BSidesCLT 2021: PowerShell’s Return to Power - Dahvid Schloss
Show transcript [en]
hi thanks for for coming to my ted talk about powershell um my name is david schloss i'm the offensive security lead on cyber and risk what that basically means is i'm uh i lead all of our red teaming pen testing anything that kind of emulates a criminal activity or things like that i'm running that um real quick just because the obligatory we're a small company i like to throw us out real quick and we do offensive security testing defensive security testing and compliance it's a it's really fun i like it i like to shout out the company whenever i can so let's actually just jump right into it and talk about today's goal today i want to talk to you guys about
powershell and i want you guys to leave with a healthy paranoia around it uh the way we're going to do that is we're going to first talk about the allure of powershell you know why it admins love it why attackers love it we're going to talk a bit about bypassing organic controls like amsi whitelist the science script execution and then we're going to wrap it all up with some malware deployment and how you can protect yourself so why do it admins love it well it's everywhere windows linux mac i have it on my linux machine you don't need to learn um bash you can just use powershell on linux to communicate with windows it's it's great
it's easy to use and learn uh it's one of the first applications that i learned even before python and it enables more functions around remote administration so you can take your hour-long really resource intensive task and turn it into five minutes it's great so why do attackers love it well it's everywhere it's on windows linux mac i have it on my cali machine i don't need to use impact it to communicate to windows from linux it's awesome it's uh easy to use and learn there is a lot of resources out there for learning offensive powershell techniques and they're written pretty well and it enables more functions around remote administration so it makes lateral uh lateral movement techniques
relatively easy to use so you can see that the attackers really have the advantage here i think what a lot of people forget is when you have access to a terminal scripts can be run entirely from memory you can just copy and paste there's actually no reason to have a script on disk which makes this really difficult for like signature based avs uh to detect this activity it's scriptable.net uh we'll get more into that a little bit later but it's the main reason why we started seeing a shift from powershell to c sharp and the last reason why attackers really have the advantage here is organic security functions are constantly getting defeated people love to just find
ways to defeat microsoft and then they brag about on the internet and because they brag about it on the internet then it becomes uh de facto knowledge for attackers so let's get into the meat and potatoes of why we're here the first part we're going to talk about is this organic control or bypassing organic control and the first organic control we're going to talk about is script signed execution for those who don't know this is a control in powershell that will stop a unsigned or untrusted script from running what most admins would realize or recognize is this uh when we try to do execution set execution policy here to bypass we actually have no permissions to do that
uh but this is relatively easy to get around and it's the reason why this is not a a security control so really when you want to go and set an execution policy to say bypass which will make it so you don't need to have any sort of science script you can actually just execute powershell with tech ep or tech execution policy bypass and it only sets it for that instance um this is the reason why this is not a security control microsoft has said it's not a security control but only in their forms the way they write this out in their documentation uh they make it seem like it is but it is relatively easy to bypass the reason
