BSidesBUD2023: A Deeper Look at the Disrupted Bot Farms in Ukraine

Show transcript [en]
okay our next speaker is ready to go anastasias pingios thank you
okay yeah it works okay hello everyone um first of all I know this might be a controversial topic because there is an active war going on so please try to approach it from the technical perspective and um of course what I'm talking about is about Ukraine and Russia but at the same time every single government out there has a similar capability so keep this in mind let's try to remove emotions from this presentation of course it's a personal research it has nothing to do with my employer I think yeah that's pretty obvious and now going back to the main subject let's see can you raise your hand if you know what's happening in this video
okay a couple of hands so what is in this video is the Ukrainian Security Service known as the sbu reading a boat Farm as they call them and that was operated actually by the Russian special services to conduct information operations so this could be the topic of this presentation how this was happening the two sides and of course as we'll see it's not only Russia that's doing that it's a practice that's the that's used by other countries too so on one side we have the Ukrainian sbu if we talk about the actors what happened on the other side and to understand that we need to go a little bit back so we had the Soviet Union with all of
the member states and as you know the KGB was handling anything security related from border control to internal security foreign operations anything you can imagine and for this presentation the most interesting part is this one they call the fifth department they were calling it or political internal security and that transition to what we have today so what happened after the collapse of the Soviet Union there were a lot of iterations to split all of the responsibilities that the kgp had to multiple different agencies and the ones that are more relevant for this talk is the the one you see on the left side is the svr the Fourier intelligence service and the one you see in the
middle is called the FSB the Federal Security Service in theory how it should work is that anything outside of Russia should be handled by the svr anything inside the Russia by the FSB practically it doesn't work like that practically what happened is uh that anything that goes in the former Soviet Union States became a responsibility of the SBR sorry of the FSB so for our talk SBR is entirely out of scope and you see that they didn't mention that all about the G argue that you might be hearing a lot in the news grgu is the military intelligence and why didn't mention that is that grg existed before the Soviet Union and it continues to exist today of course with a
different scope that means for this talk on one side we have the sbu of Ukraine and on the other side we have the FSB with ajru since we have the work going on the fifth service became part of the FSB and all of the informal networks all of the resources everything they had in all of the former member state became responsibility of them and there are also a few other units that are actively involved in the activities I'm going to be covering so when I'm talking about the two sides these are the two sides I'm referring to now in terms of the process so how things actually work for those bot Farms if there are two part practice in
parallel but the one that's more relevant for this talk is this one first the FSB or grgu mainly through this fifth service they Identify some tech survey people that are able to do these things they help them on how to set those up they get the payments either on some sanctioned system or through cryptocurrencies they buy this equipment mainly from Chinese market places that we all know of those are perfectly legal to buy in most countries so there is nothing illegal and they are very cheap from those Marketplace so this is why they buy those there and then they start using them in parallel to that there is also another group of people that they
are not starting with this approach instead they are purely financially motivated they see that they can actually sell the service to both cyber criminals and state actors and they develop those and they rent them out in a pay-as-you-go model this is how the theory works in practice now there is actually very simple it's basically a few computers with some SMS gateways and a few other software to manage those systems some GSM modems that anyone can buy and basically what you see over there you can think of it as each slot it's a separate mobile phone that's the easiest way to describe it and as you see each one of them has a different antenna because they need to
