with this is to make sure we can destroy and recreate stuff with like a simple command uh we also want to make sure we can configure host like okay this host is going to be created we have the code and then when it's created it's going to run these commands and these scripts and do this stuff so we make sure it's configured especially for the for the current like engagement um and we also want to import Secrets or tokens or whatever we might use during the
installation to make sure it's safe so they are not actually disclosing the host so if someone compromises the host they are not going to find our passwords or license keys and yeah this is the result so we're going to use infrastructure as a code there's multiple uh providers for this but what I've chosen because I I think it's the most popular one it's terraform um I'm not going to go through all of these details but this is like a sample on how the project look in the end of the research and we have like a I would say there's half of them are the most important thing in the folder uh the first thing that is the cloud init did
everyone hear of cloud init before okay so when when you deploy like a new instance let's say anible or whatever you're going to need a provider that goes in the VM at the end and they are going to install whatever you want so that's called a provisioner so clouding it is a technology that is going to be used after the VM is created to install everything we need we're going to say install a Pache modify the file and have that configuration uh install certificate so we are going to need like a some sort of interface to say what commands we're going to need to be run on the VMS so this is a folder that is
going to contain one file for each of the hosts with commands specifically for that host how it should be equated and this is also uh code so you actually if you need like a new configuration or like you need to modify the Apache configuration you just go in the folder go in the host file and say okay now I want this in the configuration change it uh also another uh another important I would say couple of files here are the ones that start from the C2 back till the end so they they specify for each Host this is the terraform file that they specify create this host which should have like One processor one gig
ram uh it should have this configuration which is related to the cloud in it uh you should be able to access it using this SSH key and other stuff so the they usually look like the same it just like the name is different and if you have like specific configuration uh and in in the in the last part we have the most important ones which are firewalls DNS uh I mean firewalls and DNS for now uh so firewalls is going to specify every firewall rule that we want to implement in digital lotion in this example but you can also do gcp or other stuff and then the DNS is going to be everything that is going to be created by default
as subdomains or anything else that we need if we if we are doing our own custom SMTP stuff we're going to specify the whole SMTP relay what pre cords you need to create and other stuff so this is the I would say the most important ones the the first one like the variables and providers is like basic terraform stuff I use the variable the variables because I I actually love coding so I like you know separating stuff from the code and everything is a variable and you just go in the variables if you need to modify like the operator IP the front domain name the SSH key name you just go in the variables change it and everything is
updated so if you create this environment that I just just show you it's going to look like this like in the in the dashboard so you're going to have all the hostes that you created and the domains that you have registered already in digital ocean also if you go like to the dest records and see like everything that the has been created on a networking level you can see all the records here and also all the firewalls in the same place so it's very easy to see and manage if I want like a very custom St that I didn't add in the code I just go in the dashboard of digital ocean and then create it here so this is
the basic stuff so we create the VMS we know some tools now the question is how do we customize this because we I mean it's not that easy to create like red team infrastructure and have everything like you know at least very uh modern in terms of like we want to make sure everything is like compliant with the with the new stuff that we have to create and defend against so the first thing we need to do because a lot of tool doesn't support SSL we have to enable SSL for every uh proxy R director everything so they are going to all have ssls and we are not going to do that manually we're just going to use like
let's encrypt and we're going to buy code specify which domains we want and they are going to generate SSL certificates by default uh for the back host we don't need uh like custom SSL certificates we just need like self signed that's fine for the front facing we're going to need let encrypt so we always need two domains but only one domain is going to get certificates so let's say if the front domain domain is burned and you don't have another one you just switch the back domain with the front domain because you know no one has seen the back domain yet uh we also need to remove every indicator of compromise from goldfish EV Jinx or any other
