Identity Security Pitfalls: Common Issues and Misconfigurations in Entra ID

Show transcript [en]
[Music] All right, good afternoon. Um, it is afternoon, I think. And for those that are hungry, food is going to be served afterwards. I'm not used to standing on a podium, so this is kind of weird. Identity security pitfalls, I think, is the name. And we've done so many of these identity sessions over the last two three years helping customers understand what identities actually mean and what they look like inside of Microsoft 365 and also erggo what lives inside of Azure. How many Microsoft customers in the room or consultants more and you not allowed to speak? Um, if you want a guy to come talk to you about serious identity, he's sitting right over there. His name's Victor. Um,
and he'll be taking all questions after this session on my behalf. Um, so today's session is really about the common issues that most organizations face when working with identities in this new way of working. You know, there are still some customers today that live on prem. I mean, for those that come from the information management space, there was a CVE that had to do with SharePoint server. I don't know if anyone heard about that. It's SharePoint server. It's not SharePoint online. Let me qualify that. Um, so for those that haven't patched their SharePoint servers, they've probably been hacked and some customers in South Africa have actually been exposed because they still running SharePoint server. So today's session is
really going to focus on what happens inside of Intra ID specifically. That's the identity management platform we're going to be focusing on today specifically. If you're not interested in that, stick around, but I don't want to bore you if you want to talk about some sort of other amug. I have since then grown a beard. Um I haven't had any professional photos done since then. I've got more ink on my arms. Uh, I'm a Microsoft MVP. I help customers work better with not only Microsoft 365, but also I spend a lot of time with customers talking about data security. Um, I've been doing this for probably 30 years now. I started off as a cobalt
developer, couldn't get a job, and then moved into infrastructure and then I fell in love with gaming like you always do, right? So, I I'm still into gaming. I just don't game enough. My kids do it on my behalf. And probably for the last seven or eight years, I've been speaking to customers about data security. How do you do information protection, data life cycle management, retention, um those sorts of things? And when you look at zero trust and you'll be hearing a lot about zero trust in today's session and the methodology behind that and why it's important to have a plan or a framework um inside of your organization so that you have a northstar and you'll notice
right at the end they talk about data security but today we want to focus on the left hand side of of of zero trust identities and endpoints because that's the way you access content in your environment. Be it an application running in Azure, be it a document sitting inside of SharePoint or having a conversation with someone inside of Teams, it all starts with an identity and you need some form of device to connect to this application that you want to consume. And I don't think I have a slide in here that says identity before firewall, but I mean, I'm not a hacker. There's probably a couple of people in here that know how to get into systems, but how many of you
are actually physically attacking firewalls today? Real question, who's hacking a firewall? The guy at the back. >> Okay, so you still very traditional in your approach. There's an open port. I'm going to get through there and chances are I'm going to FXP into it and then upload Ghost Recon Advanced War Fighter, right? because you're a courier. Yeah. Like in the old days. Um but today's attack parimeter is identities and that's really what we're going to be talking about today. So just a session overview. Um if you're moving a customer from Google Cloud Platform and they don't have anything inside of Microsoft 365, chances are you can do some cool stuff right straight straight off the bat. But
normally you encounter a brownfields environment. There's things from active directory and you can speak to Andre Kirkland about active directory because I think back in 2003 he actually helped Microsoft build the schema. Um I'm sure he did that with a bank. Um so if you want to know about active directory go speak to Andre. Um they talk about a 25-year-old attack vector and it's still the same. Although they have improved active directory considerably in Windows Server 2025. So, you'll have to ask Andre if it's a good idea to upgrade. I recommend you upgrade if you're still running a domain controller on prem. Um, upgrade it to server 2025. Now, there's a few things that you're
