Analysis of the GR TLD Cyber Espionage Operation

Show transcript [en]
Hi everyone and thank you for attending my talk. This is a presentation about the Cyber Espionage Operation against Greece from 2019. The disclaimer of course, this is a personal research, it has nothing to do with my employer and the analysis is limited purely on publicly available information. This is a little bit of information about me and this is what I'm going to be covering today. Let's start with the TLDs. On the top we have the root level domain and underneath we have the TLDs, the top level domains like .gr, .com and so on. Then we have the second level domains like BCH, Athens, Ministry of Foreign Affairs and so on. And finally the subdomains like .tab, .tab, .tab, .webmail and so on. What we care about for this talk
is the TLDs. And more precisely, we care about the test TLDs and the country code TLDs. The reason is that in 2019, the .L and .GR TLDs were taken over. Both of them are managed by Forth ICS. And if you ask yourself, why would someone target a TLD? There are many reasons, but to summarize it to two major points: On the up side, it can enable all sorts of cyber operations, from man-in-the-middle attacks all the way to supply chain, waterhole attacks and many others. Of course on the down side, it is very trivial to detect. Even with limited access you can monitor for DNS changes and identify these kinds of attacks and from the defender's perspective it is also equally easy to mitigate them. You just have to
revert the changes that were made. Now let's move on to the operation. The first time that this attack became known to the general public was in April 19th 2019 with this data breach notification from 4th ICS to owners of .L and .GR domain names. This notification was saying that there was a data breach on systems managing the .GR and .L TLDs, that it was part of a global campaign targeting TLD infrastructure and that there was no leak of personal information. It says then that 4th ICS reverted those changes and an important point is this one that they changed the password reset process. Now if we move a little bit later in that year, in July 9th 2019 we have this post from Cisco Talos. In this blog
post Talos team attributed this operation to a threat actor they were tracking as C-Turtle and they also stated that they maintained access until at least April 24th Also that the threat actor searched for PHP proxy tool and DNS hijacking tools on Cisco Talos blog and UK government's NCSE. And as a mitigation step, Talos recommended multi-factor authentication and strong authentication for VPN and ccTLD management systems. On the bottom right is a map of the victim countries and this was also the first time where we get to see some technical indicators. So using those indicators, we can start our technical analysis. The threat actor had set up some DNS servers that they controlled and this is what they were using to deliver their attacks. Specifically for Greece,