Frameworks if you use any and we would like to make sure we are not discovered so I would say that this you know trying to be hidden from the other guys is usually going to be done by blacklisting everyone so this is like just a simple demo on how like the synta text looks if you want for example in the cloud init file for a specific host if you want to enable SSL uh you just need to modify some specific Apache config so you would specify that when the host is created please write this file with this content somewhere on the disk to make sure Apache knows the configuration and it enables SSL also here all of the proxies
would have the rewrite rule we have logging so we can filter based on user agents and other stuff and they're going to proxy everything to the back domains yeah this is another example of the configuration so it's usually there's a pair of three files that you have to modify to make sure SSL is enabled and everything is supported and rir it to the back hosts uh also we are going to need like some commands to be ran also in the same file as before uh we need to generate the certificates enable some specific Apache modes uh Delete the port 80 because I never like having it open um and this is pretty much all for the red director so it's I
would say it's it's usually simple to create the red directors now if we go to the actual framework that we're going to use so it's gfish if we go on GitHub and clone it and we try to find like what indicators might show a scanner that there's goish there because even though they can only see the front facing part for example the 404 template so when they the scanner goes and they go slash something that doesn't exist there is a 404 page they're going to do like a md5 su or a sh suum and they're going to compare to like a known database list where they know this sum is for the goish 404 template so we need to modify
that because they would know it's goish even though they don't see the goish port or anything else uh we also need to modify like specific controllers disable or replace at least the default tracking uh parameter delete specific uh they specific headers that they're going to add in every email request because in email if you go to show original you're going to see everything that was added in the email and if you use gfish by default they just going to be like an X goldfish header there if you look so that's also an indicator of compromise um you can do all of this manually or via script or you can use the the the the project which is called sneaky goish
goish and it's also used here um which already has all of this installed and to create the VM with this I just create a VM install Docker and then run this so This has like a dockerized version and now for the a jings because I'm not sure how many people know that they have left like a lot of indicators of compromising the code uh so for AAL Jinx which is the main in the middle of framework they're they're not going to do like a lot of stuff to to tell everybody they are evil jins the only thing they're going to do is add a new header in every request that says X EV Jinx and the actual host
that the request is coming from so this actually tells everybody this is EV Jinx and this is the host that is being used as the heav Jinx host um and they didn't make this like very clear because they did have like specific you know encrypted bites with hex they exort something they create a new header they don't specify EX Jinx they specify replace the home directory with some letters and the actual result in the is X Jinx um yeah so there's multiple places here I think there's also a function that says you can't find me or something this is in the actual code and also because now there's a newer version for this which I actually
used uh in the project a JS 3 they also had the same stuff they they differ a bit like like the code they added because they know everybody knows about the code before so they just created like a new function that replaces some strings and then they put it as in the header so now about the whole backlist stuff because this is I would say the the part where we would try to you know make sure no one finds the infrastructure and they cannot detect Us and something like that so blacklisting first every provider on the internet but I'll start with Google and Microsoft they will scan the entire public range every day so this this is what they do
uh they scan it and they map every service every service fingerprint everything they have they added to the database and and that's how they can find like easily detected fishing page if you hide if you put something on the Internet like a fishing stuff and you don't block access to it it's going to be detected in like a matter of hours uh also if you have like a cobal strike publicly available they they can map the service they see the fingerprint and then know this oh this fingerprint might look like Cobalt so we are going to block this host where we go to Amazon and say this is Cobalt strike we actually H had this so we had the cobal
strike that we left it there for like a month after an engagement and then the Amazon came in and said hey we have uh we have received a complaint that you left the Cobalt strike why are you using this is this legitimate or not so just make sure you you know about this you know scanning stuff and you you block you block all of them or you just remove it uh and also this is not specifically related to Google Microsoft uh because every trade intelligence business will do this the thing is that most of them will probably say somewhere publicly especially Google Microsoft what is their IP range of the scanners or protection for example if they have
