Phishing With Phineas (Again) Hack Recreation On Steroids

Show transcript [en]
hello everyone my name is and i'm here together with my good student and friend just can adjust in order to present you our work on fishing with our work entitled fishing with is a hacker creation an old attack on more or less new mediums and with more attack vectors george hello my name is i am a student of the professional battalions i also work right now in the security industry and this is a previous work of ours during my stay at the athena research center
so as george stated before this is a previous work that uh finished a few months ago practically on april 2022 uh it's mainly funded by two eu project cybersec europe and lockhart um this is uh what we point out here it's just our personal views on these matters i have nothing to do with either the commission or any current employers of the people who were in the research excellent so let's describe the main motivation and more or less the idea of what we are doing here so practically as many of you might know there was a famous security incident that was made from someone who coined the name phineas fisher practically what he did he what he did
is that he created a zero day exploits or some services from some service scanned the internet in order to find which are let's say the available and vulnerable endpoints that use this service and try to penetrate them during this course he managed to penetrate a web bank uh from cayman from gaiman islands and hiking his way in and he provided all the details of what he did how he did it the very concept is that practically we have the details from the attacker side not from the analysis of how a financial institution is actually viewed in the eyes of the attacker and nevertheless this is rather old what we wanted to do is that given the
current threat landscape is to try to find ways to create this experiment in terms of new c2 servers in terms of new attacking methods however also to try to stress test the defensive mechanism that current critical infrastructure current let's say financial institution would use next prior to continuing it's worth noting that uh in this case we will try to instead of using an external facing asset like the sonic world vpn that uh finance are used and exploit for we will move to more realistic things as we will see later and also uh that in a malware testing lab uh it's not always uh effective simulating user activity which will give an attacker places to hide things to hijack and also
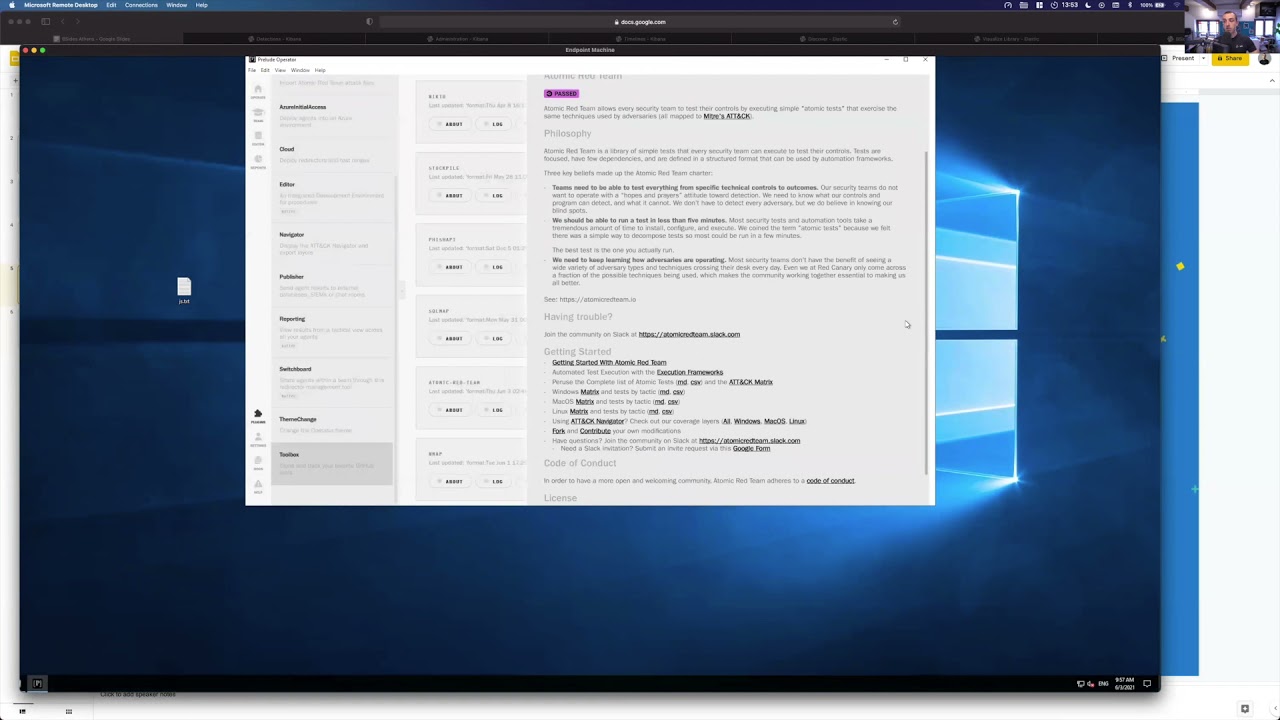
a false positive rate so which he can blend with so this is something we can keep in mind that in a malware testing lab malware will always stand out and give the defenses some kind of advantage so so practically uh as we said we were trying to recreate the environment uh a so-called serwood that finesse officer actually detailed in a more let's say recent environment here in the diagram you can see more or less the network setup that we used it's all recreated using vms practically you can see that we have a pf sense uh in order to more or less provide some segmentation to the network you can see that in the end points we have used 71 and 40 adr
and the idea here is that we try to create a heterogeneous environment where different machines are protected with different security mechanisms so that it's more difficult for one [Music] for an attacker to hope from one machine to the other so [Music] the idea is that we have positioned a citrix server in a restricted zone to allow access only to the job server more or less to recreate how things would be in a bank's secure zone george so yes we use the hyper-v server to host everything here you can see more or less the zones the work zone the secure zone which contain the citrix xenapp and the jump server we tried to make things look
as realistic as possible network wise we would have to go from here to the jump zone to the citrix server and also we use some things like clam av on squid to filter basic network traffic blah blah so it's just we focus more on the endpoints to this extent so let me present to you the offensive capabilities we had as we if you read the articles of finance fisher you'll see that he was mainly using things like partial empire interpreter things that are out there so uh modern uh apts and offenders in general will use some kind of command and control means uh things will not always uh there are scenarios where you can use
like already existing assets but you will always need some kind of malware to ease your way in and do things and so we chose five diverse yet uh highly promising malware uh that are used but are not uh that are private and proprietary not out there for everyone uh so we will start uh by presenting nighthawk it's the work of mdsec one of the top security firms at this moment uh it's a hardcore red team toolkit for from harvard correct immersed for having red dimmers stealth configurability and feature richness is in mind but the main point that makes always nighthawks stand out is basically there are two points private research that is applied uh by
