Exploring Emotet, An Elaborate Everyday Enigma - Luca Nagy
Show transcript [en]
The stage is yours. Welcome, everyone. My name is Lúcia. I'm from Sophos. And now I would like to give you an overview of the most widespread trojan family I struggled with in the last few months. The first EMOTED samples we detected popped up in May 2014. The intention of that sample was completely different from the current funds as the earlier samples were designed to steal Bangkok conditions. That's why they spread the word as banking trojans. It has always been using heavy spam campaigns. Firstly, they targeted German-speaking countries like Germany, Austria or Switzerland, and then they gradually expanded their scope to countries like US, Canada or the UK. The binary is frequently modified and finally it was improved to a modular structure. It
got a banking module, spam module, a JOST module, and this was the version two. And then they started to focus on anti-VM techniques of obfuscation. The latest variants has modules for information stealing, for spreading, not only through the local network, but through spam emails as well. The latest variants are capable to download additional malwares like ransomwares or other banking trojels. Emotet is leading our list of occurrence. Ahead, malware families like Gantt, Crab, Osorwood, Formbook, or Hawkeye. On the graph, you can see our detections on daily basis, and you can see it's thousands of Emotet samples popped up in every day. These detections were located mostly in US, Canada, in Europe, in France, Germany, or France as well. An immotate infection begins with a spam campaign.
The victim receives a message that claims to be an invoice of a bank or a telecommunication company, even a shopping notification, confirmation, coming from seemingly a legitimate organization. The email content has a malicious link leading the victim to the downloader, or these downloaders can be as an attachment. We have seen a wide range of attachments like Word documents, Excel, JavaScript, PDF, or even password-protected zip files. But the most evolving method is when these malicious objects are inserted into an email conversation chain. And this was appeared in the last few months after the email testing module appeared in October and harvested not only the email contact list, but the email content as well. On the right, you can see the document which was
the victim to the protection of it. And in the case of the macros are enabled, it can be accessed. And as soon as the macros are enabled, The code results in a PowerShell script, which downloads this emoted payload. The macro codes are heavily obfuscated with full of junks. For instance, what I have analyzed, almost thousand lines with full of garbage codes and functions. There is a shell function, which has a parameter made from returns of other functions. And in the case we delete the chunks and put the useful parts together, you can see on the left side the code snippet which calls the CMD with a long argument which is the character coded representation of a PowerShell script which downloads repeatedly, try to access the URLs
and downloads the emotech. I'd like to talk about some anti-analysis techniques starting with an own custom packer. which appeared in June 2018. Immotet has always used packers, but it was slightly different because it could make the flow tracking more difficult. It's a two-layer packer. It means the first layer decodes the second layer and loads it, and while the second layer loads the payload, but the approach is somehow tricky because the second layer writes the code chunks into different memory blocks. So it cannot be observed as a whole without putting some effort to it. As you can see in the picture on the left side, the CC bytes replaced the real opcodes. Immotet discovers the environment it is running on. So for instance, the earlier samples check the
running processes, checked some VM and antivirus related files and folders, and in the case they detected a VM, they had a second set of fake IP list in order to connect to them unsuccessfully to mislead the analyst. The latest variants sends the whole process list to the server, so this VM checking happens on the server side. The earliest variants used the processing action to the explorer.exe, which further injected other running processes. But as the modular structure appeared in EMOTAT, it is used only by the modules. For instance, the wrapper module, which decodes its embedded executive and injected to some legitimate processes. As some sandbox and antivirus products are capable to hook only the 32-bit end version of the
NTDLF for WOFF64 processes, and the most debugger and disassemble are not capable to handle the switch between the 32 and 64 bits. So for this reason, the following technique can cause difficulties over the course of the analysis. In the picture you can see a desystem with code of the wrapper module of AMOTED which, so as it switched to 64-bit in order to use the 64-bit NTDLL for the processing action. To access the 32 or 64-bit code execution is possible from different code segments. So we have to modify the segment selector. That's why you can see on the left the push 33, which is the segment selector of the 64-bit. And the far return can specify besides the return address the
