Account Takeover via Exploiting Misconfigured Password Reset Feature by Tuhin Bose at BSides Toronto
Show transcript [en]
misconfigured password research feature. So he is a cybersecurity researcher, bounty hunter, and a penetration cluster. Hi, Tulhin. Hello, Sudebi. Also, he'll be there after the talk. He'll be in Discord to take any of the answers. No one's monitoring the Twitch chat, so don't write anything there. He'll just be there in the Discord to help anyone with any questions. OK, Tulhin, you can take over. Best of luck. So much.
So let me know my, if my screen is visual wall.
Okay. So hello everyone. First of all, thank you so much for attending this session. I hope you and your family are fine and good in this COVID-19 pandemic situation. So my name is Thuhin Bos and today I'm gonna talk about account takeover via exploiting misconfigured password distribution. So let's start. So before starting, let me briefly introduce myself. My name is Thuhin Bos. People usually know me as Thuhin1729. I am a bug bounty hunter having 4 plus yourself experience in this field. I am currently working as a CISO at DSPH. Besides that, I am also an InfoSec Trainer. I am also a crowdsource security insercer at Detectify. And I am also a speaker and I used to share my findings and some
bug bounty tips and test cases over media and Twitter. So I am a blogger also. So let's start. So this is our Twitter's agenda. First we will learn about what is a password is a feature. I know that you all know about what is the password is a feature or what is the forward password feature, but still we will have a brief intro. So then we will learn about common password implementation techniques that are used by developers. And after that, we will be moving forward to our main topic, which is account takeover via hacking and responsible password is a feature. This is our main topic. Then we will wrap up the session with our beautiful constitution and Q&A. So as you
can see here, we have a very beautiful agenda today. So let's see how it goes. So what is a password to such feature? So for example, you have a, let's say you have an account on Facebook, Instagram, Twitter, Snapchat, TikTok, right? You all have lots of accounts in different websites or web applications, right? So for example, let's talk about Instagram. Let's take an example of Instagram. When you open Instagram, what will happen? If you open Instagram.com, it will ask you for your registered phone number or email address which you entered during the signup process or it will ask you for your username and it will ask you for the password. Right. And as soon as you click on the login button, the Instagram will verify whether
the given credential which you entered is matching with their database or not. So if it is true, then it will give access to your account. Otherwise, it will show you an error like incorrect username and password. So, for example, similarly in Facebook also it will ask you for your email address or password. Then as soon as you click on your login button, it will check whether the given credentials are correct or not. And if it is correct, it will give access to your account. So you all have different accounts in different websites. It's the basic cybersecurity principle that you should not use the same passwords in all your accounts. So obviously you wanna use different passwords in different accounts, right? So it may often
possible that you will forget your password. For example, today you want to log into your Instagram account or let's say today you want to log into your Twitter account and when you enter your username and password, your Twitter username and password, It is showing that let's say incorrect username and password. So in that case, what happened? You forget your password. So if by any chance you forget your password, you don't have any other way to access the account, right? You will completely lost the access to that account. And you cannot access the account until you remember your password. So this is a big issue, right? So to overcome this issue, developer introduced a new way
or a, let's say a new feature called forward password feature or a password reset feature, which will basically allow you. So in case if you forget your password, this forward password feature will allow you to reset your password, basically to change your current password and replace your current password with a new password. Okay. So obviously they will not gonna, uh, allow anyone to change anyone's account. For example, you cannot change my account's password, right? Using this forward password feature. So to change your password, first you have to, first the website or first the application will verify whether you are the actual owner of that account, right? So for example, in my country, if I have to prove that I am actually even worse, then what I have
to do? I can use my passport, I can use my visa, right? So similarly, there are multiple ways that the developers will use to verify that you are the actual owner of that account. So there are multiple ways to verify that you are the actual owner of that account. So first developer will verify that you are the actual owner of that account and if the verification process goes correctly, then what will happen? you will get access to that account. Sorry, you can able to reset the password of that account. The application will allow you to reset the password of that account, right? So this is basically called a forward password feature. Basically, it is nothing
but it is the action of invalidating the current password for an account on an application and then setting a new password. As I said earlier in the discussion. So you may often see that most of the services, 99.99% services have the password is a feature which forward password service, which will basically allow you to reset your password. Right. So I know, I know that you all know this, what is the forward password feature, but still we just talked a brief intro. So let's move on. So now we will see some common password is implementation techniques that are used by the developers. So see the motto of password is a feature is same, right? What is the motto of password is a feature? The motto of password research feature, the
main motive of password research feature is to reset your password and change your current password with a new one. But as I said earlier, the verification process, first the developer have to verify that you are the actual owner of that account. So this verification process may be referred from developers to developers. So let's talk about some common, in this section, we will talk about some common password research implementation techniques that are used by developers. So sometimes what happened, for example, let's talk about facebook.com. So when you open facebook.com and click on the forward password section, what will happen? It will ask you for your registered phone number. It will ask me, it asks me for my registered phone number, which I entered during the signup process.
