08 - Deep Dive To Entra ID Token Theft Protection
Show transcript [en]
The title was originally deep dive because I only have 25 minutes. So, it's just a regular dive. So, not that deep. So, my uh previous record for this uh talk has been 29 minutes and and 38 seconds. So, let's see how can we do today. Uh so, there's a lot of things I'm going to cover today. So, just jump into the subject. But before we go forward, this is a a tweet about a year ago from my friend. So he has like a kind of like policy uh for social media. So whenever he's sharing his slides, he's betting the worst picture of him. So whenever they see him alive, they are like, "Hey, that's not that bad." And this is how he
looks like. So uh my name is Dr. Nesto, also known as Dr. Azer and I work for Microsoft. I need to double check what the organization is nowadays because I was reorged on Monday. So it's cloud uh application identity research and what I do is so I kind of like two things. So one is that I'm going to I'm trying to find vulnerabilities before the bad guys do. So you're welcome. Uh and the second one is that I'm trying to educate people and that's part of the role I'm here today. And uh I created a tool called AAD internals. Some of you might know that. I have some stickers which you can get after the uh talk if you want to.
And if there's no time for questions, I will stay here hanging around after the two other talks. So we can have a chat if if we want to. And this is almost the last uh like uh speak or talk in my uh the non- US tour 2025. And last time I checked, Canada is not part of the US. So happy to be here. And uh I only have one one thing uh left. unless uh I got accepted to other other things. So I just need to go to Buenos Iris in three weeks. So it's going to be like three different continents tour. Okay. So let's uh start then so with token based authentication attacks. So uh let's start with the key
concepts that are involved in in when we are talking about token based authentication attack. So we have uh three roles. So first is user who is consuming services. The second role is um service provider who is providing services. And lastly, we have identity provider who is providing identity and access management services. Examples could be like me as a user. Then we have a service provider let's say uh exchange online and then we have the identity provider entry id in this case. So how cloud works in one slide. So we can put these roles into actions. So first there's a user like me nest I want to access uh access online using outlook. So I need to first start and go
to identity provider or Android in this case and endro doesn't know anything about me. So it only knows about me when I tell it. So I need to prove my identity. I can use username and password. Uh I could use uh uh phto keys or whatever. But anyways I prove my identity to intra somehow. And when Entra is happy, Entra believes who I am. It creates an access token, a refresh token and then sends those back to the uh user and then I can access the actual service. I go to service but again the service provider doesn't know anything about me except what's inside the token. So now I already logged in that access token says okay this guy is nestary he
can access online using outlook for one hour. And after that expires, you need to get a new token. But that's kind of like how cloud works. And then start with a couple of quotes. So first is that attackers doesn't break in anymore. They just log in. So quite easy because there's nothing where to break into anymore. And then let's uh see uh some statistics. So this is from our report called uh Microsoft digital defense report 2024. And what we have witnessed is that most of the attacks are nowadays passport attacks. It doesn't mean that they are successful but they have been trying to attack those. And only like 1% is something else like what we have here.