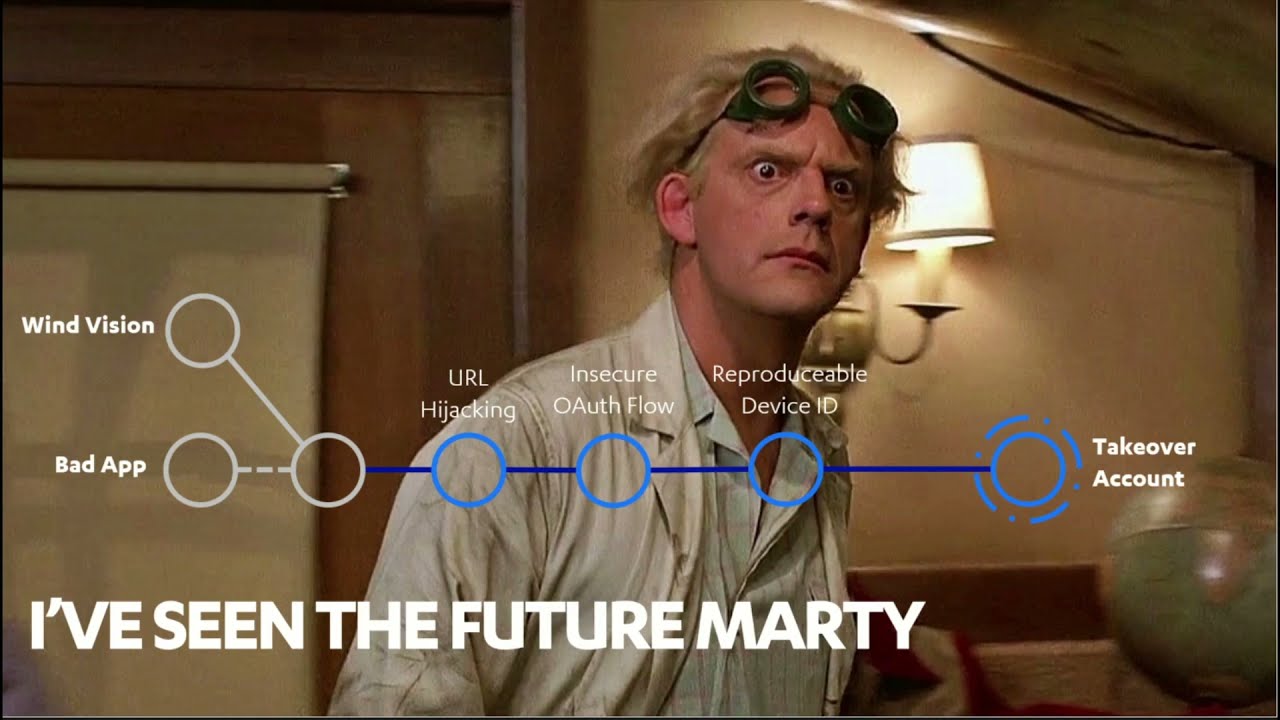
there were three separate hosts that were set up to target different domains. Those were the hosts along with some contextual information. The domains that were targeted is the police webmail, astinomia.gr, the Ministry of Foreign Affairs and the Parliament and Ministry of Foreign Affairs. In terms of the step to execute this operation, first the adversaries were taking over a management account for those TLDs, then they were updating the DNS servers on the target second level domains like mfa.gr for example, with a DNS server controlled by the third actor, Since they had access to the domain, they could issue a TLA certificate, and this is exactly what they were doing using a certificate authority that was not normally used by this domain.
And finally, they were updating specific subdomain records in order to perform man-in-the-middle attack, in order to steal credentials and access the mail servers. If we do a link analysis of the operation against Greece, we will end up with something like this. Something that stands out is this one, that on the webmail.astinomia.gr a different certificate authority was used. However, after checking multiple operations of this redactor, I can tell you that this is not unusual. Although their default was the Let's Encrypt Certificate Authority, they have been seen using different certificate authorities on different targets. And continue with the technical analysis, we move to the timeline analysis. What you see here on the upper part are the many
in the middle attacks and the notifications and on the lower part we have the attacker controlled infrastructure. So the DNS servers and the hosts that were stealing the credentials from those domains. It's worth noting that the DNS server was live throughout the entire operation while there were separate hosts set up for each of the targets. Another important point is the order of the targets. If you recall what I mentioned earlier, when you're doing a TLD takeover, you don't have a lot of time, so you have to be very careful about what are your priorities, which targets you are going to be hitting first. And what we see here is that the top priority was the
Hellenic police, followed by the Ministry of Foreign Affairs and for a very short period of time, the Greek parliament. This prioritization can help us understand the motivation of this threat actor. And here is why. Here you see the login pages of the Ministry of Foreign Affairs as it is today and the Astinomia.gr, the police website. Also we see that the MFA now supports multi-factor authentication. But since Astinomia.gr was the first target, let's have a closer look on this one. In both the current webmail page and the 2019 webmail page, we see something that stands out. There is a drop-down box. And if we open this up, we will see that this webmail portal, it is