And as soon as I enter my registered phone number, it will send me a six digit code or a six digit OTP in my phone number. As you can see in the screenshot, in this case, my OTP is 107.330, right? It's a six digit OTP they sent. And I have to enter that particular OTP in the facebook.com page, right? As soon as I entered my phone number, then it will ask me to enter the six digit code that they sent to me. Okay. And if I entered the code correctly, then they will allow me to reset my account's password. So this is a way that the developer will... or the server will send you a
code to your registered email address or phone number and if you enter the code correctly then they will allow you to register your password. This is a popular way. Another way is they will, for example, in Instagram whatever, if you open Instagram.com and click on forward password section, it will allow, it will ask you to enter your registered email address. The email address which you entered during the signup process, right? And if you enter the email address, they will send you an email to the registered email address. For example, see here. As soon as I entered the email address, my account's email address, they sent me an email with a password reset link. What is the password reset link? It is nothing but a link which contains an unique
token and some unique parameters. The value of parameters are totally unique for my particular account. will just generate a unique token for my account and they will send the link to myself okay and when i since i am the actual owner of that account so obviously i have the access to my email email account right so i will simply open my open that particular email and i will click on the link see here in the reset policy set your password button there is a link and as soon as i click on the link what will happen uh it will allow me to reset my account's password it will ask me for the new password which I want to set. And as soon as I enter a
new password and hit the enter button, it will allow me to reset my password. So this is the most popular thing, sending a reset password link. And this also used by some developers, like sending an OTB. So these two are the most popular way that developers use to implement a password reset feature in their application. There are also some other ways like sending a security, just by using a security question, or something like that. There are also lots other way, but these two methods are the common ones. Okay. So let's move. Now we will discuss the main thing that is account takeover via hacking a misconfigured password user feature. So when developers implement a password user feature, there may be some kind of error,
right? Since developers are also human, so they may also do some kind of error, right? So in this section, we will discuss that how this error can be exploited by a malicious attacker. How this error can be exploited by a malicious attacker to hack anyone's account in that particular application. Basically to achieve account takeover vulnerability. So let's see what are the ways. There are multiple ways. We will talk about some most common ways. So our first one is host header injection vulnerability. So basically in this section we will discuss host data injection, basically password reset poisoning we will discuss. So see, I hope you all know about host data injection. Okay. So, uh, for example, uh, my website, let's say I am
testing on target.com and my website is, uh, behind the proxy server. In that case, I can try this password reset poisoning vulnerability. What I can do, I have two test cases. Okay. So I have only two test cases. First one is changing the host header from target.com to evill.com or any other website. Okay. Let's say attacker.com or xyz.biotcollaborator.net or any kind of thing. Okay. First one is changing the host header to another domain. This thing I can do and click on the send button and that is what I can do. I can add another header called let's say xforwardedhost.evill.com or xforwardedfor also I can use. There are lots of headers. Okay.
