Ad Weary
Show original YouTube description
Show transcript [en]
everybody I'm Jeff Wong is to talk today about adware through the background of myself my Cisco Panther these in your closet or one of the managers former investigator I did a lot of that I guess you guys stuff I'm basically looking for all the things that I'm really bad and I will hug and go his mystery for identification his advice and camera ratings so anyway it's a Cisco do is a response security architecture before that I had worked at the University of Carolina at Chapel Hill live in Nashville you know every year my thoughts and I organized a conference in Amsterdam go for the floor has to be responsive security teams you go take a
little bit of air show up it's time to be signed by the top of that system is their response groups of smart defence focus some long information there's for the food air and some cones and I put together both commanding can it goes into our philosophy our strategy our operations or how many things in Cisco so you're should I check it up so memory so that you know why we're talking about everywhere it seems like something from 1993 right whether above or other sentence ago people use right for whatever reason right it's still relevant today which is why I would grade up and nineteen and Cisco you know we look at all the security monitoring
you know yes alerts but you don't the other alarms they're coming in we started noticing that quite a bit of the vineyard stuff is coming into these plugs hazard right we're also seeing a lot of issues on the hammer on diddly he thinks going out those should be internal only going across the border so he looked into a bit more thought you know ever is pretty sure that culture sooner or later to be happy about that they should investigate it and see what the impact really isn't school case you don't know Sysco corporation 120 countries and 3040 thousand seven one these massive company right step all over the world so we have quite a large
footprint in tech so you can imagine the a massive algorithm salsa or you do they buy why you know we're talking about that what it is what I'm gonna still do it and then what does it look like at the enterprise and now I'll save a little bit of time at the end you can talk about the solutions although they were pretty obvious and some pieces they're not excited so miss your mother book one of the best programs ever written for Windows ever but why should you care there's a lot of reasons why I wonder about your personal informations that state if you're giving away your data whether you choose or not this may be but it also gets they can get it more
nefarious think about things like kids being online right looking at PBS websites for kids low side skiing those like you know when you're cute behaviors locations cliques are being attractive in school weird right when you have federal regulations in place to kind of look after that it's happened down I'm very less I just show you a little bit more about kind of the child are perhaps the protection that does have its role and where this but also I'm one dimension of like that you know everybody's talking about ransomware today right that's a sexy thing in malware today everything's ransomware because it ties with the real world but people understand about kidnapping because they understand what
ransom is right it makes sense people normal technical right into us it's going to pull this off using version sometimes apiece is really good a Christian or whatever most pieces pretty poor in there easy including their use no interesting stuff they're holding data hostage so this is exciting interesting adverts are late right it doesn't do that kind of stuff but I think you'll see hope you'll see under this that actually does have significant impact or overall that's how things are happening today and I think Edward from what we've looked at has a much we were massive presence any in corporate networks impressed well absolutely because it's just not as is mutters right and it's often backed by legal entities
they're not quite the same thing as experiment guys so we did a lot of digging almost all the error that the softly mrs. scoop came through browser helpers toolbars applications slick step from C minute alikom Softpedia you guys my Gruber a couple years ago in math it was a distributed SourceForge and it was bundled with some adware and computer where I'm already pissed off about that right so a lot of patient that as well that makes things a little bit more difficult to detect I've been pretty good at finding by Theresa finding plugins other stuff is a little more challenging what being is that the most common methodology we see coming through what else is ever would that mean well
