Command-Line Obfuscation: You can run, _and_ you can hide

Show transcript [en]
uh hey everyone welcome to this talk as as R just said we will be talking about command line opusc in the next 40 45 minutes or so um you may have heard of the expression you can run but you can't hide well today we will find out that sometimes you can do both uh so just briefly before we move on um who am I so yeah my name is vit that is a Dutch name I'm originally from Amsterdam uh but currently I live in London where work as a um threat detection and response engineer um I really do like cyber security I've spoken at other conferences before I'm involved in other uh open- Source projects as well for the entire
community so later on we will be talking about the L bass project as well it's one of the projects I help out with and um yeah I'm just looking forward to um sharing some of that knowledge uh that I also um got through other resources with you guys today so I was going to say let's just Dive Right In um so command line ofation right what what is that just a reminder I know some of you um have different levels of of technical detail so I thought let's start with the basics command lines so every process on your computer has a command line might not be much on it but there is always a command
line attached to any process you're run on your computer for example um say notepad I could start notepad just say notepad.exe on Windows that will simply start the program program um however sometimes it's a lot easier to just give it some extra parameters so extra context on the command line and that will allow the program to change the flow uh before the program is even properly started so I could also say notepad.exe followed by hello.txt that will tell noad when it starts to open hello.txt as file seems straightforward right um on windows are many more different ways in which command lines are used you very often will see these um command line switches with a forward
slash followed by one letter multiple lce so for example shut down SLR that tells the program shut down to not only you know stop your computer but also to restart it so yeah as I was saying initializing parameters that allow the program to change the flow now my fourth example here is an is another example where you see that a command line can contain everything right so we see here reg.exe export then we see a registry location and then we see a file path so these are all different they all different functions right um now this is the context so that's that's a command line This is how we use them um why why does this matter
in a cyber security context now if you are a threat uh Defender like myself command lines are hugely useful because they tell a bit of a story right so from threat detection point of view looking at command lines can really help you understand what an attacker might be doing or trying identify behavior that could be an attacker because if we look at these examples I Gave You by just looking at the command line right just not even understanding what the processes do but just looking at these starting commands I can tell you what these programs are doing the first one is opening notepad the second one is opening hello. dxt and notepad the third one is rebooting the computer
and that last one is exporting something from the registry so command lines tell a story and that's usually helpful if you're trying to establish what is going on and for that reason lots of antivirus and EDR software you know so the tools Defenders use um rely on command lines in order to detect possible malicious behavior today we will be talking about command line obfuscation excuse me off ation means in this context that you're trying to hide what the program is doing so in these examples that I gave you those four it's very clear what the com what the command is intended to do but as an attacker you can imagine that you don't always want
um EDR or or an analyst to understand what you're trying to achieve so masquerading the true intention of a command you're trying to run pardon me so yeah as I was saying that poses a problem because if I can change the command line in in small ways I can bypass potentially defensive measures like antivirus like EDR tools U because very often these tool rely on command lines that in itself is not bad like I said it's a great source of information if you rely on it too much or if you make the wrong assumptions it can be dangerous so in this talk I'll be talking about Windows Mac but also Linux and I will show with very small subtle
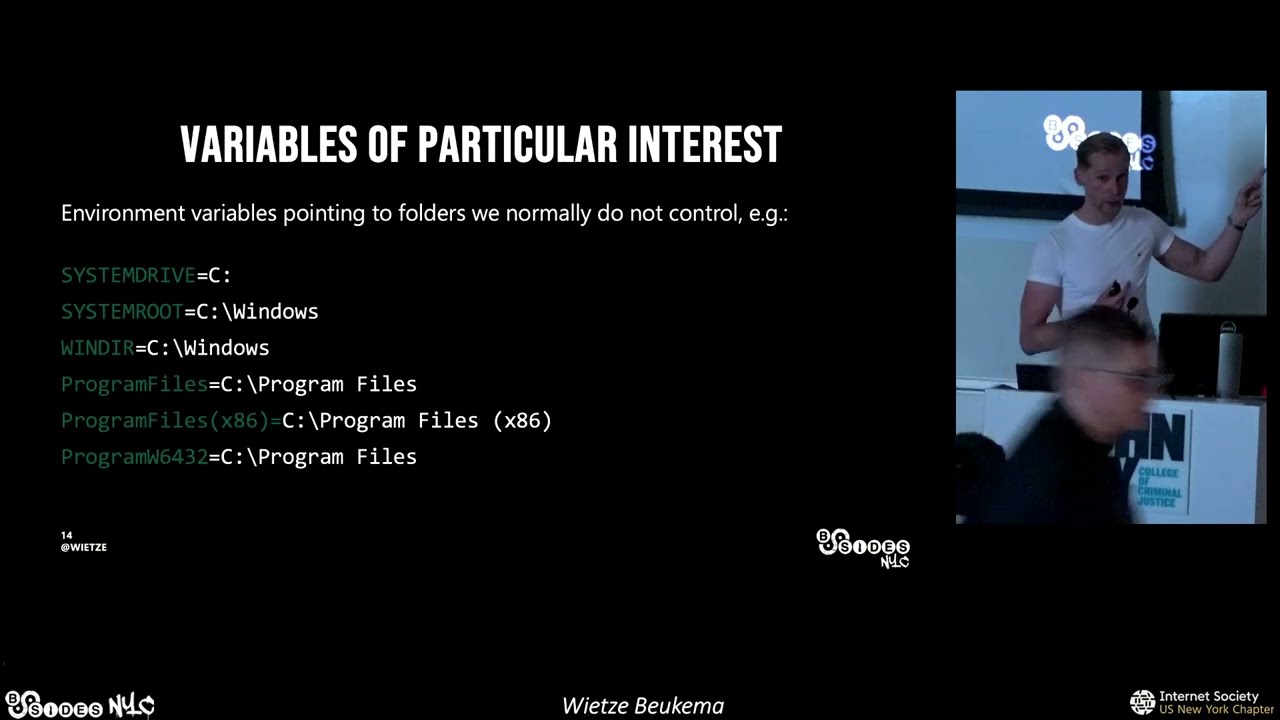
changes how you can bypass known security tools so yeah for that we're going to be looking for um command line equivalents what I mean by that is that you find a command line with um you know that you would normally run but then I'm going to change small things so that the command still works but an EDR tool might not spot it so as I was saying we will start by looking at windows and we will look at what what command lines regularly look like and then we're going to be looking at four different programs as an example of how command line officiation can be applied there so on Windows there's a number of conventions so these are not hard rules
but sort of I don't know like uh normal uh behavior of command line tools that most programs adhere by so if you use Windows this will all look very familiar to you command lines often use forward slashes um we saw that shutdown command SLR here's a couple of other ones ping sln1 CMD SLC ip config for SL all so very often you will see command lines that have forward slashes you may know that sometimes hyphens or dashes you know these These Bars are also used um more on that later Windows is also very case insensitive you you will also know this right like a file path doesn't matter if you include upper lowercase characters Windows considers it all the same and
