Threat Landscape: Greece
Show transcript [en]
Hello everyone and thanks for joining. I am Anastasios and I will be talking about the threat landscape in Greece. There are a few different ways to deliver a threat landscape. In this case I chose the historical approach which means looking at what has happened in the past and based on that making some assumptions for the future. As you can probably guess everything I'm going to talk about is my personal research and it is not related by any means to my employer. Now about me, I'm a Principal Security Engineer at Booking.com. I spent some time also contributing to the MITRE ATT&CK framework and some of you might have known me from a blog I used to have some time ago or Twitter. And for the last probably five years I
have been spending more and more time on the intelligence side. I have attended a few different trainings and certifications and that was quite useful for this specific presentation. Now on the format I'm going to be having for the presentation. First of all it is the sources that I used, then it is the process I followed, and then the analysis split in three different sections: activists, cybercrime and cyberespionage. Lastly it's a quick assessment. And the important part for this one is to make sure we all speak the same language. So when I'm referring to hacktivism, I'm talking about threat actors using hatching techniques in order to promote some ideological point. In cybercrime it is using hatching techniques for financial profit. And in the cyberespionage, it
is typically nation-state actors that try to obtain access to some information.
Now, on the sources that I used, they were very diverse and it was very hard to categorize them as a whole, so what I did is I list them as broad categories under the open source intelligence of OSINT. So, there were news outlets and media, social media groups, some forums, hacking forums, forums from cybercrime groups, hacktivist groups, also some blog posts from security researchers and security companies. Some of the content, especially the historical content, it was removed, not longer available, so I had to go back to archived web content. And malware repositories for the cybercrime was also a good source. I want to highlight a few of them. First of all, the Hellenic Police publish every year
statistics for cybercrime, which is quite handy. Safeline.gr publish reports on cyber-related complaints that they get for Greece. In Zone H you can find most of the well-known hacktivist groups where they are sharing what kind of attacks they have done recently and what did they manage to do. And for cyber espionage there are quite a few books that go through different periods of time and they explain what kind of operations were going on at that time. As you can imagine, I can be more specific if you ask me afterwards, but this gives you a broad understanding of the sources that I used. And to be clear, all of the sources mentioned in this presentation are open sources, which has the downside that there might also be a lot
of activity that is not covered in this presentation because it's not publicly available. On the process that I used, it was the intelligence cycle which has been around for decades and the last few probably 10 years has been adapted also on the cyber side with the cyber threat intelligence. The first part is the planning and direction which in this case it was very clear. We have these different categories and we need to identify the threats that have happened in the past for Greece. The collection was to collect as many incidents from the sources I mentioned earlier as possible for as long back as possible. The processing in this case, it was categorizing all of them in spreadsheets and they were in total a few thousands and
then creating different tags for them and try to make it something useful. That was the processing and exploitation. Then the analysis, it was the actual manual process where I had to go through all of this content and try to summarize it in a way that can provide some insights. And the dissemination is this presentation. I'm sharing my outcomes with you. And I would really really appreciate if you give me some feedback afterwards since I might be missing some important points or I might have misinterpreted something so please any feedback is very very helpful for me. Now going on the hacktivism. The very first hacktivism case was in 1993, when a group of people hacked the national recent center called Democritos and the network that