why this works in this way is when you run the command set execution policy you're actually trying to change a registry key in the hkey local machine registry hive which requires admin privileges but the tac ep or attack execution policy flag is allowed to be run on execution of powershell and it'll only set it for that instance instance so you're not changing it for the entire machine um i wanted to throw this out first because i have had clients in the past who told me that there's no way i could run a script on their on their workstations because they had this set execution policy set to restricted so now that you know that uh don't treat it as such
so let's get into the real mean potatoes of bypassing we're going to talk about bypassing amz for those who don't know what amsi is amzi is the anti-malware scan interface that microsoft has pushed out it's an interface that allows security products to hook into different applications like the windows script host or vbscripts office macros powershell you name it in the context of powershell it blocks known malicious scripts and functions so the most common one that defenders and attackers would see is this uh iex or extended command download string um this is this is quite used a lot uh and mz will go out and actually just block it it sees it as only being a
malicious script so you can't run that while empty is running additional to that it'll look for known bad strings like mimikats bloodhound power view you name it it'll go out and stop the execution of those scripts some antivirus applications that run this right now are like mcafee sofas kaspersky windows defender duh uh and there's probably more i just really didn't dig too deep into it is microsoft doesn't have something that's readily available from what i saw that lists out all the uh the security products that use it so now that we know about know about amsi how do we go about defeating it well it's pretty simple uh powershell 2.0 is usually installed by default and uh
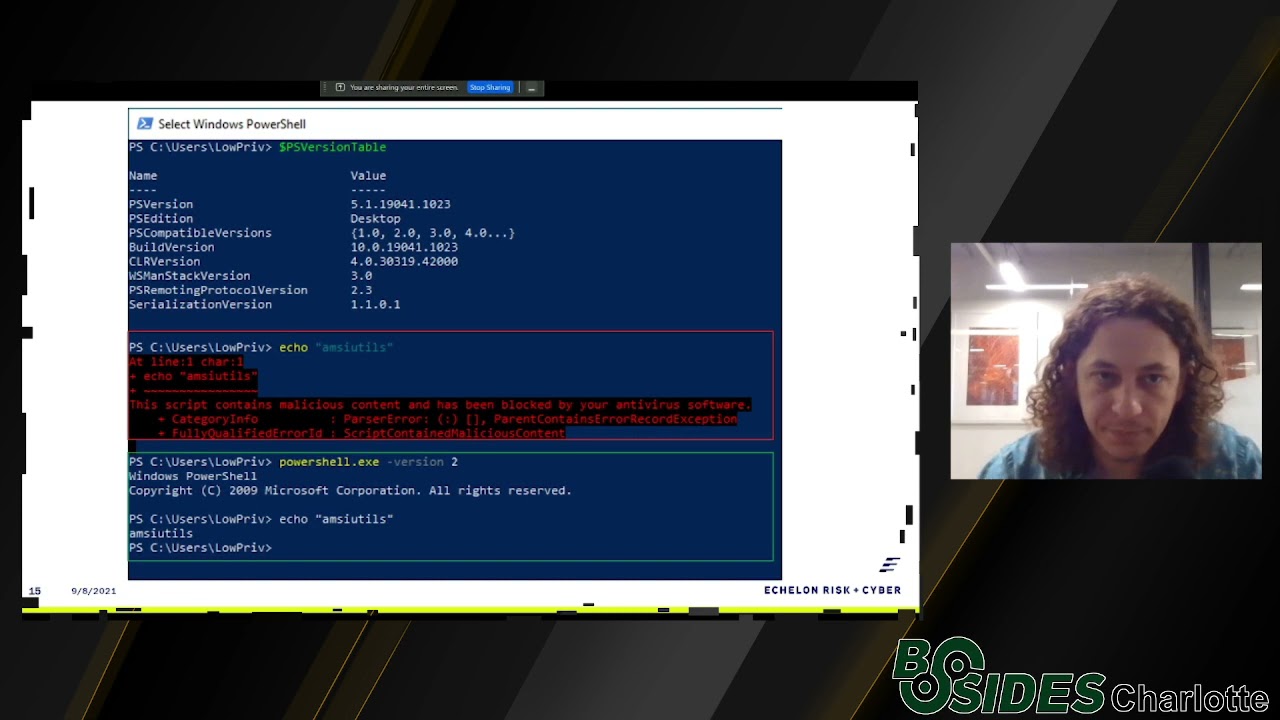
it doesn't have amzi so because it doesn't have amsi it doesn't have automatic script lock logging on suspicious scripts which uh then thus it defeats two two different uh security functions right there right so to caveat all that uh powershell 2.0 does require.net version 2.0 so that is not installed by default but if you're if you're running old applications that require net 3.5 then 2.0 is going to be there and you are vulnerable to this downgrade attack the reason why when you look at like powerview.ps1 it tries to execute powershell.2.0 so to run this attack really really easy in the screenshot uh we can see the first thing i'm printing out here is the the ps version table the
reason i'm doing that is so you can see it is running 5.1 which is the newer version of powershell and i'm trying to echo amsi utils the reason why i'm not going to amaze the utils here is amze sees that string as being malicious as you wouldn't normally call it so it just blocks you from being able to call it it's a it's a test function but by executing powershell.exe with tac version 2 which is it's that simple you can now echo am the utils so these these uh really easy way to to get around right um but what happens if you don't have 2.0 net 2.0 how else can you set amzi into a failed state
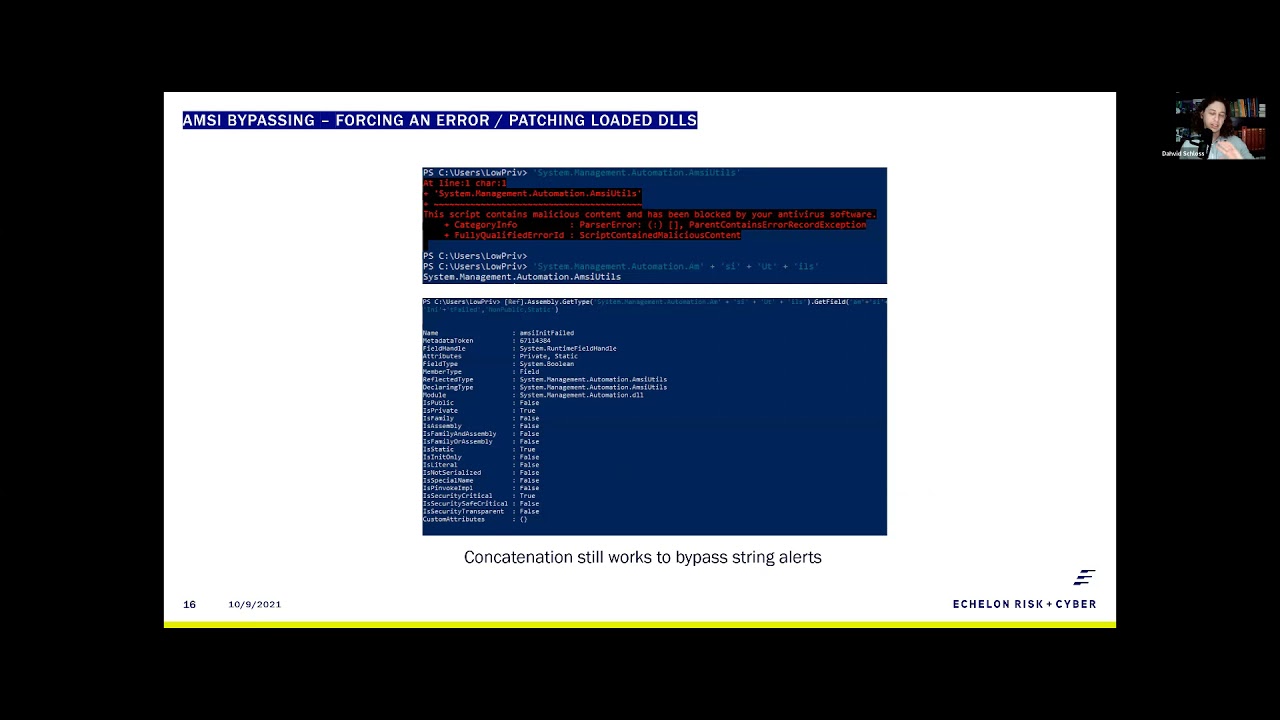
uh well quite simply when you do try to defeat amzee uh all you're trying to do is set the amsie and it failed to true the reason why we're trying to do this is amzie doesn't have a recovery function so if you crash it or set that amazing failed value to true it won't restart and it won't won't read anymore which is great for that for that instance so the most common method that has been used to defeat amsi was uh the genius matt graber came up with this reflective method to call the amsi utils function and then get the field empty and it failed and sent it to true this was done back in
