SIEM Slam: Tricking Modern SIEMs With Fake Logs And Confusing Blue Teams - Özgün Kültekin
Show transcript [en]
hi everyone um first I'm very honored and place to be here so thank you for this amazing event and invitation and today we are going to talk about our latest research which is uh we called it CM slam uh it's about tricking modern CMS with fake logs and confusing blams and we are going to focus on mostly splank As the CM so about me what I do um I'm 22 years old I'm currently working as an offensive security engineer at trendal group which is um highly Tech focused e-commerce company in Turkey uh and it's actually the biggest e-commerce company in turkey and currently rapidly growing in the global like Netherlands Germany and uh my focus in my company is I'm in
penetration testing team mostly focusing web active director and mobile pentest and also uh I'm working in the briding attack simulation um I do red teaming and some purple teaming so our contents for today we will start with a quick introduction for General CMS and splank uh after that we will talk about our problem and our solution for that and how did I explore it how did I exploit it after that uh I will show a video of the demo and after that we will talk about endless ways to cause distraction how can we exploit that uh even bigger after that we will talk on the mostly blue team site fighting back and finish with road map
so let's start with introduction so CM CM CM so anyone uh currently using CM tools actively in their company yeah right because these are essential and anyone who is using splank and I'm not asking I was not supposed to ask that question then you're probably not supposed to answer with it but okay um it's a centralized platform for monitoring and managing security events and incidents it's called security information and EV management so for many organizations like probably each of them cm is like the essential component of the security operations like like years and it's um critical forab teams because they are just enable them to detect some potential attacks and respond to them quickly like you can
collect and analyze logs from there it provides a centralized log management and it generates alerts um these alerts can be used to uh used by the security analyst to investigate and remediate any potential threats and besides that it also helps to you with compliance and regulatory requirements because they are generally uh need you to have that like gdpr PCI DSS and other things and it also help you along the historical analysis and forensics because it's store the security vlocks for for extended periods and you can just analyze it in backwards so let me start talk about CM products I asked what's the most popular CM solution in general through chat gbt which is uh my very close friend lately
and it's helped me that it says as of my knowledge cut off in September 2021 uh splank is the most popular CM solution I'm not saying that I just chat G with it and um there's also some other tools too like q r from a IBM L meaf solar winds yeah but it's quite Dynamic market like splank has been sold for $29 billion um bought by Cisco I guess yesterday I don't know maybe they heard about that research and just want to sell it and let's start with um explaining what plung and how it works so as you can see there are data sources as we said earlier CM tools can collect data collect logs from various
sources that can be on premise cloud and application and there's forwarders there and forwarders is just an agent you Deploy on it systems like it's the agent on your computer which collect logs and sends them to the indexer so there are two kind of forwarders uh one of them is universal forwarder uh it's actually just forwards row data without uh any prior tratment and on the other side have a forward is just perform some parsing and indexing uh at the source at the host machine and just sends the P events to the indexer not need to go into detail uh and indexer indexer plays a huge role there because it transforms data into events like that's what what we uh see
on this plank clocks it's it's made the search and after that we have some search ads it's actually the just UI that users can use and interact with Splunk and in general forwarders consume the data indexers index index and search the data and search it just coordinates all of them and there are Management console for splank admins it's also web based interface and as the last splank web app it's just like the Superstar of the splank uh people often mistake it for for the main attraction but it's just the fancy part this is the full splank structure yeah that's that's the splank B UI you probably seeing it into your dreams a lot and chapter one uh there's
a problem and there's a one solution for that so let's talk about a hypothetical scenario uh let's consider an attacker who has managed to success successfully compromise a Target computer within a large company let's say very large company and uh subsequently escalated their privileges in into to obtain root privileges or system privileges in Windows let's say you have the root privileges or system privileges in the Target company so after that what are the possibilities I mean as an attacker after that we got the root uh we can steal some sensitive data disrupt some business operations or maybe even launch a ROM we attack yeah so options are really numerious and consequences as you can see could be