for many command line tools that applies as well so Comer selection all uppercase lower case combination all works double quotes also often used on the command line if you have a space in your command line argument by wrapping them in double quotes the program can understand that you mean a space and it's not a um separation between individual commands again more on that later because that is actually great way to bypass security but an important Point here to make is that this these are all conventions in Windows none of this is enforced any program you write so if you write a program yourself or you use a third party tool the program itself decides on all these rules it doesn't
have to be case insensitive it's just most windows program decide to be and that means that there is a scope of us make small tweaks and that may have big consequences so e it was saying we will now be looking at four programs most of you hopefully know if you used the windows I'm just going to show you how an a techer may use it and how you with minimal changes can successfully bypass security so let's start simple with option characters um hopefully you're familiar with Powershell Powershell is Windows version of a bash or scripting environment um is used for automating tasks it has lots of deep Integrations into to the system therefore it is loved
by attackers um an example here I could run this command power shell 4 Command right host P hope I said that right hope I passed the integration test um and if you execute this in your shell it will um just give that word back on your command line um now you see that the forward slash again which is normal in Windows it turns out if you run it I hope it's not too small and too low um that works we already knew that but turns out there's a multiple option characters you can use there so you see that Powershell um hyphen command and then you see what seems to be three more hyphens right it looks like they're four
hyphens for the word command now if you look at these commands not in your shell but in task manager or in this case process monitor you will actually see these are not regular hyphens so if you look here at the the third column you see first for slash then you see a regular hyphen like a small bar but then you see a slightly wider hyphen you see a really long hyphen and then you see a weird one that's sort of at the top what's going on here turns out that Powershell accepts not only forward slash and The Hyphen but also the so-called Unicode equivalence you may know that in Unicode there's lots of different characters uh and for example
there are multiple types of hyphens or dashes so as you see here um I also put the Unicode uh codes there you see for Slash and hyphen that's normal but then you see these really high values so 2013 14 and 15 which are different types of dashes the N Dash the M Dash and a proper horizontal bar now it's not normal for a program to accept these right in Windows normally we only expect a program to accept that forward slash but by having four other options um this is actually allowing attackers to bypass very simple and naive detections because consider this detection rule through the course of this um presentation by the way I will
show you different sources of detection content um open source different vendors and I don't mean to pick on them but I just want to show you that um it's very often uh not taken into account and therefore you can bypass detections so this one is for Microsoft Defender for endpoint it's taken from this website by the way grade resource if you use Defender mpoint um but if you see here what it's looking for in this detection rule it's trying to look for encoded commands and it does so by looking for a command line containing the word hyphen encoded command or hyphen NC if you now look at the examples I just gave you right um we know that
there is four other ways in which you can invoke the same command with a forward slash with a n Das M Dash and a horizontal bar so detections like this look great and they will work in most of the cases but by simply replacing their hyphen with a forward slash you would completely bypass this detection so as an attacker making this minimal change you can already potentially um allow yourself to bypass detection mechanisms so I hope that made sense this is a very basic case but as we go we will go further and further oh thanks I do need that cheers all right so let's move on that was power now msac so um Microsoft
install or executable allows you to install software packages you may have heard of this system administrators use it a lot to install um extra software on on their um endpoint Fleet attackers also like to use it because they can inst malicious software or sometimes even legitimate software that they use for bad purposes so a normal way to invoke this program is to say Ms exec for/ package and then the name of some um tool you want to install now we already looked at the forward slashes so let's not go over that but what about other characters we've seen that that that that uh hyphen had four different equivalents right can we do the same with letters
turns out you can so if you look very closely at the screenshot here you see Ms exac slash p and then a small a and a subscript a or superscript and then regular CK again a small A and G what I'm trying to do here is install the tool any disk which is a remoting tool but as you see it accepted it so again this can be problematic if you have a detection rule looking for installations with Ms exact you may be looking for the word package but if you use this small a the command line will still work but your detection may fail so again I hope you're trying to understand what I'm trying to do here small changes um that