Oh, wrong way. And let's try this. So we have for instance token test. And why is that is important is that nowadays well who is using MFA to login. Okay. I don't who is using phto keys or something like that. Yeah. So it doesn't matter if somebody steal your password. They don't have any any use with this those. So that's why they are stealing tokens and that's why we are focusing on that. Okay. Uh second quote from our security vice president uh John Lambert which is a quite famous quote. He said that if every time he would have a dime when somebody's showing this. So basically what thing is here is that um that attackers they try
to find any uh like a a way to the the end goal whatever that is and we need to be aware of those so it doesn't work like it used to be that I have a firewall and that's it because there are other ways to get into. So that's why I'm using graphs now. My name is Dr. Azeri or handles because I really am a doctor. So I I I'm doing like this like proper research also. But this is a paper um I sent to a conference and when you kind of like send these kind of papers and this was about craft theory and attack crafts. So they are reviewed right and the first review was yes this is very good. second
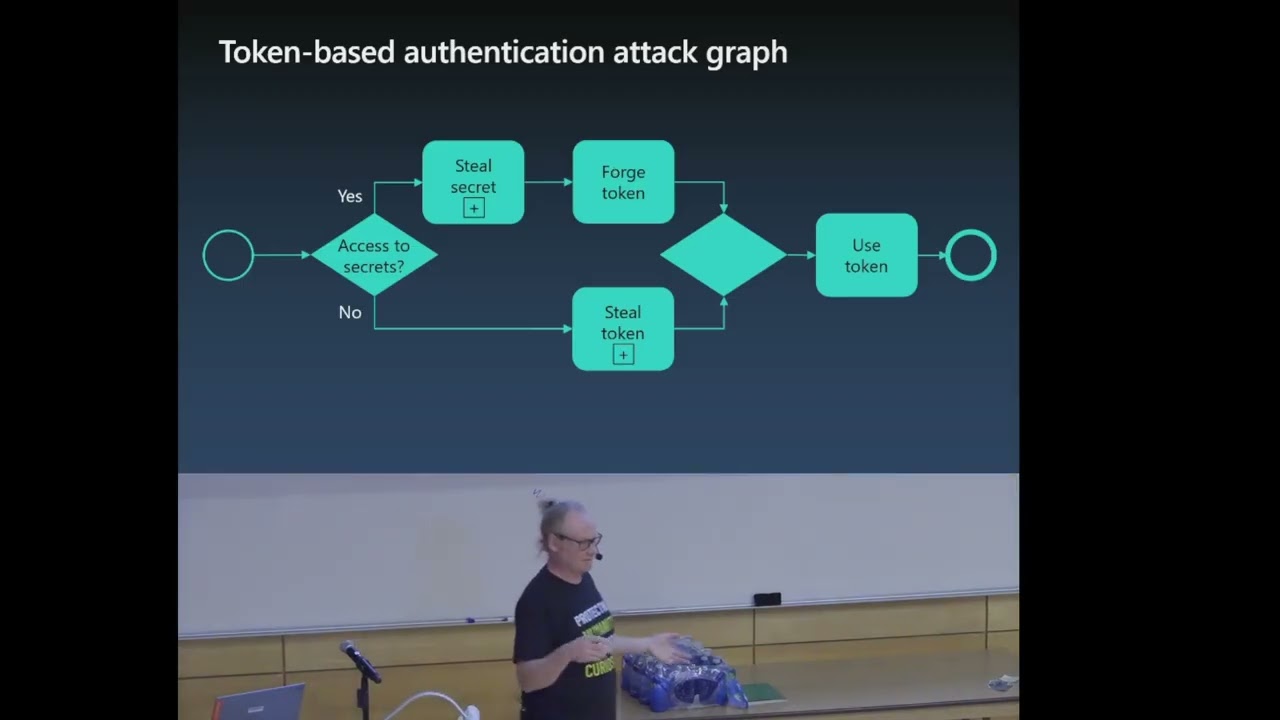
one wasn't that nice to me if you will. So his or her first question was so where is the graphs and uh where is the graph theory and that wasn't the first question. So it looks like this. So I I made nice graphs but it didn't work but anyway it was accepted. So my interpretation about graphs I think that's okay. So that's why we are having these graphs now. Um yes so this is like a the whole token based authentication at a craft. So you have two options. So if you are nation state actor you could steal secrets let's say from us that you can then use to forge tokens and that actually happened a couple of years ago. So there
was a actor from the country who was able to get off the hands on one of our signing keys. And if you don't if you're not like a station na nation state actor, sorry about that. Uh then only thing that you can do is to steal tokens. But I had to update this uh graph two weeks ago because uh there's a guy called MMA was one of my friends. So he found a way that he could just forge tokens to all the tenants in the whole wide world. But that's now fixed. But still this is a quite accurate. Um so let's just jump over of these and then to token theft. So they are kind of like we have witnessed
like two kind of things. So first is like what we call sometimes network based attacks uh and that involves kind of a link to some site which looks like our site but it's not and and uh then there's adversary in the middle who is collecting our stuff and um so basically you are not going to our login page but we you are directed to some bad guy and and you can use whatever thing to implement this but evil sync is quite often used. Who has heard about this? Okay. So, I'm going to show a demo about that. So, let's hope that hope that demo guards work because I had this presentation like two weeks ago in um
Belgium and the network just didn't work. So, no demos. Okay. Evil jinks. And we start that in developer mode. and going to copy the URL and as you can see this is like the URL so just one letter replaced with a zero and we can copy this and then we go to the uh victim's computer here and our victim is using Chrome and now he's clicking link Okay. And now this looks like uh our signing page. But again when we go up here we can see that it's not. Okay. So, username
and then password.
