Root To CISO or not?
Show original YouTube description
Show transcript [en]
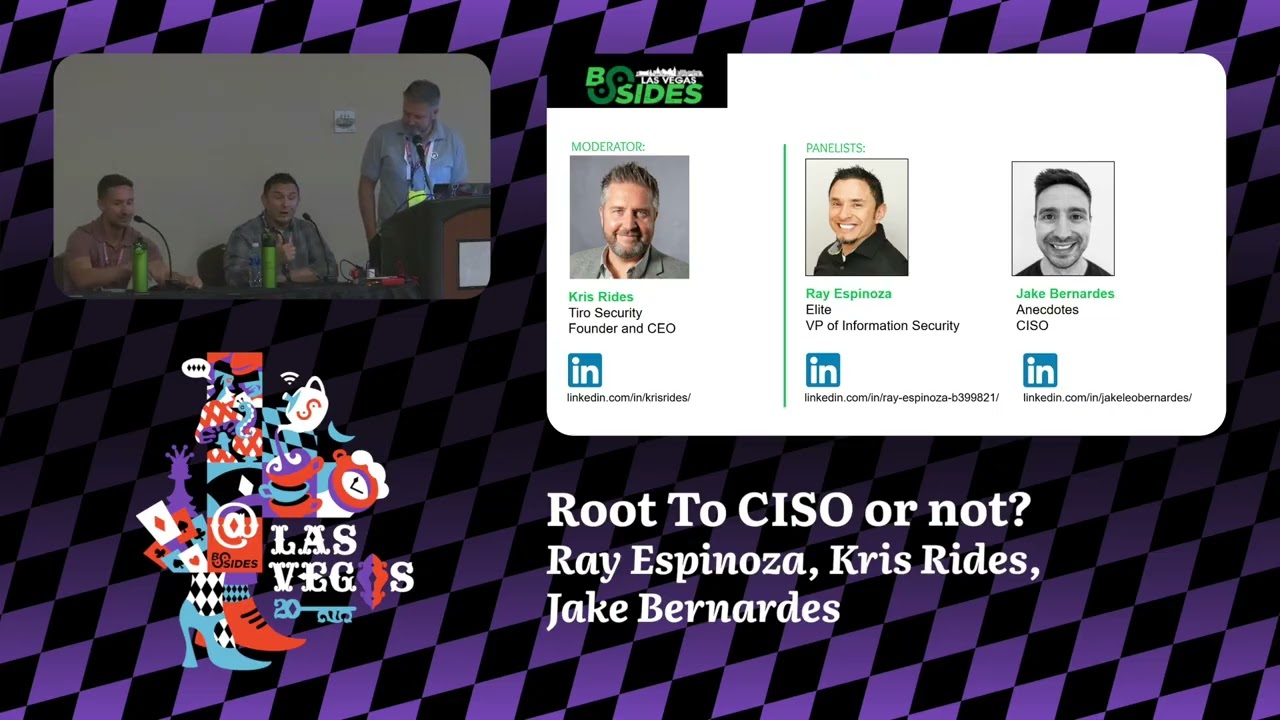
Okay. Okay. Welcome back to Higher Ground. Don't forget we have the world famous recruiter and bonus hiring manager panel at 4:00 today. Hacker Tracker is wrong. The site is wrong. That's okay. It's a hacker conference. And then we have a networking social from 5 to 7. And without further ado, the very prestigious Okay. >> Route to CISO or Sizo, depending on how you pronounce it. It's a debate or not. Moderated by the one and only. >> It's not a debate. >> Chris Rides and Oh my god. Jake and Ray. >> Yes. >> Yes. >> Well done. nailed it. >> Yeah. Well done. >> Proud of you. Thank you, Kirsten.
>> We were just discussing that, so there was a reason behind it. Thank you everybody for joining us today. Let's do this. Here's some nice pictures of us, some things we do. We'll do the introductions in a second. First thing I will say is that we've got 30 minutes. We'll probably try and get through this quite a lot because I I the Q&A part is the most favorite part for anybody that does a panel I feel and that's the way you guys get your actual real questions answered. Um but if you want to know more about both of these uh they were both panelists sorry both guests on my podcast which is called the route to
CESO podcast. So um >> can we just do live Q&A like people can put their hands up and ask whenever they want? >> I mean we could do just ask where they want whenever they want. >> You really want to do that? Yeah, 100%. >> Wow. Okay. Wait. Oh, yeah. Well, >> yeah, that'd be great. No, get Let's get Let's get a mic. Oh, whatever. I don't care. >> Whoa. We are going off script this. >> Yeah. Yeah, that's fine. >> We didn't really have a script anyway, so that that was good. Um, so just a little bit about me. Uh, I'm Chris Rides. I'm the CEO and founder of Tyro Security. We're a cyber security
staffing and professional services firm. uh started out of LA and we're actually I'm based here in Vegas or Henderson I should say. So it wasn't very far for me to get here today. Been involved with Bides for a long time. I think this is probably my seventh or eighth year speaking here. Um I speak at a whole bunch of other places. So I've spoken at Defcon, RSA four times, Infosc World, uh ISC2's security congress. I'll be at both of those later on this year speaking as well. So hope to see anybody there. Uh very involved with the community. One of the founders of the SoCal chapter of the cloud security alliance and I sit on a few boards. The
national cyber security training and education center. I lead the industry advisory board. I'm on UNLV's board here. Uh also Washington Cyber Security Center of Excellence. Uh so that's me. Yeah, very involved with a lot of stuff. My background is recruiting. Been doing it for 25 years. Uh, and I know a bunch of CISOs and they're usually kind enough to chat to me about their careers. So, that's it. Uh, Ray, over to you, mate. >> All right. Hello everybody. I'm Ray Espinosa. I'm VP of information security at Elite Technology. Um, I had the honor and privilege of being on Chris's podcast and shared a little bit about uh my journey, but it was more of the
technical journey route into security and then working my way up uh to a CISO level role multiple times and then stepping sideways to a different type of role as a technical program manager and then back to a CISO role. Um, so excited to share a little bit of that journey here. Um, and hopefully can add some sort of value. Uh Jay Bernardes. I'm the CISO at company called Anecdotes and a multiple time CISO as well. Do a lot of advisory work at startups, a lot of design partner work particularly in the Israeli ecosystem as well as a lot of the VCs as well. I've got a fairly standard background. I came up as a hacker. I was
terrible at web app testing, even worse infra testing, but it worked out after a while. I was quite good at social engineering and breaking into things. Um so that's how I actually got my first job. I literally stole someone's backpack from a Starbucks, tailgate into a building, sat down the CEO's desk, and went, "You've got a problem." Um, I got hired. So, >> I'm the problem. >> Being a CESO parallel, not a long technical road. It's just you just have to be a thief. But, um, yeah. Cool. >> Okay. I'm not saying that that is something that anybody should do here, right? So, uh, there we go. Well, we I was going to we we were going to sort of
talk a bit about our careers and and or their careers and and how they got here. I think it would be good for them to have a little bit of a background of of the journey and then really Yeah. Yeah, I mean if people want to dive in with questions at any point, just put your hand up, come and ask a question. You got two set multiple time CISOs here. If you want to be a CISO or if you're thinking about or you don't even know whether you want to be a CISO yet, then these are the people to ask. So, uh Jake, do you want to just give a bit of an overview of, you know, you you've
given a a pretty brief overview already, but give a little bit more detail maybe on that and, you know, anything that these guys would find interesting. >> Yeah. Oh, I even haven't even started yet. His hand went up. Go ahead. Hey, what are you going to ask? >> Wait, let's get the microphone. >> She's running. >> A can't get the employees nowadays. >> Still, I didn't work. >> Just shout loudly. I'll repeat it for you. >> Oh, we got to get it recorded. >> Hello. >> Yeah. Go on. >> Can you guys hear? >> Yeah, you got it. >> All right. in your roles moving up to CESO, there's lots of times where you don't have the money to do much more for
your sock staff or whatever. What were things that you did on the way up? You've kept the the little cherished nuggets that I can do this to help my support staff without costing a tremendous amount of money. >> Um, great question. Should >> I go? >> Sure. >> Yeah. >> I've got two lessons I've learned as a CISO. Uh, one is don't piss off engineering. Um, so like your best friend is your CTO and your next best friends are your SRRES and your next best friends are your devs because they're the people who can either like completely railroad and destroy your program because they don't want to do any like vulnerability management whatsoever or they can just start
building crap really fast and causing even more problems for you. Make friends with them and make them your allies. If like you build security culture, you build it inside of the engineering team. That's the only bit that really matters. Like that's where it works. Um, the second is design partnering. Like I've spent my entire career being very open to any conversation that any founder reaches out to me on LinkedIn and it happens a lot multiple times probably a week. Um and I'll look at anyone's product and give them my time. The reason partly is because I kind of believe in pay it forward. I'll look and say this is a terrible idea. Most of the