will detect simple naive detections now let's look at a more problematic one because this one works on a couple of um build-in tools but not all of them this one works on nearly every of them cscript again hopefully you know it is a um tool that allows you to execute FB script and jscript on Windows computers so again system administrators use it it's a bit of a legacy tool but still um malware writers love this as well because it's present on every Windows version and you can do a lot with it U one way to run it is this command so cscript SL no logo for/ for engine VB script and then uh a command uh a file
path containing your FB script in this case my FB script might just say Hello World um so look at that top one that is just the vanilla version right that works as I was alluding to earlier double quotes um are common place in Windows so um you could for example say for/ e colon FB script wrapped in double quotes that would still work what you could also do is add more double quotes in different parts of that command line so as you see here um FB SC R ipt does still work um and I could put them even if you look at the bottom one right basically every character is wrapped in double double quotes and for some reason the
output is still the output you would expect to be right if you now look in task manager or your EDR tool it actually gets passed on those double quotes so it does not live just in your command prompt this is what your EDR tool will see and again this is a big problem for detection this is another great resource again if you're new to cyber if you've not heard of this the sigma project great project there lots of Open Source detection rules and again I don't mean to pick on them because they have great content there but this is one of the detection rules they are looking for cscript execution if you look at the
very top that have a command line that contains at the very bottom for/ e colon VB script now if we looked at these different versions that I just showed you on the previous slide that that first version the original one that most people use it would detect that any of the other ones it would not detect and we know that you know this is what your EDR sees so um that means that this detection rule will be completely bypassed as was alluding to this is probably the most common type of command line officiation you can use in Windows and because nearly every program is is vulnerable to this at least of the ones that are built
in I don't know why I have such a dry tro I'm sorry cool now to make it even more complete I have a bit of a demo this is a video there's a lot going on so if you lose me at some point because it gets too complicated that's fine um towards the end I'll try and wrap it up and give some to more sort of like high level Lessons Learned what I thought I'd do is look at this specific dll um hopefully some of you here will have heard of the lbas project um it's a great open source project where it tries to list these living ofth land binaries and scripts one of them is com
svcsd so on this website you can find many tools that are available on nearly all windows versions that have some weird functionality the reason this is one of them is because this dll can U dump the contents of a process memory now what why does that matter well on Windows you have this process called Elsas it's probably the most important process on Windows because it does everything that relates to security this process contains lots of sensitive tokens sometimes even clear text credentials but also just hashes um as an attacker you often try to get contents of this process because it will help you um get further into the network right you can possibly move laterally so with this tool let me
enlarge that with this tool with this DL you can use run dll 32 which is another built-in Windows 2 you can call that dlll and then with these with a specific structure so mini dump it's the name of the um export then the process ID of the process you want to uh drop which is Elsas followed by a path here it's dump bin and then the keyword full so this is how you run it and again trust me lots of attackers do this they would use this specific command in an attempt to try to dump credentials so naturally as a threat defender or as an antivirus software you try to detect and block this now in this demo it's a video I'm
going to walk you through it um you will see that Windows Defender does prevent this to some degree but with minor changes we can actually bypass it so let's have a look I'm going to need my computer for for that so the first thing we need to do is to understand what the process ID is for elss right we just saw the structure that we need so I'm going to do that shortly and then um let's start by just executing the command as it says on the law bass website right what happens if we do that with just vanilla Windows Defender so here I found the process ID 680 and I'm going to run it um so this
is what the lawas website said right rundl com svcsd then the word mini dump then the process ID which we know is 680 then a file path which I call variant one because it's my first attempt and then the keyword full now if I run that Windows Defender tells me you can't do that that's not safe so it says access is denied so sadly you see on my left hand side no file was created now now let's try to make some small changes because there's again with the knowledge we have from the previous examples there's a few things we can do oh how am I going to move this forward let's try this um so if you use rundll you may