Of course, I'm not using my real password because I saw that last weekend in in Rome. So, I had to change that. But anyways, you can see that uh here here it says that hello Toronto and now I'm going to move this away. But but basically what happens here that whenever now you enter your username and password in that kind of site even that you are using MFA uh they can get your username and password and they you might use that in other places. So that's one value and the second one is that you will get a hand to session cookies which then you can use later on to log in as that person. So that was one of the attacks and the
second one is that uh if you uh sorry where it is okay let's hope this work. Okay then the second attack is that if you have um access to user endpoint then you can steal stuff from there and there are sort of things that you can steal. So uh first one is that if you are like a local admin and there's no TPM, you can steal the identity of the device. So keys that can be used to like prove the identity of the device. And if you have no uh admin permissions, you can still steal a lot of stuff like um session cookies and uh certain keys and tokens and and so sorry not keys but cookies
and tokens and what kind of tokens you can have. So there's also a lot of different like tokens other are more valuable than others and uh the first one is like what is called primary refresh token or PRT and a session key that is like bound to that token. So again if you are a local admin you know users username and password or pin and there's no TPM you can steal that. I'll demonstrate that later. And then we have like different kind of tokens. So but there's a little time so we are not going to go deep dive into all but the PRD is like a most valuable because it gives you persistent access to any uh
resource using any client. The normal refus token gives you a persistent access to one resource and one client. And then the access token gives you access to a uh certain client certain uh resource for a certain period of time which is anything from 1 hour to 28 hours. So it depends which kind of configuration you have but we will get back to those later. and a demo for that. So let's start with uh user permissions. So easiest way is to start the best browser in the world called Microsoft Edge and hit the um hacker button or F12. So now it starts kind of recording that what is happening here and what do we want to
search from here is like string like this. So whenever you are authenticating uh or sorry you are using like um services like with outlook you are calling a certain API and there is a header called authorization and it has the bearer and then there's your access token. So let's start uh just search for those and there's a lot of them. So let's take the first one. So basically you just copy this. So now you don't even need to log in because you are the person if you just uh copy and use this. I'm just going to show you what's the content. So datwt.ms I paste it there. And then when I move down we can see
that you have a outlook web and you can access graph and graph API is u like our API that you can pretty much do anything and we have some scopes here also somewhere here. So you can do these things if you have like a permissions in the back end. But anyways quite easy nothing to hack. And the second one is that uh we are now um compromised the endpoint. We are administrators. So we can then just um import my toolkit called AAD internals and uh the for the endpoints version points hit the enter and it doesn't work because this was blocked by your antivirus software. So let's just remove that and
And we can do this because we are the hackers.