time it's usually actually it's a great idea but like you don't know what your USP is. You don't know how to sell yourself. But we have been in the first 10 customers of multiple now significantly exited businesses uh by being early doors and that meant that we had grandfathered deals like I I was paying whiz like 10 grand as an example. So I think yeah I think that's the one right get in early look at other people's work share your expertise and in doing so take their products for free then you don't have the cash flow problem. Okay. >> So, um I'll echo on some of that. I think being having been at multiple startups, a lot of times you have to be
crafty. I think the first thing is to help your team understand what's the landscape and what are we dealing with and being honest with them first and foremost and trying to find ways to add value to them and their day job. Uh but if you're trying to solve problems like in the sock or other things, you know, as you mentioned, finding startups and design partnerships or finding ways that you can be mutually beneficial, I think are hugely valuable in a way to solve a security problem while also leaning into the ecosystem and driving overall change. Um building relationships, uh trying to get crafty with solving problems. There may be times where I was able to work with technology and
development teams to create some tooling that we needed to solve a security problem which meant I needed to better evangelize what the problem was that we were trying to solve. So I think it's it's a ton of PR and building relationships internal and external that can really make the dollar stretch a little further. I >> I want to add something actually as well. I'm talking from a recruiter's point of view. So I see why people stay at companies. I see why they leave companies. Um, and I think in terms of getting more without being able to just throw the money, most companies can't just throw more and more money at people. Um, the really key things that I
I think make a difference is um, having a really great mission, right? A lot of companies and and teams um, keep their staff because their staff believe in the mission um, and want to work and want to move forward and if they have to get paid slightly less than someone somewhere else because they believe in the mission, they'll still stay there. So, that's one thing. Um, and I guess that kind of also feeds into um, feeds into sort of them feeling part of the team is like making sure you listen to them. People want to make a difference at a company. Um, and the best thing that I think CISOs and leaders can do is
like engage their staff, listen to what they're to their thoughts, ask them their opinions on some of the stuff you're doing, right? Can you bring them in? If you're doing some PC's, can you bring those staff members in and get them involved? they feel like they're having an impact in your business and in the team. So that's what I would add. >> There's one small point that I would add to that because you can be very pessimistic to be like, "Oh, this sucks. You know, we have no budget. We have all these problems. We can't do anything." A lot of times that negativity will breed negative feelings across the team, but helping them understand. I think Chris
is spot on with finding ways to have them connect with the mission and what we're doing. And that was part of what I was trying to say, being honest of where where we are as a business and what we can do and what we can't do. But um yeah, listening to them and being having them be a part of the ride is is huge. >> Yeah, I >> I think we survived 11 minutes. So I'll break it by saying AI. But um like that's ch that it has changed the game in this respect. So like when I when my team come and say we need money for this, my first response at this point is
can we just replet and zap it? Like do we do I need to buy a tool? Because I there's multiple things in my stack right now that we just built. like the the the idea that it's completely natural language processing and you don't actually need any competencies in coding is complete BS, but like the reality is it's much easier than it used to be. And you can build a lot of the tools on the market right now in security yourself. You can build integrations very quickly. Like you can do a lot of this stuff now in a way that you couldn't do before on a a headcount budget you couldn't have thought of before. So I think that's changed a lot
as well in terms of budget constraints. >> Good stuff. Any other Yeah, another question here. >> I ruined this Chris right I love it. This is the best. I love these. So, this is the best way to do it. >> Um, hi. This question is for Jake and Ray. And no offense, Chris. For people who were kind of more technical and you made your way into CISO role. >> Wow. Okay. All right. Thanks a lot. >> Unless I'm wrong. Unless I'm wrong. I'll see you later. Um so the question is uh and for the context I've moved from being a highly technical person now I've moved to become a security engineering manager for a while and I feel like I'm missing
out on doing hands-on work um let's say from 100% now I've moved to like 50/50 and from looking up top looking at our seesaw I can see that that is going to translate into like not doing any technical work at all. Do you miss being part of teams that did like highly technical work? >> I'll start. So first I think it's completely dependent on the organization. I mean I've been at large enterprise companies uh and I've also been at startups and so I've been the CISO at publicly traded and startups as well. I'm in a hands-on technical role and my company's probably mid to small enterprise. So I think it is absolutely um company dependent. you have the
ability based off of the skills that you bring to add technical value. Uh there are times where you do need to think strategically. You need to make sure that you're showing value above the team, you know, to uh the rest of your executive leadership team and the board, etc. But it's highly dependent on the organization. Like I'm still tactical and technical, but also strategic and with the board as well. So it's it's not just a oh you see them in sort of the ivory tower and they come out, you know, with the tablet says here's our strategy for the year. Uh I don't know if that's a role that many CISOs have outside of maybe Fortune 100, but