the people at mdsec and as features and also the malleability this means that this is a highly uh a malware that can use highly diverse techniques to evade detection you can always attribute the specific pattern to it because there are many ways in it to do uh things there are some techniques that are some of them are being slowly published by uh the team some are kept in private you can spoof things like atw ti uh instrumentation which takes place in takes place in ntos journal which it's very hard to avoid and spoofing strategies for mini filter callbacks which is also driver related technology avs use the the basic driver technology avs will use they will have a mini
filter with kernel callbacks to monitor uh operating system events so uh some of the features that we actually used and uh had the chance to test and do our work with was the rope based system called unhooking and later full dll unhooking stealth feature and other stealth features it will make the operator's life easier by cleansing the process and reducing uh api based [Music] iocs that will occur from tools uran because we need to separate iocs that are related to the c2 and those that are related to the tools if i run let's say safety cards this will have all the is of loading mimic ads and also accessing elsa's regardless of my c2 and this will get
caught so there are things that you will try to do this applies to user mode protections mostly there is also thread stuck spoofing trying to evade uh thread analysis and what the threat did and in memory hiding while sleeping trying to disguise in memory nighthawk so that it will evade scanners there are some customized process injection methods and some process injection methods that you can use but are like uh opsec boosted let's say in some cases so that as we will see later we want blending and also network and callback related uh features for undercover beaconing you can use teams you can use like custom templates you can use many means of transfer so we
will now talk about bluetooth lc4 it was created by dark vortex and more specifically an experienced operator it's a low-cost alternative to kabul strike and it's supposed to be lesser known more effective and more stealthy some of the features include customized reflective loaders some both files bigger object files that will execute after some memory allocation that will execute in memory held up sentinel for enumeration easily configurable ttps through the malleable profiles of it and the settings uh thing is uh this product was not the most stable we have seen we had several issues with it there uh the delivery methods were limited so when you load something dynamically there are more chances of it to get
caught especially in the case of those specific two edgers we had that have some very intriguing let's say methods to target cell code itself and we tried to spoof that in some cases it worked in some cases it didn't but uh and we will see that this c2 the city's function will be highly dependent on the environment and the endpoint for example if there is an in process client because we had things like sometimes an infinite loop or we had like we tried to turn the solution into passive mode and see what gets caught and when and where uh in general we had some functionality issues but the main idea is that basic tasks can't be
performed however even though we got a foothold the way in some cases things were performed it would trigger the adrs on post exploitation and this is something we need to keep in mind that okay we've got a foothold what do we do next how do we do it what is our context and how are we secure did we raise the score for some reason etc so uh we need unfortunately uh we didn't manage to complete the scenario with this one and uh we saw we learned things uh because we had diverse ways we had like uh many ways the adrs would detect uh for different things of this tool and on access in some cases or as i told you
after some post exploitation tasks but we need to keep in mind that we need adaptability a holistic approach towards opsec and kill chains and uh stability this is something an operator good enough wouldn't be able to afford to lose in a real bank or raising the alarm as we will see later which could mess the operation so kabal strike the most well-known many much work done from the community many features now we the latest version at the experiments time was 4.4 now cobblestrike would have to say that they do some great work on pushing updates and also some things were changed in general in help systems so uh we see a lot of potential to be coming