that I can use. So see here in this screenshot, what I did, I just hide the targets. Now, obviously I'm not going to expose the target name because of security reasons. So what I did here, I just captured the forward password request and in the body, as you can see that email ID, it is a victim's email ID. So throughout the entire talk, we will assume that rumpab75.gmail.com is the victim's email ID and rumpab75.gmail.com is the attacker's email ID. We will assume that. So here the forward password request looks like this. Request is sent to slash API slash users slash forward password. And this is a post request. And in the body, this is the email ID. And this is the recapture response. They have set up
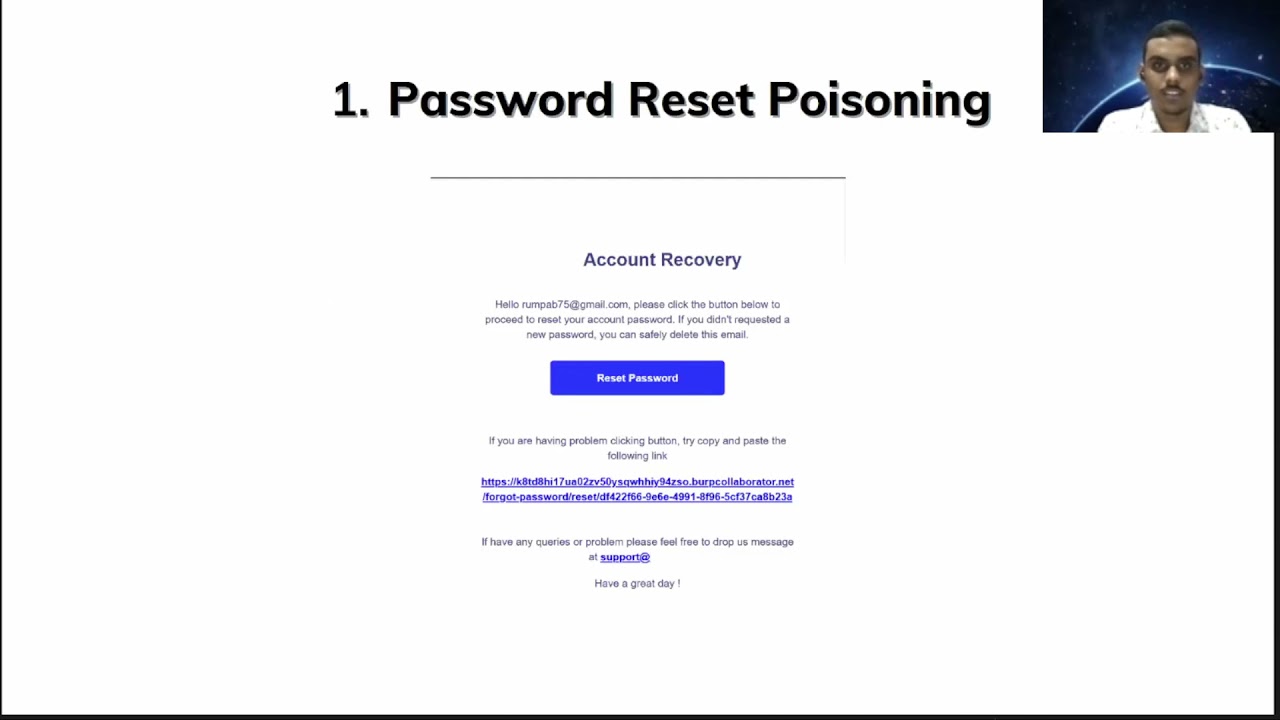
a recapture in the forward password page to prevent rate limit. So what I did, I just captured the request, send it to repeater, and add that particular header, xforwardedhost, xyz.barplowator.net, okay? And hit the send button. So now if I check my email, And it also send me a response 200. And now if I check my email, I will see a password itself link, right? The application will obviously send me a password to my email address, right? To this particular email address, rumbab75.gmail.com. So when I opened my email inbox and check the email, which was from support address target.com, I was shocked. The password is here in this screenshot. The password is a link which I received is Instead of target.com, the
host header is getting replaced via xyz.verbcollaborator.net which I entered in the x forwarded host header. So that means what? This particular website is vulnerable to host header injection. Basically, more precisely, it is vulnerable to password reset poisoning. I can able to manipulate the host value of that particular password reset email link. So what happens when I, for example, here, Roomba B75 at gmail.com is a victim. Okay. So if I perform this malicious request, send a malicious request, this, uh, the Roomba B75 at gmail.com will receive this kind of email. And if, uh, if for example, I am the victim. Okay. I got this particular email and I will see that, okay, this is coming from support at the target.com. So this must be legit. So when I
open this particular email, I will see that, uh, This is the link. They are asking me to reset my password. What I will do as a normal user, I will just click on this link. And as soon as I click on this link, the password reset token will be sent to that attacker, right? The password reset token will be sent to the attacker because when I clicked on this link, the get request will be sent to the attacker control domain. In this case, if I look my BIRP collaborator server, then I will be able to get the victim's password reset token, this unique token. DF422 blah blah blah. I will be able to get that unique token in my collaborator server. And after that, I can
able to reset the victim's password by just simply changing the host header value from xyz.burpcollaborator.net to target.com. I will be able to change the victim's password. If I just simply change the host header value from this to target.com and open that link, it will allow me to change the victim's password And after changing the password, what I can do, I can simply go to the login page of target.com and I will enter the victim's username or email address and I will enter the new password and I will be able to take over victim's account, right? I will be able to take over entire victim's account. I can do anything, right? So this is the first way that you can use, you can test for whether website or
whether web applications password is a feature is vulnerable to password is it positive or not. This is the first, very first method to test. So I hope you understand it. So let's move forward. So the second one is modifying the request URI. Okay. What happens? So first let's discuss what is actually a request URI. If you observe the first line of a request in this screenshot, if you observe the first line of a request, which is basically in this case, post slash this API user forward password. So the first one is post, which is basically the HTTP method that I am using. It may be get, post, put, delete, whatever. And then this is called request.uri, okay? This slash API slash
user slash forward, hyphen, password. And after that, this is the protocol that I am using. I am using HTTP version 1.1, okay? So sometimes what happens, if the target is having some kind of protection or some kind of feature, or if the target is behind somewhere, then what happens? It will not allow you to change the host header. or sometimes adding a X forwarded host header also will not work. In this case, what you can do, you can try to change the request URI. For example, you can, let's assume that the forward has been password is the actual request URI. So let's, you can try adding HTTPS colon double slash attacker.com before the URI, or you can try at the right attacker.com append at the right
