Bypassing 2FA with Android RATs
Show original YouTube description
Show transcript [en]
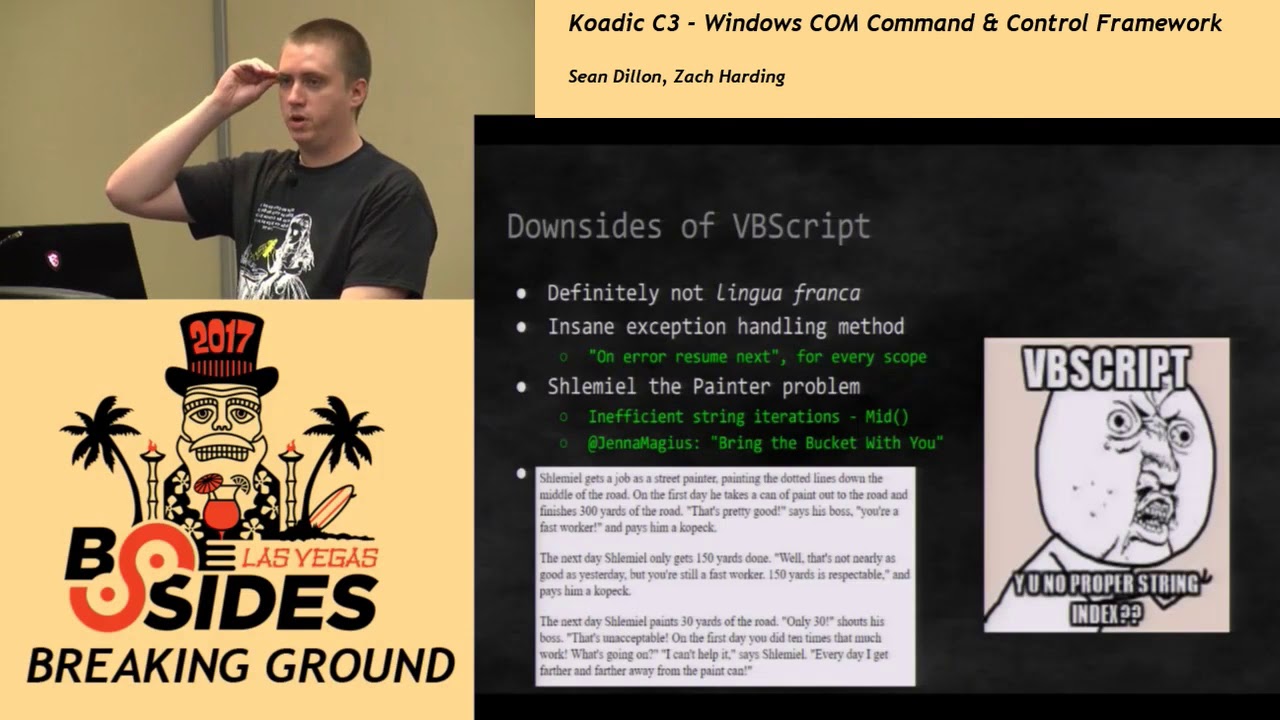
it's pretty cool that kind of led into this discussion a little bit about myself I'm a security threat analyst mainly handling customer submitted Maur samples right now for fish labs as the June 6 been there for about three years and one of my passions is about malware hunting is also taking a look at PHP and finding vulnerabilities within those malware C 2 panels so I'll talk a little bit about that too in my talk being a drummer I'm a huge Red Hot Chili Peppers fan so I really like Chad Smith I definitely want to be like him so today we will talk about why miscreants are utilizing mobile remote access Trojans for account takeover we'll talk about
three different families how are these being spread in the wild has some examples of some previous campaigns will talk about the command and control infrastructure mitigations of that you know if your organization who's thinking about switching a two-factor or if you already have talked about you know some of the means of combating some of these attacks on the mobile side and my personal passion eyes are already you know talked about is the vulnerabilities of these malware families so we'll get into that as well first a little disclaimer since some of the there are some live links maybe in my presentation so you definitely don't want to visit those on your mobile device we also be
talking about exploitation of proof of concepts of live malware so do not try that at home unless you like to be visited with men in suits so as financial institutions implement to factor these miscreants are utilizing this for account takeover no longer is the possibility of solely getting the username and password for account takeover necessary for a full account compromised so anyone in here have a Google account yeah several folks right has everyone implemented two-factor on that yeah how about LastPass recent breach with them right so they came back and said yeah definitely want to implement two-factor with that but that's not the end-all to be all right one of the main issues that we see some
of these financial institutions their user base is already used to going out to third-party stores to look for the unofficial application for that side so you have Joe Schmo that realizes with customer of XYZ bank there's not an official application so this user base is already used to finding these unofficial applications and third-party repositories or even the official ones and it's a very low entry point for miscreants to get into this type of malware some of the families I'll talk about they're freely available we're not freely but they're relatively inexpensive and low entry point compared to your PC man-in-the-browser malware there's also a lack of mobile antivirus adoption I'll show you some slides here of recent samples out of hit virustotal
and we'll take a look at the the signature count of how many a V's actually are popping for these types of families because first keeper doubt put out a very interesting report last quarter of 2014 they said one in five Android users have encountered some type of mobile threat in that last year so you're starting to see that ecosystem evolve and definitely see more as a you know especially developing nations they might not have the financial backing to purchase a full-blown PC where are they turning to mobile devices to access that internet take you through the steps of a traditional fish account takeover so our evil miscreant here on the Left sends out a spam campaign that contains a link
to a fish our victim clinks on clicks on that link looks just like the the banking website that he's used to logging into plugs in his username and password right sent back to the miscreant one other attack now we're talking about mobile attacks themselves is you may have run across them on the Internet you can create an account on a website and you know plug in a URL and it creates a Android application that's automatically shipped off to the stores so in some of the attacks that we've seen one issue of concern is utilizing these store wrappers as we call them to wrap the actual phishing site so there's been a couple examples that I've ran
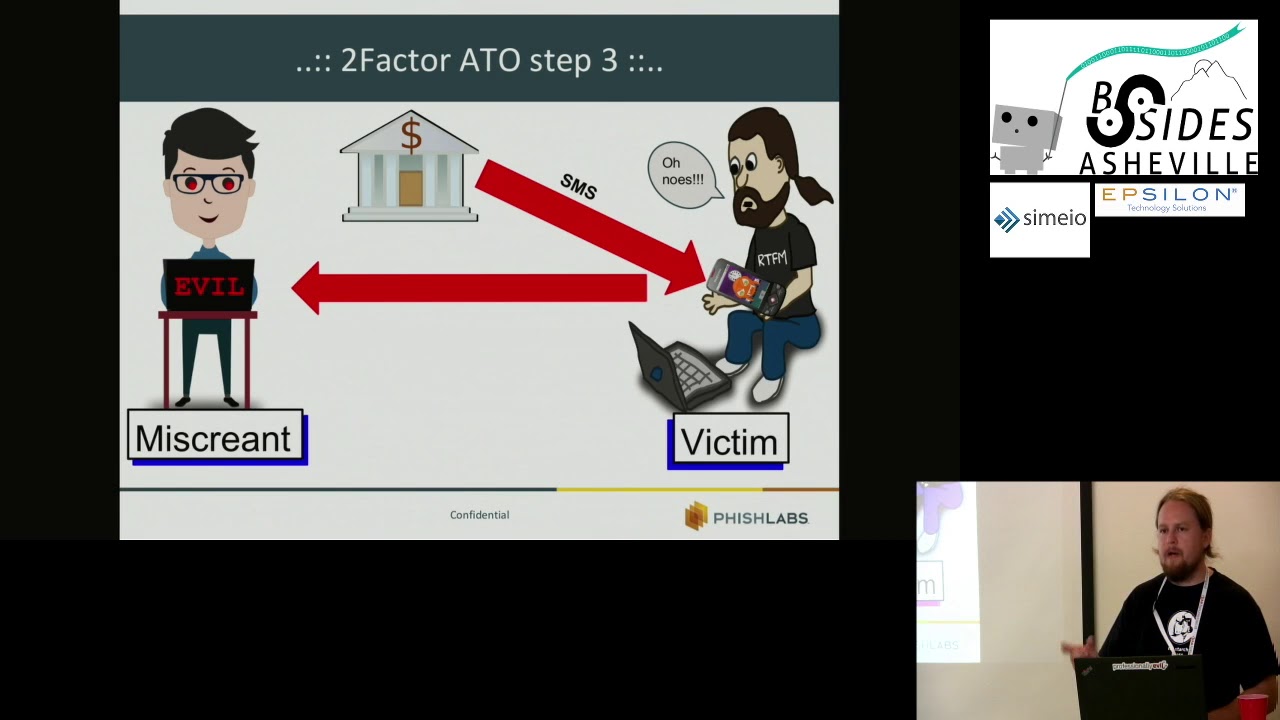