it delivers ads obviously that's the app are they aware of shoe and maybe redirect you we pop up things that me good with Billy at websites we're drinking clip from that kind of stuff oh maybe they can do things like monitor what we do right monitor your behavior and most importantly your preferences and your patterns all right which can tell a lot about you I think there's a lot of research we'll get into a little later on but you can find a lot of that person things interesting everything else is grayed out that may come up later the other so but I want to kind differentiate between Edwards for an hour of course the hilarious usual licensing
and the privacy policies
[Music] this is real this is real all right hello everyone who surely see this right when does an explorer cybus is so surreal yes where the cities might come from Windows 2000 Oh excellent or expertise high speed it is an XP you know we got a copy of this image [Music] okay all right so this is good partner progress is good partner attention Cisco's Network gets pops / Cisco right there anybody said what topic are a remote access trojan who annex estrogen takes snapshots and screenshots at the desktop Mike seen the investigations team and pulls these screenshots off during an investigation so thankfully this is great presentation father uses his image of years now it's
great that right on they're thanking because it helps me to get this right addition there's a couple of funny things here it'll talk about one decision actual system it'll compromise how do you the rack ordered this was t confirm a spanish-speaking country did you see a lot of stuff in Spanish but what really opened my eyes to this problem we were looking at this thing a couple years ago it was like and be really installs terminal more seeing that really kind of hit them to me a long time ago that I think they likely might mention it that the user awareness stuff in cosa is is important I agree it's argument warranty we also agreed
it's never gonna stop you're always gonna have someone that wants to install ones toolbars or five toolbars [Music]
[Music]
this is my really little Stephanie want to get access to stuff for free right and people don't have the skills to do it they're gonna do all kinds of crazy stuff to get through things and so nothing real to stop here you guys forgive yourself but the one that I wouldn't hold out for the hollyrock my past GUI Peters dishes and watch me tease you penny mind as we go through some of these things so we have this little session here there's I'm preparing to do the spyware so anybody review what this is from superfish
that that was considered spyware house a really big deal really big deal but what is the spider right well still that the question will you love right a lot of eighty there's just a potentially unwanted right here's a good one a program or there's a wanted application anyway that place to say put potentially and then maybe you don't want this if you do and if it was somewhere should also have in some cases in many cases you actually have a lot of other clips right like it's not your route certain software you want a future without question I've asked you to see all that stuff and then you know different permissions you can that and
in the big music whatever spyware is really that's where things get a little bit degree at you know the ad coverage sucks would see as on your face you click on things or to get your computer make you click on things quick revenue-generating so whatever let's go to the next level of nefariousness bad stuff from good or better you know we're in the middle with spyware right and these were getting worse but they're not as bad as they can be is their answer at least it's not that but what's the difference you know kind of getting into that I would hear talking about what makes my work eat in that regard and what makes it it there to
control the unwanted program at least idly right so look at the that's right you know malware is that where are you with that right and miss you hate to have software to remove it or install my block by your any virus encryption for that reason spyware or petition and running program is also bad right looks this it's less mad because you most likely agreed to install that's awkward right you might have put through you might done something else you really wanted to watch that movie you really wanted to bypasses you any restrictions states is your lab all right I really want to watch that movie okay so the big mark right there so he's also right spyware vendors developers