attacker.com slash forward password or you can use a colon or you can also append the add direct attacker.com after the forward password, after the endpoint. So let me show you what happened when I entered, I used this. So see here, what I did here, I just, the actual request, the actual endpoint is slash API slash accounts, slash users, slash password, and recovery. What I did, I just send the actual request to the quicker and just added add direct Google.com before that. So when I sent it, it was showing me a 200 okay response. Okay. But when I opened my email, so what happened, let me show you. This is the actual screenshot of that particular email. So the target, instead of getting
services.target.com slash blah, blah, blah, I got the domain services.target.com, add that at google.com, right? As you can see in the screenshot. So if you know this add direct trick, or you can also do an experiment. Simply go to your browser and type google.com at direct bing.com. So it will open bing.com and it will take google.com as a username. So in this case, similarly, if the attacker, if the victim, when the victim receives that particular link, if the victim clicks on this thing, clicks on this particular link, what will happen? It will send a link. It will take services.target.com as an username and it will finally redirect the victim to google.com So basically instead of google.com, if I just enter xqz.verb.net or my
accounts or my website's URL, right? If I just enter attacker.com, so I will get here attacker.com, right? Then the victim will get here attacker.com, then what will happen? victim will, when as soon as victim clicks on this link, it will redirect victim to attacker.com slash API slash account slash user slash password recovery question mark, token equals to that unique token. And when victim will be redirected to that particular link, I will be able to get victim password as a token in the log, in my log files, right? Or if I'm using my collaborator server, then I can apply to see directly, right? So I will be able to get victims, the password is a token, right? Then I will simply change the host, change the domain name
from attacker.com to services.target.com and I will be able to research with these passwords. So modifying the request URI is another way to check whether a password is a feature is vulnerable or not. If you send this kind of request, you may try any of these four. And if you just append any of these four in the request URI and you get this kind of thing, This kind of link in the, this kind of password is a link in your email address. And if you've got this kind of link, then it's vulnerable and it may give you some four days boundary also, right? You can report it easily. So this is the second way that you can test modifying the request URI. So I hope this is clear. If you
have any doubts, you can obviously think me on Discord. So let's move on. So the third one is token leakage. So sometimes what happens, the developers often leak the password insert link, the password insert link or password insert token or the OTP, which they sent over the email or phone number, right? They may say leak the password insert thing, password, sensitive information over the response or over some JS files. So in that case, what I mean, see in this screenshot. So when I just entered my phone number, phone number in the password insert page, The end point is basically just as Ajax, that's reset password.php. So when I entered my phone number and hit the send button, it leaked me the OTP, the four digit OTP, which they
sent to my phone number. As you can see in the screenshot, in my case, the OTP is 9220. So they just leaked the OTP. So what I can do, I can just simply take over anyone's account. For example, I know your phone number. Let's say your phone number is XYZ. I will simply go to the forward password page of that particular target. I will enter X, Y, Z in that phone number section and I will just observe the response. Okay. In the, since in the response, which is leaking the OTP, then I will enter the OTP, that particular OTP, which I got from the response. And since the OTP is correct, they will allow me to reset your password. Right? So in that case, what is the
root cause? They are just leaking the response. They are just leaking the OTP in the response. So similarly, there may be some kind of JS files where they are leaguing, for example, in some variable, let's say bar otp equals to 123456. They may leak in some JS files, right? Similarly, I will show you another one. See this one. So this was found by one of our popular researcher. He found it in an Adals website. So what he did, let's say that in this case, the victim's username is case 1337, okay? So he just entered this one, two, three, seven in the forward password section. And this adult website sent the forward password link to that