again the top but it's still the norm for uh threat actors and the red teamers out there however we wanted to break the norm by exploring alternatives in this case we have now user-defined reflective loaders both reflective dlls we have various kits which we didn't use to a great extent because as you will see later the basically uh on touch on access kabul strike was killed by many traps of the adrs either format wise because of the shell code either behavior wise uh it was not something it's something that the companies invested a lot into and there are many ways to do this behaviorally from emulation many things uh memory inspection uh and we tried other vdrs apart from the
two we tested above and we saw that if we didn't do much work on our own or would then use some kind of state zero or we didn't use some very specific configuration or loader specific uh methods and have a good op sec wise logic we would get caught by things by uh other edrs as well that are not so known some of them based on network stuff like uh network inspection and becoming patterns like many things like memory scanning behavior such as loading dlls etc so uh as you can see uh we can try to avoid some iocs but it's mostly up to the operator and in this case we will see a research
from sophos in 2021 and kabul strike out of 405 tools observed it was it represented the uh seven percent of it so it's rather a rather interesting statistic to this one so uh no this is not a blue screen in our case [Music] those features of cobblestrike like the kits etc were not very helpful but uh i already described uh what we wanted but uh what they have to say is that google strike is also much let's say configurable and if you decide there was an interesting article out there showing that if you sideload kabul strike into teams and also make the network behavior look similar to teams you would be able to evade some kind of
inspection so kabul shark is a high quality product but unfortunately at this time uh it wasn't what we wanted and what we needed and uh and sometimes about the tools that are there there are very skill coders very still redeemers but in our case sometimes tools out there are not developed full-time by a company so this is something to keep in mind so havoc was created by a personal friend of mine it represents the other or unknown threats and in my opinion uh it's a very ambitious and very well designed code wise attempt we had some generic issues because this solution was created for the most of the adrs and not our niche thread landscape
we managed we helped paul as a team uh we assisted in the development process and we created some generic uh edr and ops safety related features and we were able although the communications were limited now they're not because uh new uh listen new beginning options were added but at the time it was still at beta same went for nighthawk and we tried as much as we could to uh make this uh solution adaptable and we managed actually to use a solution that's like you've seen the movies a young person with a hoodie coding in the dark etc uh this is this managed to work really well and we managed to complete although with some more effort and some more trial and
error and digging into the internals of stuff we managed to operate and this is some of the very interesting points of this research so oyabanda was a stage zero what this means is that it will make uh just some basic recon and execution tasks there was like uh ngoc integration go native reversal it used tcp dialer and uh goes way to execute system commands which was very helpful keylogging and discovery features it's not 100 percent stable always but that because it's a new product as well but the team uh tries as much as possible and they we have had like uh a significant amount of effort and growth in terms of product and product i mean as
technology and improvement and learning uh with the team so it's a very interesting product uh they try to make it more and more stable they will change the code base soon from what i know uh thing is it's just a static and staged binary it may be limiting at some points you can turn it into shell code if you like with some kind of recreation of bootstrap reflective loader but uh this will be unrelated at this moment uh we managed due to this nature to do things and uh we will proceed to the next slide professor
professor we can't hear you sorry the nice casualties that we have from streaming and from online meetings so there are several differences compared to let's say casual engagements first we have to note that we have two different solutions that are working rather differently um so the case of unhooking is not always an option in order to evade the defense mechanisms so for example fortinet is based on memory patterns and kernel based filtering so practically uncooking is not that easy and in the case of sentinel one like it also has some generic [Music] sorry cooking mechanism for uh in the kernel nevertheless it uh also tries to find uh low hanging fruits in the case of