2016. um and since it's been quite a long time you you know it's it's not going to work anymore but up until about last year this bottom command which is just concatenation of amz utils and amsi and it failed did work and and as you can see though now it doesn't so uh we did a little bit of digging to see what was going on and i'm gonna show you exactly like how simple it was to to get around this uh the first thing that we needed to do was figure out does concatenation no longer work um well simply put it no concatenation still works you can still defeat amsy that way in the first screenshot i'm just showing
you that mz is is running it's still alerting on ams utils as being malicious and when we do our simple concatenation of amc utils it does print so where is it starting to get caught do we need to go one step further let's see if we can get the field so this bottom uh screenshot we're doing concatenation on the function and then we are finding the field for amsi and it failed and we're actually able to print all the information so still works and you know in 2021 which is great uh what really ended up happening and shout out to the uh the secure this page um you can find their link at the github
link below has a great write-up on this but it turns out that amsi's doing a little bit of of some regex so when you go git type and get field and then try to set value the regex code then goes all right let's concatenate the information and see if you're if you are typing in hamsa utils so it captures all that which is which is good um but rule number one when defeating anything in powershell is when in doubt and code it out at least that's my rule um so just avoid base64 but because that's organic to powershell but you can use hex so taking the concatenated string like amzee utils and formatting to hex we can
see that our little hex code does print out amazing utils without being blocked so now that we have our hex into text we got to turn our text back into hex which gives you a nice little dr seuss rhyme but uh a relatively simple one-line code which is just splitting up each hex and then converting each value back into uh a character we can print out anti-utils very very simple kind of bypass so using the still this matte graper method we can uh execute just using hex so what i'm showing here is i'm typing in amsi utils show you amz is functioning we copy in the now hex encode hit enter and type mzutils again showing
that we have bypassed it so a a bypass method developed in 2016 with very minimal change is still viable today which is pretty concerning right there's other ways about defeating amzi though um there we go the there's a lot of text on the screen and you don't need to copy it or anything because it is just rosta mouse direct method which is patching the dll i think this is really cool and i wanted to point it out because you're able to patch loaded dlls in in powershell using like c sharp code this is just c sharp being ran in powershell and it's loading up the mz dll finding the first couple bytes of amz scan buffer and then
patching out those um first couple bytes so that it fails uh what i think is really cool here and why i wanted to point it out it's proven a point that you can do a lot more than just editing amsi from this regard um if you were really sneaky you could probably reload hooked dlls and to get around some some common hooked methods from edrs but what that looks like is very similar the first thing i'm going to do here is type amsy just show you again that it is running and now copying roster mouse no editing took place in this uh just copy and paste hit enter and when we rerun amzee utils it's going to come back and show that it