not only for the police website, but instead it's for all of those domains. And if you wonder what are all of those domains, the first ones are indeed the police, but then we have the Ministry of Public Order and Citizen Protection, then the National Passport and Secure Document Center, Then the European Union's SIRIN program, the Center for Security Studies, the Asylum Service and finally the National Coordination Center for Border Control, Immigration and Asylum. So this is probably why this was the highest priority target for this adversary. And based on this quick technical analysis, we can drive some conclusions. First of all that we are talking about a targeted cyber operation with specific hosts targeting specific TLDs and specific subdomains. Second of all, that
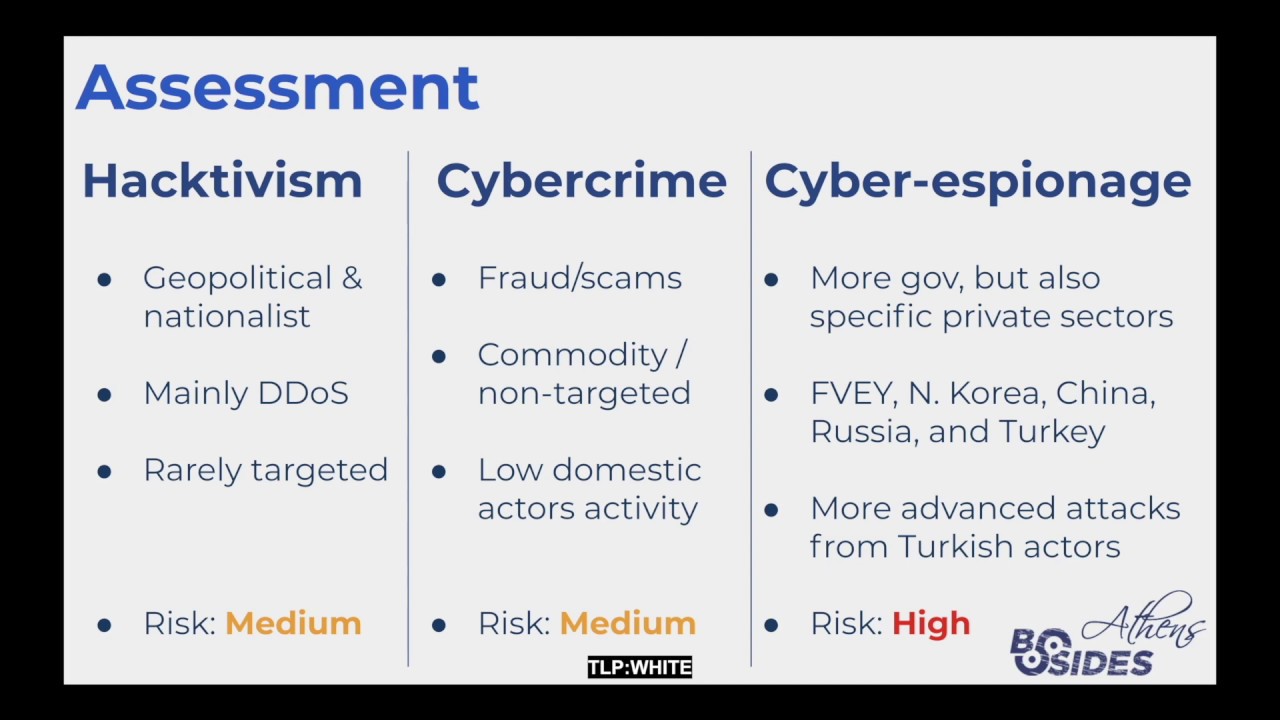
the focus was Greek government entities which could be valuable for a foreign nation state. Then, that the threat actor made a few opsec mistakes, like reusing the same DNS servers, searching for proxying DNS hijacking techniques from the same operational servers, and similar smaller mistakes. and more importantly, based on the order and the length of the compromise, we can assess that the main targets were the Ministry of Public Order and Citizen Protection along with all of the related organizations, followed by the Ministry of Foreign Affairs of Greece, almost certainly for intelligence collection, especially since there was no destructive operation that we know of. And now that we cover the basics of the technical analysis, let's move to the second part, the intelligence analysis. In January
of 2020, Reuters published this news post. And in this news post, we're reading this quote: "According to two British officials and one US official, the activity bears the hallmarks of a state-backed cyber-espionage operation conducted to advance Turkish interests. The official said that conclusion was based on three elements: the identities and locations of the victims, which included governments of countries that were geopolitically significant to Turkey, similarities to previous attacks that they say used infrastructure registered from Turkey, and information contained in confidential intelligence assessments that they declined to detail. Now, from our side, we can only validate one of these three elements, and that is the identities and location of the victims. the other two are information that we don't have access to.