across where miscreant was using a compromised websites a host of phishing form just a username and password login form he wrapped that an Android application and it was pushed to Google Play as XYZ Bank users you know looking for that application on the official Play Store then downloaded that and divulged their credentials but as that Bank implements two-factor let's let's take a walk through this begins with the normal spam campaign or PC malware as I'll show you with one of the families since - the victim captures that username and password and it's also sent back to the MS grant but now that phishing site also gives some verbage about well you need to download our new
mobile application to make you more secure right in order to capture that SMS most of these by the way are solely to capture that SMS one-time pin right now is that SMS is sent to the the victim since that a miscreant has a remote access Trojan on the mobile device he now has a copy of that pen so that's essentially all the pieces of the pod for bypassing two-factor any questions on that campaign style
this was a yeah I didn't draw him by hand I'm not that sound um forget which website is like free graph it open graphics released under common license or something like that yeah absolutely yeah yeah everything's up somewhere read the [ __ ] man
right yeah absolutely so the question was what is the time frame from or the duration of the time out for that SMS pin correct so yeah that's definitely one of the mitigation factors and I haven't studied actually you know with most systems I think Google often indicator even it's 24 hours if I'm not mistaken I may be wrong in that but generally there's some leeway with the the duration and as one of the mitigation factors we'll talk about you know decreasing that value as well so how are these remote access Trojans being presented to the users as official applications one other method that they're utilizing is an method known as binding so taking a look at the
PC malware in comparison you may know of it as packing and executable whereas with on the Android side we call it binding a lot of the toolkits um so this is actually a screen of one of the remote access trojan c2s and handles ap Caid generation for the actual malware and also you're able to upload or bind this application with an official-looking application that the user would be then tricked into installing on their system another screenshot of another binder here all right let's talk about the two different communication and control types just with PC remote access Trojans I'd like to break those in pretty much the same categories you have your Java C 2 which
runs on PC and one of the families that we'll talk about there is the Andrew rat also known as Sandro rat and Droid Jack which is now able to be downloaded from their website the other C to type the one that I like to find vulnerabilities in is the the PHP panel variety so these are hosted on you know compromised VPS azure websites that the miscreants have you know unzipped that the PHP website to in order to have seats you from these compromised mobile devices to families we'll talk about here is I banking and dendron taking a look at the the Java C 2 again the evil miss green actually hosts the server on the their PC they
have to port forward you know that from the internet so I have it routable back to the PC usually you see these set up with some sort of dynamic dns account like no IP or you know dine dns one of those free services for dynamic DNS hosting so it begs the question to running this type of situ on the computer does that open it up to the miscreant - you know application vulnerabilities there's a really good talk recently I think at b-sides London a researcher was talking about some of the exploits in should I forget one of the PC it'll come to mind I'm sure after I finished talking about it but anyways one of the remote access Trojans for pcs
he was able to find a file download vulnerability so any requests that he sent to the server he was able to download any file from that computer it's pretty neat and I can't remember the name of the town but alright I digress so also there's these you know websites or hack forms semi underground where these families have been leaked out a lot of the a lot of the malware the rats that you see on there are backdoor by the people that are releasing them for free right get nothing for free right so one of the huge issues with this since we're hosting it on the PC side is that is extremely flood susceptible whoops now
let's talk about the PHP C 2 panels as they're referred to in the underground vernacular one of the huge issues with this is lack of input validation so you have everything from you know sequel injection shell upload remote local file inclusion it's also you know being hosted on usually scarce resources on a compromised site or VPS definitely susceptible to layer 7 flooding or HTTP flooding one of the first families we'll talk about is and row rat this is a example of the Java C 2 was talking about earlier first discovered it in the wild August 2014 targeted Polish financial institutions and this is actually the the lure email lure on the right masqueraded as a an