devastating uh but we as an attacker we need to like uh be careful about that because every move we make uh just leave some kind of Trace behind us right so and Bulet team is just chasing us we are racing with the time and we are still leaving Tres while we are trying to steal some data uh so it's a Race Against Time toer to evade detection and cover their tracks to not getting coughed and you successfully compromised and your main aim is just to steal data and what can you do about that right now and this all the images I'm using in the presentation is generated with AI I think otherwi Firefly so what do you do I mean you
need to um distract blutin to steal data right because they are just working on cting Q right now so by if you able to generate false data like this is the where the art of creating and injecting fake logs comes into play uh so if you generate false data you can make the buet team changee their own Tails while you make your Escape so let's think like a hacker for a moment like we always do if you had the power to create fake logs what would you do like you can mimic another attack right like you can you can show that pretend that that someone just hacked into the payment server which is much more critical than than
the already compromised one actually or you could just creely um completely made up events like create some chaos someone is injecting dangerous PS to the other host and that will surely create some chaos and confusion for bu team and even if these are not just enough you could just Spam logs like if you are able to inject logs you can spam it like you can send millions of logs into one minute and it's also creates some chaos so uh we talked about that but are we really able to do that against modern CM tools like splank so our research focus is pretty evil in there uh because in our original research we have discovered that one particularly
effective strategy to create and insert fake logs into the CM to CM toll um which can mislead the the blue teams at the end so we are basically um discovered that by doing some kind of men in the middle attch between forwarder and indexer structure uh and do some loog defacement there and we can also use that in red teaming like making lock defacement a part of red team campaigns maybe essential part in the future and chapter two how did I exploit it and how did I explo exploit it with uh introduction to lock slipper which is the tool we are releasing maybe in a week maybe in two weeks but we can use it right now and it's going to be open
source for sure so exploring CM traffic uh in our research and research on creating and injecting fake LS into sank we just conducted a mitm attack like I said before forwarder and indexer uh we intercept the TCP traffic between them they're just um communicating with TCP TCP uh protocol and we catch some text logs there like there are not any SSL or TLS into that and we pass this logs and make it readable so we extracted some userful headers like uh executed comment on the target host host name IP address and we just uh modified them fix the TCP packet structure like check some and length of the TCP headers and we send it back so this is exactly what we did uh
you can see the forward here and index and this is where we uh where our location is and you don't have to be physically between them you just can um in the in the forwarder machine and you can just run some kind of a IP tables or nfq uh as you may have guessed so first one is outgoing Sam looks and second is attacker me intercepting packet form Q like there's a queue that HS the alling pockets and I just modify the packet and send it to q and after that Q it just modified lock goes into the indexer and search at shows the modified loog and you can see the confused and some angry
confused blue teams so um in the previous section we just discuss how attackers can modify CM loog packets on the fly to evade detection but actually we can also um create a brand new fake loog like we can uh create some kind of madeup os commands on behalf of any other uh host in the network and it doesn't need to be real you you can just uh made up for the host names so what our logic is inspect the realtime traffic on the forwarder machine execute OS commands in parallel and catch your own created locks so when you inspecting realtime traffic at the same time at the same time you are um executing some OS commands and your OS
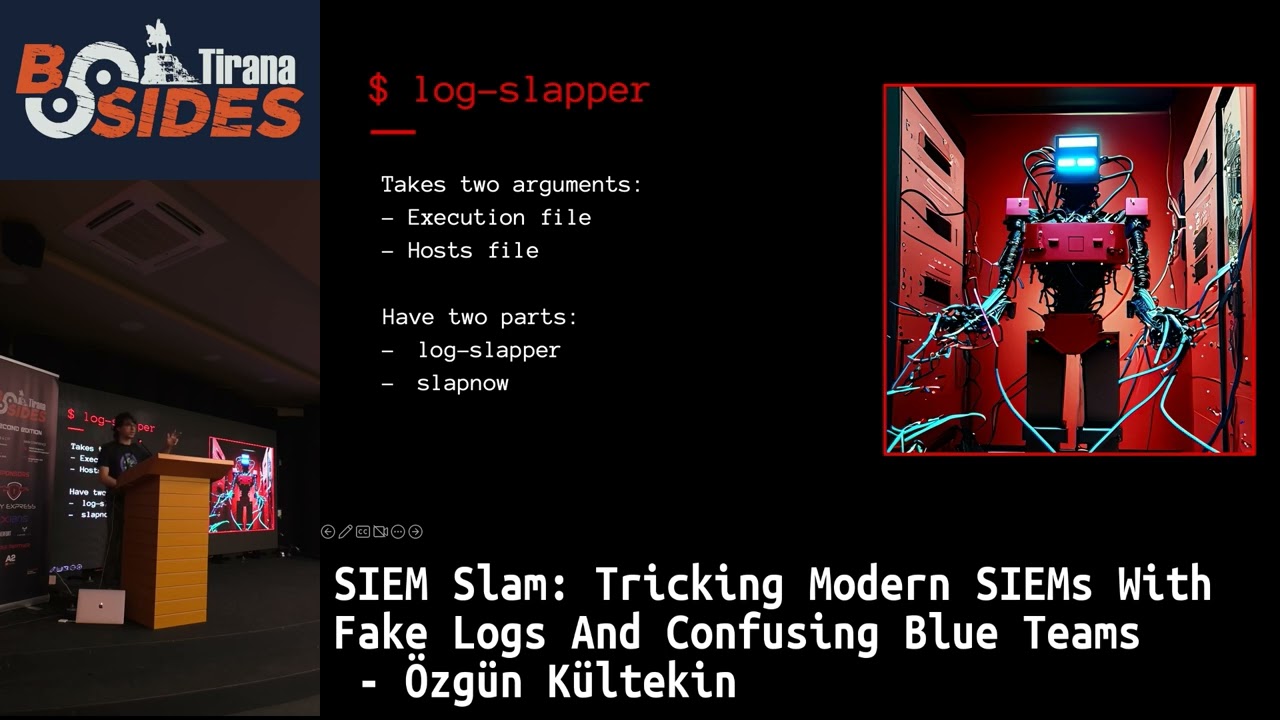
commands will create some splank logs and you can catch the logs on the Fly modify it and send to indexer so basically you are um modifying your your own um log and that's what our Lo sler tool looks like um right now it takes two arguments one is uh execution file and other one is host file execution file is just like the uh order of the commands you want to run on behalf of other computer in the network and slap now tool is uh the when you want to start the action actually so it's right now it consist from con of two different program so we developed a go we write that program with Goen and it just