>> uh I think you've got the wrong people in the room as well on the panel. So both me and Ray come from technical backgrounds. There's a lot of CESOs who come kind of audit advisory backgrounds and I think they then create this persona of this completely non-technical CISO. Like it's not the reality in most people. Uh most of us crave and still find a way to be involved. So I I think point one is like you have the requirement to be the one thing I hate most as when I was coming up is like you'd have a cease or leader who just threw voms over the wall was like fix this you're like context like
exploitability like reality any of it like in the reality is you have to understand the text that you've got in your business you have to understand how the code is built like you the same speaks to AI when we talk about AI as CESOS and whether you're going to protect against it or allow it or shadow it whatever it might be right you've got to understand what the hell you're talking about or else you lose credibility instantly so there is a degree which says you have to grow up like you have to gain new skill set. You have to become financially way more bilingual. You have to become capable of talking strategy. You have to become
better at hiring and getting people in place who can do the stuff that you no longer have the time but maybe you do have the capability to do. So you have to get a way in which you enjoy that. And some people don't right if like if you want to stay deeply technical don't be a CISO. Like you're not you are going to lose some of your technical time like and you're not going to lose salary for it. I know guys who are deeply technical who get exactly the same pay as I do in the company. Um but that's staying in their lane of what they wanted to do and what they enjoyed. So I think it's work
out what you want to be and be that. But this concept that CISOs are not technical is certainly not true in most of the CISO rooms that I sit in. Most of them can speak to their entire codebase can still hit like can still speak to it can still hit the command line and >> do whatever they used to be able to do. >> I'd say and I know this not a question for me but >> yeah you didn't say you could answer. >> I love Yeah. didn't say I love the sound of my own voice. >> Assume that recruiters aren't technical either because Chris can speak tech. >> Yeah, I can speak tech. Thank you. Um
what I was going to add now and now I'll probably give a really bad answer and it was like oh what on earth that Chris bloke on about. Um yeah, so what I was going to say is I did a I've done a couple of things. So I've got I've so far interviewed 30 uh CISOs for my podcast. Two seasons, 15 CESOs a season. I'm about to start recording season 3. So I've got a lot of data from that. But I also went out to over 500 CISOs two years ago. Um, and I asked them for the most important attributes that they felt they needed to be a CISO and I can promise you that being technical um, is
absolutely one of the top it was in the top five of the of the things you hear. So having that background, having the knowledge as these two have said to at least be able to call on some of the stuff that's maybe going on, right? Um, but also to be able to help people and maybe guide them a little bit more. So you will always have that but you are right the big as the companies get bigger as Ry said you get further and further away from being technical and you end up being a much more strategic the ones that I know tend to be like if they still love their tech stuff they're still playing with it in the little bit
of time that they've got at home right but anyway there you go any other questions yeah oh good look we are definitely going to get through this with with just quick Q&A this is lovely >> see I had a plan >> you did I love Jake, I want to do these always like this. This is great. >> Um, so on the other side of the skill set, like what skill sets have you built or grown since becoming CISOs? And what are ways that people maybe communicate with you differently now that you're a CISO and not in a technical security role? >> Yeah. Um, communication. I didn't used to wear knitted polo shirts. So like communication and presentation
definitely change. um you have to kind of grow and mature a little bit when you sit in a lot of the especially in the VCs a lot of the time um you have to kind of fit in. So I think there's a way of speaking you have to learn to translate tech and security to non- tech and security people. You have to learn very confidently and acutely to speak about risk um in a way that people understand and get. I think you have to understand finance. Like the the best thing I've learned is you have to really understand accounting. Like if you want to the guy at the front, if you want budget, you need to understand how to explain what
the cost implications of not doing your ARM. And then strategically as well, you have to think outside the box. I think that if you sit in an executive team, I'm sure agree CISO is your title, but it's not your job. Your job is to help the business grow and develop. So you've got to develop skill sets around understanding go to market about understanding product design and development around understanding finance around understanding CS and relationships like support you have to understand this because in the end like I sit in a room of eight or nine people between us it's our responsibility to make the business grow um and they will contribute to my world and I will
contribute to theirs. So you kind of have to develop this way broader understanding and skill set. Does that make sense? >> It's a perfect answer. I mean, he was checking off things on my list. >> Nice. Yeah. Good. Yeah. I think the um the stuff that I would say I've seen cuz again, you know, I'm not a CISO, right? I'm a recruiter here. But um I think the things the big difference I see with a lot of CISOs is like building and growing their business knowledge. And actually, I think that's something you got, you know, you all could do from the start of your career. you know, understand what's going on in the company. Read stock market reports, you
know, try and get an understanding of that because you will be able to build and you not only a better career path, but also your your pro your program and your reputation within the business um very quickly understanding why the business needs the security, right? And if you can sell those two things together, your program will be more successful anyway. So that's that's probably the number one attribute that I saw come out of top CISOs is their real understanding of the business. And um I I'll give you one example of of a from a CISO that um she she was on a panel of mine in Houston and uh she told me about something she does which I thought was