official notice from Kaspersky saying hey you need to download our latest Android security application so as you can see it's kind of fuzz doubt but it's you know dot a PK there and in we'll see there's also talking to German financial institutions and that was masquerade as a Google service framework update the actual attribution of this from a gentleman in China I'm sorry not China but India and he is now using it's now called a droid jacket some of the capabilities of this remote access trojan complete file manager as SMS interception of course two factor bypass I am spine contacts grabbing GPS tracking records calls and audio right remote bug if you if you will
same thing with the video remote spy cam here's what I was talking about available now Jack net for the lifetime price of two hundred and ten dollars you can own this Trojan yeah yeah another screenshot here at seal on the left of the actual Java C two that's running on the PC so handles everything from not only the the bots check-in apk generation binding so forth still very prevalent appellees stats on Thursday so source being a virus total intelligence for this I'm still very widely seen in the wild so in the lab I set up fun thing about what I do is being able to play with these families and you know wanted to mimic how long would it take
for a simple syn flood to knock one of these offline and really didn't take that much at all so again being you know a java-based application and you know poor coding Sanders these guys aren't necessarily going through quality assurance compared to actual product that's being released you know officially or legitimately in in the ecosystem so any questions on George a good to go next family I'll talk about is I banking so this targeted financial institutions in 2013 and is still very active today mainly in Europe and Asia where most financial institutions have implemented sue factor a not so much of a big deal right now in the u.s. because unfortunately we haven't really jumped on that bandwagon
famously used by the never quests also known as vault rack crew is anyone familiar with that malware family by chance not something folks okay cool I'll talk about that here in a little bit when this was initially sold you could tell that the the in buyer that was you know purchasing this crimeware kit was solely set up with crime wear intentions you know these other families have really nice slick gooeys and it's mainly to attract that that newb customer right but with this family solely being sold for crime wear so you'll see the UI is not that slick but they have features like well after campaigns over I want I want to delete all traces of this trojan
on the device so you'll start to see some of them more anti forensic capabilities than this type of family source code was leaked in 2014 and of course you know especially with crime wear as an example of the the Zeus malware as soon as you release a elite copy like that it spawns several variants for that so starting to see that now of course so going back to vault Rack vault Rack is a man in the browser PC malware family what that means is as a computer is infected as that victim visits a website there are specific JavaScript injects injections that are injected into that stream to not only grab the username and password but they might also grab or a prompt for
all your user information credit card numbers list goes on so taking a look at one of the vault rack configurations that will just pushed out about a month or two ago we saw a bunch of P&G base64 encoded strings within this vault rack config so I pulled that down scraped the you know the the image base64 decoded that out and dumped into desk and I started looking at these images here Facebook OTP or one-time password it's like okay interesting some other pictures here that were decoded so what we're seeing here is the actual picture decoded injection for the instructions of how to install this Facebook application from an infected vault rack victim computer does that
make sense video all right so give you a little background on this you know I went back after taking a look and seeing these images that were decoded there were some couple of obvious skated lines of JavaScript in there decoded those and sure enough there was a hot link to the actual apk download grab that anyone in here has done a PKD compilation it's Jason in here a little bit so especially with an apk you can actually reverse it to somewhat readable Java or Smalley code so you run a decompiler on that and just grep doubt any urls and sure enough I plugged in that URL you know of course preserving an offset on the browser but took a look and it was
