LightBasin: A Roaming Threat To Telecommunications Companies by Stuart Davis
Show transcript [en]
okay so just uh in terms of introducing myself um so I'm a part of a company's incident response um Team um I have a call later on today a customer was kind enough to call in last night um so working on a particular case with that down in uh another part of the the world so I cover Europe in the Middle East and uh spent nine years in the Middle East and I worked for another company Mandy and I was their director of instant response as well so instant response Friday night seven o'clock you know get the phone call that's that's basically my my job and I do that for clients um and I've been doing that for quite
some time so in the context of this um in what we're going to talk about I'm really going to frame it in terms of the investigation right so like the stuff that we found what happened um so first we'll start with who is the actor so like Basin um so I just start off by saying we we don't know enough about this particular actor right um we wish we knew more about them they're just particularly good at their job so there's a few reasons why you if you've ever heard of um you know things like Wicked Panda or any of these naming fancy bear I don't know you know these names that we give to threat groups different vendors have
different naming conventions they give we have ones when an actress promoted to a certain level because we've known about them for long enough we give them a name and and it's usually aligned to a particular country or motivation whatever it might be here this actor light Basin to be known under various uh other third parties uh onc 1945 some of their toolings would be also under unk2891 and then you've got like other vendors uh th239 as well so basically we're all using loads of characters and you know things because we don't know who they are right well why don't we know who they are well the reason we don't know who they are is they're very good at their job and they
have a they basically maintain a very high standard of operational security when they come in now just put that in context your standard ransomware actor is like a bull in a china shop they will come into a network and you finding out who they are is their goal they leave a notepad text file on your desktop saying this is who I am like you can't actually that's their job is to make sure you know who they are these guys do everything they can to make sure you never even knew they were in your network right so we'll talk a little bit about that okay well what did they use and where do they move around I have 50
slides you will be well informed and there will be caffeine at the end of it don't worry we will get there now they mainly Target telcos but we've actually found them in financial services as well as did one other firm uh but mainly we find them in telcos well why do they care about telcos we'll go through that um as we all know cyber threat groups have motives right ransomware actors want you money you know when you think of North Korea they also want money Bitcoin people have motivations it might be ideological it might be Financial it might be just doing your job right you work in the governments and the government says go hack into that Network and go steal me
some Trade Secrets and you basically go sure thing boss I'll ask no more unless I decide to tell everybody about it and run off and whatever you know so there's always options for that in terms of their abilities um because they're very good at it it's difficult for companies who come in to understand exactly what they did and we'll talk a little bit about that as well all right so their focus and goals as I was saying to you so they've been known to basically focus on telecommunications carrier Network now we talk about vulnerabilities when we think of the parts of networks that really do not get patched it's things like ICS networks this is when
you like so if you have an oil company they'll have an IT Network and then they'll have an OT Network and they they don't like patching the OT stuff because the OT Engineers don't like touching anything it just works don't touch it similarly with your you know ATM infrastructure in a bank you don't like messing around with that lot because it runs a critical you know service for consumers so does your carrier Network your carrier network is the thing that makes all of our phones basically work right it's a little bit complex because not a lot of companies like building all that infrastructure themselves so they basically go to third parties and they say look we'd like that whole you know
mobile thing you can you build it and run it for us and just offer it as a service no problem we'll kind of put our name on it so every every vendor you know uh has those companies in behind providing that we'll talk a little bit about that because that starts introducing a bit of complexity to it as well now this particular actor as you'll kind of see down here um they know that if they're living on the normal place where actors are like Microsoft infrastructure that all of us cool cyber security vendors we're all going to have our super weapons and laser beams and guns because we know Windows super well so these guys are