was named Ariadne in there. And they informed the media about it and it reached quite some publicity at this point. And we can consider it purely based on the definition of hacktivism as the first act of hacktivism. The interesting part is that from the early 90s to the late 90s it was the time when more and more groups started forming in Greece and they started doing a lot of defacement attacks. You can see one of them in the Ministry of Education in 1998 and more of these followed through 90s and early 2000 with a widespread of targets. Typically it was government websites and celebrity websites. And the motivation was either to prove that these groups exist,
saying that we are here and we can do that, or in most occasions it was opposing against a new regulation or a new government decision. What has changed? It was from the 2000 era until 2010, we started seeing some groups having heavily nationalistic motivation. And it was also the time when we started seeing Greece being targeted by foreign groups, mostly same nationalist groups from Turkey. And you started seeing this form of a fight between hacktivists in Greece and hacktivists in Turkey. And some of them, that leads us to today, they have evolved to a situation where almost all of their targets are hatching each other, like promoting one view versus the other. The most interesting change that has been
happening in the later years, so 2010 to 2020, it is some of the hacktivism groups in Greece collaborating with international groups in that space, like Anonymous, and also participating in wider movements, again like some anonymous operations that do not directly affect Greece but because there is anonymous Greece groups they participate in those and if we have to draw some trends throughout the time looking at that we see groups becoming more and more organized and more and more connected to foreign groups We see that the C-level still remains relatively low, so as most of the companies and organizations have better security, we rarely see website defacements anymore and data leaks. What we see is a simple denial of
service attacks where people either buy this as a service or they use some very simple type of tool that's publicly available to execute them. Another change from the 2000s was that Greece has been targeted by both foreign groups and domestic groups, although the majority remains geopolitical and nationalist motivation. You very rarely see activism attacks that are not driven by this. Moving on the cybercrime side, it was very hard to find information from specific targets. As you can imagine, a lot of companies don't disclose this information. But in 2004, one bank in Greece disclosed a public report on how they stopped some account takeover attacks. And this is one of the earliest reports that I was able to find. That also matches
with if you consider the adoption rate of internet connected businesses in Greece that was not so high until later in 2010 and 2015. That also reflects in some statistics, this is from the union of IT and telecommunication companies in Greece from 2008 to 2011 and what you see on the second from the top statistic is about cybercrime and it goes from 0 to 25% That is not actually realistic, but what is happening is that more and more companies started reporting on the cybercrime cases they have and they started having actual security teams to do something about it. And this is what we see in the cybercrime in Greece around that period, that it was the time
when it started becoming a thing. Moving to later in 2000 and 2015, we saw Greece getting hit by some cybercrime campaigns but usually it was indirect. Like in this case, this is from 2014 when the first mobile encrypted token was released and Greece had a 6% impact from that, it was one of the, let's say, top targets. However, if you check other very very popular malware families, you will see that Greece usually is not even in the top 10 or top 20. And if you think about it, if you have been in any of these forums where these groups are interacting with each other, it kind of makes sense since most of these groups want to have the biggest amount of profit without a lot of customizations in their