particular user's email address. Okay. Now while observing the requests, he found a request endpoint, which is basically slash API slash reset password token slash the username, this one, three, three, seven. Okay. He just opened this one. And as you can see in the screenshot, forward password token, basically the unique token which the application generated. The token is getting leaked over this particular endpoint, right? The token, the timestrap, the ID of that particular user and the username also. It was getting leaked. And so in this particular screenshot, so for example, your username is 2min17, okay? So as a malicious attacker, what I can do? I can simply go to forward password section and I will enter Tugin1729 as a username.
Then what I can do, I can simply reset the password. And after that, I will go to this particular endpoint, okay? Slash API slash reset password slash Tugin1729. And then it will leak your account's password reset token here. And their password is a thing for looking like this one. Basically, company.com slash hashtag slash change password slash the username of your account. then slash token. So here what the researcher did, here after getting the token and the username, the researcher just went, visited this particular URL, company.com slash hashtag slash change password slash case13337 slash the particular token, this FYJ5RS blah blah blah. When he visited this URL, it will allow the researcher to reset the password of that particular
account without having any access to that account, right? this is obviously a big issue this is a zero click account takeover right we can able to take over anyone's account so by expecting that like token leakage vulnerability you can say it's a token leakage vulnerability right information is so that you can say so obviously while testing the password is a feature you can you should uh check the response of that particular password is a feature maybe they leak some kind of links and maybe they leak some kind of password token or they may be the leak, what do you always search for that particular thing. You can also try on some JS files. Go to the specific source code and check for JS files and in the JS files,
search the particular OTP. You can also use the BERT search method using BERT search. There is option in BERT search section where you will simply search the OTP and if it is getting leaked anywhere, then you can report it. And you will get some bounty. Okay. So this is another method where you can test in which you can test also. So our fourth one is HTTP parameter pollution. So what happened? For example, the password is a request is looking like post slash forward hyphen password, HTTP slash 1.1 post, let's say target.com. And in the body, it is taking the email address. This email equals to victim at gmail.com. Okay. So here let's talk about this first one. What I did, I just entered email
equals to victim at gmail.com and email equals to attacker at gmail.com. I did this one. So sometimes what the application can do, what the server can do, server maybe generate the password reset link for the first email address. But this victim at gmail.com, what the server can do, server may do that they will generate a password link for victim at gmail.com this first email address and they will send that particular link to the value of email parameter what is the final value of email parameter see here first i declared the value of email parameter is victim at gmail.com then i declared the second value is attacker at gmail.com so what is the final value of email the final value of email parameter is attacker
at gmail.com right So in let's talk about C programming. In C programming, if you declare x equals to one and then after some time you declare x equals to three, then what is the final value of x? The final value of x is three, right? Similarly, here I declared the email parameters value victim at gmail.com. Then I entered attacker at gmail.com. So what is the final value of email parameter? attacker at gmail.com, right? So basically here the application made what the application is doing. Application generated a password is set in request. for this particular email address victim.gmail.com and send the email send the password reset link to the value of email parameter which is attacker.gmail.com then what will happen the attacker will get
the password as a token of victim and using this particular by exploiting this particular vulnerability after so the attacker will get the password as a link of victim and he will be able to reset victim's password right So similarly, you can try these kinds of things also like you can say, try to send as an array. You can use percent 20 comma this sign percent, whatever you can track these things. Let me show you a practical scenario here. So see here what I did. Let's not focus on the first instructions. Let's only focus on the body. There is a parameter called email underscore ID where I entered the victim's email address. Roomba b75 at gmail.com.