like I ain't touching that stuff so they live on your Linux they live on your systems that nobody likes to talk about the stuff that we hide behind the cupboards you know we open up once a year we blow the cobwebs off and we're like yeah that's the AIX server so they live in the part of your infrastructure that works operates and probably has an owner that you know Peter and he's very aggressive he never likes you talking about his applications and you stay away from it Peter do you mind if I deploy an antivirus I'm not even going to ask Peter that because he's not going to let me touch them where these guys go to there's no
security tools installed nothing just nothing it's a third party is managing us and rarely do vendors even make antivirus or security products for those types now there are out there are privilege access management tools and some Legacy AV vendors they do support them but most the time when I'm investigating the systems where light Basin goes there's nothing so that basically means free roam okay so we'll talk a little bit about what they care about uh well and and importantly as well not just on the Linux part but also they've kind of been like hey there's also non-linux there's also different types of architectures that maybe we also want to live on just to make this even more
harder and more valuable to us that we can maintain access as you can see here in this website it's not just crowdstrike who cares about this stuff you can see light Basin here being discussed on the opportunities for threat actors on Eric's Erickson's website ever since are pretty big right pretty big company they care about this stuff um they now this is them so I'm not taking any credit for this um this is their view on the kind of what the actors look for you know stealing personal data eavesdropping location tracking selling data fraud disrupting that's kind of like their concerns and their risks that's you know that's their website that's their views that's cool
um but most importantly they write about what like Basin cares about and that's what we're talking about today in terms of the GPRS and the telecoms infrastructure the carrier Network right the thing that keeps your mobile phones working right and I don't mean like Facebook I mean the fellows who make sure that you can talk to Facebook these fellas so the carrier Network a bit like when you become uh experts on OT networks in oil and gas right uh you probably would have heard like famous attacks in the past like shimoon and stuff like that where it impacted uh technically it didn't impact the rot network but it shunned the light on uh the vulnerability oil and gas
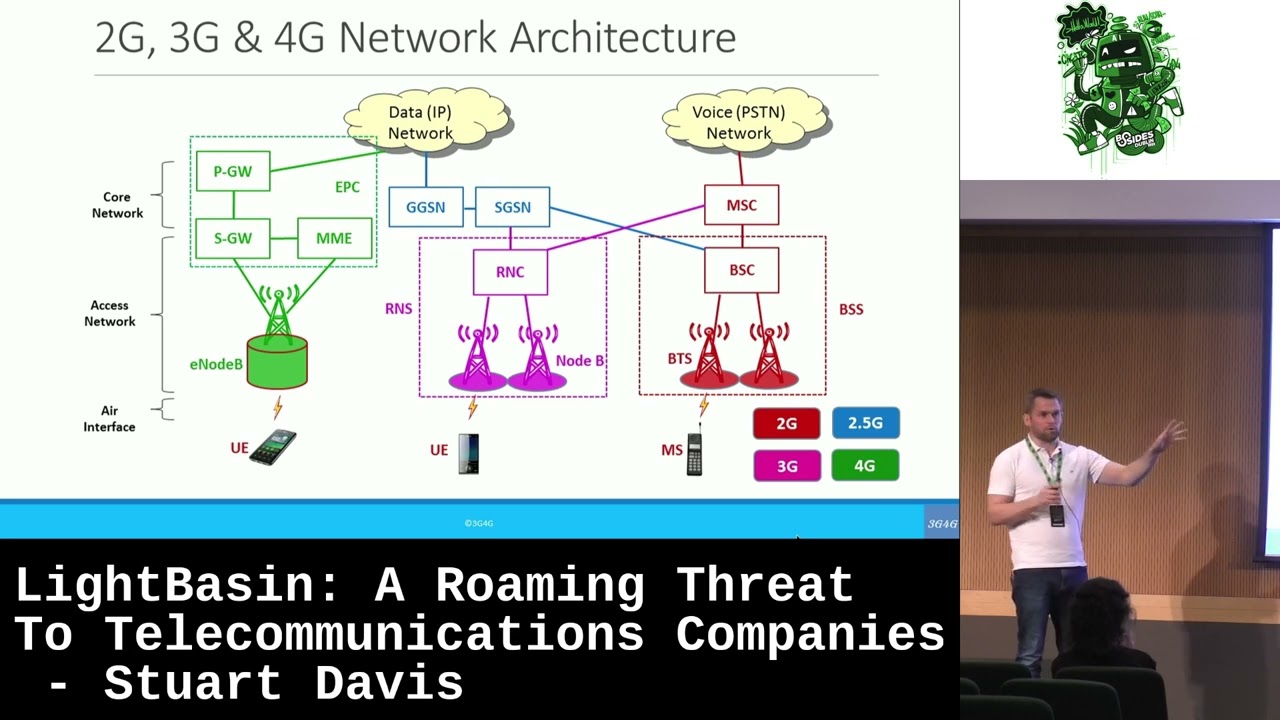
vendors have um when they build their own networks and it's very complicated and no one knows how to protect them similarly with telcos these guys have to build pretty complicated systems you see here the ggsn sjsn they're the two things I want to focus on these allow all of us to walk around roam 2G 3G 4G whatever now 5G and because of this stuff we are able to simply walk around connect to the internet uh start basically browsing seamlessly we take it for granted that this is all here but basically what you have is you have what these under the GPRS for the radio packet switching you have Gateway and supporting systems that allow people
like me and you even if we go over to Turkey we go over to Greece we can get routed back so that these guys can provide the service to us but what this also does along here is it tracks all the billing because like let's let's not kid ourselves right Vodafone air they don't offer a free service they need to give you what you need telephony and 5G and whatever but they need to bill for it now when you Bill you got to keep people's phone numbers who they called how long it was and now I think we can all start figuring out that that's pretty relevant information right who called who and all that type of stuff we
know that from legal law enforcement's ability to intercept that well why don't I just build my own way of doing that so that's what we're focusing on here when we talk about an attacker who's interested in this so they're not interested in just getting into your network and attacking your active directory and then encrypting your systems and asking for payments they want to get into these parts of the network so that they can start then misusing them so we're going to talk a little bit about these systems here this supporting and the Gateway services so the supporting services here basically when you connect it makes the decision of how you're ultimately going to connect back