connect to the uh for network and when they connect the phone network they can do anything that any mobile phone can do they can make calls they can send SMS messages they can sign up to internet applications more or less anything that yeah any phone can do they the issue is that they can do it at stale and when we're talking about stale we are talking about large jail this is another example of disrupted operations and you can see what we're talking about and this is the main limiting factor in those activities the amount of SIM cards that you need because each phone number well you can have all of those jet switch but you need a lot of SIM cards
you need packets of SIM cards all of those are from arrays that have happened thousands and thousands of SIM cards so this is one of the hardest thing to acquire to for these operations to run the rest of the equipment is relatively simple but yet this amount of SIM cards it's not that trivial and when it comes to how people install them there is the whole spectrum of what you can imagine from really small installations like what you see here that uh there are maybe I don't know a couple of dozens of devices to uh some other one that they also try to hide it and maybe it's close to the window so that they have better coverage
because again needs to connect to the gsm network and you can also see the art initially cover them with plastic bags so that they are not visible of all of the blinking lights and there are some even smaller ones that can be easily hidden in different places or they have been discovered some more uh yeah Innovative let's say with a lot of Standalone dongles it's dongles again GSM device and even much larger installations like this one where you see all of the dongles uh like uh in a roof so that they can have good coverage and they can be used those things are used for the same purpose so also the other different installations practically it's the same
infrastructure now how they are being used okay we learned who's excuse them what are the two sides what's happening but why do they use them the examples are just there are thousands examples of such activities almost all of them are used to set up fake social media accounts and then whoever controls them either cyber criminals or in this case the example we're seeing is from the Gru and the FSB is either to let's say make real news that are out there more popular let's say it's a story that fits into the Russian plans the Russian media so they are going to propagate it by like sharing it and uh yeah make it more popular the other
is actually sharing their own stories and also creating and operating large group so let's say create a group and suddenly you get thousands of likes in that group a lot of people sharing that so it becomes more popular the other which is the more traditional not only from Russia also the Us and other countries have been doing the same where they are getting involved is to do psychological information operations which means sending Mass SMS messages or calls either with this information or asking people to surrender or like there's going to be an imminent attack you have to move out otherwise to get an enemy and anything you can fit into the side open entire space and those are examples
of what you see on the screenshots on the right a very interesting other use is that cover Communications channel so basically when they have a group that they don't want to be associated with operators from Russia or vice versa they can use this as a proxy some more or less have those as intermediate so that you don't know who is on the other side you only know up to the first hope and again they can be used to set up telegram channels and other things a very interesting case because this one quite a few military operations the moment operations were happening those were used to do the denial of service attacks and flooding attacks on a
government service so let's say for instance there is a city that's going to be raided and you start the denial of service attack on all of the emergency response numbers of that City so which means if people try to reach them they will not be able to reach them this is another user has been seen from those the other is of course the target specific individuals basically to hack them so send them let's say facing links send them SMS messages with malware more or less ways to uh yeah to get access their devices and of course at the moment Ukraine I don't know how many know that but there is an extreme amount of censorship