office suit they were going to specify on their Microsoft page that this is the office protection IP range or something so they're going to scan emails attachments with that IP address so it's very easy to block because we know them uh but the problem is that every intelligent business will also scan it and they are not going to say us this is my range so how do we find it uh an easier way would be to either like put a fi rule that we only Whit list specific IPS but this is hard because if you do a fishing you don't know like what IPS the the clicks are coming from so the other option would be if you
use for example EV Jinx I can just spin like a fishing template this this is intended uh put Blacklist mode on and left it there for like two or three days and everybody that is going to enter that u i I mean my my domain or my site my fishing site it's going to be like an automated scanner because no one will ever know I mean by default the link is not going to be in a blog post or like in Instagram post they not going to know there that it exist exist except if they are like an automated scanner so after two days I have like a huge list of people that try to reach me and then I
just block the next time I destroy this recreate it with the Blacklist instead and I know who is going to scan me there are also like specific uh software on GitHub that they do some sort of custom implementation of goldfish and they already have like what they like their Blacklist from what they've seen in the world or what they collected from Microsoft and Google uh Pages yeah so if if you want the tool for example in Blacklist you're you're going to start seeing like this so there's a lot of ips or ranges that are going to try to hit everything uh that you have opened and you know by default we're going to block them but this is how it would look okay
so let's go a bit on the coast because everything is almost free so terraform is free for local deployment I also have used for this project the the cloud version which is also free for up to like 500 resources which is I me I have like 60 maybe on the project so I would say everything is free so you don't actually need everything extra you just need to spend some time on you know learning how to code in terraform and build the infrastructure and for the normal cast here for digital provider but this is usually not relevant because if you have your own service you're also going to have Cod so we are not reducing anything
you just need to like the VMS so okay we talk about what we can automate the question is what is left and what is still what still needs to be done like during each engagement um and the the most important thing is find the right domain and purchase it so this is one of the things you you would try to find domains that look similar to a specific client name or something like that but in general uh you would also want to like find a domain that has like a very good reputation also you after you buy the domain because everything is managed by digital ocean you have to make sure you change the name service to digital ocean
because that can be automated I mean probably you can do a script to do like a query on the API and add the domains but it's just like a simple like one minute stuff um and and also you need to create and configure like an sntp relay so goish will send emails but you have to tell him how do I send these emails like what what mail books I'm going to use so you need to create that and configure uh and also build build a reputation on the domain that you purchase so you you get a domain and you make you want to make sure it has like a good reputation it's not going to be
blocked uh for example if you're trying to mimic like a bank or like a financial institution you want to make sure that a lot of providers on the internet know that your domain is actually banking or financial category um and one more thing that I think it it would be worth customizing is linking the goish with the EV Jinx because at this point the only thing you can actually track with this combination of goldfish and EV Jinx is who opened the email if the email was delivered or not and who clicked the link but if the after this they are redirected to the evil Jinx and when they enter the credentials it's not going to appear and
goldfish because they are not linked they are different hosts so I mean this is this is the downside of not using goish like in its full potential because by default they have like a landing page where the actual victim goes and you provide like an HTML code where you say okay this is the the password form this is the user form but that's that's not going to work unless if it's like a very basic page and I don't know I I would never use that because you have OTP you want to do more like multiple steps if the user enters like a wrong character I'm not going to say successful I want to know if the username is
valid so what's the the whole thing about SMTP so I I've actually started uh working on this project like one and a half years ago and initially when you have like a digital ocean host whatever you can open port 53 and you can actually on your own domain create like a SMTP relay so you can spin up post fix and other software to make sure you send everything from your domain so they have realized that a lot of people were using this for like fishing scams and they said every provider on the internet they are blocking everything related to SMTP so you can no longer open port SMTP on the host and send emails from yeah you
know the the the the ho that you just deployed on the cloud provider they're going to block it so uh for this you're going to need to like one one option would be to migrate from the cloud infrastructure to like if you have your own VMS and servers locally you don't have any restrictions so you can simply you know configure the VMS but we have the problems that we mentioned before so terraform is is going to work with like Cloud providers if you want something else you're going to have to change to anible or other stuff and they don't have the full support that CL terraform has and a lot of the features you're are