And I declared another same parameter, email underscore ID, which is basically to winbo70 at gmail.com, which is basically the attacker's email address. And I clicked on the send button and they will respond as a 200 okay response. So as you can observe here, what the application is doing here in this case, application is generating a password is a link for rumpab75 at gmail.com. And it will send the password to the value of email underscore ID parameter. The value is to winboss70.gmail.com. So as you can see here, this is the inbox of winboss70.gmail.com. You can see the DB. And here, the support at the company.com, what they did, they sent the password link of frumpavi75, right? You can see the internet here.
They sent the password link of victim to attacker's account. This is to winboss70.gmail.com, right? So what I can do? I don't have access to rumbabi75.gmail.com, right? What I will do, I will simply click on this password reset link. I will be able to reset rumbabi75 accounts password. Then I will be able to access the rumbabi75 accounts password, right? It's also a zero click account database vulnerability, which can be achieved via HTTP parameter policy, right? Similarly, you can try this kind of things. So here I assume that the parameter name is email. If the parameter name is different, then you will set up the different parameter name like this one here. The parameter name is email underscore ID. Okay. So I hope this is
clear. If not, then you can ask to Discord also. Let's move forward. The fifth one is insecure direct object reference. You all know about this particular vulnerability. So in some cases, the forward password session can be vulnerable to IDOR. Okay. So what you can try, you can, for example, there is a ID parameter. Okay. For example, the password request contains three parameters. First one is email address. Second one is ID and third one is recapture response. So for example, you entered in the ID, the ID parameter contains the account ID and the email parameter contains the email address of the account. So what you can try, you can enter your email address through the email parameter. Let's say email equals to 2.070 and there
is gmail.com. And in the ID parameter, you can try to specify victim side. Okay. For example, victims ID is the two and my ID is one. So the normal request would be email equals to two in both 70 at the gmail.com and ID equals to one. Okay. So what you can do, you can try email equals to two in both 70 at the gmail.com and ID equals to two. Okay. So it may happen that they will generate the password on the basis of the ID parameter and they will send the password on the email parameter. So you can try this kind of thing. Similarly, you can use paraminer to get some extra parameters. Sometimes running paraminer over the
forward password request may give you some additional parameters, maybe UID or ID, whatever. Paraminer is nothing but a barcode extension. You all know that. Or you can append some previously known parameters. For example, during the profile update, you may came across a parameter called QID or ID. You can also try to append that site. And you can try ID or on that particular ID. See in the screenshot what is happening. What I did, I just entered my phone number here, which is basically 8408.4169.
And after that, the same thing is OTP. which I entered 7566. Then I entered my new password, which I want to set then confirm new password. As soon as I click on the reset password button, see here, I got this particular request, but surprisingly this request has no OTP. Okay. It doesn't contain any kind of OTP which I entered. That means the OTP is getting validated over client side, not over server side. So what I can do here, here the user ID is my user ID. What I can try here, I can try to change my user ID with another one. For example, if I change this user ID 268159.