so that you get your IP addresses you get your access to your internet uh the Gateway ones are for when you're roaming and they're basically keeping a track where you're going so can switch you around if you guys see all the little you know I'm 3G I'm now 5G I'm now H I now have no internet or you know back to 5G that's all kind of happening through here and then this stuff is irrelevant it's just all of the stations you talk to but like what we do when we when we browse to a website we start with a URL and it resolves to an IP address this infrastructure has something like that but it's very complicated but it
supports no matter where you guys walk to no matter where you fly to it supports the resolution back to your original carrier so they can bill you they need the billing information and unfortunately that billing information has some pretty useful stuff for threat actors now there is a concept in this that we need to explain known as idns and edns this here is a grotesque image of how the backbone of the DNS implication works for your phone so when your phone needs to figure out how it has to be registered to one of these uh ggsn or sdsn Services it needs to basically be told uh what's the quickest way and what's this the the
shortest path and it needs to resolve those so every Telco has a set of these idns and edns servers this guy does resolution when you're in the network and this guy resolves external ones this is all about figuring out how are you to be connected back for billing purposes and for the telephony that you're being provided there are some examples of what some of those types of requests look like they happen in the background none of us care about that it all is automatic by your phone it's automatic by services that are providing the 3G and 4G that's pretty messy stuff right all I want you guys to take away from this is in the world of DNS that we all know
about when I go to facebook.com it resolves to an IP address your Telecom infrastructure how you get connected to the internet and the little bar changes that has its own version of that okay and similar to that it um it's shared like the icann it's actually shared as a group of DNS servers and it's put into a an environment known as a grx which is the roaming Exchange that's going to set the scene for us when we refer to grx and stuff like how uh how the actor actually is interested in in accessing data in this environment so now we've got idns edns and we have a basic understanding of what grx is which is the backbone of servers that resolve
how you guys should be connecting back and getting access to your your telephony services no matter where you are in the world that's the most important thing so that environment known as the grx which is this kind of this representation this contains all the adns servers in the world right now the actor in question decided to misuse this so what they've done is because a lot of this infrastructure are just servers right they're providing services and they're doing resolutions they're just built in a different way but they're just Linux servers running SSH protocols they've actually hacked into different telcos and decided well we're just going to live within that interconnected Network so I don't need to get into your Telco
because I'm already in this one so I'll just SSH over to this one move over to that one and I'm in yours I don't need to attack you I don't need to send you a phishing email I don't need to do any of that stuff I'm living in a perfect little environment that there's barely any security there's no monitoring etc etc and I can kind of just connect between these so if I want to Pivot from here to here to here I can be in this Telco and I can move over here Etc obviously we notified all those telcos as any provider was and then they had varying degrees of approaches and responses to it depending
on how they could actually deal with themselves now in terms of the techniques so we've kind of got a little idea all right so these guys attack Telco networks they don't attack Enterprise networks okay we got it right so they're over on this weird carrier Network all telcos have us there's no security products nobody monitors it and mostly it's outsourced now there's three providers who tend to provide that and they have what's known as effectively in oligopoly right there are other providers but they're the biggest ones and they basically offer the best services so most people when they set up a Telco they'll go to them they'll be like hey can you set up my service delivery
platforms my OSS and all these things the telcos need and these guys no problem we have your Billing System we'll have all your access and then the Telco just needs to go off and install base stations and put down lines in the ground and all the really expensive stuff but in terms of that billing part and the the way me and you as all providers the way we get access to our bills the way we get access to just support and like if our phone needs to switch Sims that all has to be managed by these carriers now the threat actors themselves employ a particularly high level of sophistication so if anyone here has heard of would you have heard of the