inspect the real time outgoing loog traffic and on the parallel SLP Noob second tool can execute OS commands while loog slipper inspecting the traffic and modifies it so with that way we can just mimic some fake ransomwares um or I don't know we can just modify the host name time stamp destination IP we can do all of them so it's Lo slipper and in the in that chapter we will Analyze This tool with with a demonstration uh so let's get into the demo details uh what our aim is uh execute a ransomware scenario on behalf of another host in the network so let's say we compromise their host uh in the in the Target company and we have root
privileges right now and what I want to do is while I stealing some sensitive data I will I want to mislead The Blue Team so I will show that someone is just executing a r scenario on just payment server or any other server so the host I um compromised uh his his host name is O machine and his host IP just ends with 6 before I blurred for some obvious reasons and the target host name I want to act behalf from them is called tyana demo that will be it and I will uh set his set its IP to 10302 it's just made up you can do anything you want so we should start with some
creating configuration files as you can see there's an execution file um these are the numbers are just slipping times like um to mimic the real Attack like uh I want to show that like the real attacker is doing that in parallel so to make it more realistic I just put some slips between them so what our um imaginary attacker doing is he's pinging the osun malicious site.com then sleeps then he will um install some randomware T gunzip from from that side then it just unzip it uh goes that directory and launch the random V attack all right so that will the um mimic attack and there's also some constant file for the host file and
it just shows the uh which host name or which IP you want to replace so I will um change the 64 uh IP with the 10300 to so I will show I will um act on behalf of this 103 1002 machine and it will uh have the host name of Tran demo so when I was when I stealing data from the uh Target company in parallel BL team will think like oh there's a called there's a machine called trano and someone is launching a ransomware attack on that machine so I can in parallel steal some sensitive data because they are probably want to deal with this ReRe so it's demo time uh I will show
the video and we can talk on that
so in that scene I'm showing that right now maybe I don't I don't know if you can see that but it's locks from the Osos machine uh which is the original host we are compromised uh it has their own logs running on and its IP is ending with 64 so it's the normal machine we we have compromised and um right now I'm showing that the target compromised host is running splank pseudo system CTS splank status and after that I'm prepping for launching the attack so it's the execution V we went to run uh like it's again like I previously explained site he is installing some random from there and launching it and slipping between them and there's also some host file
that will contain the constants like what we would want what we would to change like I would I want to change the 64 ending IP with the 1030 1002 and I want to change the O machine name with the Tran
demo and now I'm uh launching the attack sud sud Lo leer uh takes two parameters execution log and execution file and host file then it started to inspect the real time TCP traffic there the red and green ones uh you see is the change I made I mean red ones are the um no longer in the TCP packet and I add the green ones instead of them like because I set two constants one of them is host name one of them is IP address so when it detects this IP address on the TCP traffic it immediately replace it with the host name I put into it and if you see the if if this tool see the old news machine in
the TCP traffic it also removes it and put tyan demo into there so we are modifying the traffic and while loog slipper inspects it we can see that now we have logs coming from Tiana demo machion and it's actually doesn't exist on the network but we got some demo machine locks on this plank even it's not existing and we have our madeup IP address and our madeup host name tyano so even though there's no machion called tyano in the Target Network we have its logs and now uh we want to run a ransomware attack on behalf of that hosts so I launched the slap Now command and it actually what it does is um it's
sending some hash commands and because I am using sha 50 uh sh 512 uh it actually creating an original packet so I can when I inspecting the real time traffic I can just uh find this hashes and replaces it so after some sleeping I'm just running the comments and at the same time I'm catching it and replacing it and the attack is over and 20 seconds later SL lock slapper is going to finish to and after the attack launched let's search for pseudo command on the target H Tad demo which is not existed and as you can see there is some logs going on with with run with pseudo like I we get the um site
so what blue team will see is when they log to their L plank they will just see that oh there is a machine called Tiano in our Network and it just launched Ransom attack what the hell is happening right so they mostly focusing on there while I am stealing some sensitive data from the [Music]