going to see today about misisconfigurations that live rentree inside of Entra ID that starts as an identity from active directory and because you're running some sort of synchronization service, it now lives inside of Entra, but you trust it because it was there, right? And it's been there for 10 years. So now it goes up there and it's not as secure as you hoped it to be. So we are going to be focusing on that as well. And some of the misconfigurations actually stem from that. But when we look at what we're going to talk about the common ones, things that you can go after this session and go look at and I say red means bad. You're definitely going to
see that how these misisconfigurations get exploited with a handful of real world attack stuff. And I guarantee you everyone in the room that lives their entire lives in cyber, you probably know of a hundred more attack vectors. I'm using simple examples today to give you an idea of what you should be looking for. Some best practices from a hardening perspective, things that you should be doing that you may not think about because you've inherited an environment that you have to worry about and all of a sudden it shouldn't be your problem. but things that you can go do now free tools that you can sniff your environment and have a look and identify these things and then also looking at
some of the continuous monitoring side of things with some tools as well. So best practices goes handinhand with what you need to do from a monitoring perspective. Um the best practices we're also going to be focusing on some frameworks in this case we're going to be focusing on one specific framework and that's a zero trust adoption framework. Anyone implemented zero trust outside of this crew over here? There are people. Was it easy? Did you get decent buying from business? >> Okay. When did you start it? Okay. Did they know what zero trust was when you said the words? No. Okay. All right. funnily enough, uh there's some tools, there's a zero trust assessment program from Microsoft and there's some
new tools dropping in the next couple of weeks around what you can throw at your environment, not just using anyone use the zero trust assessment uh spreadsheet. It's a pretty spreadsheet. Um it's literally a paint by numbers guide, but you need to know what you're doing. So let's have a look at the traditional identity security mistakes that and it's not bad that this lives inside of it's bad for your tenant but don't take it the wrong way. You haven't made the mistake the move from onrem to the cloud. The fact that your entire app authentication stack now lives inside of your identity management platform. I mean who in the room are identity engineers here? Nobody.
It's the wrong crowd. One guy. Okay, everyone else can leave. You need to stay. And this is by no means giving anyone the right to go hack a tenant now because of these things. But typically when we talk to identity and access administrators, identity access managers, um there's things that they don't think about because all of a sudden they've inherited the entire app stack that lives inside of the environment. Your orth now sits it's called either an application registration or an enterprise application that lives inside of enter ID and that needs to be accessed by some form of identity service principle managed identity a service account that you are giving username password permissions either MFA or not MFA but
that now belongs somehow to identity people not security people but do the identity people speak to the security people different thing do the security people say hey we need to have a look at this because it no longer sits with us I don't know and trying to find a happy medium where identity professionals and security professionals have equal responsibility to a platform that lives inside of identity >> right sometimes you want to pull in your your dev team to say well dev secc ops is a thing and you know it's not just about code quality it's also about authentication especially in today's world where Everyone can vibe code and you can go build an app and you go,
"Shit, I don't have to pay a developer for 400 hours to build the app. I'll vibe code and I'll deploy it." And then you end up with an app that's been hacked in 3 days. So we as security professionals are going to become inundated with customers going, "Oh no, we got this guy and he vibe coded this app and now it's running and it's talking to a database and there's some payment gateway and we got hacked." that's coming because AI is taking over. And also the threat of AI when it comes to being able to sniff, you know, guys are using stuff like worm GPT or Ghost GPT um for attacks, you know, they'll suck in the MIT attack
framework and go cool, we've got a frame of reference now, and we're going to use ghost or worms GPT to execute against things. So just a couple of the common ones that we see you know why is it important to to you know focus on identities anyone want to take a stab right so look at the stats according to Gartner and this is non this is workload identities right it's non-human identities from a crowd breach perspective what percentage anyone want to take a stab in 2024 for 70% of attacks focused on workload identities or non-human identities that service principles managed identities ID secret all of those things the same thing with Microsoft statistics again you know