term again nation state actor has anyone heard that yeah yeah yeah boo anyone who's asleep gotcha um so nation state actor is is typically someone a group of folks that would work at the behest of a Nation right sort of a government right you know the NSA you know different groups like that you know the massage you know you guys have heard of all these right um the Chinese Army uh PLC the the Russian armies GRC the Iranian um and so on so all these different governments have these teams cyber Warriors and they basically come in and they check in every day and they check out they just have its job right they're in the
military nice folks whatever um you know they're nice on equal sides I heard that somewhere before um so these people just do a job they come in they're given a Direction go Target this thing they don't really know what that thing is go get access to it if you find records on it bring them back that's your job go do it and they go off and they do it and they use the same tools or they build new tools you know depends um depends on whether they're a millennial or not right they're Millennial they'll build new tools through old school they'll use the old school tools you know it is what it is so let's talk a little bit about the
attacker and their techniques now I love mytra I'm a very big fan if you don't know what Mitra is it's basically just a way of using language that describes an attack um technique across the life cycle of attack so if you get hacked someone's gonna get into your network move around steal stuff that's a description of you know initial access how they persist how do they steal credentials how do they figure their way a laterally around what did they collect what's exfiltration so it's just a way of describing what the tools were and then if I could describe this if I could put like red for everywhere that your company is really bad at and
green for where you're really good at then you could go off and just fix the red ones because you know you're not good at fishing so go buying a fishing solution you know test fishing and buy fish meat or whatever and then it goes green so um that's attack it's an open source Community they're brilliant for kind of taking feedback and all that stuff so let's go through the different sections then in terms of How It's described in the Mitra piece so that we can make sure that we're um you know we're using that common language and then at the end if you guys have any questions I can also answer it in the context of um you know you might
be like hey they did initial access but is this you know do they do this other types of initial access that's not what you sound like but if you ask me a question I'm assuming you're a talk like that yeah whatever okay just trying to catch you out there um okay so initial access typically we all hear about like companies got hacked because they opened a phishing email I think that's fair that's pretty common you know from a newsworthiness point of view um there's lots of different ways you can get into a company's Network um like there are people who like take USB Keys put malware on it and Scatter it in toilets those people are really at
the bottom of the pecking order of the human race but that could be a way that when someone opens up that and they plug it in and they're like oh there must be something wonderful on this USB stick they get infected and and that's how the initial access occurs yeah that can happen um look I'll credit to people who do that um so it's not hygienic though um so here in this case the actor is more interested in leveraging what you already exposed to the internet like SSH for those who don't know what SSH is just secure shell um you know if you've ever used putty if you've ever used well if you use telnet
it means you're just a little bit older than me um but I'm okay with that um and if you use some sort of newfangled version of Hoodie called Commando putty I don't want to hear about it I don't care um SSH secure shell is basically a command line access with lots of cryptography or adequate cryptography to make a connection between me and you and a tunnel and it's nice and safe ish because it's so lightweight and useful and free everybody uses it like here so Sheldon is like hey there's 18 million SSH servers on the internet that's that's that's a lot right um Lots in the US Lots in China whatever something wrong with that that's
actually very good right because um SSH provides a very affordable and secure way of accessing systems personally myself I always get nervous when I see SSH ports exposed to the internet but whatever I'm just a little bit paranoid here we see light Basin frequently compromises victims through external remote services such as sh they will continue that uh kind of uh let's call it methods by leveraging that within the grx infrastructure which was the roaming infrastructure dedicated to the telcos themselves so not only will they kind of Target your external SSH servers but then when they're in your environment they'll go into the grx and then kind of own that so really SSH they like it big