So the account whose user ID is 268159,
that account's password will be changed. So this is basically a simple item which I got during my bug bounty. So what I can do here, it can also lead to mass account takeover. let me just tell you see here if I send this request to repeater and run this run over the user id value of this user id from two lakh to three lakh right so all the users whose user id lies between two lakh and three lakh so there are one lakh users whose user id will lie between two lakh and three lakh all the one lakh user of the website's password will be changed right all the one lakh user's password will be changed which is basically a massive disaster for the company. All the
user password can be changed by exploiting this particular vulnerability. So this can be a P1 vulnerability because it's leading to mass account and you may get some 5 digit bounty also for that. So this is a simple vulnerability IDOR which would take hardly 5 to 10 minutes for you to hunt but it may lead to a 4 digit bounty. So let's move forward. This one is home. You can try homograph attack on password research page. Let me first discuss what is homograph attack. I'm running out of time. So let me do it first. So basically, homograph is nothing but, for example, if you search Cyrillic small letter, Cyrillic is nothing but a language. If you search on Google that Cyrillic small letter A, you will
see that the Cyrillic small letter A is same as the English small letter A. See, using by your human eye, Can you differentiate between these two email address? You cannot differentiate, right? You cannot differentiate with a normal human eye. But if you use some computer program to differentiate these two, they will show you that these two are different. Because here, the A is normal English alphabet state. But in the second one, the A is really small letter A. If you simply copy this gmail.com and paste it in your browser, You will get this kind of domain. You can just try. I will just share the slide and you can copy this gmail.com and you can try to paste it
in your browser. So let me just now discuss about what you have to do. What you can do, for example, the body of the password is email equals to victim at gmail.com. And if you replace that gmail.com with this one, I am telling you that this A is different from the previous A. Okay. This A is different. So if you just open this, if you simply capture the request, change this particular email with this one, what will happen? It may possibly end up the server will generate the password reset link for victiminder.gmail.com and they will send the password reset link with this email address. This email address means what? This particular email address, right? So they will generate the password, they will
send the password link of victim to this email address site. So if you simply go to Godaddy or any hosting provider, if you simply go to Godaddy or Nameship and buy this domain, you will able to get victim's password link, right? Since they sent the password link to this particular domain victim address, blah, blah, blah, right? So now the main reason, the main thing about this is how you can generate this kind of homograph. There are two problems. First one is how you can generate this kind of homograph letters. So for that, you can simply go to this particular link and download it. It will ask you for the name, which is the end at Gmail and then the top level domain, which is the .com. Then
it will generate automatically that email URLs, multiple email URLs that are possible. This is one method, one thing that I solved, how to generate these homograph things. And the second thing, second main problem is that obviously you don't, you don't, you should not want to buy this particular domain, right? This is costly, maybe costly. So how you can test this particular vulnerability? So you can simply try to create an account with your work collaborator, this to win 1729 at the right gmail.com.exe.exe.exe.
You can simply try to create an account using this link. You can simply go to password reset page and enter this particular email. Now remember here this particular A is the Cyrillic small letter A which I discussed earlier. This A is the normal English alphabet A but this is the Cyrillic alphabet A. So you can try to reset a password of this particular account. If the website is vulnerable, then you will get the password to your collaborator server. And the link will be sent to this particular email address. It will send the password link to this particular email address if it is vulnerable. Otherwise, you may receive no response. Okay. So you can try this particular
IDN. You can try homograph on password set page. I hope this is clear. So let's move on. So as I discussed in the password is an implementation technique that they may send a six digit or four digit OTP to your account. They may send a six digit OTP. Okay. So our four digit OTP to account and you have to enter that particular OTP. In that scenarios, in that particular implementation technique, you may try to try two factor authentication bypass techniques like response manipulation or like using account A, token in B or let's say that force browsing. So there is a lot, lots of techniques, all the two factors and all the possible two factor authentication bypass are dispersed in this particular URL.
I just uploaded my checklist over here. There are more than 18 to 20 cases of two vector authentication bypass techniques, which you can test if your target is sending OTP or a code in your email address during password is you can try this one. So, okay, let's move forward. So you can try to append a dot just after the entry. So one day I was randomly browsing Twitter and I got this tweet, which seems to be interesting. So if your backend is based on Ruby and Rails, what you can do, you can try to append a .json. There is an access control vulnerability in Ruby and Rails, which may help you to get the password reset token getting leaked.