amazing and for her to to bring stakeholders to the table. She has individual meetings, right? Everybody does that. That's fine. But she sat down and she asked them, "What is, you know, what what are you bonused on? How do you achieve your bonus?" Because if I can create my security program in a way that helps you achieve your bonus, because she knows the bonus is tied into what their bosses want is we're tied into what the company wants. If I can tie those things in together, I'll have a successful program. You'll be happy and you'll do, you know, you'll talk to me and want to be part of the security um goals that I've got. and the business
will be happy. So, I thought that was really interesting. She's the only person that's ever told me that and um and I think I've spoke to a lot of CESOs about it and a lot of them have been like that's a great idea. You know, so a lot of them don't haven't had that conversation before. So, who else had questions? Just as I say go to the nearest one first might >> thank you for your uh for your time. uh apart the uh experience which education uh like >> could you move the mic a little bit closer to you because I can't perfect better. Yeah. Yeah. Thanks. >> Which um apart the uh experience uh which kind of uh education,
bachelor's, masters and certification licenses uh do you recommend to being a CISO? >> Okay, good question. So that was um certifications and education. >> Yeah, I'm glad this is being recorded. Certifications are BS. >> They are absolute nonsense. Like a C CISSB means you can memorize crap. Like it means nothing. I've I've interviewed plenty of candidates for jobs who had every letter possible and knew nothing about the job I was interviewing before. So like build actual knowledge. Like there's two types of actual knowledge. Whether it's Pluralsight, whatever other platform you've got, go and listen to people who actually educate you about like how cloud security architecture works, about like how AI security looks, about how AI functions full stop inside
of like a SAS product. Learn about actual technology in a way whichever works for you best, right? Maybe that is watching videos, maybe it's labs, maybe it's hands-on yourself, I don't know, it depends how you are as a learner. Then whatever that first method was, get hands-on and do stuff. Because I can tell you that whenever I hire, my first question is going to be like, "Show me you can do this." Whether it's a hack the box or whether it's like standing something up or whether it's like explaining what I'm showing you in code, like I'm going to challenge you. Like the letters need mean nothing. And I can tell you that 95% of CESOs will agree
with me. And they won't hire based on the letters after your name. They'll hire based on what you can demonstrate you've learned, why you learned it, and how you can apply it. Uh, and that is a skill set that you can't get doing six-hour pointless exams on machines. Um, I would say it's a it's a bit of a bonus to a degree, right? Like going through it, you may be able to learn a few things that you can apply. And I think it's awesome like if you are going to invest your time to learn new some new skills, um it can be beneficial especially for your resume to have it. Completely agree with Jake, you have to
be able to demonstrate that you actually understand what it means. But if you're searching and just trying to develop in new ways, you're going to learn new skills. You either have the ability to apply it and learn it in your job or you need to find ways to seek some of it out to get yourself ready to go. So I think they have utility. They are not the if you have them then you get hired piece. um you know like I didn't graduate from college and so I had to learn a lot about business and my like initial fail my first CISO level role I was a CISO at proof point absolutely was not ready I
came more so thinking about it from like a security security operations point of view and you know I fell on my face after the first six months or so because I couldn't articulate to the business I didn't understand how to make the business successful and minimize risk and how to speak about it so I had to learn those skills along the way and so you can develop those in the classroom you can develop those you know in your in your job. So I think having those skills and understanding what the business needs and how you can enable them to succeed is the most important. Like I still don't have a college degree and that hasn't stopped me from you know
finding the success that I have in my career. It's not a path that maybe I would tell my kids to continue to follow and hopefully get to the same spot but it's you know it's not impossible. So they have utility. >> Yeah. I think um I'd add again from a recruiter's point of view, you know, when we're looking at what clients require, of course, we'll see certifications in job descriptions. Um but the truth is then at this point they're never an essential. Um there's nobody ever being got rid of and rejected out of a job because uh they they didn't have a certain certification. Occasionally, we get clients that still expect degrees. Um, but it is very rare even even for that,
especially if you we're talking about experienced people here getting into the into the role and applying for jobs, your experience generally will count more than a degree. Um, I would say if you want to spend your money on certifications or or more education, great. Good. Good for you. Um, do it because you're interested in whatever the subject is. So, if you're going to like if you're asking like which certification should I pick, pick the one that you're interested in, >> right? or the one that maybe you can utilize in your role so you can turn it from sort of I know a bit about this to actually I've implemented it and and and I know how it works. So that would be my
p piece of advice. I mean >> spot on like we talk about me not I've been in the industry since 2012 just in cyber security and and as a recruiter right you're right I'm not going to sit there at a computer and be able to do a lot of this technical stuff. Um, but I did my this the uh ISC2 CC. Um, I did went and did that cuz I thought it'd be interesting to pass it. I passed it first time. I I get 60 70% on the CISSP exams. So, I mean, I don't know what that tells you about about that stuff, but I'm not going to be able to sit down and and do the work, right? And yet, I
can still get that stuff done. So, it's it's interesting. I think, you know, do the stuff that you're interested in. Do the stuff and be able to speak about it. Nothing worse than having a certification and then when somebody asks you what did you learn? How have you used that? And you just say well I passed it. So more questions.