not going to be able to implement like firewalls and other stuff maybe so the other option is to use like some services that are online to you know send the emails on behalf of you so you either use like Google or Microsoft we a business plan because you have a custom domain so you have to register the custom domain of the provider so you send emails for them but that's a bit sketchy because you are going to send like a lot of fishing emails and they are going to see it because it's Google and Microsoft so you you don't want to send through them you want to just send for like a provider that doesn't care if
if it's malicious or not uh so you can use like mtpn domain authentication it's called with like a provider such as send grid which is the one I used for this project and which is free for like up to 100 emails per day and you just create an account configure your domain you have to create like some custom DNS entry to make sure it is your domain and then you're set to go like everything is going to go through send grid if you want send grid will also provide metrics on people that open the emails Open click the link also if you want to do that like but this is already done by goish I mean you you don't want
that so this is how you just go in sangid and create like an API key go and goish and uh set the SMTP details to be sent through Sid with your API key okay so now we are going to talk about domain reputation because if you are only going to follow this test until now and you're going to go and send an email from your domain it's probably going to be marked as fishing or scam or I don't know I don't trust this I have never seen this so uh the important aspect is to make sure your domain has a good reputation on the internet and this usually requires like I would say like a
minimum one month to do this depends on how how much money you have so one option would be to buy a domain that has a good reputation this sounds weird but if you go and track and monitor domains that are going to expire and you you know look for them and in the day that they expire you go and purchase them you might get lucky and buy a domain that has already like a reputation of like a known bank that was I don't know maybe a weird place somewhere on the globe and they just forgot about paying the the domain and you just go and buy it so you have the good reputation already um you can find them on expired
domains if you want to track them uh I'm already working on a tool because you want to find like a specific domain on a specific category so if you go here you don't have the specific filters so you have to pull every data they have then you have to go through each domain and search online to see their reputation if they are specific category so this is also like some things you can automate and if you want to build your own reputation so not buying a domain that has a good reputation uh as I said you can create like a landing page at a WordPress you have to do like a lot of I think it's cell or whatever they're
called the you know having a lot of links to blogs creating a Blog that links your WordPress so you know you have to do like all this stuff uh also you have to make sure that you create the WordPress with data that is relevant of the domain reputation you have you want to be so if you want to be a bank you're going to you know try to provide like specific I would like uh to have like a blog post on like banking stuff and how to secure a bank and other stuff so it's going to be categorized as banking um and if you have time it's good also like to post comments or news
or use any social media to make sure there is some sort of uh knowledge about this domain and people go there they know it exists leave it someday so that Google has time to index it and see it's legitimate there's no fishing and after that you actually use it for the engagement and another thing would be to warm up your inbox which means there are specific providers but I think you can also do this which is a bit harder uh where you log in your mailbox and for like a period of like 60 90 days they are going they have specifically created mail uh email addresses on different providers and they are going to ping
pong messages with those providers that they have so they are going to send emails every day and say Hey how do you how do you feel today and they are also going to respond yes I'm fine this way the the provider ERS know that there is a actual good and real communication between different email addresses so they are going to know that when they see a fishing email from you this email has provided like 1,000 email that were good before maybe this is a mistake maybe I mean if if it's not sure about if this is a fishing or not the previous messages are going to help so this helps creating like a good reputation on your
mailbox okay so as I said you have to make sure you have the right category so if you you create the domain and wait for one week and you still don't have a good reputation you can manually go through some of the vendors and try to submit like a uh a request to make your domain be health or banking this is for example a good list of providers that are known you can go uh on the blue code or other providers and you know submit a request for domain observation so they would go M supposedly they go manually and inspect your domain and then say okay this is legitimate we have our database we're going to update it to