compromised workload identities not user account things so as much as we've said to the world hey two factor multiffactor authentication here's an app non-fishable um fishing resistant MFA because you're using the authenticator app with some sort of biometric signature. You're not going to receive a text message with a six-digit code. You know, that sort of stuff, which is fine. We're no longer doing a fishing attack against someone saying that, hey, click the button and you know, follow the instructions and now we have your identity because fishing resistant MFA means I'm not going to clone your SIM. Right? So we've already established that we can get identities to do that but that's human identities and that's an easy way switch
on MFA or app only 99% of your problems are gone but when we look at workload identities the other identity that lives in your AM space even according to Microsoft 68% of what Microsoft regards as cloud breaches have been done based on non-human identities and you know it's simple things right automation accounts inside the organization, how they compromise those things, right? Um they have broad permissions and if you've ever heard of privilege escalation, we can talk about that as well. Things that are living inside of I mean you can use a deployment token from a web app in Azure and you can stick it into your pipeline and you can deploy on build just using a deployment token and
you can deploy that application. So if your GitHub repo is compromised, they can inject stuff in there and because your security team or your identity team is not working well with the developers because I mean who does um these things happen, but it's up to us to even if you do allow those things to happen, what do you need to go look for so that you can identify when it does happen or how long it's been running in your environment? Any ideas number-wise? You guys should know how long a threat actor lives inside of rent free inside of your environment before you find out about it >> in the in Europe it's about 20 28 days
um and what they're doing from a ransomware perspective because of GDPR they ask you for 4% of your annual turnover and because European companies have cyber insurance it's easy 208 days according to I think it was IBM 28 days before you even know about it so They super super good at what they do. Now there's no clock in the room. Where's the guy with the sign? Um he's here. I'm good. So when we look at the most frequent ones, the easiest ones, right? Um the easiest ones because I'm just, you know, rambling on incoherently and I just want to make sure that I'm not losing time. Oh Okay. Half an hour. All right. So again,
disclaimer, Active Directory is not your friend either. So if you think that uh upgrade to 2025 if you are in the room that's server 2035 over permissioned accounts many times we'll developer wants some graph API permissions and we give him a we don't give him a read write we give him a read all and he goes no I need more things and you switch it on because the CEO wants an application deployed gets deployed and I'm equally guilty of this. I've got an application. I wonder if I can show you an application running with no permissions on it. Um because the way the third party application writes to the API, it can't pass modern author
across. Yeah, nobody knows what the endpoint URL is, which is fine. Um but if someone did sniff it, they'd go, well, there's not much in it, so you're welcome to hit it, but I've done it. So it's not like man you know holy grail standing on a podium and you know you do all things right these things happen right MFA again you know how many people in the organization can guarantee that every account inside of your organization even service accounts with conditional access policies running on top of those things you're going to enable MFA or complete MFA rollout right life cycle management for joiners movers and lever Do you have accounts living inside of your environment that have no
owners as in human owners? And I'm not talking about non-human identities. I'm talking about human identities. We we will get to a point where we talk about um orphaned applications with no owners. Another problem that you have. And then lastly, when we start talking about um auditing, right? Do you care about risky login or does everyone in your organization run some sort of VPN or some sort of DNS proxy where they're logging in from Texas? I mean, did you ever have that conversation with staff inside of your organization? Impossible travel policy. They come to the office, they log in in Jober, they go home, an hour later they're logging in from Usuzbekistan. They can't travel in an hour. And what