because of course they want to control what goes out of the country because there is a lot of well there is a work going on so some of these people also sell those to specific groups inside Ukraine to bypass all of this control and go directly to the internet again use them as proxies so pretty massive amount of different use cases and oh yeah sorry and they had a translation of what those means in case anyone wants to see it is a very traditional side of messages you will find them in any world any country uses the same approach so it's nothing unusual the unusual part is the technical implementation of all that of course all of that has some some
limitations so first of all as I mentioned it needs a lot of SIM cards thousands and thousands of them and also even if you have all of the setup you still need to know who to Target who are you going to send this message to so somehow you also want to collect a lot of lists of Target phone numbers and of course this is not done by the people that operate the infrastructure as I mentioned those are paid for for this service all of that part is done by the people that are using this infrastructure that are typically the Russian special services for this scenario and the other part is that they are relatively easy to discover if you are a
government of a country if you operate all of the communication providers it's not as hard to pick up that in a certain region suddenly you have 20 000 new mobile phones popping up in the in the j7 not to mention if you just have other people say doing patrols with a emcee catchers and suddenly they see in an area a huge amount of phones again it's not that hard to find those out but at the same time it's really cheap and um and fast to set those up so yeah and the other part that is not limited to this operation but generally the information operation space it's really hard to measure the success so let's say
that you use this you send out spam messages to everyone living in that region how do you know that it worked in some examples they might have cases that say Okay x amount of people went back to us and they want to become informants or whatever by us I mean the Russians in this scenario as The Operators but in general it's very hard to measure the success of that actually in the US they are trying a different model which is when they send information operation messages at the same time to monitor the activity of those users to see if it changed their behavior in any way I I don't know if Russians are doing something similar
maybe they and the other is for anyone to get recruited and operate something like that they need to have a certain level of technical expertise it's not anything extremely so but still it's not something that the average citizen could do easily and now on the main topic of the presentation so throughout this time the spq has been publicizing anytime they disrupt these networks apparently because it is a good demonstrate to what they are doing why they're doing that and that gives us an insight into the scale of this activity so since February 2022 and that's of course when the invasions are Invasion certainly this is why I started with this statistic there were 47 such networks and the spq calls them
both firms technically they are like cellular networks that operate outside of the telecommunication provider in total they had over 2 million online accounts and over 65 000 SIM cards that were being used and in case you wonder like how they are separated it's more or less in every major city of the country so it's not isolated a certain area now the interesting part is not this one because this is I assume expected the issue is what happened before February 2022 and actually such networks have been getting disrupted for quite some time and till since 2020 and basically so two years before uh anything happened in terms of the invasion and uh it was interesting to see what
they were being used for and uh some depending on the region the whole point it was to create uh divisive subjects and the Very progression view to the local population so for instance when there was a lot of division over the vaccination there were a lot of messages related to covet like for instance do the vaccination or not do the vaccination depending on the audience or for instance in the local Adonis correction it was again that those need to get support from Russia in order to become autonomous region a lot of these messages so you can think of it the whole point of course how to get more people on board on these topics a very clear
example of information operations actually and if we map those two from 2020 you can see that um yeah there are a few more regions also including Lucan Indonesia didn't have any before that actually the latest one that was disrupted was only two weeks ago and in 2023 because it's not really visible from that graph there have been three disruptions so far and yeah the vast majority you see 37.5 is in here and on average we're talking about 9 300 SIM cards per uh per Farm almost all of them are used for this kind of things that I mentioned the formation operations and psychological operations but there are a few of them that's the exception that they are used