company so we started Lo slipper we started slap now which is the start of the real attack and we after that we waited for like 30 seconds because that was our sleep time and in the mean in the meanwhile OBC the ransomware comments are just sent to forward indexer and we just catch it change this overc commands with the real ones so CM loock created by that command is immediately captured by lock slipper and it can modified and now this is what we will see on the spank what will blue team will see so there's some random R attack going on on Spang webia if you just uh extend the details you can see that uh the IP
address has changed the 10300 to and host name is changed to tr demo from machine so uh we have that power so what what what what can we do further uh andless space because dist direction is the other chapter's name so it's when hackers get creative like we can blame others any any modification can have severe cons consequences but let's say um if you just made a reversal alarm on behalf of other other uh host machine or we can just create critical events like we did ReRe attack and besides that you can use it for hiding the noise misleading balloting while EXP exfiltrating data because exfiltration takes time makes some noise even even though you have no Falon or
just any other uh EDR installed on the target computer you can you can have the noise because there are some network uh Network Tools that will uh catch this data exfiltration so you really want to mislead The Blue Team while you're doing that so you can just create scenarios like mimic is just dumping ntds D file from the domain controller on the target Network or just you can create an alarm like someone disap the defender so you can just inject Windows Event locks too and even if if there are not enough you can just Spam the locks and chapter five fighting back this part is mostly for blue teams uh there are some Harding points of course
uh but there are just two weak point the the weak points that made this possible is first one is SSL TLS issues because because there are not SSL TLS we are able to do that right and and the second one is operating system issues and we will just talk about that uh on SL TLS yeah I know it's direct solution comes to mind but that's not easy and uh as you said earlier you are all using splank and I assure you probably you are not using SL tls2 because uh it's disabled by default and default and it's it's not that easy because um you have to manage certificates for that spun to and if you
um you just lost some locks which will have severe consequences in terms of gdpr I don't know and um there will be also extra burden and delay for this encryption and decryption process so it's not that easy um and some expiration problems will arise on the splank site so there's some delay risks expiration problem expiration problems and managing certificate issues are there and also splank has has an option to use some TLS um in their one of the one of their solution but unfortunately they are using the same certificate for each sulun instance they are not creating for your just company uh I mean let's say there are 20 companies there and actually we are all using the same
certificates if we uh go with the default certifications then that's that's too bad second one is operating system arings um as you know in in Linux systems it's pretty easy right like doing some service injection capturing some outgoing packets you can just set some IP tables Rule and create a create a queue so you can just capture the ongoing packets modify them and just send it into Q again you can do that on Linux very easily but on the Windows side we generally have some kind of hardenings like let's talk about edrs like let's talk about Falcon you probably cannot uh just inject into this processes even even though you are uh system user on the Windows because they
are running as PPL like protected uh protected process light so you cannot just normally inject into processes in Windows but splank also doesn't have that so in Windows you can inject sulan process if you are using if you're a system right on that Windows host and you can use some tools like Echo Mirage and inject Echo Mirage into the splank process on Windows and you can see the ongoing TCP packets and modify them as well so uh splank should have some OS hardenings too and the last chapter what's our road map so as part of our commitment uh to continuously improve our research uh we have number of plans for future developments and enhancements like uh
this includes we are going to do some common and control Integrations uh we are uh currently working on developing some um addons on let's say Cobalt strike so we can make it a common step on red teaming operations so we can we are we are going to be able to use it with one click uh and we will improve loog slipper we may be some automate wellknown attacks like you can just giving one parameter and you can just run a mimicat attack on on the host you ever want we can we are going to be able to add headers right now we are just um changing the headers but we are also able to add header uh
make it more UI friendly I don't know if if that really doesn't matter uh and we are going to make it more consistent of course but the most excited thing here is I think uh adding this into C2 Frameworks like cob strike so that was my talk uh you can reach out from me and I personally thank thanks to ail uh he's my colleague team Le and I I couldn't make it without him uh he was always supporting me so it's time for questions thank [Applause] you