whatever you want to call them they saw that early he's really not that bad so it's not malicious code okay but it offers a framework a platform for third party and fourth party affiliates to inject so anybody can buy ad space or ad network I mean put any anyone in this that's well on top of us so the same thing happens with the spot around right will posting this same thing and then so the big takeaway here is there were companies sued by the companies that developed yeah we're so Edward developers adverse favorite companies can actually potentially could potentially review action against speed the semantics in that right because hey you're blocking my application you're
debating and you're surrendering answer say that this is advances what was just come up in our software has Richmond sis just like yours is right and so why eaters have done this they've said okay well let's just call my weights potentially we wanted we can't taste malware we also can't say it's legitimate so we're going to give you the option well you want block pumps or not right we'll see some interesting stuff then they'll leave this finely tuned once powered I think everybody in here should know about where I got already it's party on this right this most of these other things up here of course - Beulah is you're not really stepping it but I thought you know do
things like take you data for hostage ready and stock people use really nasty stuff we all know what is right we know the difference and I think that's the that's the big takeaway when I was friendly to find in my head what's the difference is that it's kind of like pornography right you know it when you see it burst opportunity you know we see in rocket ups obscenity you know be sin and sitting there right but this slide here really illustrates how the core concept of why I'm talking today and its really kind of about I think I'd like to hear what folks have to say after it earlier but is interesting debate right what is the different and like should
maybe companies be forced upon this stuff right when you know there's millions of dollars happening in the back end revenue kinds of stuff is happening it is it it is an enterprise is it a criminal enterprise you know you make that argument right so it's open every situation that guess what it boils down to this there's the motive make the difference of the Installer or the developer how about the delivery mechanism right did you miserable carcass or wasn't wasted on you buy some dinner okay is there you do you care does it matter did you intentionally install the software or not you know that's a big one and the really cool thing is you know
it's one of those things that this is a really weird argument but you know is your legitimate saw part being slinky innovations or other techniques detection in tech support our debugger detection right why would you not other piercing arrow if you've got nothing to hide right that's gonna rip flood maybe there's opportunities from everybody forgot it there in the dead process they advocate your debugging or whatever I don't know kudos why right but the point being is net we didn't a software doesn't see what we do now right that's really a useful way we looked at it in terms of are the risks or organization I apologize but there is no organization was what we do right yeah we detect it
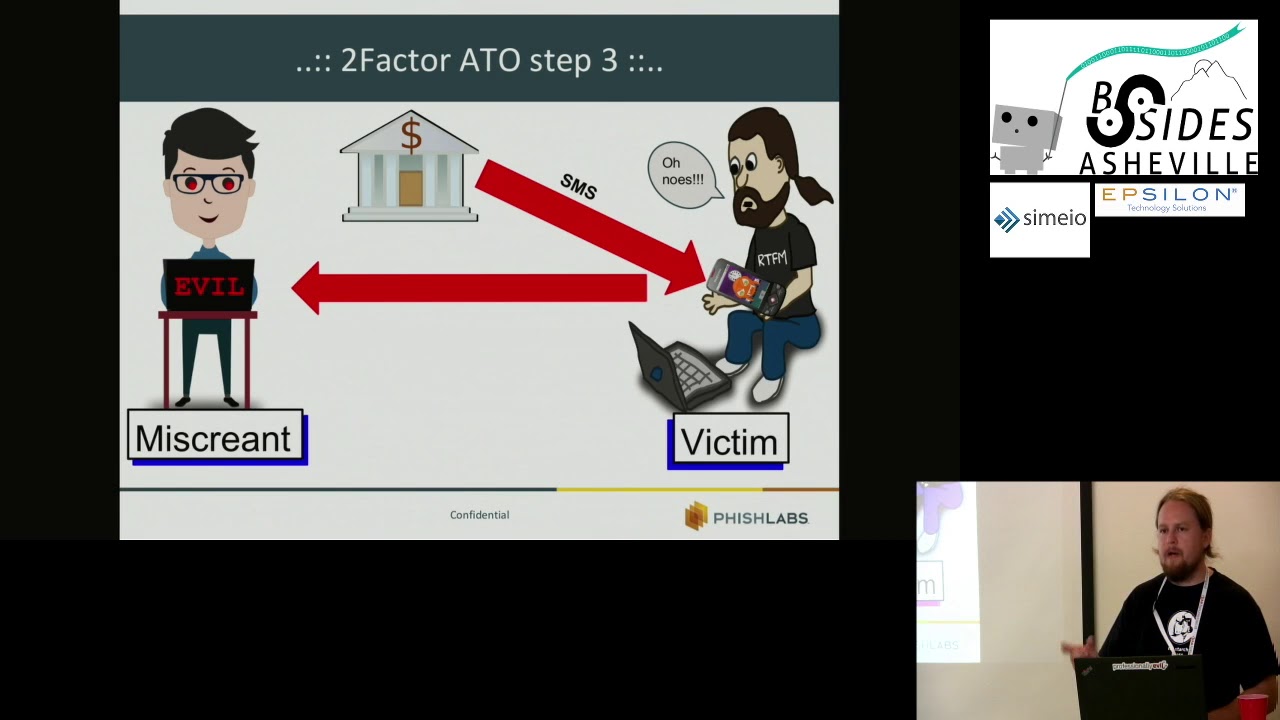
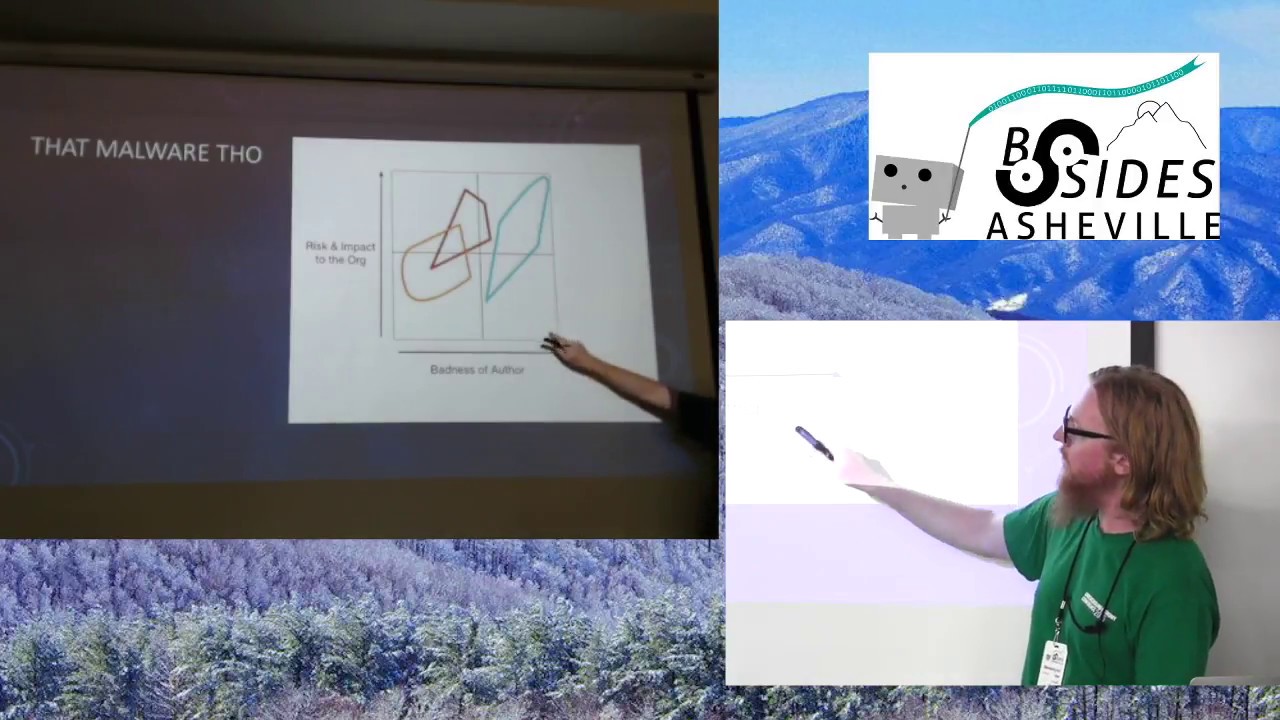
respond to it but we're going to put an adware spyware right and so you kind of get this ID like all of your screen and actually the ability slightly essentially or yeah simcha what you're seeing is on the right hand side this is the side is what we call power all right this is another side so you see the risk of impact your organization is really high yeah the battle of the creator or you know the crew monitor or developer whomever else kind of who's that expensive that was really that in the worst of the worst alert from here okay do we have the red the middle and that is the spyware right so that in some