is defeated but this isn't getting caught by amsi at all and this has been out in public for quite a long time the only thing i would uh caveat on this is it is using a function called add type this creates a temporary dll on disk and can be read by a antivirus system so it is one way of getting caught but you can use matt graver's reflective dll loading to get around that so what happens when you can't run code to bypass amze right like there's restricted mode or constrained language mode something in that sense well the really cool thing about powershell is it's just a bunch of dlls loaded on top of the command prompt and somebody was
like oh yeah this is like a power shell bro um so you can just use living off the lan binaries to create your own powershell we won't get too deep into the code here is now we start to venture away from it but it is something to be aware of as it does concern our application um the most common one that i've seen and the one i've used for years is this ms build shell which is a c sharp project file that you can just build using the msbuild.exe so what i'm showing here is you have a command prompt i'm going to type in ps version table that's to show you that there is no
powershell loaded in here and i call the ms build.exe binary which is included by default with the.net framework version 4.0 and all we're doing is building a our cs project file which is named ms build shell and as you'll see it'll come back with an error that error is just the matte graper amsi dll there's no editing there but you can edit it and now we have powershell right and powershell 5.1 i exited out show you that we are returning back to a command prompt the only difference between this and a normal powershell prompt is that you don't have tab completion but if you don't have access to be able to execute powershell because constraint language
mode is is there you can just load the dlls and it'll work the same way some other ways of doing this is like the powershell dll project which uh you can use multiple different living off the land binaries to to call powershell and personally my favorite which is the sync app publishing server you can use netcat to actually capture a callback from that and that would be a a powershell prompt shout out to i read team for some of these great red apps i would definitely check them out if you guys want to learn more about uh app locker restricted language bypassing so why do we talk about all that why do we talk about amz for like 10 minutes
here well it's all getting down to malware deployment uh you know the bread and butter of of any attacker um for for malware deployment within powershell all you need to do is really take your c sharp code and turn it into powershell and vice versa uh that's exactly what we saw when people started moving away from powershell into c sharp they didn't really have to reprogram anything so execute malware we only only need a few things uh we need virtual alec and create thread from kernel 32 and we need the marshall service to be able to copy the shell code into the allocated memory and then the next thing we need to be able to consider here is is avoiding avs
despite not needing to defeat amsi again when you do create a new thread the antivirus does have the capability to read that so you need to still do some shell code obfuscation reflective method of calling dlls things like that so this uh this becomes quite easy to do uh as you can see this first line here is importing the virtual alec from kernel 32 and that's just going into c sharp the one right below it that is using the matte graber reflective method to load virtual outlook very similar uh you know you're still setting it as an integer pointer and then you're calling a few unsigned integers it looks almost the same and the same goes for when you want to
