I Am Not Who I Am: Bypassing Biometric Authentication Systems - Oluwasefunmi Alabi
Show transcript [en]
Good afternoon everyone again. Um well I'm known as I mean at least that's what the biometric authentication system at the door thinks. Um but let's be real. Um you know if someone lost or if you lost your password today would you change it? And you know if I think the possible answer would be yes. But if you lost your face or if you lost your identity today, you know, what would you do? You can't grow a new one, can you? No. So, um the the whole context of my presentation today um you know, is just to show you how the almighty biometric um authentication systems aren't asking the question, who are you? But, you know, they're rather asking, do you look
enough like the JPEG we have on file? you know and that understanding you know it's basically what brings us to know that I am not who I am um quick introduction about me um the community knows me as Shay or Moj I love freedom and technology um I have a cyber security academy which I just started off um we build um CTF labs and assessments for people who are just joining cyber security and also those who are looking to upskill um hands-on technical knowledge I'm a senior security engineer at Amazon X Tik Tok and central bank of Ireland. Um, so why biometrics? Basically, um, we can tell that biometrics are built for convenience and security. In today's
world, we all have smartphones where you just from the swipe of it, your device is opened. Um it's basically increasing the numbers of traditional authentication systems like passwords and pins and um we it's basically guide wire said um it has a market projection of over $70 billion um by the end of 2030. So there's a rapid adoption of this biometric technology and humans have you know we've used features such as the faces, the voice gates, even your earlobes, the ear size, the iris to identify, you know, and recognize each other for years. But only recently um have we been able to use biometric based um systems to authenticate individual and the reason for this is biometrics
are meant to be you as your password. Uh but what you know you you look at it and you ask yourself but what happens when you can't be faked or what happens when you are fake and with the adoption that is rising you know using fingerprints to unlock the applications and various other um um technology uh or things out there you know we can't really trust um the nonreplicable identity that is being challenged in this situation. Um moving on when we speak about uh biometrics we're going to talk in depthly about the types of biometrics. Um first we have you know fingerprint recognition like you know we have the facial recognition we have iris retina scanning. Basically
biometrics is you know the science of establishing or determining an identity based on the physical or behavioral traits of a particular individual. So fingerprints DNA signatures iris face, voice, so many so many vein patterns, even the shape of your ears and more are all part of biometric systems. So we have a vast range of that. And how biometric works basically uh I would explain from this lisu flowchart we have. Don't let it confuse you. Um the biometric systems are essential, you know, pattern recognition systems, you know, that they read from the top there. Um the user we have the enrollment phase there where the user signs up um on the system and on the fingerprint scanner we have a biometric
sensor which picks um the the imprint or from the finger and sends it for feature extraction. Um while that is moved to the identity part um it identifies the user and stores whatsoever it has in the database in a store template and then moves to the authentication part of the system where the user um is authenticated by same biometric sensors and feature extraction. Now it asks the very important part is this decision making part. Um so it ask you know if it's a match in the system. If it's a match definitely it gives you access to whatsoever you're requesting and if it's not a match it goes through the whole process again to reauthenticate you. So
the actual question that the biometric or what the actual biometric recognition system is doing is just checking your impute with whatsoever is stored to be able to check um to to quantify for similarity and various other patterns just to grant you access. Now we know that fingerprint recognition on its own um we have we have cups we have various um items whereby you know moisture and grease as soon as you grab on them your fingerprints is imprinted on them and deliberate impressions on the you know entire fingerprints can be obtained by ink by grease for other substances also um but when you look at how fingerprints works themselves on each person's finger the fingerprint is you know it's an
impression um that is left by the friction of ridges. The ridges are just the elevated lines on your skin that actually grants the print. Um the human fingerprints are detailed and they are nearly unique per individual. When I say nearly unique is because um the biometric recognition systems also does uh it has like an algorithm that checks for similarity. So if we're able to spoof or able to do particular kinds of attacks on the biometric system, we can as well almost get access into the system. Um, and the fingerprint scanner basically just see it as a super smart camera that looks at uh, imagine your fingerprints the the delves on your fingers are like roads or like streets.