Okay, let's try again. Much better. Okay, I should have the credentials already here. Yes. So can say does the get a int keys from the cloud access AP uh cache. I provide the credentials and now because there's no TPM this machine I can do this. So now we have the refest token or PRT and also the session gear that is required to use that. So I need to speed up a little bit but anyways now we have the attack token theft attack graph. So basically uh can you access endpoint? Yes. If you have no uh permissions you can just steal tokens. If you have permissions, you can install malware and steal tokens or you can even steal secrets in some cases and
then you can acquire tokens. So let's imagine that you have the PRT and system key then you can ask new tokens and then just use them. If you don't have access then you can use in the middle and to steal tokens. Okay. So we have a kind of the three um uh token security best practices versus condax policies. Who have heard about those? Okay. And then we have a token binding and then we have continuous access evaluation. So let's walk through of these uh three things. So how these uh conditional access policies work. So basically you go to entra and you say that who you are and so on and they are evaluated there. So basically you can
limit that okay I can't access exchange online or I need to use MFA but anyways if Android is happy you will get access tokens and then you can uh access access the service. So condition access policies may may prevent against adversary in the middle attacks and also to acquire tokens. Uh and how so for instance you can require that you can only login from the devices that that are like compliant and the adversary in the middle guy is using computer that is not that compliant. So you can block that and the acquire tokens means that you can um uh you can configure that. Okay, you can you can't log in unless you are in the safe network or that kind of thing.
So you can use that to prevent that. So a quick demo about that. So I have a tenant here. I go to security conditional access. check the policies and require compliant device and I just turn it on and that should do it. So now,
so let's try the chrome
Okay, now I'm going to use the real password password.
Okay. But it says that you can't get there from here because I I I use this simple simple rule that requires that I need to have like compliant device. Okay. Then to token protection. So I'll just like walk this through quite quickly so that we can get to the uh point here. So how this works is that you have a supported device. You go to Enra and you said that I'm I'm using this client is supporting token protection. So give me protected token and what then happens is that Entra sends you access token but those are encrypted using the keys that are available on the endpoint. Okay. And then when the tokens come to the
endpoint they are decrypted and then after that they are used. Uh so token protection protects uh tokens in transit but whenever they are reaching the endpoint you can still get those uh decrypted uh access tokens. So it prevents advers in the middle attacks because even though that you are able to intercept those tokens you don't do anything with them because they are encrypted. So that's what this thing does. And the last part is uh what we call continuous access evaluation or guy I don't know how to pronounce that. Uh so how that works you go again to entra and entra doesn't know that does your client support that so you need to tell entra that so you
said that okay I support this client supports this uh type of token and entra will send you a token but that token is now valid for up to 28 hours so not one hour but but 28 hours and why is that so let's see So you can consume a service with that access token now but this continuous access valuation means that uh exchange online for instance it supports that. So entry is sending like critical events like for instance if users username sorry password is reset it can say that you need to reauthenticate but if you have the normal access token that is valid for an hour so even though you reset users password during that hour you can still
use that but with this you can't. So that's kind of like what it helps us to do. So this conditional access validation may prevent token replay. So if you get it from from this endpoint for instance, you can configure that you can only come from the same IP that it was originally requested and may because not all clients supports that. So it's not like a silver bullet. Now this is the interesting part that um you threat actors can can exploit this. So to use this you need to have like P1 premium one license but uh you can use this even though that you don't have that. So threat actors can for instance if they are able to
compromise your endpoint they can go and ask and say that give me K compat compatible like access token which is valid for 28 hours instead of the one hour that it used to be earlier. So here's like a short u KQL you can use in your clock analytics to search for that activity. Uh but but we will get you can have those slides after the talk. So uh let's just move to the last slide which kind of summarizes everything. So we have these things. So like uh cont access policies and token protection that helps to prevent the adversary in the middle attacks. Then contra policies can help us to protect against this one and and cont access valuation flash part
helps us to protect this one. But there's no mitigation for this part. So if threat actor is able to u compromise your endpoint depending do they have like local admin access or not they can steal tokens or they can still install malware and then steal tokens. And the only AI related stuff in my uh slide deck is next one. So I ask uh AI to create a uh uh Simpsons themed old guy with a ponytail shouting at the cloud. So with that, thank you [Applause]