did we do back then? We phoned everyone said, "Listen, Bri, have you got a VPN because you want to watch Netflix US?" "Yeah, okay. Tick." Uh, we just accept that everyone is doing it and we don't care about impossible travel policies. So, these are the things that happen, right? And when we actually look at you know what over permission things look like right it's a simple thing right standing global admins who has global admin rights in their in a tenant somewhere
>> has everyone rolled that p because that's what I'm hearing everyone has rolled that p >> hey I don't think so right service accounts right like I just explained now I've got an account that has access to an API and it's got and I'll show you what directory rewrite.all all looks like right admin roles granted directly for specific things right do you manage your arbback when it comes to no global admins or no administrative accounts and you've switched on everything we switched on pim for every account or any a privileged account have you can you confidently say that you've done these things right so when we look at overprovisioned things I'm not going to say overprovisioned
accounts because applications can also um be affected in these ways or managed identities or service principles. Um, these things do happen depending on how it gets deployed inside of your environment. So, you know, some remediation is to implement PIM, right? PIM is your friend. It might cost you some money depending on how you do these things, but you want just in time or just enough access. These shouldn't be foreign words to you. If you don't understand it, go back to your identity people and say, "Hey, are we doing these things inside of the environment?" So, go do that now. Right? When we look at what's available to you inside of the Microsoft ecosystem, they've got amazing
technologies that live inside of Entra. Well, inside of Microsoft, right? I'm not going to say it's exclusive to to Entra. Some of these tools come at a cost. So, it's an additional cost to whatever Microsoft 365 license you have, or if you don't have any Microsoft 365 licenses, it's usually a P1 or a P2 on the Intra ID or Azure plan. Um and you can switch all of these things on. It's there. It's available for you to consume. You just need to understand what they do. So from a management capabilities perspective, you can start looking at simple things like do I have overprovisioned apps inside of my environment or overprovisioned identities with privileged pro with
privileged roles associated with them. The tooling exists there. You can literally just run through this, you know, looking at weak access policies because I don't have a lot of time. Um, MFA not enabled across all apps. You can do MFA on condition, you can do conditional access stuff on applications. So if you expect that people hitting this app comes from a known location, switch it on. So if I'm in the building, no MFA, you can use that practice to make sure that some guy sitting in Usbekistan trying to hack your system can't get in. Simple math, right? Same thing with legacy apps, right? You need to understand that modern author is the way. What are you doing with legacy
apps, right? And then also understand that you can configure policies that's going to monitor things as simple as signin policies, right? Switch on default deny in that policy. Switch it by default deny access unless that condition equals true. When we look at life cycle, that was quick. Again, same slide when we start talking about these things and you'll notice how they still call it Azure AD. Um, when you start looking at this engine that lives in the middle, the one that does the the evaluation, it's a risk profiling engine. Simple math. These slides are this I did not create this slide. All the ones with the pretty weird people in, those are my slides. This is
Microsoft slides. Microsoft actually's got what they call the Microsoft cyber security reference architecture pack. You can download all of these things. It's our holy grail. It's our northstar. It's our bible. It's created by a guy by the name of Mark Simos. Um and a and a crazy guy Tar Darwood if I'm Is it Andre? Tar tar. Yeah. They scare me. Um and and they've created this. This content is available for you today and you can consume these things. So when we look at life cycle management gaps, do you worry about these things? Are you provisioning people deprovisioning accounts applications inside of your environment manually? Um having orphaned applications and orphaned accounts inside of your environment. And do you
even care about guest accounts in your environment? Have you got a guest access review policy deployed? Oh no. Invite this person to a team. Boom. Member in inra ID. Do you care about those things or do you say well we've given the the responsibility to the business and the business worries about these things and then that identity gets compromised you don't control that that gets compromised so these things you need to worry about right and there's platforms like enter ID governance I don't think it comes with a P2 I'm not a licensing expert but you can switch these things on or pay for the platform I know workload ID uh that's expensive when you when you switch on workload ids