Some of them are broken, some of them are are split into two, but then the fingerprint scanner checks. It's just like a a a super big camera that checks each of these roads, each of these junctions to see various patterns and using those patterns is able to um then do analysis on that. Now, this kind of remembers how far apart these ports are, you know, and where they are exactly. So, when next you come in after you're enrolled in and you log in, it already just checks from the database to be sure that everything matches and grants you access. Um, the thread surface basically will look at what kind of attacks um can happen on biometric systems and some of
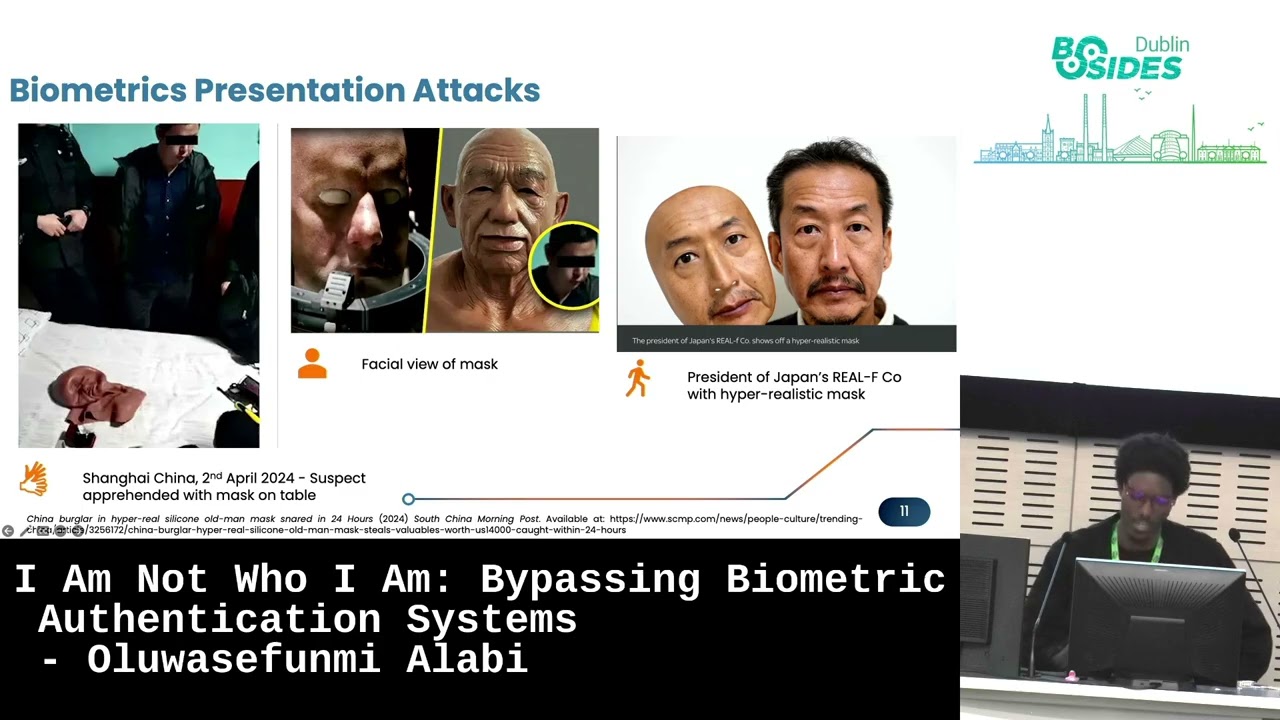
them, you know, each biometric system has its own unique vulnerability. Um, think of lifted fingerprints, you know, from a glass. Um that's basically an example of the spoofing part of the attack. So we have fake fingerprints, we have fake faces, we have fake voices right now. Um we we basically have um you know deep faked um replays attack and we also have AI powered um recognition systems that can perform um adversarial um attacks. We also have you know sensor variabilities um and AI model manipulation for some of the hardware that are out there that don't meet um certain specification and certain standards. some of the um you know the sensors can be spoofed and can
be manipulated. And moving on from that, um we're just going to go a little bit deeper into the kind of attacks that would have. So like I said, there are many different um fingerprint sensors on the market, you know. Um first off, we have the optical sensor. And the optical sensor, the optical fingerprint sensor in this case is one of the oldest method of um you know, capturing and comparing fingerprints. And this technique basically just does um it's it basically uses an algorithm you know to detect usual patterns of uh of the surface you know by analyzing the lightest and darkest part on the optical image. Um and then the second one we have um which
is the capacitive sensors um basically instead of creating the traditional image of the fingerprint you know the capacitive sensors stores uh capacitors on uh the device. So when the finger is placed on it, the charge is read and stored in the capacitor. You know, it would change slightly in the database and then this is used to generate the image and to actually check uh for similarities. And then the last part um which is the newest kid in the block um ultrasonic sensors, you know, it captures the details of the fingerprint. So basically the hardware consists of um an ultrasonic transmitter and receiver. So when you put your fingerprint when you put your finger on the fingerprint
reader um basically an electronic pulse is sent to your finger some part of it is absorbed and so part bounces back on the on the on the sensor and that is used to then calculate similarities for that. Now because of this kind of sensors they because they are very different kind of sensors in the market we have various kinds of attacks and the most recent ones or the most ones you see are presentation attacks. um basically you know the is a type of direct attack that are performed on the sensor level. So uh the sensor is fooled rather than you know being replaced or being tampered with. You're just seeing a vulnerability and you're just fooling
it. And then the other parts where the attacks can happen at the indirect um indirect parts basically through communication channels. You can you know modify biometric samples also from the database storage part. You can also use adversarial AI to um deceive the machine learning um decision engine at the back end. So these are possible um um attacks that have you know attacks on biometric systems and I'll be showing you in um an example of one of these in the demo. But when we look at real world um biometric failures um we can see examples of like researchers being able to bypass Apple face ID you know with mask and close eye patches. We can also see you know deep
fake um voices and videos of facial movements being used to bypass authentication systems. And we've also seen adversarial patches introduced into systems into biometric systems that have been used to manipulate them. Um an example, these are just some of um the top cases that we've seen in 2024 and 2025 um across boards. And we also have some that have used um the 2D 3D mask printing um you know to actually bypass biometric um systems. And for the defense strategies um that we'll be talking about. Yes. Um we we have a point where you have to incorporate liveless detection for the fingerprint. So it's smart uh movements warmth you know blinking pulse poopy dilation is basically uh behavioral
pattern recognitions but while this is also implemented I mean we have to also follow the security principles of uh defense in depth um you know so having multimodal systems um dual factor authentication or dual forms of biometric authentication like something you have something you own uh you know a face a voice a pin and then also um AIdriven spook detection uh and logging and monitoring on whatsoever ever system is being deployed is um also part of those that are important. Yes, biometric um you know biometric behaviorals um analysis is is promising and it's it's it's harder but it's harder to mimic but it raises concern you know over things like false positives. So regardless of