typical bypasses that an adversary would try to make but also let's say through the star rules that it has tries to find many bypasses here in the environment that we have recreated it is worth it to note that one mistake is enough in order to showcase that an attack is being has been launched the idea is that currently with all these mechanisms which are monitoring all these uh system requests uh all these system calls uh the network traffic etc uh operating in an opisec way is not that easy nevertheless it's mandatory because it will immediately show that the attacker is doing something malicious as a as i noted earlier the environment that we have created is
very diverse meaning that its host has a different endpoint security mechanism so practically this means that whatever works in host a it doesn't necessarily mean that will work on host b so practically this means that in every hope that you make inside the network you need more you need to be more cautious because you need different tools and different methods something that was not pointed out is that as we said the experiments finished on april nevertheless they took several months in order to to be made and the main reason is that we had engagement with several of these vendors in order to report issues in order to report bags so that they will be passed
and not make uh more or less a red or not a red team but uh yeah exactly uh more or less a guideline of what to do when you are facing a financial institution and how to penetrate no that was not the case so we responsibly disclose issues that we found so that the whole ecosystem is secure it's worth noting that the traps of both solutions are quite innovative because in the case of sentinel one there is a drop to cover it up to cover a trap and we had the chance to beta test many of those traps in during the scenario uh before they were ready for production and also in the case of 40 dr uh
we were uh we had the chance to also check stuff and see how the real-time memory structure inspection works and it's not like casual scanning it's how uh shellcode for example would be different than a valid pe and if there would be like uh no normal uh normal behaviors so um from how they look in memory from those there's a difference of how things will look in memory and this is hard to avoid so some of the basic ttps are uh some excel files uh dll files with a specific uh icon which is very tempting to click and a specific expert that will launch specific code customize injections like uh dll hollowing which will patch the
address of entry point with some kind of shell code or we will try to like
blend several injection techniques or objects say the techniques like uh where we inject and what we inject and how do we do this msi files are well known installer files we can add actions that will include persistence like adding registry keys services blah blah whatever this could mean execute commands run our binaries use it for dll side loading which we will mention later whether it's a loader or a static binder it's a good way to blend in with an application so privileged driver based loading and vulnerable drive abuse we try to abuse other exploitable drivers that may expose for example in ioctl that we can take advantage of and do or execute our code through this driver or
impair the defenses an example are anti-root key tools which you can use for example to load the driver do whatever you want to some extent uh in the system from the journal level disable the av uh maybe some shadowing uh as there are in internet cafes you can use such tools to evade shadowing and see the coin miners the employees have planted on the pcs this is how i get my free coffee when i go to the internet so i i never uh told anything about this snitches get stitches but in any case uh we tried to use customized vendor specific spoofing and bug abuse techniques that we would things we would do from the architecture of the solution
itself to turn it around and make the edr hit itself so credential theft we could use drivers again like wintmem to dump the physical memory and parse it and get credentials reflective loading and loading of tools including clr and ps power cell tools and reflection are things that we tried to see how they would behave in such a scenario where we load the clr what's the process if it's excel through an xll for example it's easier because uh excel will be will make network connection which is which is better for coverage and also uh it has the clr loaded by default so this is a quick meter mapping professor yes so practically we try to map here