but these things you can do. And then from a monitoring perspective, if you don't have a seam, you shouldn't be in the building. Or if you're not monitoring um or looking at threat analytics that's coming out of the logs that you're shipping somewhere to Sentinel, you know, or wherever it's going, you should be monitoring these things. Go hire a bunch of interns to look at a dashboard if you don't want to do it. But you need to it's a continuous thing, you know. It's not just a set and forget. It's not a firewall, you know, and it's important to understand the capabilities that live inside of Microsoft. All of this is there. I mean, you might have third
party tools that you've inherited over the last 10, 15 years. You can actually start looking at, well, is there an equivalent function or feature that lives inside of your Microsoft ecosystem that can give you very much the same equal or better functionality because you're paying for the license anyway. So when you look at the seam source stuff, shift left, shift right, it all lives inside of your environment. If you are at a Sentinel customer, you should be looking at logs. If you're shipping your logs off to something like Wazar, you're still going to get that telemetry data, but you need to monitor things like signins. That's a simple simple example, right? So the reason why we want to do
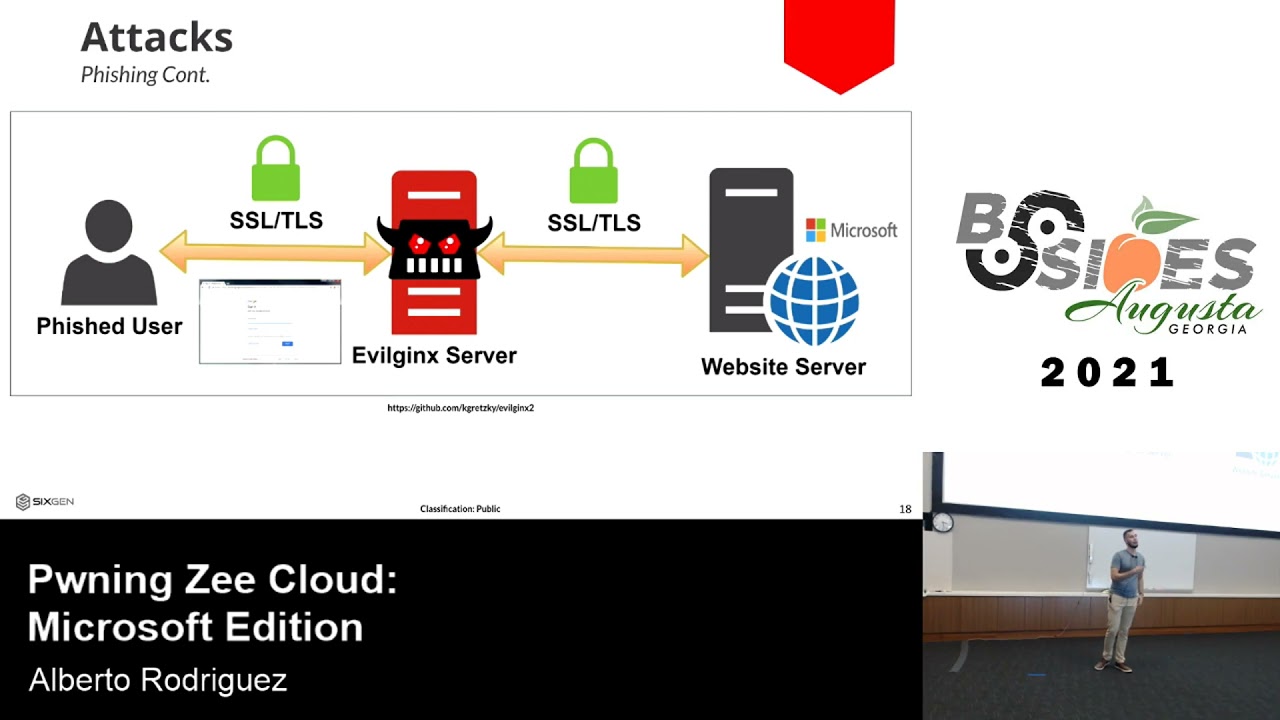
these things is because there are some real world attacks that happens and I'm just going to expose you to a handful of them, which is super simple, right? a standard MFA bypass logs in through an ex excluded app. Boom, they're in, right? Policy doesn't apply there. So, they've got access to the application and then they can do some sort of escalation. Midnight Blizzard was an escalation attack. I mean, everyone knows about Midnight Blizzard because the world stopped and they blamed Microsoft. It was a dev tenant exposed privilege escalation. They managed to get GA in and that's it. Done, right? These things happen because of misconfigured permissions. Service account abuse. Uh it could be anything. A service principle with an
app roll assignment, right? That's what happens. Again, privilege escalation straight over the top, right? Token theft. We've seen anyone follow Linus Tech Tips. Yeah. You saw what happened to his YouTube channel and he changed the password, right? And he goes, "I'm sorry. I changed the password. It's okay." No, they had the token. So, they just kept on logging in because it didn't expire and the videos got deleted. So, understand once they've compromised the identity when they get in, they can do a lot more damage than even if you've switched that identity off of change the password because that's what we do. Disable account number one, reset password, number two, reinforce MFA. But if they got a token
session, if they got that session, they can still do things using that identity because it's been approved, right? And again, uh, did I click this? Yes. From a cloud perspective, when you look at AD and accounts that are lived there that synchronized across, it might not match the specific permissioning profile that you have because you're synchronizing. You trust what's in the building, right? We'll talk about trusting what's in the building. But because you're not segmenting on-prem accounts that have privileged rights to what happens in the cloud, I mean these things happen and 3 4 500 users in an organization and you've been running for 20 years, there's applications that you don't know about because you've been working there
for the last 3 years. It's vitally important that you understand these things. So those are three attack vectors that people use. you know, MFA bypass, sniff, identify some sort of endpoint or an application that's got excessive privileges and you try to exploit that. And I mean, I'm sure people in the room have done this. So from a best practice perspective when we start looking at well now that you know what can happen you've seen the common pitfalls that's available how do we go about understanding from a methodology perspective what we can actually implement inside of the organization or just a thought process how you should be thinking about these things right now start with a plan find your northstar uh
NIST people in the Yeah, CIS people in the room. Has anyone gone through a CIS benchmark? Like four people. The rest of you need to understand what CIS is. Zero trust, FINRA, Fed ramp, you can even go down the industry vertical, but start with a northstar and most of the times the methodology and or framework because it's usually a methodology or framework. It's not a standard. NIST is not a standard. Weirdly enough, I found out that I always thought NIST was a standard. No, it's a framework, something to subscribe to. If you go download the CIS benchmark stuff, they'll even tell you where to go. Go to this portal. Here's the URL. Log in, switch that tick box on, and carry on