Uh so obviously everyone's situation is different but do you find that it's easier to make the transition from like a technical individual contributor role to a leadership role by you know internally or by looking for a change you know an open role in another organization and you know either way like do you have advice for the best way to sell yourself that you're ready for this kind of different type of responsibility? Uh, I'll definitely got the answers the answers to some of that, but you guys have the actual experience of doing it. So, Ray, do you want to talk through your career? >> Sure. So, I'll say it really depends on the company that you're at. If there's
if you built enough goodwill and enough trust, sometimes you'll have the opportunity to step into a new role because people trust. You're just somebody who gets stuff done and they'll teach you on the fly. Like my first role into security was at eBay after seven years of being in operations on the technical side as a Windows Unix admin and then a a manager. They're like, "Hey, come and build instant response for us because you have the relationships. You know how to run a SEV. Um we'll teach you all the security stuff that you want." And so they were willing based off of my reputation to give me that opportunity to be able to do that. You may be at an organization
where it's just not there. there's either a glass ceiling that you're already hitting and you look for other opportunities and you're really trying to sell the attitude, the mindset, the experience that you do have and why it's applicable for this new role. So, it's tough to say like one is more than the other because I think it really does depend on what your overall situation is. But, you know, sort of golden rule of thumb for me that I tell lots of folks is treat people well and kick ass at your job. And and if you do those things, many times those opportunities may find you or you're willing to seek them out and have enough goodwill and
trust to be able to have a conversation about why it might work. >> Yeah, I think I think Ray's point on treat people well and kind of just be a good human is a great one. I think you recognize very quickly if the person you work for wants to actually advance your career or not. Like I I've said a lot in public place on LinkedIn a lot that like my proudest moments are where the people that I've trained or have been employees of mine have gone on to become CESOs and are sitting in the same communities at the same tables as me. Like that's the greatest achievements I've made is watching those things happen. And I
think if you identify very quickly if that's your boss, great. Like that's the person who will guide you and either give you the opportunity in the org or will help you find it somewhere else. If it's not, then get out. Um, but I think the the one thing I would add is you mentioned about like self-elling. The best skill set you can learn at all like to advance your own career and be a leader is storytelling. Like you have to learn to be able to say like what you're good at. Articulate why that's relevant and tell it in a convincing, approachable, like consumable way. Like there's other thing I think I' I'd say one more thing and I'll get back to
Chris is like we have this obsession right now in this culture in this time that like you should find your flaws and improve them. Like I think that's BS. Like work out what you're good at and double down on what you're good at. Like I know what I'm good at. Like I'm really good as a startup scaleup CESO building security making it better getting a point to a near exit and going into it and again because I hate I hate enterprises. I couldn't have done what Ray does, right? I couldn't have been those. I'm not built for kind of the blue tape and the governance. So, I I think find out what it is, whatever it
is that you're really good at, make sure you're the damn best at that. Find out if your boss wants to accelerate your path from being damn good at that. And if they don't, then go and find someone who will. >> Yeah. Yeah. If I look across um when I look across sort of multiple roles that we feel, I I'll say a few things. First off, in the current market, it it is extremely difficult for you to get the promotion by applying for a new job because there's a lot of people that your your competition are people that have maybe been let go, you know, laid off that have already done the job at somewhere else and are making a lateral
move. Some of them even making um you know, moves dropping down from from stuff they've done previously. you know, we've got a we got a director of cyber security role that's reporting into a CISO and um I've got a hell of a lot of CISOs that are reaching out um and there might be some of them might have reasons for why they would want to do that, you know. Um but some of them are kind of forced because they're not working currently. So, it is tough. The best and easiest route is getting a promotion internally. Um and being able to do everything that these these guys have told you will really help you with that.
But there'll be a point where at some point maybe the person above you just is never going to move, right? That you know the only way they're going out of that job is in a box. So, so at that point you either got to try and create a position and a leadership position in some other way there or you've got to go elsewhere. So, >> or you could reach out to Chris on LinkedIn. >> You can of course >> that is his job. >> That is my Yeah, that is that is what I do. So, >> hi. Thanks for doing this. Um, just a question. What are your favorite sort of generic KPIs? Ones you find really
creative ones that you might have cave up on your own for upwards reporting. >> Um, so it's only really in the last year or so I I to your point about budgets earlier, I put a budget up. Um, my CEO looked at me and went, "That's nice." Like why are we buying any of these things? And it made me rethink about how we actually define and design security programs. And I went back to going, well, actually, let's look at all of the risks in my risk register. Let's look at every tool I've got right now, every headcount I've got, every consultant, every program and align it to the specific risks that I think that's reducing or mitigating. Let's look at
what remains and then let's look at what those percentages I think are likelihood or or impact and what I can reduce by doing something. So like my first KPI which is not really a ground to your question is that you have to talk in risk. I think that that's the fundamental one. You have to have to say here's the risk that we have. Here's how much I've reduced that risk portfolio. Here's what remains and here's what it would cost to bring it down X% or to remove it entirely. That that's number one. Number two I'd say is ROI. Like I think we've been saying security for long enough that we're not a cost center but still CISO struggle to show that.
like the ROI that I hear in boardrooms. I advise in a lot of boardrooms and the the CISO will stand up and go well this is the cost of a breach. So that's how much I should get to spend. I'm like that's a hypothetical tragedy. Like you can't build on that. Like you go into a sunglasses company like a Maui gym or someone I need to tell them you can sell X more pairs of sunglasses because of the dollars I'm going to spend. So you've got that's the next KPI is what's your ROI and your security program. So you've got risk, you've got ROI and security program. Then for me right now I go to human security. That's my third
and I think the one that's most relevant. Not internal fishing like simulation crap about gold mines in Africa. Like not about like training scores but like actually measuring in some way how competent your internal employees are in defending the business whether you want to start hacking them yourselves whether you want to use some kind of automated tool whether you want to whatever you want to do to measure them. Um produce metrics around that. So those are my three. It would be risk, it would be ROI, it would be humans or people security. >> So I I would say definitely those three. U one of the things that I learned in uh in like my second or third time being a
CISO is how to sell, how security is impacting sales. And that's um positive as well as negative. Anytime that we have a uh a close lost for an opportunity because we didn't have a certification, we didn't meet their security bar. Fro pro procurement perspective I was able to tie that back to how do we help the business win overall as a whole as well as the opposite if we've invested in in certifications or we've invested in additional diligence that we had to provide that's a net positive for the business that security program uh is adding that's yeah it's tough to uh it's tough to talk about if you don't necessarily have that there um the only
other thing I would add to that is you know when I've been at startups or early stages many times I'm selling security maturity we didn't have these capabilities before we didn't have the ability to respond or address these specific risks. And now we do. And so this is what the road map is going to look like on our path towards maturity as a whole. But that that only gets you so far. That's like one indicator along with still how do you help sales win and then how do you drive down risk for the organization and how do you spell ROI like critical >> stuff? More questions. >> Yeah, >> that was an awesome awesome question.