So see here, this is the normal request. Basically post slash reset password, HTTP slash 1.1 and in the body, this one, okay? And in the normal, this is a normal request and the response, it will 200 okay. And with no content, but if you append a dot JSON after the particular endpoint reset here basically, this class reset password dot JSON and in the body it is this one. So in that case, it may get, it may leak the particular topic. If the backend is based on Ruby and Rails, then it may often possible. So as you can see here, it is getting leaked. That unique password is a token of victim. getting leaked and by using this particular token you will able to reset this password right so
you can also try this particular method so our nine point is we can fix them what will happen basically uh sometimes while generating the password token as i said earlier password token is a unique token for your account so sometimes uh while generating the password token developers may use a weekend right For example, they may encrypt the user ID or username of victim and the time step, which some we can like base64 or Caesar Cipher 13 or something like that. So in that case, you can able to generate anyone's password token, right? For example, they are encrypting the username and time step with Caesar Cipher. So what you can do here, you can simply enter your victim's username and enter the time step of when you generated the password
of victim and combine it and just change it with just encrypted with Caesar Cipher 13 or if they are using base64 then just encrypt it with base64 and you will get victim's password reset token right and using that particular password reset token you can able to reset victim's password right so this thing you can try although nowadays developers use a strong encryption so you It is your luck if you find this particular vulnerability. So let's move on. CRLF injection, let's talk about this one. We are running out of time, but okay, let me see. So CRLF injection, if sometimes what happens, as I said earlier, if the target is behind some WAF or if the target has some creator, then you
will not able to change the host data directly. In that case, what you can do, you can use the, you can try to exploit CRL of injection vulnerability, which will allow you to modify the host header in the servers. So see here what happened. If you simply decode this particular payload, which is nothing but host, attack.com. So here what happened when I was testing the particular target, when I changed the host header value to Bing.com or attack.com, it is showing me for the forward. But when I just append this particular payload in the request and hit the send button. It will show me a 200 okay response with this particular body. So when I opened the link, when I opened my Gmail account,
see here, the password is it? The domain is changed from services, the academy.target.com to attacker.com. Right. See here, I just modified the value of hope, data, while you're exporting this particular CRLF injection vulnerability. Right. As you can see here, attacker.com is there. Right. So, okay. So, this is basically similarly same as the first section password reset poisoning. If the attacker, if the victim simply click on this particular link, you will be able to get the victim password reset token, right? Using this particular thing. You can check the log files or if you are using collaborator, then you can simply visit the collaborator server and click on the poll now button to get the victim's password reset token. and simply change the host
value from attacker.com to target services. They are in this case, academy.target.com. Simply change it. Then you will be able to reset these passwords, right? And you will be able to get it. Okay. So let's move forward. So sometimes what happens, changing the value of changing the request method and content type may help you. For example, in this one, see what I did. It was basically accepting a normal form email equals to tucungbos70.gmail.com. What I did here, I just changed the normal form to this JSON body. Or what you can do here, you can also try to change the normal form to XML request also. And check how the application is responding. Sometimes the application may send the password, leak the
password is a token when you specify an invalid content type or when you change the request body. So you can try observing how the application is responding when you are changing this particular content type or when you are changing the particular body. You can try observing. Okay. So our next one, last one is appending null bytes after your email. Similarly, appending null bytes after your email may help you in resetting a password, in a forward password. It may leak if the password is a token or some sensitive information. Okay. So for example, this is a normal request, email colon to winbox70.gmail.com. What I did here, I just appended a person 00, basically a null byte after that particular email. And you can
try to observe how the application is responding similarly, like the previous case. If after appending a null bytes, the application may leak some kind of OTP or some kind of token, password is a token or some kind of sensitive information. So in that case, you will simply be able to get the password reset tokens. So you can append any null byte like %00, %0d, %0a, %0c, %09, blah, blah, blah, right? You can try to append different null bytes and observe how the application is responding.
If the application is leaking some kind of tokens, then you may try to escalate it further and escalate it to account over, right? So for more, I'm running out of time. So that's why I don't, I cannot tell all the methods to test the password is a feature. But if you want to learn more, you can see the link. I just uploaded all the possible cases of a password is a feature. So whenever you came across a password is a feature in your target, you can open this particular link and you can test all the methods which I specified one by one. And if you have any doubts during the test cases or if you have any doubts regarding anything, you can also contact me over the
Discord channel of the business or you can also contact me over Twitter or Medium or Instagram. You can give me a follow also. So here are my IDs. Thank you so much for ending this session. I hope you enjoyed it. So give me, you can give me your valuable comments and suggestions over the Discord session. Thank you. Thank you so much.