cases we've seen Square where situations in which people are they have a toolbar and they have some browser a graphic and what it does is it logs your be really dirty so now every URL our internal intranet right is now leaking out to the third party site they're developing a searcher before we have it looking at content that we have they might be looking at product defects soccer you fix that Cisco might have right well it's anything right coding for projects whatever else secret stuff that we don't want the world to know about right that's our business to protect that there's one where the risky impactor or be super high now when it comes to that so are the test a little
bit because then the yellow one here is admin which is still herb is it somewhat of a risk but most of it is just people taking advantage of the way the internet works and we advertisement works right you want to put up an ad network to add software and have manner that's how revenue works on the internet right so the normal but if you see is scale here a sliding scale people doing weird stuff with the other as well so it's not a bit about the mentioned innovation this is an interesting blog on to ask research before you can see that over here on the side this is under to start replication they're intentionally installed it does
change your search so you have blue or whatever else and then basically this search this application doesn't interesting stuff now I'll let you read the blog article but essentially this is application that doubt that the first package installer you get it doesn't checks to see you know who's running the applications are there other things happening if they're a debugger present is where things happen if someone easy to pull this apart right it was fascinating actions to at least I stopped by you each of superman' teachers are article there's a notice to take a seat this is this purports to be legitimate application but it does actually check to see if you're being if it's being pulled apart so well and it
took a case what we ended up doing was basically we pulled it apart from the rehearsing medians are responders we worked in the consulate divide American interior to compromise that's what we do killer boots is one of its host based network based whatever else we could get human behavior of a heads up for a little ticket so what we did was we didn't we developed a search to see if it was massive advert wasn't hard we found him with URL look at your relatives with our total URL sorry I'm sure sweep you may have used that um you give her money back from the varsity well you see that five companies companies actually detected this has a
picture camera so we know some people aren't you sending that's it's okay you know click pretty difficult when you see the pulling apart we see to this under search application still pops up here as is diva is another person right so again unusual why I know we can see some of the other columns you got a product right a certain application you see the live I'll be cutting get dropped out so trade baby great now we've got more indicators here anybody at Cisco that has any of these files that smell any specific paths one of the likely has this is my work and stuff as well right so we should be able to figure out you
know who's better to spell or is it out of network without you know having to do a lot of recent murder the Olympians work we actually did was the elusive will query with Microsoft's sequel database SCCM clothes from the CCM standard configuration editor creates literally this is what we did so if you recognize this interface with one of the files explode your source around with the network so we've had them they're here Israeli is not using out the stated here but you see there's a Bob came out there's a guru the Patil so here's here's the size of the pilot is using ready to have it's all for those new things that were so giving idea that
ended up finding I think them 85 people ahead installed which even subsystems not too cute but still we think about 85 people what their browsing habits are being dumped everything that they're looking at online petition being they're partying solvers hold its hold again right with our information that that one in this room so what gives them their right to do this right how can they do this I installed this software on purpose I'm going to do this yes in the right isn't there privacy policy or their end user License Agreement which are frankly ridiculous right they almost always are this I think is from sir whole lot Indian we're going to talk a lot about me and here here's a