know that you can also use a comma instead of a space so that was my first try let's try that does that work does not work it's still blocked I even dropped a do DL bit which you can also um leave out if you use run DL 32 but sadly enough no luck now something is is uh like Windows Defender is picking up on something right it knows something about this command line that it knows it should block maybe it is um the process ID maybe it knows that L say 680 so when it sees that number it will try and block it so what we could try let's go come on so what we could try is
simply changing the number little bit and then maybe we'll have success so what I've done here I've simply added a zero at the start of that process ID and if you look at the left hand side now we have a file varant 2 a another thing you can try is adding a plus sign at the start of it and again it does work that seems weird right because the number 680 is still there we just represented it in a different way so simply adding one character already bypassed this detection so um interesting is there more we can do well let's have a look another approach uh that we could try is using ordinal this is a bit more
technical um we've seen the word mini dump right in that in that command line thanks we've seen the word mini dump in that command line now dlls often also have a um numeric representation of that function so every dll has functions you can call those we use mini dump but you can also use the numeric version so um in this case it's 24 you need to look that up this it's not straightforward but um once you figure that out instead of the word mini dump I can also use ash24 so interestingly enough now I don't need to uh pad that with a zero right if you look at the very first version um 680 still worked so I don't
know what Windows Defender is doing but clearly it wasn't just looking for the number 680 um because # 24 also worked without um the paded zero however the 24 we can also Pat so # 0024 works but also we can add the plus sign again so now we already have five memory dumps over there right so this is what we not want to see but somehow we we did work we did work it now let's look at some more options can we do the same but then with a comma this is weird these are the exact same commands I just run but in instead of a space I used a comma over there um that somehow is blocked so
Microsoft Defender is aware that this this trick exists but it's only looking for the comma version which is quite strange what I think happened is that Microsoft found a Blog where this trick was described they saw that in that blog they used a comma and they just didn't think about like oh maybe you should also look for the space because the space also works so um there we go that one is blocked it doesn't matter if we padded with zeros it doesn't matter if we padded with a plus now look at the very bottom so I've I'm not patting it with like five zeros but with like 15 what do you think is going to happen if I press play you can
see where this is going so if you if you add enough zeros at the start of that hasht 24 if I now press enter that did work so we have another file there so again don't ask me y but if you add enough zeros you can still bypass this detection so crazy now um let's look at two more
versions let's clean up so another thing you can try that's long um so we looked at commas and spaces now we know Windows loves to double quotes so what if we just leave out a space um interestingly enough if a com svcs and then don't use a space or comma but just wrap it in double quotes and make it follow with ash24 rund dl32 is clever enough to understand that those are two separate things so I'm not using a comma I'm not using a space and now the now the command line works again so that's another variant that we have so we already have seven version for seven different bypasses uh oh that's not what we
wanted this we [Music] tried this we tried oh my goodness it's going to restart every time okay um this is getting even more complicated now we reaching the end I promise you um numbers in Windows in any pro uh programming system or any operating system system numbers are represented in memory right and um for the computer science students you will know there's different ways in which you can store integers sometimes they're signed sometimes they can be small numbers sometimes they can be large numbers what I'm going to try now is an integer overflow so these exports we were talking about this hasht 24 um that number is what they call an um oh it was
a name supposed to be name for it a 16 bit integer so that means there's 16 bits of data you can put in there for that number and if you exceed that amount basically what will happen is that the number will return to zero so what I'm doing here is I make the number so big that it doesn't fit in the memory space and therefore this number 65560 in a 16bit um world that means it will just become 24 again so if you make the number large enough you get an integer overflow you can see what's going to happen now if I press play that created the nextra file so again because the detection is
looking for ash24 um it's it's it's not working but if you increase the number now even that version with a comma there was block before if you remember right there was one version that was blocked by simply creating increasing that number we still get the result that we want so again the the detection here that Microsoft is using is not very resilient now final one this trick we can also apply to that um process ID because do you remember there was one version again where the process ID was being detected now process IDs are a different type of integer they are a dword which is an unsigned uh long so that number can get really big it's almost like 5