whoever asked that, that was really, really good. So, I just have uh my my question isn't so much on the trajectory of how you become a a CISO. Mine is, and you kind of just answered it in a weird way, but mine is around how much influence you have in that position to enact certain, you know, technologies, processes, and how do you go about learning of the things that you want to grab onto? In other words, do you just go out and kind of talk to other CISOs and understand what everybody's doing? So you bring that back in and you bring it in and you kind of try to normalize that or do you listen to in some ways
the salespeople the you know looking at you know different things internally to help you define kind of what you're going to drive I'm really curious around the you know what drives you to latch on to something and then really push it for your organization. I'll start. So the first thing I would say is you need to understand you need to understand your business period and you need to understand what's your most important asset and then you start to figure out from there you start you start to work your way from the uh inside out of do we have enough security controls do we feel comfortable with our capabilities around our ability to protect our our most sensitive assets
you know for us it's our customers data it's it's you know our customers client data is it's paramount and so all of our controls start with um when I I lead with the rest of our team around why we're investing in these areas. It's because of that and it's easy for me to sell and to be able to talk to. It's because we all agree our customers client data is the most important thing that keeps them in business keeps us in business and you start to figure out from there. So I think if if you don't it it is also great to be able to bounce around ideas with other CESOs as well of how do you report and what do you think
about these types of things. I mean we're not all that bespoke but you know only you know about your business and and what makes sense there. And so if you don't know, that's when your CTO, and I know that Jake mentioned this earlier, find those allies internally who are willing to give you the good, honest answer of what they're most concerned about, what they see as flaws in the business, and what do we need to get better at, what's going to prevent us from finding success, because they'll they'll help you provide some of that context. And then from there, as far as how to action it, maybe you don't necessarily know. And that's where you
get to leverage some of your relationships to say, well, how would you solve this problem? Is it a vendor tool? Is it a change in culture? Or, you know, what are the best ways to go about it? I I I agree with that. But I think there's two things. I think there's appetite and capability. Appetite is what do you want to enact what you want. So like you look and you go, I've got security people. Great. I need it because it will help me develop and deliver and control the endpoints. Great. I'm going to need some kind of dev sec ops or whatever the hell we call that because I want to control the info
and I want to be able to get things done in that world. Great. I'll inherit them. quite often a lot of CES will go I quite I want S surres because those guys now control a hell of a lot of stuff and they can do things very quickly and change things very quickly. So you start to look actually what people or groups inside the org do I want because they will help me deliver my plan. So I I think that's the first one and definitely like there's a hundred well there's not 100 there's a few very select and important CISO community slack groups in behind closed doors where we talk and we exchange ideas and
say have you done this and they'll say yeah and we'll go well I know someone who happens to have done this um and so we build off of that. The second is capability. If you're a good leader, you inherit these things anyway. Like if you deliver on your promises and you're a good leader in your own perfect sphere, you get another sphere and you get another sphere. And then at the point that anything you ask for, you inherit. At various times, I've had all kinds of functions. I've had IT, I've had SRRES, I've had parts of R&D, I've had HR, I've had support, I've had all kinds of random things because in the end, if
you're good and you show that you could deliver on the requirements and KPIs of that business unit and you want it or at least you're willing to take it, you will get it anyway. stuff.
>> Still can't get the staff. >> She's not even trying. She's just sat down. >> Okay. All right. Um, so >> oh, I'm quite scared at this point. >> Perhaps you all can talk about delegation as a strength in your seeso adventures. >> Indeed. Okay. Yeah. Yeah. Yeah. We'll do. So let's do that question then we'll talk about how important delegation is and actually finding the right person to delegate to because yeah some mistakes can be made. >> Yeah I like that one about hiring that's a good one. >> Um so this question is about the emerging legal landscape against CISOs. Uh last year I attended a talk at Black Hat which was about how to not get your
CISO sued. >> Was it Tim Brown or Joe Sullivan? >> Uh Sullivan. >> Yeah. And it was basically about, you know, preventative measures, you know, how to ensure, you know, you're doing the right right thing. >> But, uh, Chris, from your experience talking to CEOs, uh, or from personal experience with Ray and Jake, do you have any experience getting close to being sued or with any of the >> I I had I haven't so far, thank goodness. Um, >> yeah, I I think it would be interesting to hear what what you guys do because it's it's become a thing. Well, the whole director and officers um insurance thing has become more and more important to candidates to ask that question. Um
there are still plenty of CISOs that will take jobs without asking and some that will even take it knowing that they're not going to get it. Um because people want to be CESOs, right? But it's a very important question because we have seen like Joe Sullivan the consequences of getting stuff wrong. Um and and and the amount of pressure that a lot of CISOs are to do things that go against the grain of what they know they should be doing. The problem is we're reading into edge cases. So Joe will say to himself like Uber threw him under a bus, right? It's a specific case because the CEO didn't just not back him. The CEO intentionally pushed him very