little snippet from rolla's privacy policy Liberia all this stuff let's just trust me that's all that what this really says here is that we're gonna compete on your system or arsenic virus which could be anybody right or you know the guys who actually sold a lot to recognize your gross reading that would be and receive information have to be based on your appearance interests of Heritage's the Brody that you session any gains to middle Scrooge's so they put a go get a machine right here can you do swim research again we just looked at here's another here's a different right this one this is blue read on my screen I can on you guys so this one is actually even
worse what kind of stuff this information includes information like your IP the UID Parker software model of but never no one was this one here it actually until a report back what items you might have put in your online shopping cart right so even if you were like excluding things in there and we're into being good buy them right as a joke maybe we're just looking nothing now splinter search knows a lot of search for it might actually try to suggest that to you in future or related products so she might have actually want right can these get early we're safe so that gives you a demo it is another thing I was going to
show you the end up and I'm like a clutter practicing policies interesting enough that kind of good about that for sites to find privacy policies they were blocks can actually get them out who's a good thing I'll show you when they look at I feel it better so that's the scope we've got two primaries at knowledge we use or for blocking traffic okay it's quite a few the two men one trip of course the Edward are web proxy and our RTC are not halls in the DNS I spelled them about the NS are easy and responsible for defending a network come talk to me food is awesome and we use it all the time you can see
150 other everybody milling it and I think in the several month period as I physical objects we took it we had a nation do with bad Isuzu campaign or advert and drop them into a response policies no notable because all this woman's right every time I they try to resolve on Khao Lak it's keeping idea that's pretty massive right here is another image probably unreadable she's gotta see this is for web proxy these are some of the categories that are that were plug on some of these malware activities right so you see by far and large that the main associated with risky or offensive content and most cases actually means that we're definitely risky business when you see
up here how how that works all new the numbers in fact and take a look at this right here this was smart web proxy learn this was over the same time period from May to June he put this food back you can hardly these numbers hold up throughout the entire time headed you could actually see here where adware is about two-thirds the logs done proxy this is an automatic loss right so give you an idea the reason I'm showing you this is you can idea that this is a real thing right here at your ransomware and stuff is that are up here or undo and not being Punk'd that's the little represents a small fraction of what we have an adversary so
you know you're not getting your data encrypted the other have a month hospital but you're normally or I'm Emily shooting out all of your confidential in or a lot of copy probably don't want to go see or confuse that you don't know about or we had agreed to attention and here so we've got a couple of Keith's studies sort of some things that we've worked on in the cyber Cisco has anybody heard of a lot PB inserts
okay so research just a while ago we didn't know so much when we saw our network talking about all the detail about how all of us and essentially how it works is you install software right and you are acting to disputed here network right where you're allowed to you know basically resell your your internet damage so I saw hola I can now browse other the other countries it doesn't have any in service right but my network traffic is idle or even when it's not you can reserve a slice of that sell it off to other companies doing whatever they want here most likely or whatever else they want to do right so now what happens is