with your life. So, it's very simple to improve the overall security posture of the organization. And when we start looking at that strong off conditional, you can do if you want to do it on workload ids, you need a workload ID license specifically for conditional access on I think managed identities. Um, so some of these things are license dependent, but switch on conditional access and MFA for applications, right? Strong off, fishing resistant MFA, do that. Make sure that you actually look at a dashboard that says these are all the logs coming from the systems that I have stuff from Azure stuff from Microsoft 365 everywhere else. Make sure that you've got a centralized place where these logs come
into and you have someone staring at a dashboard that says red means bad and they'll tell someone to go do something right. Provisioning things inside of your organization. Make it easier to do the manual click box. Anyone can do anything. We've got a customer and our team actually implemented some security stuff and I wanted to switch on pay as you go for co-pilot studio because we bought a $200 pack but you have to switch that on. I could see that there's the Azure subscription but I couldn't apply it because I didn't have the rights and our team spent the last week making sure that you can't just magically even with GA you can't just magically do things like this. They the
team didn't know that we've switched it on and an hour later they came back and they said it took me an hour to do this because you guys switched it on. I said well security is paramount. Welcome to our world. Right. So these things are important around how you go about making sure that there's some form of automation or process when it comes to not just PIM but elevating specific rights inside of the organization from an enduser perspective to do perform privileged task inside of the inside of that and then also understand what lives there right I mean how many of you actually run a monthly report to look at identities that you've disabled but
you're keeping it there for whatever the reason. Do you even look at that? You need to start understanding what's going inside of your environment. Right? And there's a lot that you can do with the tooling. And you'll see these slides are all from the MCR. But it's vitally important. Does this button work? Hold on. Can I do cool Like where am I pointing it at? Okay. I just want to see if the button worked on the clicker. So conditional access is your friend and you should have I don't know what an optimal amount of conditional access policies are inside of your organization but there's stuff that you can do around app control policies. You can actually
ship it off to Microsoft's CASB. You know you don't have to use Net Scope or or what's Kato or one of those platforms. You can actually reboot content and give them a different experience. It doesn't always have to be deny signal detection in force. give them a reduced experience. You don't have to stop them from doing what they're doing. The platform exists and you should be switching these things on and it also extends um to third party apps as well. So if you haven't used Defender for Cloud apps, that's what they're calling it today. Yes, it might change. You can do conditional access stuff. And I don't want you to just think about conditional access as conditional access policies
inside of Entra. I want you to start thinking about risk profiling human and non-human identities in your environment. That's what I want you to start thinking about. Now, non-human identities are typically used in application layer and we'll we'll jump into some app registration stuff. Am I doing for time? Um, okay. All right. Slides are great, but that's cool. Hold on. We need to go back there. Back. Back. I'm running out of time. All right. So zero trust is a personal favorite of mine. Um we spent a lot of time Andre as well um with Microsoft and uh for those that think everything happens outside of the country. No. Um we spend time with Microsoft in Seattle
building out a lot of the security stuff. So the zerorust adoption framework we spend time on it. Andre over there helps Microsoft curate a lot of the certifications. All the SC's that's your man. And we even built a game. Um, we helped them build a game. I've actually got that board game framed. So, never trust. So, if you look at the principles because I'm running out of time. Damn it. Assume breachs. Breach. Breach. And second to that, prepare for breach. So, expect someone to break into your house. We do that, right? We get expander brackets and everything and we put all these cameras in because we're assuming someone's going to break into the house. So assume breach and prepare for breach,
right? Verify explicitly. Trust no one. Trust nothing. So you know, trust but verify. No, verify and then you trust. Get that out the way and use lease privilege inside of your organization. So from a tooling perspective, I'm actually going to jump into a demo and show you a few things before I go back here. What is happening? Oh, this is a Mac and I hit max. PC. Where's my mouse?