big fans and to be honest you're going to see why I mean they're all CLI based so pretty cool now what what did we what do we have here what are we displaying here well this is kind of um in the running process on an impacted system this is what you would you'd see right so in the running process you'd see connectivity from that external connection which is the attacker coming back in with the process that they're using they use a lot of malicious software let's call it malware let's get it out onto the floor I'm going to use the word malware all right so malicious software they use a lot of malware they use lots
of different types and some of them are for proxying their connections so that they come in they get connected in and they move laterally within your network this is one way we found them within the environments through the process listings because SSH has log files so it's actually very good you can stick your logs into your sim but these guys are very good at cleaning up their their tracks okay so those logs are usually gone so in some cases where the actor was still active on the system even they were they were just moving around while we were there um and by the way we were we were pretty slow at investigating compared to what
we normally was because we are also in an environment that we're not as familiar with Linux and Solaris and all this stuff so collecting this evidence was a lot harder okay but here we were able to see where they were connecting from and then we were like hey what is this external IP and then we started figuring out oh no they've actually connected from somewhere that's compromised it's owned by another Telco and eventually we started piecing that together and we got the diagram I showed you earlier on so lots there in terms of um how the actor Will gain access SSH is not that difficult to misuse so this is all fake by the way I just
typed this up just in case anyone's gonna if there's any Huawei fans if anyone's going to stand up and say I work for Huawei how dare you I'd be like this is made up relax uh so here it just gives you an example if someone was to decide to use Metasploit and load a just a basic set of passwords and if they were to point it at a lot of carrier Network infrastructure especially internally that password and that username would actually get you access to root on a lot of systems funny story uh there's also other ones just like the other providers their username passwords default ones would get you access to so basically the bad guy knows this they
know that not only is there no security software on this stuff but most of the stuff is all just default passwords why why not because this Telco Network by the way it's very insulated normally it's on this network the grx is protected but it's vulnerable vulnerability it's vulnerable because of that because everyone assumes oh it's it's separate you can't get in but once these actors get in they pretty much own the whole thing so here you can kind of see they um you know just what it would be like for them on their side if they were able to just scan a broad range internally that's how easy it would be for them gaining access
but what if people do change passwords oh no well we'll talk about that as well maybe I'll steal your passwords well how would you do that that's not easy so let's talk a little bit about that now this is a persistence so we said initial access so they scanned your network and they got in uh you know because you're one of the 80 million SSH Services running that's all exposed to the Internet so you know you can just run a little script it's not that difficult um if they get in they persist so persistence is just the term of like how do I maintain access for instance even if somebody rebooted their computer like how do I persist through reboot I don't
know if that's the clinical definition of persistence but it is for me do you know what I mean like if you got onto a computer you were remote desktop you're like oh yeah I can persist and then the computer reboots and you can't I'll be like oh I can't persist I don't have persistence but I shall be persistent to get back um so here we see they use cron jobs and various other built-in Linux commands that allow them to basically tell the computer when you boot back up uh like the the CIS vianit which is the init tab so it's like the first thing that's kicked off by the kernel and it Forks off all the stuff that's booted by the
the Linux computer or the various Unix operating systems so if you can misuse that stuff and again no AV nothing's going to catch this right it's just modifications to it you need to be root granted but they already have root so it's not an issue default passwords usernames um so they're kind of moving around um and they're basically employing persistence methods to get into these jobs and then just renaming Linux binaries outputting off the dev null so you don't see anything and then they're very good at masquerading so that even when the administrator gets back onto their server their STP platform or their whatever and they're you know and they're like everything's working perfectly CPU is fine this server is