billion so by simply adding that very large number to um our process ID which was 680 again we can create an integer overflow uh Windows Defender doesn't know what's going on and we still get our memory dump so as you've seen we've had numerous detection bypasses so this is an overview of all of them that we've seen so we've seen it blocks the obvious ones the ones that are on lbass the ones that are have been blogged about but we've seen numerous versions with small tweaks adding one or two characters or sometimes just leaving out a character did bypass Windows Defender right like the most used security tool probably because it is building so before we move on to Linux
and Mac what did this tell us right what do this teach us so um we've seen here that we had a single command that we were interested in but we found like 15 different ways of um getting that command so there are many different ways in which you can express a single command now what we've also learned is that EDR or AV Tools like Defender are not very resilient they were very focused on specific samples that they've seen but they didn't take into account that you can express commands in a different way so both as offensive security specialist as well as defensive ones look beyond the surface because by making small tweaks you can see here the
the the difference could be between dumping credentials and not dumping credentials right so that's that's a big um big reward now that's Windows bit of a mess but as we will see Linux and Apple Mac OS are not necessarily much better they just have different problems perhaps on a smaller scale so think about um command line arguments on Linux again those of you who use both windows and Linux will know there is a difference um Linux does not do command line arguments that start with a forward slash but it's very simple reason that their file system often uses that right so on Linux you will almost exclusively see hyphens um often you see these Single
Character arguments like dash s but often you also see these long form arguments so hyphen hyphen and then a word or in this case almost a sentence so long form arguments Single Character short form arguments um what's also really annoying from a detection point of view is that often you can combine these short form arguments so if you have hyphen a hyphen B hyphen c um you see that you can also um use hyphen ABC and it will have the same effect again if you're writing detections this can be really annoying uh something I I won't have time for today to talk about but what is different on Linux is that arguments are not a string but they are passed as an
array of arguments that does make a difference again I won't go into too much detail but for that reason I would say on Linux this problem of command line officiation is slightly less worrying as we will see uh there are still issues but still just as I said with Windows the problem here is that these are conventions they're not rules um there's nothing that prevents you on Linux from having a a detection tool that uses U forward slashes or um on Linux things tend to be more case sensitive right it's not a rule you can uh as a as a program writer you can just write your own interpretation uh but um typically it's not however because
programmers have their own conventions this will cause problems so let's start with the first one oh sorry so these are the three executable be talking about B 64 xxd and netcat or NC so this is a very simple one base 64 it's a tool that is found on most Linux distributions it simply allows you to encode or decode content to B 64 straightforward right so if I run this command um Echo and then this this blob and then vertical pipe base 64 D- dcode I will get the string he bides now as you already probably have noticed from the screenshot um you can also leave out letters from that-- decod Deco deck de even-- D Works
despite the short form version being just- D if you see all the results under that this all works now again you might think why does this matter right um because this probably just to help users out so you don't have do remember the word decode or if you're lazy you can just press enter and it still works again this can be problematic this is an open source detection from Splunk again um great website with lots of resources again they do great work but this is just an example where you see what they're looking for they're looking for base 64 or base 64 um hyphen D and hyphen Hy and decode so it would detect the top one it
would detect the bottom one but everything in between I hope you you agree with me will not be C by this logic so again small changes potentially big impact because we now bypass a vendor detection now you might think oh but maybe it's just B 64 and B 64 is not a particularly interesting command I agree um could still be used as we've seen there is a detection for it after all however this is very common in built-in Linux programs so this is taken from yuntu um the versions I could find on the latest um stable release W get C touch LS Ln many many more they all have something like this so on the screenshot
you see W get again a tool attackers love together with curl to download stuff and again you see the same sort of behavior where you can leave out letters command still works as you see at the bottom um but you potentially bypass detections so again that's problematic right um another example that I think think is actually worse um xxd you may not know this one it's a bit more Niche but it is like Bas 64 it allows you to decode and encode hex content so um it's just a slightly different alphabet compared to Bas 64 so the characters only go up to to f so it's 0 to 9 or a bcde e f um but what you could do for example