actually execute virtual alec the first one is c sharp code and then the next one is our powershell so translation becomes relatively simple especially if you already have something available in one of the languages so then the next piece would be how do we obfuscate our shell code well this becomes even easier in my opinion than c sharp as powershell reads bytecode as decimal instead of hex so zero x zero zero is still zero zero zero and zero x f is two five five so you can do something like a caesar cipher which is pushing the bytes the right or the left depending on which way you wanna go so if we do like plus five on a caesar
cipher zero zero zero becomes zero zero five and uh two five five becomes 260 which is in a illegal operation as it's an integer overflow so how can we fix that pretty simply we use modulus and powershell has this nice little modulus operator which is the percent sign so now we can do 256 minus or plus our offset modulus of 256. and if our offset is five zero zero zero still becomes five and two 255 becomes zero zero four so we've solved that uh what that all looks like is is this um we're going to run some interpreter code from our powershell script so our interpreter callback is an https reverse callback um some things to note before
we execute code the first thing is the powershell pid which is 11496. i'm going to show you that amzi is enabled here just to show i'm not cheating um and then another piece that i wanted to show off here is a different way of importing code i've talked a lot about just copy and paste into a terminal but you don't always need to do that even with amz enabled you can still use the net web request function to create a new web request and then download that information into a variable so that's what we're going to do here we're going to download b-sides.ps1 from our server it's going to load into a variable and then we're going to use the extended
command to execute that variable into memory now we can call invoke b-sides give it our offset value of 66 and hit enter uh one thing to note is there is no alert like av alert right so when we go back to cali we can see that we do have a session that is running we do our get uid we can see our low privileged user and our pid is 11496 which is that powershell interface so we are now running meterpreter within there without being caught so now that you may be a little paranoid and you've seen all this stuff what are some of these things that we can do how can we fix this well quite simply uh one of the easiest
ways to do is just disable powershell um i don't know of anybody who would ever give their users python so i don't know why you would want to give them powershell uh definitely look at expanding your application blacklisting not everything microsoft provides to you is safe i'm pretty sure most people remember dd auto that was fun i use ai-based security products things that hook into kernel 32 or nt-dll to help determine maliciousness is always great as well as being able to detect if a sensor has been disconnected those are quite important and then the last piece is is a little outside of all of our control but microsoft definitely needs to start fixing some of these these holes
in 2021 concatenation still works and i think it's partly because we stopped paying attention to powershell when everybody moved to c sharp so these security controls didn't get as much love as one would expect so it's definitely star it's definitely time for for microsoft to go back and and look at this and start fixing some of these very simple um bypasses so past that here's my information again if you guys want to download these slides you can go to our webpage and slash b-sides and and get these slides yourself um if there are any questions i am willing to answer them now thank you