There it is. It's going to come. Ah, I've got it back. And how do I mirror screen mirroring? Change entire screen. Yes. I'm winning. So, there's a couple of tools. I want to show you one specific one. Um, is it this one? Yeah. So, this is a paid for tool. It's a paid for version. I talk a lot about the governance stuff. Um, I want to give you an identity idea of this is my dev tenant. All right. This is an application called appggov. You can go look at it. There's there's free versions of this. But a simple example, right? So, I mean, you can go do ping identity or or ping castle. You can download that.
There's admin droid as well. There's a free version of that. You can deploy it inside of your environment. And because I've got Oh, I've still got a little bit of time. 10 minutes. All right. I can drink some water then. So, the reason why I want to show you this is a lot of the times we don't know what's going on. Microsoft's got some cool tools that live inside of Intra. Um, got a whole bunch of things inside of Intra that will give you an idea of what's going on in and they've improved this. This is relatively new. I mean, I haven't done any identity secure score around that, but you should be focusing on it. But this is a tenant that I've
had for quite some time now about eight, nine years maybe. Um, and we just deploy into it, right? It's a dev tent, so it doesn't really matter. But when I started thinking about identity security, it was actually quite scary. I said, well, let me run a tool against my environment and let's go have a look at what it's saying. Now, this is the app gov score. This is not a sales pitch. It's just an easy demo to show you what you can achieve today. Now, this score is similar to the your your secure score or your security posture score, whichever wording you like. This is rated at 43%. forget that number. But living inside of my tenant,
I've got 92 enterprise apps, which is a lie. Um, there's more, but these ones don't look at anything weird. I'm high risk of 20. Um, four apps with public client flows. We can have a separate conversation about that, but I want to show you something simple. Where was I? Um, let's just go here. I want to do a search. Okay. Now we talk about applications. Now remember if you deploy any application into Entra or any application inside of your tenant in Azure you need to authenticate against it and chances are you don't want users logging in all the time. So you're going to spin up a managed identity or service principle. Managed identities get automatically created
from an application registration perspective when you spin up specific services like a Azure automation that will create a managed identity and then you typically go to the object ID. Let me get it right. The object ID and you can then grant it graph permissions, right? Because you deploy an application, it might be from the enterprise applications gallery and it says SAP 4 Hannah and you click a button and you trust, right? This application now spins up a bunch of containers and it does some long analytics things and a whole bunch of things and orchestration in you migrate a database to the to the environment and now you're cloud native, right? because this is running Kubernetes. I have to
say that word because a good friend of mine says I must. Um, yeah. But do we actually look at the permissions that get granted at a graph level? Because the minute you want to talk to anything inside of Microsoft, it's going to go through the graph. That's your API reference. Right now I wonder see if I can I'm going to look for dot read write all simple thing right it come out right so this means directory means I have access to enter ID read write means I can read and write to enter and obviously all is all If I've got this permission, I can create an account. Now, if a threat actor gets that, what
does that mean? They can create an account and use the account, right? Simple math. Now, you think, well, I'm not going to grant anyone that level of permissions to do things, right? From a rback uh this roles, everyone's got a user account and we'd give them no permissions. But did you know that applications have these permissions, right? So when we look at this environment static web apps is graph and did it do a search wanted to find is it in here? Okay. People read these ones are reasonably okay. I want to find a different one. Where was it? Um, owner list apps. See if there's any apps in here.
>> Okay. Ah, here we go. We actually built this application called Janitor Authority that does stuff right now because we have overzealous developers. What is going on here? Did that disappear? Why? What? Why does it say is someone hacking my desktop? Annoying application. I don't have an annoying application in my environment. You saw that one that was right on the top right? Okay. Dot read Right. Search. I don't know what that is.
Give me the other one.