malware campaigns, which means targeting English-speaking countries, or countries that have, let's say, some banks that are international and they also affect them. So when you are talking about the smaller country like Greece with a different language, a lot of businesses that are local to Greece, they are not international businesses, you need to make a lot of customized malware. And it is not very common. I had a few entries that had this, but it was the exception, not the rule. And the same also applies to today, so this statistic from Satista, it was about Europe and the most and least secure countries, and again Greece was in the lower end of that, both in not being very secure or really insecure, but also not being heavily targeted. And
if we have to look at trends for that, what you see is that Greece is not an attractive target for cybercriminals, When it is getting targeted, and of course it does happen, it is usually due to commodity cybercrime attacks that also happen to get to Greece, but it is not the main target. Very low activity from domestic groups. If you check for people being prosecuted or arrested for cybercrime, there are a handful of cases. And what is typically happening where you see a huge spike, it is scams and frauds. talking about the business abuse cases or anything from people tricking others into tricking victims into sending them money things like this so these are still the most traditional if
we can consider it cyber crime attacks that are happening in Greece moving on the cyber espionage side it is more on the nation-state threat actors as you can imagine And most of the people in Greece are already familiar with the 2004 case where it was discovered that the US government had compromised one of the biggest telecommunication providers and they were using that to monitor some target mobile phones, all of the communications. If you haven't read it, it's actually a very interesting case. However, when Snowden leaked all of his content, we also learned about a whole 5i project and 5i is an agreement between five countries. Those are the USA, United Kingdom, Australia, New Zealand and Canada, where they are collaborating closely
on intelligence operation and intelligence sharing. And the 5i's from early 2000, they had a I had a target telecommunication providers in Greece for mass surveillance and that was one of the very earliest cyber side events that I was able to find. Now, Five Eyes have been targeting Greece throughout history. We can see that all along so I didn't include many more information on that but you can look on your own. What we see in 2005-2010 is some activity from Chinese speaking nation states redactors. Also one single case from North Korea which is the Dark Hotel case but I want to highlight this one due to the position that Greece has. So Greece is in a very key position, it's like a hub and also
it's a very popular tourist destination. Now if you think that a nation state wants to monitor some certain people, some certain targets, and these targets happen to go through Greece or stay in Greece, then Greece suddenly becomes a target. So it is a lot of cases that Greece has been targeted indirectly like that in some of these operations. However, from 2005 we started seeing a lot of cyber espionage operations from Russian groups, Russian officially attributed groups. Like in this case NetTraveler, it was targeting government and diplomatic missions and there were many more... We can talk about this later if you're interested. And we also saw some Chinese groups targeting Greece and that is quite interesting since
if you consider all of the geopolitical changes with China and all of the investments that were happening at that time, it is reasonable to think that these nation-state actors would be interested to know what they are getting themselves into before they make any big investment. From 2010-2015, lots of activity from Russian-speaking thread actors, I included two of them here, mostly targeting government, but also some critical infrastructure, especially in telecommunication. And there was another interesting leak at that point, again from Five Eyes, this time from the UK government, of another program they had, surveillance program, called Tempora, where Greece was also part of their targets in this case and again that was telecommunication providers that they had to intercept all of the traffic in