helping people make phone calls and billing none of this impacts the system their job is not to like raise CPU and and have people you know like crypto miners when those guys throw crypto miners on your servers and everyone's like oh I found them because the CPU was 100 well done Kudos so here these guys will really ensure that I'm not going to bother you you don't bother me we love a great relationship here no Hub so they're just this is stuff like putting processes in the background so you don't even see it so when the administrator's like hey what's going on you know just I'm I'm feeling Security today as an administrator so I'm going
to check some security stuff he just has kind of pushed it into the background so they're not seeing it and then kind of again misusing the SSH demons you'll kind of see that as a repeating theme also they're like hold on people are really good at like listing out files like the administrator learned cat today so they're going to concatenate you know output the file and oh no they've got me so what let's just have a bit of misdirection and a bit of nesting going on so here you see they've just got like various processes that have well they're configuration files that basically refer to another file it's like hold on a second are you the malicious file or not
no no I'm just going to be a script that refers to this other script and that other script he's going to refer to this other guy ah there you go there's the malicious guy so they kind of recognize that a bit of hiding so this is the bad guy here this is the administrator right he's tired he's we can't see him because he's nested so basically they'll do this for kind of levels of obfuscation again it makes it just harder um for folks to say oh that's kind of known now for most of us we'd say well that actually seems pretty easy well not really you do need to understand how that's going to not stand
out and remember those servers are managed by companies that build those servers their way so it's their software so like the admins should spot like this stuff's off a bit like I've been looking at this server for 19 years like I'll spot these things when they're misspelt so they kind of recognize that and they're like okay we got to do our job to kind of hide keep out of their way not cause any problems now privilege escalation is not about persistence but it's about how do I make myself more privileged like a higher power so I might be that user and I can't do much but I want to be rude right so that's kind of one of their big
goals so a lot of the time they'll employ methods either malware or exploits or malware that runs exploit code um that's one of the things they're very good at in terms of so that there's a there's a vulnerability with uh see that's twice now the vulnerability thing uh vulnerabilities with time commands and the misuse of that it's some race condition stuff and basically it allows them to it's kind of like when we see that tactic being employed on a system we'd be like aha this could be our friends light Basin again um so it's one of the things we look for as what's known as an indicator of attack an indicator of compromise on the
system another thing they do and this is misusing a known vulnerability in a Linux in the Linux commands for time um there's actually loads of write-ups on that by the way like pen testers use this and all that it's it's quite good actually Paul he's not here about his pen tester he could go through that um I don't know if he'd actually use it in his environment um they also use uh certain cow certain exploits right dirty cow is one of them you see here like cve 2016. everyone on the stage was like CV 2022 you know here we are like 2016. that's pretty old oh by the way like this attacker in this environment they were there for four
years my like to my kids aren't four so yeah that's how long they were sitting there doing these things four years put that in context of what have you done for four years you'd be pretty expert at it wouldn't you dirty cow was an exploits um again when we see that being used we would be kind of thinking okay this is probably our friends here um some of the code that is used leaves behind key artifacts so these are the iocs the indicators compromise we look for uh fire fart that's a nice one it's the username so we always like that for a joke so you kind of laugh for 10 seconds and then you get back to the serious nature of
the fact that uh foreign Intruder has invaded into your systems for four years but it's light-heartedness for a good 15 seconds um and then some of the backup files uh so it's like hahaha fire farts oh they have the passwords not so funny so yeah again highs and lows of life firefarge funny name all my passwords bad good bad so these are some of the ways this actor escalates again most of the Telco networks are quite similar granted yeah like there are certain regions in the world where I suppose the security is done a little bit better and now with the Advent of cloud Technologies most of the telcos network they're just kind of pushing all these Services into meshed