the i banking login so I banking family still you know that was two months ago from Avadh track config that's still being used in the wild some of the features of this family capture SMS and call list send SMS premium rate scans if you will right not so much big in the United States but overseas there's the method of doing transactions and sending money via SMS actually call phone numbers premium rate scans incoming call redirects so if I if I've compromised a device and I know that the bank is going to call that individual to verify a transfer that I I made a fraudulently why don't I just redirect that call to me yeah that was my that was my freaking
transfer right again record calls in microphone and you know one of the biggest things I kind of touched on earlier wipe all device data after I'm done with that particular victim still very prevalent still fresh samples hit and beat see so I talked about the the source code leaked in late 2014 a security research researcher by the handle of xylitol pull this down and found a unrestricted file upload vulnerability of course it's being patched now on the wall but just a goes to show you the lack of input validation on these types of you know c2s is definitely prevalent what's up i was otto it's all yeah yeah very very good malware researcher and this is actually
picture down on the bottom this is the login interface for i banking again compared to the other families you know not too much splashy gooeys to attract the noobs here kind of broken english and your browser must be included cookies
i'll show you the proof of concept again this this has been patched so within send file dot PHP what this file was originally intended to to to perform was any type of recorded audio on the capture device was submitted to this and that would be dropped into the sound directory on the server so there was no type of you know file mime type checks there is no type of extension check so what you can do is essentially upload PHP in this example uploading a PHP backdoor shell and then having you know full capabilities as the privileged account of whatever's running in apache on that web server last thing we will talk about is den droid March 2014 cert
India issued quite a few warnings about this particular family was originally marketed for $300 and the bike the binder author actually seen some form traffic between this particular author and Andrew rat or droid jack right so they were going back and forth and discussing different methods of how best to implement a binder and so there's quite a few similarities between the binder of this family and Droid Jack some of the features is probably the most feature-rich family for mobile rats right now access those call logs call phone numbers again premium right scans open web pages to probably think of some type of you know social engineering type of experiment that you can do with that
record calls and microphone intercept text messages of course exfil and upload files we store everything on our advice now HTTP flooding that was kind of a unique feature I haven't seen actually a DDoS client for mobile implemented yet in one of these rats and one of the other unique features is that it actually has a hard-coded forensic capabilities for some of the some of the messaging apps like whatsapp and one I can still you know passwords and stuff for some of those well-known applications and of course any type of like save form file in the browser and whatnot still very prevalent it's probably the most prevalent out of all the families that I see there's a
screenshot of the actual situ you know getting compared to I'd banking a lot of time went into the the JavaScript and the Ajax but luckily what I'll show you is not too much QA went into the PHP server side code so I'll talk about a vulnerability there again you know Google Maps tracking your your victims on a Google map display several features within this particular family so this panel source code was actually not only the panel but the entire family itself from the apk generation and the panel was leaked August of 2014 on github immediately pulled down the code and discovered a PHP remote code execution vulnerability so essentially how this works is the apply settings