uh what systems you're choosing to implement or what systems you're choosing um to as as defense as your defense strategies you have to consider all those um in place. Uh I'll be moving quickly to the live demo. Um here for the purpose of this live demo uh a request was made to the NSIT database special database to use some of the fingerprints that uh I'll be speaking basically about an adversarial patch um you know that can sort of be integrated into a system that would mislead or would um yeah would basically deceive the system um with manipulated and enhanced fingerprints. So, you're going to be seeing the old fingerprints being manipulated and being modified and then
used to try and um log into the system. So, let me just And by the way, uh I like to push to production on Friday with my full chest. So, let's hope this works. Uh yeah. So the first thing here um let me show you this folder. Ah yes we can see it's perfect. So I'm just going to take this off all this uh files in here.
Okay. Um just going to run this. So what this does is um we have original the data set gotten from the NS the NIC um database um we have the original fingerprints that are not fully enhanced. Some of them have flaws in them but um what this tool does is it picks that fingerprint enhances and modifies it. It does a similarity test then passes it through the authentication system to um try and get access. So it has processed um nine original images. Let's just see them. Um enhancement successful. So yeah, single enhanced. Um let's look at this one. So these are the single image. This for this is the enhanced version. And then let me show you the
original version. There we go. So we have these two side by side. Um, and then we're going to try to I'm just going to run this also on the background.
[Music]
Okay. Yeah, there we go. So, uh we can just see the side by side and we can see that some part of this one um is broken, some parts are dark, some parts they just have like flaws in there. And this software has enhanced this to use to bypass the authentication system. So, I'm just going to show you that the biometric authentication system play. Um now what we have here
so it loads the original file into the database. The original files are already in the database and each of the fingerprints that have been uploaded that have been enhanced are checked across everything in the database for similarity checks and it gives us um an actual um status to see if it's granted access or not based on the similarity level and um this was implemented here. Okay. So here we can see that the database stored uh this is the fingerprint the first fingerprint stored in the database and this was the fingerprints that the enhanced fingerprint that was used to check and we have a percentage score um of 79. Uh basically this was programmed to have a
pass rate of 70% uh 70% uh acceptance rate. Um so it depends on also how you tweak and you tune your authentication systems and the decision the decision logic behind it to accept um the level of false positives or false negatives in your system. And we also have this enhanced fingerprint here that also has a 79. So these two fingerprints are most likely going to get us access into the system. And we have an aggregated result here that says two out of the 10 images that we tried um were able to um successfully pass the system. Uh now if you look at this for example even though the image was um it was modified and enhanced we don't have um a
direct match in any of the entries in the database. So um this gives us the threshold of the logic that we can set on you know like I mentioned the uh acceptance criteria for your decision logic of the system. Um that's just basically uh about the demo. I'm going back into the slides just quickly for to round it up.
Yes. So the future of identity um in this case you know we know that biometrics can't be changed once it's leaked um and we know that each system has their own risk um you know and resilience basically so fingerprints are static and they're easily they can't be easily replaced when stolen so what should you do you should have multiffactor authentications you should have zero trust systems if need be you know u biometric data permanence also you know and ethical issues might arise in terms of your retention policies around keeping um some of these things. So um have guidelines, have policies, acceptable use policies and um retention policies on how you keep the data. Um also exploration of you know
decentralized um storage uh for the future. Uh blockchain in this case might come in very handy for some uh future development and um integrations. And um yeah basically um biometrics like I said are promising but they're harder to mimic and um they raise concerns over over false positives. Um key takeaways basically will be always assume that spoofing is possible and also test for it. So whatsoever you deploy in your system, whatsoever your authentication systems will always be always make sure that an assessment is done extensively. Um also have layered defense is very critical not just the traditional multiffactor authentication but for biometric system liveless is very very important um also red teaming and staying ahead of um the learning curve.
Uh with that brings me to my end of presentation and I'll be open to answering any questions. Thank you.