what we consider that has already been made by the attacker in green and more or less in red we highlight what are the capabilities that we have developed in terms of research development in asian laksa execution et cetera i hope that this is readable because it's far too many things that are listed here okay okay yes i will proceed so this is the offensive scenario review you can see some of the screenshots and proof of concepts this is sentinel one's timelines uh which are pretty cool i guess same goes for fortinet forensics they give you queries and you can attribute things to an actor but in depth like what did you find what kind of attack did you find how if you find
this kind of ioc notify me about this so here we can see a casual process injection with a new thread creation we can see execution of tools through night hockey we can see how the panel worked and how we managed to do some credential theft through keylogging and credential theft techniques in general how we execute tools and how we disabled the adr so here uh clr becomes for example well loaded in processes that indeed use such technology this is a good we need to take into account topsec so if i want to beacon through win http uh i will use a browser for example to eject into because it would be abnormal loading this uh
this tool for example this dll inside another uh whatever process so we need to be careful how we look both on the endpoint and on the network uh there's diverse tooling we use diverse tools to achieve the same things we try to use the kernel as much as possible and do things like impairing the defenses so we could then launch launch cobble strike a driver to and exploit also a navy solution to through a privileged scenario to inject into processes uh into the installing like a three av from the internet whatever you will find many and injecting into that protected process and try to avoid some of the traps this way of uh and some of the monitoring by other
tools and the aunties the response is like uh things like uh in-memory masking of the nighthawk presence and things you will see that you will not always be able to find it through tools like moneta p shave or even some commercial tools so this is the attack timeline we got initial access very quickly uh from via email from a categorized domain we had uh we tried to use msi exec combined with around the lll32 we used excel we used side loading into whatsapp and injecting into that free av we also then dropped a shortcut which would trigger an authentication to our farmer webdav server to steal credentials and we would impersonate the user do gpo abuse
use tools like standing then make our user and not mean try do all these sorts of active directory casual things casual exploitation things so then we try to laterally move sox proxies and we tried to execute the payload from a share or like launching the payload in some way we extract credentials with the wimpy mmm as i told you before we used casual things like sharp exec wmi or winrm to move through boxes uh we tried the internal monologue without the register modifications for anti downgrade this comes to the things we need to do when we want to avoid some certain footprint and we want to control the actual footprint of our attacks and tools
so again we tried to jump uh on the final uh server we used the now fixed vendor specific bug which would blind the specific context of processes for uh the solution we didn't have to face fa however there are recent articles and older articles even in finance feature you can see that you can steal the authentication tokens and bypass this and there are also tools you could use for something like fishing for that like modliska it's not something that's undoable but 2fa uh is always a good option to have this control is out of scope so what's next professor so practically we have contacted both senate one and fortinet teams in order to notify them of
let's say the important issues that we have found in the resolution whether this has to do with architectural misses whether this has to do with bugs or issues that we found misses in their detection or let's say gaps in the storyline that they created practically both teams have been quite responsive in patching their systems and providing patches to their customers so that they are more secure so [Music] in few days i believe that if not already because we are currently discussing with sentiment one in terms of providing a documentation of these experiments online uh there will be an article yeah exactly a quote or an article from me and george regarding this experiment and will be
hosted on their blog there is also the possibility of finding a similar article from fortinet however we are waiting for the response from the marketing team so a big thanks to all the team from mdsec and to dominic peter modexby and matthew george and of course my friends paul lungur he has a great future ahead and the redcoat labs team thank you for your patience these are our contact details and we hope to hear from you soon have a nice day