make sure everybody knows this is uh banking so the the question is all this process of you know automating requests through the providers and make sure they have the right category is there a tool that is already available and the question is yes uh this is called chameleon it's a it's a tool that does the exact same thing as I said before but it doesn't Provide support for all the vendors that were before so I think by default they only provide support for three vendors um but the problem is that this tool also was not updated for like in the last 3 years every vendor has implemented capture so all of the forms have changed their names and everything
is not working anymore so like none of the pro vendors that they do it's working anymore so the idea is that we already know that what we need to create so we can also code this so this is another tool that I have implemented in the project but is separate because when you want to create like a reputation so you build INF structure and then you create you run the tool which will by default go on each of the providers take your domain and say okay classify this as I don't know a parameter that I specify Health banking or whatever so you simply use like a selenium driver or anything in Python because that's very
simple you open a browser you mimic like a user going in a page submitting a request if you see like a capture there is there are like a lot of capture solvers on GitHub that are free uh and you can use that and use ch to make sure your message that you're going to send to these vendors is like look at least legitimate like hey please help me with this so um I named this chameleon V2 because it's based on the idea of the previous chameleon and for now it only provides support for these vendors that uh it goes and submit or checks the current category maybe because if we buy a domain and want to check the category
we want to see where it is we this also can be integrated with the other thing that I said where you in the expire domains pull all the categories run this tool see which has your designed uh category and then you use that and buy it uh so the question is okay we have this tool and we submit because at this point we submit like very basic stuff we say hey this is my health blog uh please mark it in your database as a health domain and the question is what are they going to respond they're going to visit my website they're going to respond like by default they're going to say no we need more details please provide like
any sort of details on your domain so what happened is that most of the vendor like 60% of them I mean we it's only five or six now so it's three or four but 60% of them just say okay we updated our database uh some other people said that okay this is still a newly observed domain because it was just bought so we are not going to flag it as anything for now and some of them flag it as it which I have no idea what it means but it's it I don't know as long as it's not malicious it's fine so this would be like a very simple uh screenshot on how the tool would look like
uh okay so the green doesn't look very good so this goes for every provider says the current category is this and I have submitted the request with your specified parameter as a category so this is also like fun with like the response that I got like some of them responded like a matter of minutes uh and especially like bright Cloud just said okay we have dated our database light speed system said hey someone manually has viewed your website and has uh Mark is as hell thank you and I was like no it's just a simple blog it's like just one page of workers and nothing else um also I I manually or I think by the tool also did like in TS
intelligence they don't provide you like an email where they don't come back to you and say okay we did it but if you go to their website and check it they mark it as health so I don't know what they did there but they just mark it as whatever I wanted and I think the last one I don't remember I think me cafe or something or semantic also Flagg it as medicines and health because that was my health blog um okay so this was the main part of the you know presentation I also have like a very short live demo where we just send like some emails and see how they look and the fishing how the
fishing Frameworks looks like um so let's just hope everything is going to work as expected so first of all the question is what is your health blog that everyone said you know this is health and this is all of it oh it doesn't oh oh God no no no no I see it here but I don't see it there that's a problem I have multiple desktops are they going to be shared on the TV if I swap them so I do have like multiple desktops is there any way I can also make them appear on the screen uh yes I mean what do you want to so this is this is desktop too not it's not
going to show there yeah do you want both of them oh I want there's like four of them but sure just can't uh I unless I can mirror your display yeah why not I mean what do we have extend yeah we have
extend [Music]
uh you also have to flip it yeah but that's the problem because on Windows I don't think you can flip only one screen well we have to test no okay and then I'll try to move them all on the in the first screen I'm just going to move them in the first desktop that's fine just go back in the previous configuration yeah but it's flipped
okay yeah
so have to move yeah yeah just I have to move this so basically like because it's not slow okay this is annoying okay oh so now I have to look here okay so this is the magical he blog that I created in like 10 minutes um we have like a very simple mailbox here that we're going to send the emails and I also have to move this window here which is not going to yeah where oh where is