API cloud services so basically uh what that means for me is uh when I'm doing my investigations the client is not going to have access to the systems in question and life is going to get worse but whatever we'll talk about that later another thing they do is time stamping uh for those that you know think what this probably means you're pretty much correct it's you know knocking on what the time is to make people think that this happened in a different time that's pretty much time stamping is right so I want to figure out how long the actor was here but if they manipulate the timestamps so that it looks like they were you know the activity was just last
week I would report back to the client this happened last week now that's important versus it happened four years ago actually time is very relevant during an incidents especially to throw off people from that perspective right so one of the other things there in terms of the I'm going to say as we talked about like in terms of misusing some of their um again kind of falsifying the the libraries are basically the services that you guys would expect to see this we would expect some of the administrators if they were auditing through a lot of the the the known file paths this should be um as it's kind of seen here and then you can see the RPC is in a different
directory so they're very conscious that let's put these processes in a different directory and it'll masquerade and that way we can kind of hide so it's a very clever way that we've often seen the actor um trying to hide themselves in in plain size Now log bleach is a super important uh tool that the guys use if you're running around and all these logs are being generated because you're connecting to servers you need a tool that can just wipe all of those logs so loud bleach is a purpose-built tool that these guys have and it's dedicated for wiping their tracks so again demonstrating an intent a proper intent to cover up where they are and this In fairness
I just like it I mean going into the logs and just manipulating the IP addresses that's just respect bad guy respect right um causes all sorts of nightmares in from a forensics point of view but basically what you have is actively taking the time to figure out IP addresses they've used in a log file so don't just delete the whole thing just modify arbits because maybe the administrator is used to seeing 5 000 connections from some known username and we don't want to delete the whole thing because then that's going to tip them off to us so they just go in and they just modify their ones it's just it's it's it's a it's a nice attention to detail and it
it really changes the game in terms of um allowing you to continue your operations also they uh they modify legitimate copies of Ip tables so we found that as well what that allowed them to do was basically allow the access for the edns so the client was like no no no no EDS no no it can't be accessed we're like no no they're manipulating the firewall rules um so yeah it is actually those that connectivity is allowed this is one of the nicest ones it's probably uh it's reported by a lot of the other vendors this basically is they modify the privilege access uh it's an identity management module that's used in Linux to authenticate you so what they do is
they replace the Pam Unix file with this one just put a comma instead of a zero and then anyone that logs into that server they can just siphon off the credentials so now they're just getting hundreds of credentials here you can see them messing around with the shadow file accesses um there's a piece of malware we're going to just talk about now in a second I've only got two minutes left um they do employ impacket which is a library an open source one this is the closest they get to Windows so they'll touch like one window system and they'll just go no no more um cord scan is important here you remember we talked about the GPRS
Network and the connectivity on the grx these guys have manipulated specific binaries so that they can scan ranges of GPRS systems so that they're completely aware at an application Level of the connectivity connectivity between the gpri systems so this allows them to fingerprint you know what's what phones have been registers uh is our connectivity still alive so do we still have connections between all the grx systems so we saw them with a real high intent to maintain this here is a very useful one they scan the whole environment they had an output file here and we gave it to the client and the client was like this actor knows my network better than I do
1556 is for net backup so they scan for you know telnet SSH all the ranges but then they also went after all the net backup servers they used um exploit tools to gain access to net backup and then maintain access on those systems as we said with the SSH movement they love this they tunnel between systems they pivot between them it gives them anonymity and a very and a small level of uh security as well because the connectivity is encrypted I already talked about the impact is so now we're finishing off here in a second uh this is the net backup as I mentioned they use a tool called Sun for me um and one of the things we did see them