you actually had your computer running at the end clients part of the special network other people around the world are using your computer of the convent almost stopped or exit no no way to get those services okay so now you're ready every year to know that that stuff what makes it worse though oh yeah I'm sorry one of the bad things about that also smoothie Ola software is that that's one software vulnerabilities you kind of see the advisor another things actually pretty bold but a long story short on this field about stuff include a number three two courses is horrible so you can stop good client if you're getting a good deal you're vulnerable all this stuff and people are shoving
their own traffic through your box and before you can your ideas here's so here's what it looks like when you kind of install it or we go to the website right djay en network okay there's the apartment right loominatee was have time to do for this talk earlier 170 count citizen traffic get screwed up yet they go to admission area it's still it's instilling it they really tried sure is fascinating what you can see basically oh let me p.m. used it is the VPN network for you right we would not easily company that basically mines that data and allows you to purchase a subscription to that data to do peckerwood right so look at this
here largest proxy never in the world that's all of you be in let's see here we're somewhere of the brightest harmlessly local data right so you can have a local organic data from where if you want where you want to be right and then now here we have to say that more hearts and we're harvesting is on there couple times here we go hard head superscalar right so this you paid to get into this is little o into today you can visit the start cap and traffic you can start getting data and start seeing user agency their IDs and some browsing to all that stuff you saw those privacy policies are now available to right
through they'll love you get numbered that when you install it you doing that right so is it malware you agreed to do it right you didn't read the thing it's a spy work most step here's another case study relevant knowledge hopefully no one knows about this either because to do that and so it's another online market research community it is actually a huge research network research and what they do is they basically together online information just like all the others photograph where stuff that's right this was actually kind of interesting we we saw this internally you we're going to do the SEC trick right away kind of see do we have installed our network absolutely
we did in fact I think this would ended up with being about pretty fair you will have this installed and laptop I'm not sure what the initial carrot was to get them to install it anyway this was actually turtle and again give you an idea about what's happening here DISA the the relevant knowledge file really changes its hash it's not the 85 X right so you down the file - check it again a few minutes later about hearing a hash consider hashes change later she was changing again it could be something councilors program could be nefarious activity to avoid detection right or blocking right what is that it's a little weird mom any folks submitted with Mac feed on their
that it comes to have a functionality called Artemis which is their heuristics engine looks for unusual activity is not a signature base they just tell us for weird stuff happening right we saw that that actually fired but we also saw that it's coming back right so you see example here here's a search but I think weird way this is to get an idea of what comes back with all that knowledge right it's the knowledgeable Mariners are eighty Center and then you press here here's all the results the front back and they're all presented with artists which means that there is no signature built-ins and actually to detect this because it's not an hour right so why
would you have a signature it's not malware however their piracies engine is lighting it up I'm crazy something weird is happening when I open smiles and we want to warn you about it we dig a little bit deeper you can actually see them as in your case of part of this file as a result of what the heuristics engine detected actually five as encouraging so on the face of things relevant knowledge is a mobile to navigate is it is a legitimate application you can install on the backend seriously the computer greatest thing keep pace with that yeah that's a group right so if again it's kind of illustrates the Dare seventeen what 80 companies are allowed to do and what