fervently in front of a moving bus. So I think that's a different And Tim Brown and Soda wins again is a specific one where the SEC said we're going to make an example of the new amount of policy and governance that people write and the fact they don't really read it. So I think those are specific edge cases. But to speak to the kind of the three points that I think we're trying to get at is one is you need to make sure you have the same level of cover as your CEO and CFO. So to Chris's point, director coverage, that is a a non-negotiable. I should have the exact same insurance that the CFO does because I'm inheriting
the same level of risk legally that he is. So that's number one. Number two is that most CISOs these days I'm assuming probably Sue has their own personal liability insurance because while I trust and I'm very close and good friends with my CEO and CFO like I I want my own personal insurance because for all I know the VC is going to hang me out to dry instead of the company itself. So you protect yourself against that as well. And then I think the third is just like being clear and strategic in your decisions. So there is no way you're going to cover everything. Every company is breachable. I've been in multiple breaches, some of which were
definitely somebody's fault, right? There's negligence in anything. You can say someone was negligent because they Tim Brown's example, there's a policy statement that wasn't fully in like wasn't fully put into place across the entire org. That's not negligence. That's just like there's a there's that wall right there, right? A thousand holes. There's a limit to how many you can plug. So, it's about being clear and strategic in your documentation to show that you actually have a good program in place. Yes, there's gaps. Yes, they might go wrong on them, but you've done the right things to get to those points. You've covered yourself in the best way possible and you form and articulate a good relationship with your board, with
your leadership, and with anyone else you can in the regulator space if you can because that's also helpful if you know people there. I think it's also dependent on and I think you partially answered that it's it's dependent on where the CISO role sits and how much visibility you have at the senior leadership level and at the board level because you're right you can't address every single risk. Every part of the business has risks and issues and they can't address and they choose not to either but they're not going to get thrown under the bus and and you know in an edge case. But if you you can present as well a strong case around your program, how you're
measuring, how you're trying to help the business, what risk you've been able to mitigate, and what your program looks like as a whole. Sometimes it could be really tough, but personal liability insurance 100%. Uh I don't look good in orange. My wife agrees. So I want to make sure that, you know, we have the ability to protect our family, you know, if if something like that happens. >> Good >> questions. >> Any other questions? We Oh, there's a couple more here. While you're going over there, we should actually talk about delegation actually because although you Josh with that um it's such an important part of being a good leader. Um so yeah, >> I'll tell you it's not delegation for me
but when no one's asked the question so I'm going to answer it anyway. The most important job or skill you have as a leader is hiring. >> Everything else you can be crap at. If you're crap at hiring, you are crap as a leader. Like simply put, you need to be able to hire people who are as good if not probably better than you in most areas. Like and then defend them fiercely. Like the best leadership lessons I could give to anyone in this room wants to be leader one day is when things succeed, even if you did it, it was never you. Like it was always the team. And when it fails, even if it was
blatantly this guy, it was you, right? Fiercely defend your team. Progress them. Try and push for their pay rises, push their promotions, push them out the business to another role as a CESO. if you need to, but like make a family and care about them. Hire well and make people feel like you care about them, not because you make them feel that way, because you actually genuinely do. Like delegation's irrelevant if you've got the right people in the room. >> Yeah. And also, so on that point, don't pick the person that's on their feet most of the day running around to do more running around. Um yeah, maybe maybe some choices can be better made
and so you have to put the you know the pressure on my shoulders for pointing out the wrong person. So sorry about that. Um who had a question? Sorry. Yeah. So as a deputy now, how do you ensure that the CISO sits with the proper seauite? Right. So in my example, my CISO sits in a completely different building away from all the seauite and he's not touching kind of the important highle parts of the business as much as he probably should be. >> It's tough because I think there's he or she may have the the latitude and the ability to to still influence and try to uh I think it also depends on where they are in their career. I'm
going to kind of bounce around a little bit because I'm just kind of applying it back to my own experience. If that there's some level of imposttor syndrome, they don't want to sit next to the seauite. They don't want to be found out while they're continuing to try to level up and make sure that they can talk like they understand how the business works and what they need to do. Uh but there are times as you continue to learn, you have failures. Failures are the best way to be able to learn. As long as you can recover from them, they're not catastrophic. Um having the ability to influence in some way. But there are organizations where it's, you
know, like I I sat under an executive team member and that was as far as I could go and I got 5 to 10 minutes with the executive team. So I had to be very pragmatic and specific about what I wanted to share and then um try to be really clear and leave them with a ton of information so they can ask questions. I still had to navigate and manage through influence outside of that to be able to make sure I was getting to where I needed to get to. But when I failed is when I didn't do that. And I recognized I was sort of put in a corner and I just sort of managing through that