here of this string I could pass it to xxd I pass it two options- p and- r and what it will do is decode it and it will tell me hello bze Pristina now the answer is already in the screenshot but what do you think should happen if I run this command as hyphen P ABC hyphen R XY Z what should happen with any logical sense right um it should either break because Hy a does not exist or U pabc is not a valid command or it should somehow I don't know um give you an indication that what you're trying to do does not work however as you can see from the screenshot it does work so I can execute
X xd- Pristina D rocks and that's a valid command because as you can see it successfully decoded the thing it was trying to decode so as I was alluding I think this is the worst kind of um software implementation of command line arguments because what is happening here is that this software it reads the hyphen it reads the letter P or the letter R and then whatever follows next it just ignores it it's not interested it's not going to print an error message it just accept it um why is that problematic well first of all that means that there is basically an infinite number of command line equivalents because I can make up any sort of letter combination
command line would work and I might bypass a detection what is even worse is that potentially you can even fool an analyst some of you may be working a s or have some other defensive role um what would you think if you see a command like this xxd D print equals documents history uh read only equals true we were saying before right a command line tells a story so if you read this you may think okay it's maybe printing a document and it's only doing that as read only well this is this is all made up right because we know xxd only looks at the first two characters so as you see in the screenshot these
command lines are are the exact same it just blatantly ignores all the extra bits that I added the lesson here therefore is um xxd can be used to make decoy commands I can even try to fo an analyst into thinking this is a legit action even though I might be doing something malicious so these Wild Card style arguments are something to look out for they're they're quite bad cool finally in this Linux section um netc cap so ncat is a tool it's it's present on most Linux distribution not always but um it's often used by um developers and also by malware makers because it is a great tool for interacting with network it can make TCP
UDP connections it can receive them all sorts of things so for example I could execute this command which will um so NC is natcat it can then uh I can pass it hyphen VZ which BAS Al tells me be for Bose and reach out for Port testing then I pass an IP address in this case I said 8.8.8.8 and then a port number 53 what this does is it tests if that IP address is reachable and if the port number is open so in this case it tells me yes Port 888 sorry IP address 8888 exists Port 53 was open and I could send it atcp uh packet so great to for just doing Port knocking
for example um this command line also or this tool also takes domains so if you look at the bottom there of my screen um you can also call google.com 443 it will then work out that Google is available and Port 443 is open so far so good now let's talk about IP addresses because what is an IP address we all know what it does right it it allows you to talk to a different computer connected to the internet but why do we always write it in this form where you have three digits a DOT three digits a DOT three digits a DOT why is that again this is a convention because an IP address actually is just a number it's a
very big number but no one is going to remember a very long number right you're going to have mistakes um you're going to end up uh I don't know talking to the wrong computer so historically when ipv4 was created they came up with this dotted decimal uh notation so if you look at the top command there um that's how we normally write it right 127.0.0.1 which is Local Host that's how we know IP addresses now some programs not all of them um also accept different notations because ultimately an IP address is just a number so netcat for example also takes 1271 without the zeros weird right to me that does not look like a legit IP
address if you look at the the bottom I don't know if this is going to work no if you look at the bottom you see there the second line says connection to 1.7.1 brackets 1.7. 0.0.1 so neat worked out that whilst it wasn't a legit or not a normal IP address it worked out oh you probably meant this one um that is weird because that's not how IP addresses work if you look at that second block you see hexa decimal notation which are characters up to the letter F again um octal notation which are digits only going up to number seven and decimal notation which is just um numeric right up to the uh 0 to9 so
interesting fun fact therefore IP address 127.0.0.1 internally actually is this number 21307 06443 433 um interestingly enough cat again is willing to convert these number back to their normal IP representation again I find this very strange like how many people actually would ever use an IP address like that um yet net cat is helpful enough to actually help you do that and it get gets worse because it can take combinations as well here we see hexad decimal in normal IP notation we see octal in IP notation but then the really weird short notation um or even a combination of all of them octal decimal hexadecimal and there's a bonus there as well you can pad the port number again
with unlimited number of zeros and as you see all of these commands worked what I think is worse it actually tells you is like oh you did something stupid but I saved the day by actually turning it into a proper IP address um so again I think this is problematic because this means um if you enter things like IP addresses you can make it look like something that is more like a domain name or something that isn't even IP address like how many of you would recognize that um decimal version as that being a connection to an IP address right it looks like something completely different so again from deception this can be um really