Is that thing just gone now? Yes, that one. Stay there. Stay. And it goes. Okay. That's not funny. Um, that was an application that had read. Write. Let's just pick another one. Graph cloud sync. Yeah. Okay. There's a simple example. I've got a application called cloud sync, right? And I wanted to show you a directory readwrite.all permission because I have applications running inside of my tenant that has that specific rights. But this one cloud sync, right? So it's got sites readwrite.all. So that means that any site inside of SharePoint well it's got access to SharePoint and it it can read and write. So it should be able to delete because it's read write um inside
of SharePoint. So I could spin up any SharePoint site and I can publish that. Right? So from a graph perspective, it's vitally important that you understand what's actually going on there. And this is a simple example of what the world looks like because there's an identity right here. Right? This application now you can go find that service principle or manage identity. If you go to application registrations, you'll be able to check the authentication. Right? You can literally click on it. You can see these are this is a client ID. This is a secret. Where is that being used? There's a deployment token being switched on for because a deployment token typically gets created when you're
deploying a web app. There's a static web app in here. I think I saw that earlier on um there right so also understand what those apps do and how people are authenticating inside of that app. It's typically a service principle and how you're doing authentication at that level and understand what graph API permissions you've granted to that. So I've been told that I don't have more time left over. So I'm going to go back to the final thoughts today around what you should be thinking about. So automation, make sure that you are worried about access reviews. Apply role- based access control and context to human and non-human identities inside of your environment.
Did this thing just come back here?
There we go. Okay, this is a zero trust architecture. Go download it from uh uh the MC. Uh so a couple of thoughts from my side. Um you can stop this. You just need to identify when red means bad. Um, you should be able to automate provisioning and deprovisioning of things inside of your environment. When it comes to human and non-human identities, understand the differences between service principles and managed identities inside of your environment. Um, fix this, you know, get to a point where you pass wordlessness. Go buy PHTO keys for all your administrators and make sure that you are enabled. you've enabled fishing resistant MFA monitor continuously hire interns who stay at a dashboard and when red means bad they
need to call you right it's a simple thing and then also at the end of the day you need to educate your entire organization this is just not for techies it's not for security people there's an entire pitch around educating the people of the organization the end users on the importance of making sure that they don't click on stupid links you need to educate at your developers around how they're writing code. You should be evaluating that because that's going to end up in your environment and you're going to need to worry about things. So, continuous evaluation, continuous assessment, it's part of the zero trust. He's just said I must stop now, but please, you know, a couple of
takehomes. Identify what's going on inside of your environment from an identity security posture perspective. Know what human and non-human identities are. Understand identities. talk to applications and graph API permissions and go find some tools that's available to you so that you can sniff your environment in Redmond's bad. Thank you very much for your time today. Any questions? No.
Yes. No. All right. Well, if you're looking for me, um, there are some resources. Do I give you the deck? I never asked. I don't know. >> Okay. check with Kurika. All roads read to Kurika. Um there's a ton of resources. If you want my slide deck, just reach out to me or reach out to Cara. You can probably grab it. And if you want to get a hold of me, my name is Alistister Pugan and I'm on the interwebs and the Twitter rotties. If you have any questions, reach out. I'll happily, you know, spend some time with you. And thanks for spending 45 minutes on the talk. Yes. >> Yeah. just um in a way I would I
wouldn't say it's a it's a question but just >> just to add as part of the the the best practices. >> Oh there sorry that's >> um also the the other thing that is very important is the assets the owners the ownership of the accounts. Yes, >> whether it is um a service account or or maybe it can be like a privileged account. So it's very important because what I've noticed is that with a lot of organizations, yes, as much as you can have so many accounts in your environment, but if you don't know who is the owner of that system or at the owner of an account, it can cause a lot of problems. M it's
very important in terms of the ownership of an account >> and also the system so that when you grant access and you manage whatever assets in that organization then there is that sort of you know identification to say who is the owner of that account is it a service account but who is the owner >> so that that way especially with managing those assets it you know as a best practice it keeps things simple You can definitely you can definitely identify and and we always recommend customers to you start with the discovery, right? Um and there's a ton of best practices around what you should be doing. You shouldn't have applications. There's applications with no owners. Go look when they spun up the
application. Did they decide on that it belongs to a human, a department? Um who owns the application? Right? So it's vitally important that you conduct an inventory of what you have inside of Entra. Not just identities but the well not just the human identities. All the nonhuman identities should be cataloged and you should manage it accordingly. All right. Thank you very much.