focusing on was gaining access across the network to as many of the net backup systems as they could uh they do use blue keep but again that's if they need it in the windows environment and this is another one of the vulnerabilities they use that we saw we had to basically track this ioc that was some of the crashes from the vulnerability and that was how we knew that they were trying to misuse the SS SSH statement process and then we were looking for this and we could see where they were where they weren't uh we also saw them accessing F5 load balancers that kind of caught us off so here's the management interface for the
F5 load balancer so they actually pivoted over and they were on the actual F5 system again after four years I think these guys really wanted to make sure if anyone was going to start removing them from a network they could maintain the access for as long as possible ping pong is a way that they can maintain access so you have to connect so they can listen on on icmp they can listen on IP addresses ports and then for very specific requests that connections to come in uh it will allow uh it'll basically allow your access on uh this is an sdsn emulator like I said before the actor goes out of the way to try and understand at the level of the
GPS connectivity who are the other environments they have another few things that are important in this in terms of identifying mobile phones what are registered what are not so again we did see them targeting specific users specific phone numbers um and these are some of the more command and control persistence um tiny shell is just a pretty well-known open source um it's basically type of remote access tool that allows you to connect back into the environments pretty well used by them um Microsoft's proxies these are things so that they can connect back into the environment and move around laterally similarly with fast Reserve proxy uh this is just one I did want to show you guys and I'll wrap up here after
this one this is one of the tools they'd used this was reported by several vendors as well in terms of a configuration that allows them to encapsulate some TCP like SSH within DNS traffic so I know a lot of people always ask me about oh is DNS the way of exfiltrating and you know I usually don't talk about that much but here I just felt like hey this is gonna honor that conversation where you love the DNS thing so this tool you give it a configuration you give it an IP and you run it and then you can basically tunnel the SSH through the DNS pretty clever is it reliable you know I mean it's pretty
clever uh steel Corgi okay I know I'm over but I do want to say this one and then I'll finish on this slide steel Corgi is one of the tools that the actor used um basically it's an elf binary for dedicated for Linux uh that's my alarm going so I am finished 100 um this guy we found uh being used aggressively by the attacker uh what it allows it's it's it's known in the industry as a Swiss army knife of malicious uh tools why these are all of the options this little tool has when it's running we've seen development of this tool for years uh there's two or three vendors that have published some blogs on it which is pretty good stuff
basically it allows you to import a number of modules and you can do all sorts of things like again targeting the net backup targeting Cisco Systems it gives you reverse engineering tools um packet capture tools so that you can kind of figure out what's on the network uh steal information scan IPS so it's it's kind of a who's who of tools an actor would need within that environment segment um and one of the things we just had to admire was the sheer breadth of the amount of tools that are afforded there so uh this interestingly this tool um is very difficult to research because of some of the anti-forensics that it employs so different versions of it basically meant
you you couldn't decrypt it um we had to actually have access to the system that was impacted um because a specific key that was used to decrypt it was this was directly attributed to the serial ID from the system itself so if you didn't know like if it just went on to virustotal and you didn't know the ID information from the system it's completely useless it's up in virus total everyone can download it they wouldn't be able to reverse Engineers you had to take the malware and the system in question plug them together and then you can finally figure out what was going on so I'll kind of I'm going to stop with that because I am
over um and I'm probably going to say there's no time for questions over there themselves before going coffee oh if there are any questions I'm happy to I'm going to go out and have a coffee anyways so I'd say everybody goes out for coffee and if anyone has any questions I can happily answer them um but yeah thank you very much for your time guys appreciate that