So this is exactly what I did. I tried to identify all of the operations up to the point of the attack in Greece based on the indicators that were released by Cisco Talos. And this was the result of that. If we go through them, indeed most of them align with Turkish interests at that point, especially if we consider the conflicts in Libya and the East Mediterranean crisis. For example, targeting of the National Oil Corporation in Egypt and Libya, or targeting Cyprus and Greece. But at the same time, there are some targets that don't fit into that picture. And to complicate matters even more, there was something else that happened around the same time. This is
the avatar of a hacktivist known as ReadMyLips. This hacktivist has been providing really high quality information for the Ministry of Intelligence of Iran. And these are some of the alliances that different security vendors are using for the Ministry of Intelligence of Iran. In one of those leaks around that time, we saw a clear overlap on tactics, techniques and procedures An overlap even in the IP addresses that were used in those operations and an overlap on many targets with the victims shown in the previous table. More precisely, there were two specific leaks that stand out. It is those two over here. The first one from March 27th 2019 for a tool called DN-Espionage and the second one from April 3rd 2019 which was a series of indicators of compromise
that were actually servers operated by the Ministry of Intelligence of Iran. Within those indicators of compromise we find some IP addresses that are matching exactly with the operations shown in the previous table. So in order to continue with this analysis, I followed a classic structural analytic technique known as the ACH, the analysis of competing hypotheses. Unfortunately, we don't have a lot of time to go into all of the details, but basically, here is how ACH works. You first start by defining as many hypotheses as you can possibly imagine. Then you try to find evidence that disprove those hypotheses. Your goal here is to disprove them, not prove them. Then you do the diagnostics, which is where you create a table
and you put all of that information in and you start ordering this information. Then we move to the refinement, where we remove any hypotheses that are clearly disproved. On step 5, we are looking for inconsistency, which means making assessments based on the likelihood of this hypothesis. Then we have the sensitivity, which is appropriately weighting different evidence and making an evaluation. And finally, we have the conclusions and the evaluation. So in my case, I started with 7 different hypotheses and eventually I ended with those 3. the evidence that really stood out during this process were the supporting indicators of compromise, if it was geopolitically reasonable for this threat actor to be doing that, if this threat actor had any known cyber capabilities, if there
were media reports about it, if there is a target alignment between the targets that we see and the targets that this threat actor would have at that point, if there were past operations that were aligning, if there was any threat intelligence reporting, supporting or disproving that, and finally if there are any confidential sources being referenced like the ones mentioned from the Reuters. Based on this ACH analysis, the top three hypotheses that stand out are those three. The first one that Turkish MIT, the foreign intelligence service, was behind the operation, The second one that was Iran's Ministry of Intelligence that was behind the operation. And the third one that was a joint operation between Iran's MIS and Turkey's MIT. Even if we look in the
future, after this operation happened, we see a similar pattern. For example, in July 2020, an APT35 server was discovered and APT35 is associated with the Iranian nation state and in there, there were attacks against Greek Navy officers. In a similar manner, we have also seen multiple attacks originating from Turkey. And it's worth highlighting that in October 27th 2020, a question was raised to the European Parliament with the subject of "Countering cyber attacks by Turkey and Iran" and referencing some of those operations. So considering all of that, if we had to make an attribution statement, unfortunately it wouldn't be something simple. It could be something like this: Based on the limited amount of publicly available information, it's assessed with low to medium
confidence that the Turkish Intelligence Agency was likely the one behind the operation. There are evidence that align with tradecraft previously observed by Iranian-MIS operation, but it cannot be determined if it was an MIS operation or an MIT-MIS joint operation, which is plausible since MIT, unlike MIS, has not demonstrated such capabilities and they have collaborated in other operations in the past. And this is the end of my talk and some takeaways that I want to highlight is that attribution is hard, especially when you have such limited amount of information, that intelligence agencies are not standalone islands. They collaborate, they share tradecraft and sometimes they also steal tradecraft from each other. Unfortunately, there was no official statements or technical analysis
published by Greek authorities, which makes it impossible to make any reasonable assessment on the impact to Greek national security. Of course, we can make some assessments on how this intelligence was exploited, but there is no way to be certain about it with the information that we currently have. And if you have any questions, now is a good time to ask them. Also, feel free to reach out to me on LinkedIn or Twitter for anything else. Thank you.