order to perform mass surveillance. And lastly going to the current situation again Russian threat actors are still very active but also in 2020 it was the first time where we actually saw in January a Turkish nation state attack being officially attributed to Turkey. Many many news reports like this one is from Reuters you see here attribute this attack to Turkey. What has happened was a DNS hijacking attack in various government websites that happened in 2019 if I remember correctly. And another interesting point is that A lot of attacks from nation-state threat actors didn't even use in 2015-2020 Greece directly but they were using it as an auxiliary, so both energetic bear in this case but also the NSA in another
leak from Snowden. They were compromising universities and telecommunication providers and using them as a proxies in order to deliver attacks to their actual targets. Now if we check for trends, you would see there are a few different countries that have targeted Greece from time to time. The only country that has been increasing operations based on open sources is Russia, which is quite interesting also thinking about the geopolitical situation in Greece with Libya, Syria, Turkey, all of the tensions in the region. And a very interesting point, again, considering the current situation with the tension that is happening, it is that we had the first actual advanced attack from a nation-state threat actor that is sponsored likely by Turkey, at least based on a lot of reputable
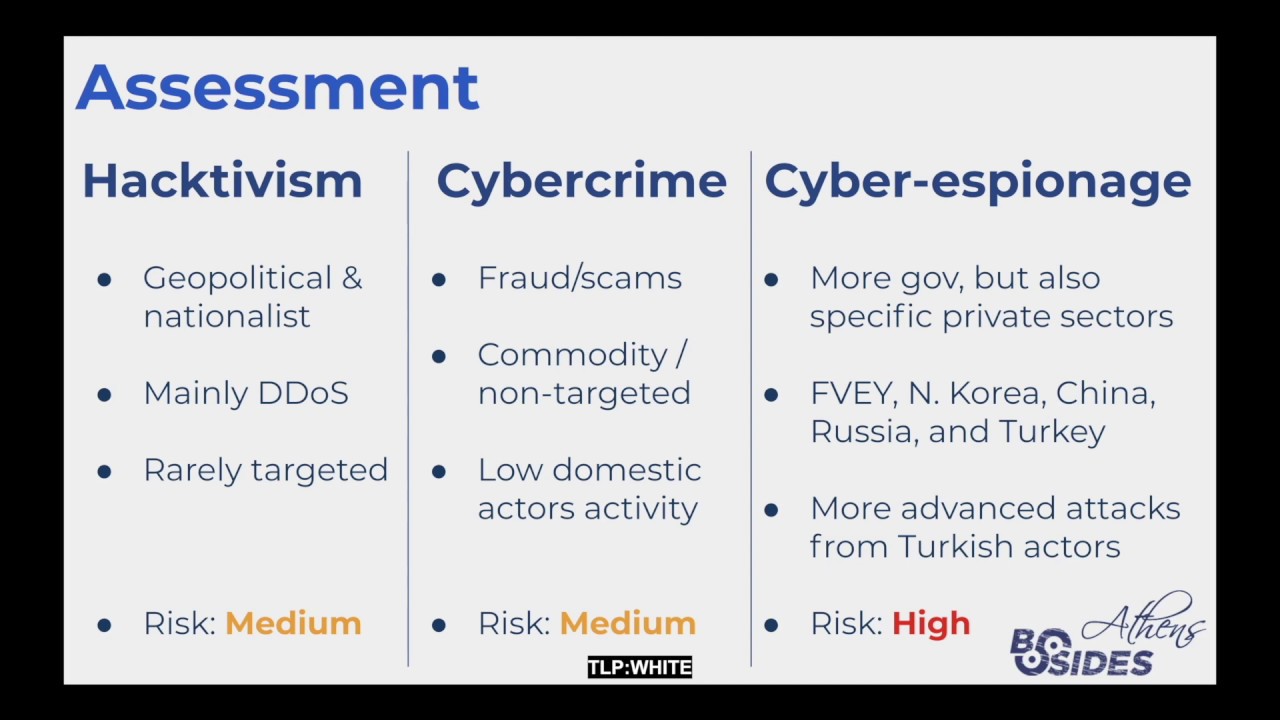
sources. And lastly, in most of the attacks, the target has been government and diplomatic missions from different countries that are located in Greece. But especially on the critical infrastructure it is also a common target. Other areas have also been targeted from time to time, like I mentioned with Dark Hotel, that was the hotels actually targeted. But the main target still remains government and critical infrastructure. Now to make some judgement for the future, here is a quick assessment. On the hacktivism, the motivation is mostly nationalist movements and geopolitical changes, which means when you see a lot of tensions and geopolitical changes, especially between Greece and Turkey, you should be expecting an increase in hacktivism activity. The skill level is quite low, which means that the majority of the attacks
are denial of service attacks. and for the same reason they are very rarely targeted. Typically they are opportunistic, the moment they will find a gap somewhere they are going to exploit it. For the same reason the risk is high, the likelihood of this kind of attacks happening at the moment is quite high, but at the same time the impact is low. This is why the risk is categorized as medium here. On the cybercrime side, Most of the attacks are related to fraud and scams, so not traditional cybercrime. When cybercrime is actually involved, it is due to commodity operations that also have a spillover in Greece. It is very rare that you see targeted cybercrime operations for
Greece. Also, very few domestic groups have been observed doing that. Now, the risk is medium in this case, because the skill level is a little bit more advanced than hacktivists, and there is so much cybercrime campaigns going on all the time worldwide that definitely every single organization will also be hitting Greece, but not to a level like other countries. So the risk remains medium. Now, the cyber espionage side, mostly government critical infrastructure, but occasionally they have been cases in other private sectors, depending on the intelligence requirements that the country has. There are a few different countries that have been targeting Greece for a while. Probably the oldest one, it is the Five Eyes and Russia.
But recently, Turkey has demonstrated that they can do some quite advanced attacks. Now, considering the current situation, geopolitical situation in that region, the region where Greece is, and the threat actors we are talking about, the risk is definitely high. All of these threat actors have the capability to perform very advanced attacks. They have been targeting Greece for a long time, consistently. So the only reasonable thing to assume is that those attacks will continue, if not continue become even more prominent. And with that being said, thanks everyone. I ran a little bit out of time, but I think that's not too much. Also, big thanks to the B-Sides team for adapting to the situation with the virus and
still making the event happen. If anyone wants to reach out to me, you can find me on Twitter or LinkedIn. And yeah, thanks again, everyone.