problematic and if you have a detection with a Rex for example looking for an IP address other than the first one is not going to match with any of the other ones right so again you may bypass detections with this now I think we need to uh make some progress here because we're nearing the end of the presentation so Mac OS I think the news here for Mac OS is that it is both is UNIX based so lots of these tools have just shown behave similarly on uh Mac OS but I thought I give you one more example that's specific to Mac OS to show you that that program isn't immune either so yeah very
similar to Linux same command line um conventions but there are some specific tools with unique Behavior and once again the implementing program decides so therefore weirdness guaranteed so this is my one example oess script is a built-in tool similar to C script I suppose it allows you to execute scripts um in different languages including Apple script now I've been told on slack overflow that Apple script is one of the least like languages um poor Apple but um actually it is quite powerful you can do lots of um interactive things with your operating system such as display a message box running this command um basically allows you to run any Apple script on the command line um and here we say
display dialogue hey friends with title waving Emoji as you see that works if you look very closely though there is a difference between what I put there and what I put in the command line boom um again very small change but we used this trick on run D 32 before as well you can leave out of space by simply um instantly adding a quote after the letter of interest and again this is a screenshot taken from the sigma project once again great project but one of their detections is looking for oosa script and uh space hyphen eace and now we've seen with simply leaving out the space and immediately putting a quote we can bypass this
protection and therefore um you might miss out on some interesting Behavior boom wrap up so what did we learn because we've seen a lot right it was all over the place lots of technical stuff what did we learn from this if you're here today and you're in offensive security you must have loved this because what we've seen here is that it is absolute chaos right small changes possibly bypassing detections um especially on Windows right um you could really benefit from this so if you are doing offensive security gigs my recommendation will be is look into this because with small changes small risk you can have a really high reward so what I hope one of the take is
of today is that look beyond the surface if you have a command you like to execute um but you're worried it might get detected look for these weird anomalies that allow you to execute in anyway command lines are much more flexible than you think as we've seen from that example of the lbass project if you copy paste it it was blocked but just the small differences um can really uh enable you to to do it what I would say however be very careful not to overdo it so um you remember these weird little A's we've seen at the start if you add too many of them then the command LEL would just look weird so that in itself might stand
out it might get detected because you apply too much alisation so um be careful same with the double quotes that the final one I showed you right had like 50 double quotes in it that in itself is likely do get caught so um don't overdo it it's my tip um then the final one Defenders if you're a Defender like me um please don't cry because it's it's not as worse as it seems and not as bad as it seems um what it should be your takeaway of today though command lines should not be relied on what do I mean by that um by all means keep writing the detections for command Lin because as we've seen it does pay
off lots of attackers don't bother changing them what we do see though is that if you don't write them carefully like the people from Microsoft um you can be bypassed it is also really hard in their defense to account for all the different options because these tools by their very nature are just super flexible so what I would recommend right don't overly rely on command lines but try to find detections that um work on other events so that um look look at that example I gave from netcat right where we were looking for IP addresses rather than looking for IP addresses on the command line what's a much better approach is look for Network events
Network events after all um they don't it doesn't matter what notation you use they will always have the same notation in your EDR so if you can write the Texs on file level Network level DNS level honestly it is much more reliable than trusting command line arguments so look for the underlying Behavior rather than the command line but finally again sometimes you just you can't right you have to rely on the command line in order to write detection so my tip would be focus on resilient detection have a think even if you're not sure um do I really need to hardcode that hyphen or forward slash in my detection maybe just leave it out it
probably won't hurt your detection it won't get more noisy but you would catch um possible obfuscation attempt but yeah assume that it might be bypassed and hopefully there is other ways in which you can detect uh the offending Behavior now finally before I wrap up um thank you for listening first of all secondly wouldn't it be great if there was like a single resource because we talked about all these different examples right I gave you all sorts of anecdotes different platforms different uh binaries how as a Defender are you supposed to know which one can be bypassed with which trick wouldn't it be grade if there was one platform later this year I hope to