and I was like, "Oh well I'm in the corner. I guess I can only do what I can do." But then I start to learn outside of that of like, "No, it's that's an excuse. You have to go and build those relationships and share that information if you don't have a formal structure to be able to do that." >> Ray nailed that. Next question. Last question. We get one more in. >> So my question is organizational. So in terms of like a lot of the organizations I've worked for, security is not as autonomous as we'd like for it to be and it normally sits under some other part of the organization whether that be legal or IT engineering so forth. I'd
like to hear uh I guess your opinions as to where the ideal place for security to sit. So, I was clear at the beginning. I think security should report to a CTO. Um, I want the CTO, not the CEO, because the CTO gets my problems, understands my language, and probably wants to help me more because the CEO's got too many other things to worry about. But that said, I also wouldn't care if you reported me to anywhere. I think security's autonomy is based on the capability of the people in the security team. So, if your leader is not capable in making themselves impactful regardless of where they sit, then as a member of that team, start doing that
for him or her. Like security has its reach based on how good the people are that are there. So it doesn't really matter. I've seen them report to legal, finance, CEO, CTO, HR. I've seen them everywhere. But the end, the success is based on either the leader that's in there or the team that sits below them. >> Nailed it. Nailed it. >> Yeah. Yeah. Because I I get asked that question quite a lot. And actually I see I see people that are applying for jobs and they'll talk to me, we'll talk through it and they're like, "What's the reporting structure?" And we'll talk through it and they might be m Yeah. and and genuinely 90% of the time it's
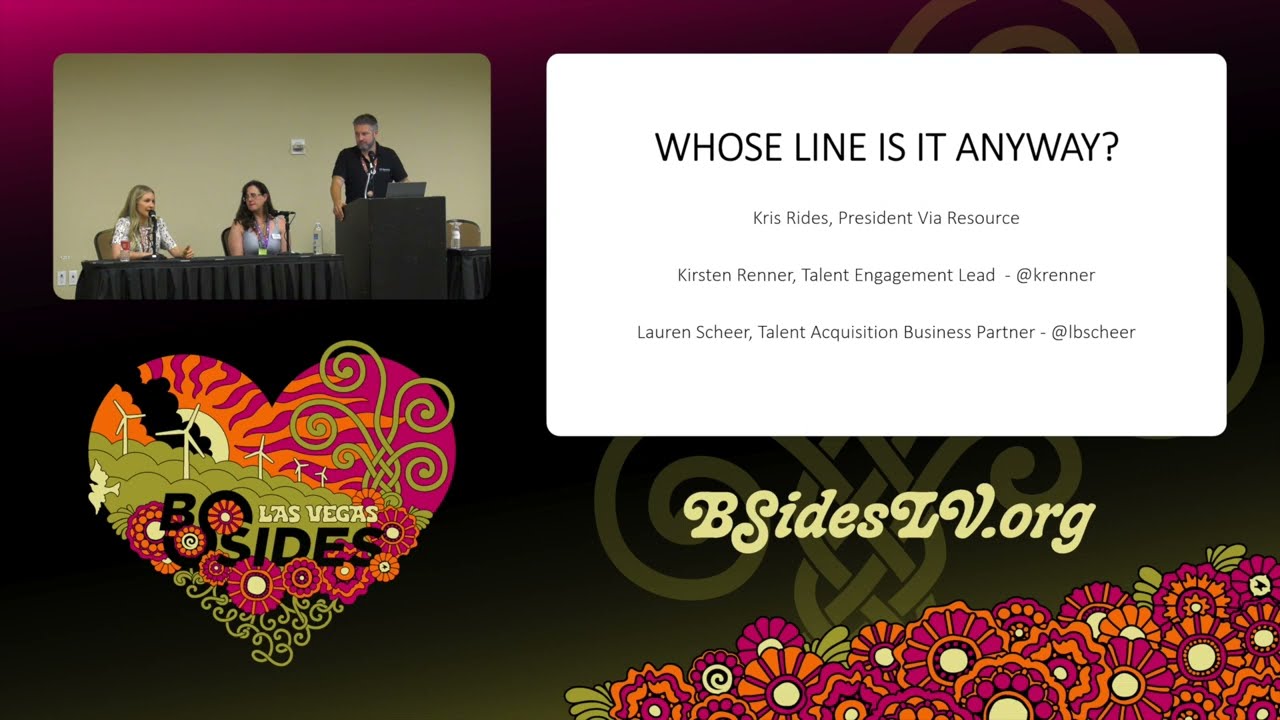
because they had one bad experience reporting into a person whatever title whichever department that just wasn't bought in um that might be there for it might be the the the person they were reporting into. So it's just who is the person and and are you good enough to to get their attention. So yeah agree. Got time for one more. What do you think? We're a bit over. Who who who is first? Okay, I'm just going to take this moment to say that the brilliant Chris will remain on the stage for our next panel. And I I love what Jake said uh two answers ago about hiring being uh a critical component in all the solutions. And the next panel is
about hiring with the perspectives of recruiters and hiring managers including Bruce Potter who just found out like five minutes ago that he's speaking. So you should not get out of your seat. >> All right. Uh my question is um you've probably heard of there's some statistic about a lot significant number of breaches are due to vendors. So how do you feel uh CISO should balance um or prioritize uh security of their products whether that's hardware software security as consulting or versus their environment for the company. Oh, I'll get on my soap box, Ray. So, I used I used to work for a TPRM vendor. Um, and I think TPRM is the most broken thing in security, like
beyond belief. Questionnaires are absolutely meaningless. Half the time I've read the answers and I know their lies cuz I know the CESO and I'm like, I know that that is not true in your company, but you've told me it is. Um, because they're a legal protection, right? They are the fact that you did your due diligence and therefore the liability belongs to them and not to me. The reality is like, and this is wishful thinking, we need to get to a point where security becomes real time and transparent and based on data. It's like until we get to a point where we're assessing vendors based on their sbombs, based on what's actually in their code,
the currency of it, the vulnerabilities that are there, if they continue to exist, what they've done to mitigate the controls or risks that they've got, until we're seeing real-time data that supports like your sock 2 posture, like the fact you've got one is irrelevant. But I can see if I can see all the data that underpins all those controls inside of your NIS framework, that's helpful. or at that point I can build real meaningful trust on that vendor and I can actually start to think about what they add to my infra and to my company not what they take away. So I I think trying to build real relationships where you get the right questions and get the
right level of data from your vendors is the best way to do it rather than asking stupid questionnaires. But I do think at the same time to your first point where you focus always focus on your own infra first because if it goes in a vendor and we talked about legal liability earlier if it goes in a vendor it's probably not you that's going to be in front of Congress lawyers or in orange. Um, I don't look good in orange either. Um, but luckily in the UK we wear gray, so it's fine. Uh, but if you don't protect your own infra, that's where you are liable for it.
>> What if our our posture to other people? Yeah, I'm honest and transparent. If I'm asking a questionnaire, I'll give you the legitimate answers. >> And it causes us problems. The sales people at times love it because it builds real meaningful relationships where they're like, it's the most honest answer I've ever had. At times it causes chaos because they're we're talking to procurement and not security people and they don't understand the answers I'm giving. Um but I I think the only way you can try and build a meaningful ecosystem broader than just my own company is by being honest and open and transparent and giving data. >> But to my point that I had mentioned
earlier, if you have the ability to measure that and we lost that opportunity because we didn't have we couldn't meet the security posture, we didn't have the controls in place, that's an opportunity to sell the need to the business on why that needs to be put in place. >> Look at that salesmanship. Boom. Thank you very much for all the great questions. Thank you, Ray, Jake, and my lovely assistants for running around. Uh we'll be around to ask a few questions, but we have got this panel next that I'm going to be on talking about recruiting. So stay for that. It's great. We do it every year. He does.