that PHP file this was supposed to only be accessed through the logged in admin right but what you can do since there is no check for that this file writes anything to config dot PHP so now we're able to write you know any text to a PHP file thus we have remote code execution so in this example I'm just pushing the take the the get parameter of C and I passing that to the system function for remote command execution once that config dot PHP file is rewritten it completely zeros out everything so not only is this you know remote code execution but essentially it's denial of service effectively ends this PHP panels existence because as
that config file is rewritten it doesn't know how to talk to the database and it doesn't know how to authenticate users and it just completely wipes out the panel so it is quite noisy now we can run system commands so pass in you know earlier wrote the the get parameter of C passing that into the system function and then being able from there any parameter that specify or argument rather for get parameter C it will be displayed and render back into the browser for remote command execution any questions on the family so far nope so let's talk about some of the FUD when it comes to mobile malware the thing is is that these families take a high level of
social engineering for them to be implemented and for a successful campaign right when you think about it a user has to not only download outside of the App Store which is a flag on Android although outside of the United States they're already used to that right especially overseas in Asia they don't actually ship with Google on the phones so you already have third-party app stores enabled by default so that's one of those XI second issues whenever that user is presented with you know there's no hiding of all the permissions that these things that these things request every permission available to it within the developer API so you know you'll take a look at that once you install it
I mean it's everything under the Sun that it requests permission to and of course what a users do sure ok it happens right now with all these families there's really no operating system-level exploits one thing that we will see I think is as mobile market saturation occurs you know as I discussed earlier you know some of the developing nations that are just now discovering the internet they're not buying pcs they're buying mobile devices so I think these types of rats will definitely be more prevalent in the future and also the again the PC mana the browser crimeware it's not expensive right for a successful campaign but with these not only can you find freely available or
elite copies the entry point themselves are you know less than three hundred dollars just to get started touch a little bit on mitigation we already mentioned in a little bit earlier and so as your company is considering implementing two-factor or if they already have realizing that you know okay what we moved away from maybe PC malware from the aspect of the only thing that's needed is username and password so we defeated fishing but we still see phishing attacks is the main issue people still fish you even if you have you know triple factor authentication I think the other realization is that as you move into two-factor you now have a new attack source so you need to plan to mitigate
those you know Android applications as well so one thing you can also do is mandatory and BOTS and D mark for Brandon attacks to factor of pin timeouts we kind of mentioned that earlier and finally it's it's up to us to do communicate with our user base the dangers of allowing third-party installs and of course reporting you suspicious activity to our security operation centers that's pretty much it for my talk guys I appreciate it feel free to reach out to me um this is my work email here and I'm also on Twitter's any questions yeah - sorry so if one rat exists on a mobile device already have you actually had an experience where you've either tried in the lab or you've
seen another rat try to be installed on the same device I have not they're conflicts I've heard of now we're taking over malware things like that my guess is with since we were talking about more of a sandbox environment on a mobile device I don't think they would impact at least I haven't seen it in the code you know how some malware might actually check to see if there's other malware present and either kill that or you know go away it isn't really the case with movement our right yeah I haven't really seen that with that these particular families good question I thank you any others
good to go well I think you've heard Sam I'll be up here all all day so feel free to stop by hang out thank you