okay so let me first I have to go and enable the internet because I need to be able to access the fishing framework where's okay well they just disconnected me from the Wi-Fi okay so
now but there's I also have like the brave browser it doesn't show here so where are all of these now where is the other window I don't know oh God is it here huh okay wait yes I have two let me move this okay but you need to move yeah yeah wait first I have to make sure I can open it again okay so this works here also think I have digital ocean here yeah
so where is the
bottom maybe go
down now let me I don't know it doesn't show the not the internet is not working yeah just the all
of
ah this is the main host that is going to have the EV jins framework so I'm just going to go where it's installed and run it so when we send the fishing email we're going to be able to go there and enter the credentials um [Music] jinx
well it doesn't look very very nice but I'm going to explain what it should see here so I have only one fishing template enable at the moment which is the office one so when you when you go to the link you're going to see the Microsoft login page and if you enter the credentials right you're going to get a token back so this is the this is a default view um so to to make sure this is enabled okay this is visible right now so now let's send the the email
okay
[Music] come [Music]
on
doesn't want to connect maybe it's do you have like in the mail like a simple email just demr the email I think I deleted and this this should work let me check first no because now the goldfish is [Music] down this looks like the the yeah the this is the
one I mean the fish
is I think let's go with [Music] just I need to have this
work maybe it's the port that is not no it was until before that pink would not work because of the firewall let
[Music] me yeah uh how do I
restart let me restart this maybe
just
yeah okay so some parts of the demo doesn't work but I have like a very old message that I sent using the goish um this is a simple text where it has like a Link at the end if you go and click this link it's going to first track all your email open and clicked links and after that it's going to do like a very quick redirect to the fishing page which is also here [Music] come okay okay so this is the fishing page which has the custom domain and it looks exactly like Microsoft so here if we simply introduce the like one good email address and password and the OTP code it's going to be successful and it's
going to redirect the victim on the official Microsoft page after so I have a test account for this okay let me get the password from the other
screen
okay let's also see the OTP
code [Music] sure okay so this is done now it redirects to the official Microsoft page now a normal user would probably be already logged in in the Microsoft page so when this redirect happens it's going to actually redirect him to the actual office you know UI which is authenticated so if we now show the EV Jinx here and move it to the other screen okay I don't think it looks very legitimate but right there down is the username password OTP code and down it says that every tokens have been intercepted so if we want to view them and for example import them in like a cookie manager and imp personate the victim uh we can just type
in sessions okay and we have the the session for the user that I introduced here and we can also do sessions one or five okay and this is the the actual token that is used like to impersonate the victim so this is like an authenticated stuff you don't actually need to go the second time and put like username password and OTP which is changed you just take this code this whole code and put it in like the browser and like import it as a cookie manager okay so this is the only part I could show if the gfish would have worked I would have also shown the how the emails were sent and when when it
says that you have clicked the link and the whole redre from goldfish to EV Jinx um but for some reasons the demo doesn't work for now so okay so this will be all if every anyone has any questions I would be more than happy to respond yay he first thank you it was really brilliant presentation uh I just want to ask some specific question is there any way to remove this annoying uh goldfish variable that appears on at the end of the link that it sent uh like yeah g so that's actually what I name it the parameter I mean you can change the parameter I think initially it's I I think it's rid from so when you
create the goish like this Custom Image has G because it's the Google tracking stuff you can name it whatever you want you can say user verify equals to but they going to add like a specific unique token at the end to map the user that were sent the emails but yeah you can change that so you can customize the name of the token the name of the parameter in the URL yes so can you also customize the token itself like the complexity the length so probably this is coded in the goish so probably you can go in and create it can be named Star Wars but there should be like a function that Maps a user that will send
the email with the actual token yeah I couldn't find it EAS way so I yeah you can customize everything like I think there is a project there so a project that is called evil gfish they already mapped the database from Gish to evil Jinx so they just when they spawn a jinx they just link the goish database because they are on the same host for their project they are on the same host so they just import the database and when they get like a token or like a username and password they go in the goldfish databas with like an SQL client and they just put it there so this also shows in the Goldfish panel