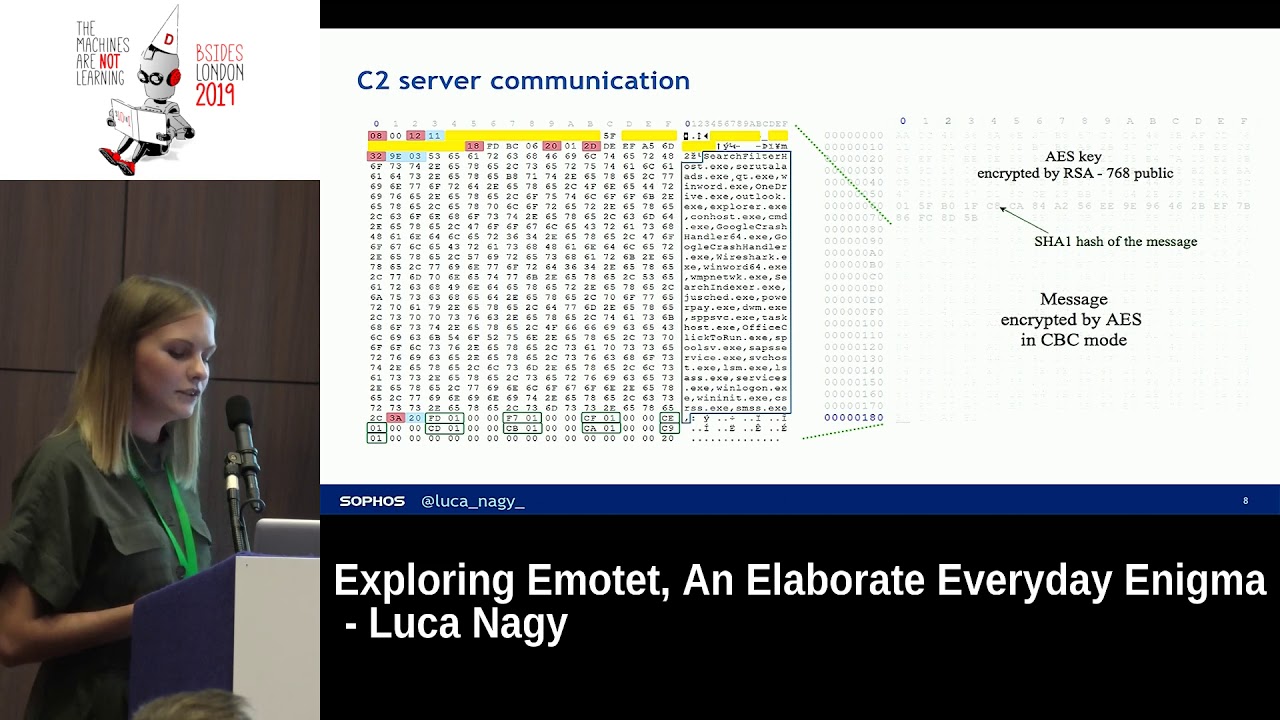
code segments. So from the yellow addresses on the left side, those bytes are in fact 64-bit instructions, which you can see on the right correctly. So from that point, the 64-bit NTDL can be accessible. The C2 server communication is based on Google protocol buffers. On the left, you can see Google protocol buffer messaging. It's a binary format. These are the sent information like the process list. There are system information, terminal session ID, There is the check sum of the sample which can be useful for the server in the decision of refresh the sample or not. There is the yellow highlighted part is the bot ID which made from the computer name and the serial number. And the last green part is the
IDs of the downloaded modules. On the right you can see the structure of the send payload with the AES key which was generated in runtime. and encrypted by the embedded RSC public key. And then S-H-A-J-1 hash is generated, is computed from every message in order to validate. And there is the message which is encrypted by the ES key. As the victim has the latest emoted sample and information sent to the C2 servers, it doesn't reveal the virtual environment. In that case, a list of the latest modules are downloaded. This list has been changed over the years and can be coupled with additional malvers as well. I divide it into two groups as there are reprimand was which
decodes an embedded executable and this can be a public domain executable like the NIRsoft tools or can be an own proprietary executable. The NIRsoft modules are password recovery tools with the difference of the web browser pursue scans the web browsers to find passwords while the Maypassview target email clients. And in the year of 2018, two property executives appeared in order to collect not only the email contact list but back to 180 days every email chain. And there are regular modules, which means it's run in the main sample memory, like the network spreading module, which scans the network in order to find network resources, and it tries to create a new session connection to the IPC share in order to enumerate
the users. And then it has a huge list of passwords, which was extended through the years. So, for instance, the earliest variants has 3,000 passwords in this module, but the latest has more than 10,000 passwords. And at the end, the main aim is to gain persistence on that victim, on that machine as well, by the means of it creates a service of its copied binary. The port forwarding module is the most interesting because it seems like the initialization part of setting up a proxy server because it uses the UPnP library in order to set the port forwarding on the local router and it bypasses some FIWR rules by the means of it enables any income inbound traffic to that program.
it creates a simple server to answer to any messages. I checked the, so on the left side you can see the port numbers which are set by this module. And I collected several IP addresses which were embedded in the main binary because these IP addresses are very frequently rotated and it has very unusual ports. And if you see, these are exactly the same.
ports as said by this port forwarding module. So this can suggest us that a great number of the current C2 servers are infected victims. On the right you can see the location of these. I collected the IP addresses and these are mostly in US, Canada, but in Europe, in Belgium, France and Germany as well. As well as I mentioned at the beginning, it's very similar to our location of our EMOTED detections. There is a spam module which firstly to connect to the C2 server, downloads these templates, the recipients, the hijacked accounts which will be the future sender, and sends out several spam emails to new victims. For instance, what I have analyzed had an embedded, had an PDF, which was attached to
an email, and that PDF has also contains that Immotet downloader. So new Immotet samples and downloaders are appearing every day. According to the US-SER, it is the most costly malware, as it can cost up $1 million per incident. On the graph you can see our 10 weeks observation and these are the new appearing emoted binaries and downloaders and on average 15,000 new emoted downloaders appearing and around 500 new binary appearing on every week. Thank you very much.
If you have any question, feel free to ask me. Any questions? Hi. For the PDF exploit, was there any, did the malware leverage any missing patches or the user had to enable any functionalities on the PDF for the link to be accessed? So it's just the downloader, it's not Xprite. PDF has the embedded downloader which leads to the hacked WordPress site which has the downloader again. Okay, so the victim had to click on the link then? Yes. In the PDF? Yes. Okay. Yes, of course. Any other?
Okay, thank you. Thank you very much.