launch an open source project that documents all these weird anomalies so if You' like to um stay informed on that give me a follow on Twitter if you're not on Twitter I'm also on LinkedIn so um I hope that really helped thank you for listening and uh if there's any questions ask away thanks so much that was so nice guys any question yeah
thank you very much so I have a question regarding like detec news cases so what do you recommend because for example usage of netcat it's red flag what do you think user Bas user behaviors would this cover this those kind of attacks or can you give us more a concrete example how can we defend against those type of attacks sorry so so understand your question so you say the ne cat example right so you said like what for example n for example if I have user Behavior analytics or something similar would affect this or can we protect or detect those activities well that's an interesting question right user Behavior so you could look at for example um anomaly
Behavior which again would not depend on the command line if a user suddenly starts using netcat and never used it before already be interesting right or if you look at frequency behavior of what command line options are used right maybe you will see that lots of your users uh connect to Local Host and 12701 but maybe not that many go to this weird you know uh decimal representation so again that's a clever way of actually bypassing this issue it's by looking for anomalies instead so you just rank them according to popularity or you rank them according to I don't know how long the command line is how many different characters are on there those are also
clever ways in which you might actually detect anomalous Behavior which could lead to finding malicious behavior so yeah you're right I think looking at behavior and things that stand out anomalies that's that's a key approach to actually making sure you do detect stuff like this also maybe I can share my personal experience we have kind of same problem we are using risk based alerting and it means that every time you use one of those binaries that you shown us it will be a RIS ore assigned to that user so if you you misuse it I don't know net five times it reaches threshold and you will automatically have alert so exactly don't overdo it because you get precisely no that's
that's good advice and it's it's also difficult right because depending on where you work I work for a company where we have lots of developers right sometimes they will just execute net cat a 100 times in a single minute right it does happen it's users are weird but that's why it's still interesting to look at the behavior right you could still see a spike and it could still end up being legitimate but by making sure you do detect it so you at least get an alert you can investigate it and depending on as you said risk score sometimes you can say a person works in the development department it's a lower risk score but if it is a receptionist
to get a higher risk score right so taking all these factors into account is also key in making sure you detect things as early on as possible so yeah thank you any other question V is it defense getting better or like these vendors like Windows you said macw yeah is an also a good question I think on the whole yes they are getting better so I think um again when research get published Defenders are very quick to actually add detections um this specific topic I was talking about today it remains a difficult problem because often we don't know about these weird quirks so um I think on the all they do get better I think there's a lot more
more attention for these sort of Tricks living of the land executables probably had their popularity 10 years ago when it became really popular they're still one of the most used tools if you read any vendor report on the threat landscape they will always tell you executables like I've shown you today that is what attch is use most of the time not the fancy malware not the complicated binaries that you need to reverse engineer it's simple tools like this so does it get better yes um what I would say though I would really encourage my Microsoft do stop some of these um weird functionalities in these built-in tools because that's making our lives as Defenders harder right some of this
functionality should not be there in the first place but because it's already present on your operating system it's really easy for malware um or attackers to actually abuse that and uh with minimal footprint still execute their target so um does it get better yes um but there's still a lot of ground to gain from a defensive point of view okay and I know is that some of the commands you need to have like a elevated privileges right correct yep y so some so for example we did the memory dumping right you do need certain admin privileges the system one because it's a protective process in more modern versions of Windows if you use kernel isolation as well you might not even be
able to touch it as all at all but that doesn't stop uh attackers from trying right so but simply by just detecting it might again prevent you from worse things to happen but yeah it is important to bear in mind all all these tools right they they assume post exploitation most commands work as user some of them require admin but again depending on how your organization is set up it might not be too difficult to get to admin right once you're in there's always ways to to elevate your privileges that's again something you need to assume if an attacker is in assume that somehow at some point will get to admin so as a security boundary
that's also important to to be mind thank you so much that was great [Applause] [Music]