thank you [Music] okay does want have okay this going to be the last question because we have to hey thank you for the presentation I'm very curious about the architecture that you built I'm just wondering with the uh with the email like the go Fisher right the fishing platform uh so there are many email security vendors that can actually filter these as fishing I noticed it myself in my experience 99.9% of these are categorized as fishing not by uh exchange I mean exchange protection but by email security uh vendors is there anything like uh let's say as is there anything we can you can Implement within the framework to uh let's say hide that malicious the link
specifically that redirects to um fishing page like so I don't think that the link is specifically marked as malitia so what I tested in the in the last thing so first of all if you send an email that has images all the images I uploaded to imer because it's a very known domain to host images and assets and that was the only website that it worked to upload image and reference from the email that are and are not blocked and then there's another thing if it's a new sender and you have images or links the email in Outlook is going to say okay you receive it in the Inbox and it says uh this is a new sender we
haven't seen before do you trust this if yes or no and then do you want to show the blocked content which is not malicious it's just images or like specific fonts that you put it uh so the thing is that if you would use like the warmup mailbox this email like this mailbox or the main or whatever should be should have been seen before so maybe Outlook will not flag it from the start as malicious and as for the links I would probably like if I would choose for for a fishing template I would not choose to put a link in the email first of all you can either put it like without HTTP and do like H XSP or
something like that uh or you can use there was like a if you do like you target Google there is like a Google open redir which is known like there's like a meeting. google.com/ redirect URL equals to so you could use that for example or you can use like a link that has maybe capture when someone goes to there uh but what I would use actually as a fishing template is the device code fishing if anyone has heard of it where you simply send the user an email where where it says okay we have a a new device connected to your Microsoft if you want to approve this you have to enter this six digits so when you go to
Microsoft and do like microsoft.com I think it's smart TV or something there's a specific endpoint and you enter this six digits that were in the email so there's no link you go that I by default get the session token of your like Microsoft account so there are ways like to do fishing without putting the links but as for making sure the link is not blocked you just have to build a good reputation that's that I mean that that would be the only thing I would think of yeah makes makes perfect sense thank you there is one more we don't have time I mean like we should have ended like 10 minutes so guys please make it
quick considering the demo time uh thank thank you Andre just a quick question when when you're building the um WordPress site um and you're sending the emails manually um did you mention it's going to be a period of 60 to 90 days or a week and uh the second question is um the male server is using a s sangri IP uh suppose you're using a digital ocean IP and a lot of them are blacklisted how how much of an impact does that have on domain reputation I'm not very sure I've heard you like correctly because it does it like the sound was very bad here so the first thing was uh the first question was
about WordPress right uh yeah U Can you say again what about WordPress so WordPress uh when you when you are um building a WordPress site and uh building the domain reputation from the second method uh rather than buying expired domain how long do you suggest that site is active for and how long do you suggest sending the emails I think I missed it you mentioned 60 to 90 days is so yeah the mail the best warmup provider that I've could seen for the mailbox would say that the they would reach the peak for like the best reputation in like 90 days so if I would have the time to prepare for a red team engagement I would buy the domain and
then wait for like let's say 60 to 90 days where we have just the WordPress out and nothing else and then send the emails to you know warm up and you know send communication to other people and respond thanks and the last the last part on can is just I'll make it quite brief as well uh the IP address um is going to be send Grid's IP which is it's going to be srid yeah yeah what if it's not send Grid's IP how much of an impact does that have on domain reputation if the srid has a bit reputation oh no so if if you're not using s s grid IP if you're using just a
post fix from um yeah so when you use so initially I had a project with like a postfix installed locally so I had these cases when I build up like a digital ocean they assign me like a random IP and when I send the emails it doesn't drive in the inbox so I go check the logs and it says the email could not be delivered to Google because Google refused and if you go online and check the IP address it says it's malicious okay so we got assigned an IP address that was probably used before and it's malicious okay destroy and recreate that's all and at some point I'm going to get like a new IP which is good or
you can there's also like a feature you can paint digital ocean and Reserve like a specific IP one get like or get like a premium IP so you make sure that's not blacklisted from the beginning no wor thank you Andre thank you I