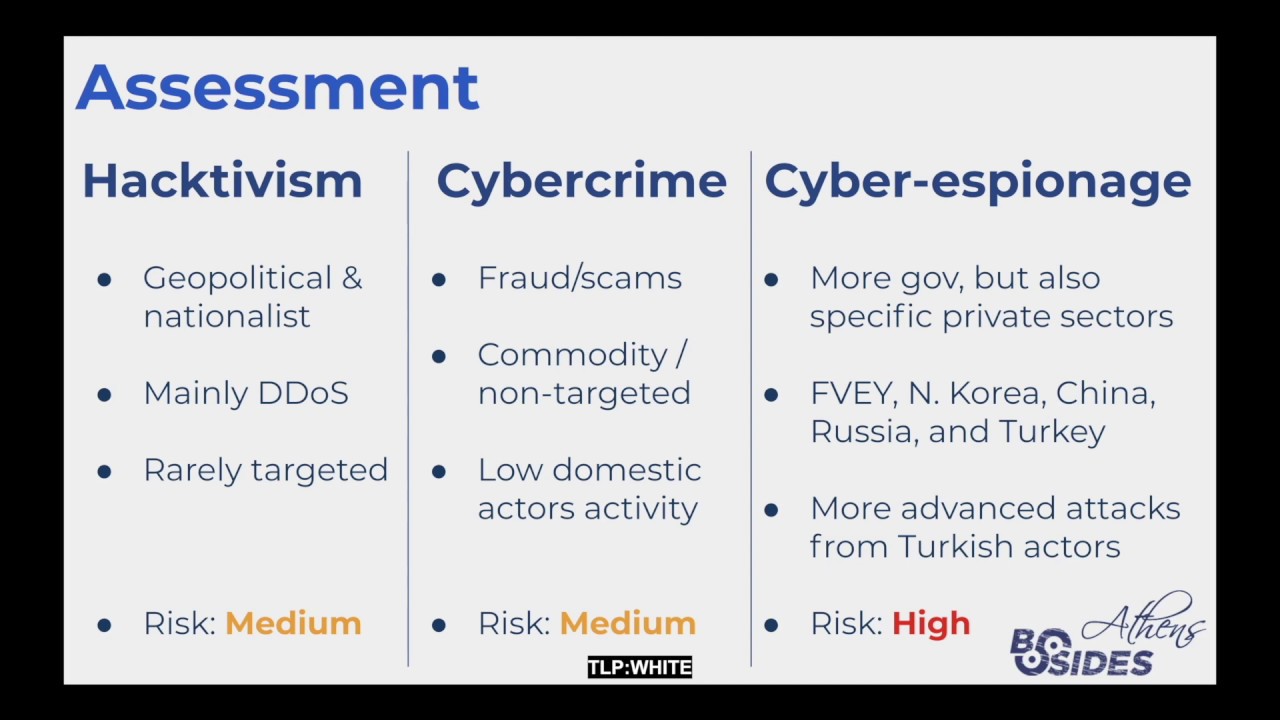
for all of the other scenarios that I mentioned proxies cover communication channels and so on but okay I cover how this works but is this actually known hasn't been used before that and the reality is yes so I found this change from 2017 where the Turkish spy agency called mid they were using exact same setup to have a cover Communication channel in Egypt and it was disrupted by the Egyptian government and also a very similar one in 2016 and 2020 in Pakistan again the borders with uh um it was used for activities in the borders with India so it is nothing new it's not only Russia that's doing that it looks like it's a wider practice
now other other countries using that maybe maybe a topic for future research or somebody in here if they want to look into that and another interesting part of this one is uh this this is actively being discussed in the British government it's an open consultation called preventing the use of sim farms for fraud and they want to regulate any sort of GSM device that can accept more than four SIM cards you can see it on the topics on the bottom here there will test our plan is to apply the measure only to devices with more than four slots and the interesting part this year that they say that they have observed in the UK those devices being used to send scam
messages around scam call campaigns and post misleading false or facing messages on social media in bulk so you can also see that's not only used for State actors activities also good for cyber criminals and also not only in Warzone but even in the United Kingdom and if you have been following the news and you saw the recent leaks of the U.S government well the alleged Elixir it's the court hasn't complete on that case yet you might have also seen this document that is quite interesting and as you see on the left here that's the Insignia of the U.S cyber command and this is the counterpart from Ukraine and they have this what's called refining information operation capabilities via
social media manipulation tool and they refer that Russia is is operating a tool built-in-house called Fabrica that is managing a network of hundreds of thousands of social media both emulating users to evade detection and manipulate the information environment potentially could be the Management console of these both forms that I talked about of course there is no Tech that connects this to the bot Farms but logically speaking it sounds like a plausible scenario basket so there are a lot of unknowns and there is a lot of space for additional research so everyone is welcome to contribute to that and we thought yeah thanks a lot and if you want to reach out to me of course
you can do it here or in any of those links listing this slide anastasios thank you very much do we do we have any do you have any questions at this time we do
very good presentation thank you you mentioned that there are thoughts on how to prevent using these Sim forms as as a these Bots to to prevent these information operations but these are the end devices that are used to initiate it is there are there any countermeasures on the user account levels on the social platforms that are being used to to detect these fake accounts and and prevent them from being used that could be well on the real end user so if we're talking about let's say the recipient I would say it's very tricky because uh you cannot really know if an account is legitimate or not on the social media platforms and maybe but they don't have access to this
information I assume that that this jail they have some automation I also assume based on my experience on dealing with boats in all of my professional career that they try to randomize the figure prints now how far are they going to that and in especially on social media platforms they always have this balance of finding boats and killing them and then keeping that balance to not telling real legitimate users so it's yeah I know these days they're using a lot of Technologies and machine learning smarter 3D prints taking more variables into account but I have no idea how is this going to be the easiest part is for a telecommunication providers that get the the initial stage of that when those
device connect to the network thank you anybody with anything else at this time okay you can reach out to an Associates at any time during the day and you'll be able to reach him also by email again anastasias thank you very much thank you