reality dates right here's another example Bruce is super cool depen shows where you see the relevant knowledge service writing here it's in fact it's Cuba and runs up this timeline it's trying to slide up this this file to actually is being blocked right well then the service we can you starting so the antivirus and all moved out there supplication to a Bartlett leaving the service there simply but we didn't help the patient you can still see how people fire these these new versions each time you try it can definitely pull it off do you know so longer this is the last piece there yeah this is a smile my favorite cases but I've had a long time to do it it's a
response in Cisco over 10 years or more now this is still my all-time favorite pieces this actually happened it's a couple of years ago I wish I could take credit for her spine hook I call it took it and he did a fantastic job but I want to show whatever you got sadena some Walker here's the website remember the bypass new IP restrictions watch movies online I mentioned earlier this is to go to this right this tool allows you to access to your web sites like Netflix or hey listen whatever else ready what you want to watch these shows and start learning this honker here you go you can watch non-american you can watch these
shows they are really interesting what it actually does is it's protein atomic this rapport with the nsobject here right it points all of your traffic to their DNS servers of course that's controlled internet right so what we'll see here that the peaks are always is very common right just everybody this is the top this is the top faster than Cisco ever a little bit got that right it's insane billions per week what does it idec's that it gives you youtube response it and when their response back right so we got some calls from people on town pair goes with all the Civic complaints right Holly this is a t-shirt so sleeping that I what's up basically
you know it's not like a pure was this year it's not my PC you couldn't say if she's we're accessing did open my I come in Adela PC it was interesting right that led us in a cable it's happening on iPhone please going on here right Mac we see other you know software platforms tweeting group that says something about probably being up who does networking stuff must be causing problem I have trade school on every operation service so this is a cash they're basically consider each more the removal and sites of our South American Center not smaller you have cash on one's there when someone fetches the file the cash engine unfortunately catches whatever the
client tells it to or it did right I hear the greedy's everybody knows what that means so therefore everybody that uses the oxygen is going to get the same data back that the person who actually has a lot a lot installed I'm sorry he has a locker installed my erotic moment was show that even if you can difference well that's why we're right it was a devote quite a lot up there this is help but what he did was like hi of course this morning you guys together here's exactly what happens right here we're going to do this for this researcher go through google right you get the act like you search through the PS I'm
awkward you get there I keep right which is this weird again here we go into my respond go [ __ ] didn't actually do it says that it was this and said that we did it by peeking back so first one there's that I'll leave you with this there are some solutions to this I don't want to go into detail better pretty routine okay looking through your log data looking for a per cuffs right looking forward URLs that you know written colonel going outside your poxy that link you something equals happening and throwing the bunch of domains into a list HR pc and blocking instant means you see gets on that that you have a
massive ever problem or gets discouraged come on sisters network this is what you see we try to go to google one of these types of things see right here now only got Cena yeah we aren't easy bet no because it's just anyway I've got a couple more things but I think it might have time we can call it a day one thing my division at the end was I mentioned the choke RC thing the other way to combat I think ahead where Martin is actually through cool off we can see here is the FTC judgment settlement against uh was in Mobile they actually found them guilty of wedding truck children's tracking and creation about the Commission may end up
finding each other performance I'm so they already wasted all that money because they were a legitimate company wanted a thing about a minute then yet this I think will be hopefully put pass close thanks [Applause] [Music]