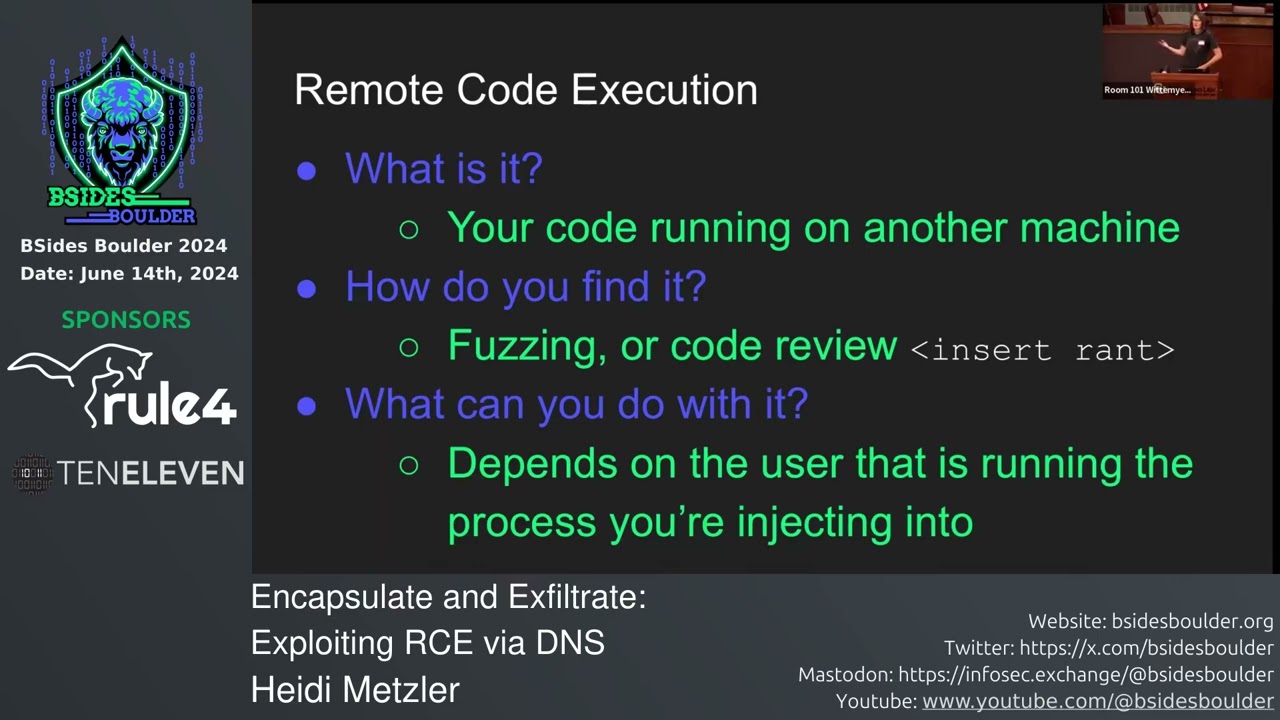
GraphQL Security: Penetration Testing and Automated Vulnerability Detection
Show transcript [en]
foreign
[Music]
or just someone who likes to hack craft too so um this is me this is some stuff I've done I'm the oswe certified um you know I've been doing I've been professionally in security for five years and like all of us doing it for a lot longer than that um and before that before I got into a professionally I did about 16 years of software development so that's that's my background that's how it got into apps specifically okay so just so I know who I'm talking to who has heard of graphql most people uh who uses burp screen it's about the same people actually um okay has anybody actually tried to pen test graphql horrible was it horribly you're gonna
love this time um okay who's fantastic graphql with Burke has anybody tried that yeah it sucks um it did so okay here we go ready uh this is this is what's gonna go on we're going to talk we're gonna do the intro to do that I'm going to explain to you what graphql is then we'll get into how to break it um then we'll talk about what tools are currently available and uh what's out there what Bert currently does and we'll talk about how I fix that and then I'll show you how it works and you can download it and ask me questions so uh what even like is graphql graphql they call it a query language
for your API so let's go straight from the basics if you are in the stock you probably know what a rest API is that's like when you make a request with a put or a post or a git or a delete method uh to some path and then in the body of your HTTP request you'll have some um some request data some input right it'll be the post format or it'll be in Json format whatever it is the body is what's important here at graphql so graphql is a specific format in the body of the request and if you take a look here the top one in the request so I need to make it bigger you guys can
see it's pretty small remember so you see it almost looks like Json almost but the properties don't have double quotation marks um not everything there's no colon after the properties not all properties have value so it is its own kind of format but just a demystic by graphql that's uh when you're making the request from the front end that's all it is it replaces the rest API and I'll talk a bit about how that happens but it's just a different body format and instead of sending it to a particular uh rest API endpoint like forward slash user slash data or something right you just send it to forward slash graphql all graphql requests go to the forward slash graphql
endpoint and every this is why people are adopting it is because everything exists in that query so you don't need a specific rest API for your users sorry you don't need a specific endpoint for your users you don't need a specific API API for your hero um you can have one API endpoint and you send the query to it and it will tell the back end what it's looking for that's what if they say it's like a quarter language it's like it's like SQL sort of but for your backend instead of for a database um then on the server side it's not magic you know there's some stuff you put in some libraries and stuff that
understands how to parse this out um and then you have just like you would in a rest API you have these they call them resolver functions which is where you get the request with all the parse data and then um the library will parse you like it's looking for this kind of thing and it has this kind of input and then you can just reply back hello or you can like go you can in your back end go uh oh they're looking for hit Heroes and they're looking for the name and the height so I'm gonna go do a SQL query or whatever pull that data back and then send back the response in Json the
response is in Json um so this is why people use it it reduces your API calls to basically just uh you have the things you can do a lot of nesting so you can make a bunch of what would be five rest API calls now is just one and you can have just one endpoint every time you want to add a new functionality you don't have to create a new endpoint and make sure all your authentication authorization is working on it all that kind of stuff here you've got some like middleware that manages authentication authorization and then it passes on the request to the parts of the query language parser and then you might do
some further authorization there like maybe I'm not allowed to see Heroes maybe I'm only allowed to see losers um so okay so he uh so let's talk about uh it's vulnerable right it's basically a rest API with a different body form so the magic that the library does is kind of opaque does it doesn't matter because it has the same vulnerabilities as what a rest API it still takes input and it's still vulnerable to a developer for getting to check to validate and make sure that you know you shouldn't have such and such character of the input um it also comes with some bonus denial service vulnerabilities which is nice we the tool that I built doesn't really
uh get into those but they're just analysis and there's actually other plugins uh that will do that for you but just quickly uh the university you can Nest so I could say like hero and then underneath hero maybe every Hero has a friend so I might do friend underneath that and then I have to ask for the name and height of the friend and then that friend will have a friend and that friend will have a friend and you can infinitely Nest these queries and if you do if you Nest them like 300D or 3 000 people um the the parser will spend a lot of time working on so that's one forms analysis they call
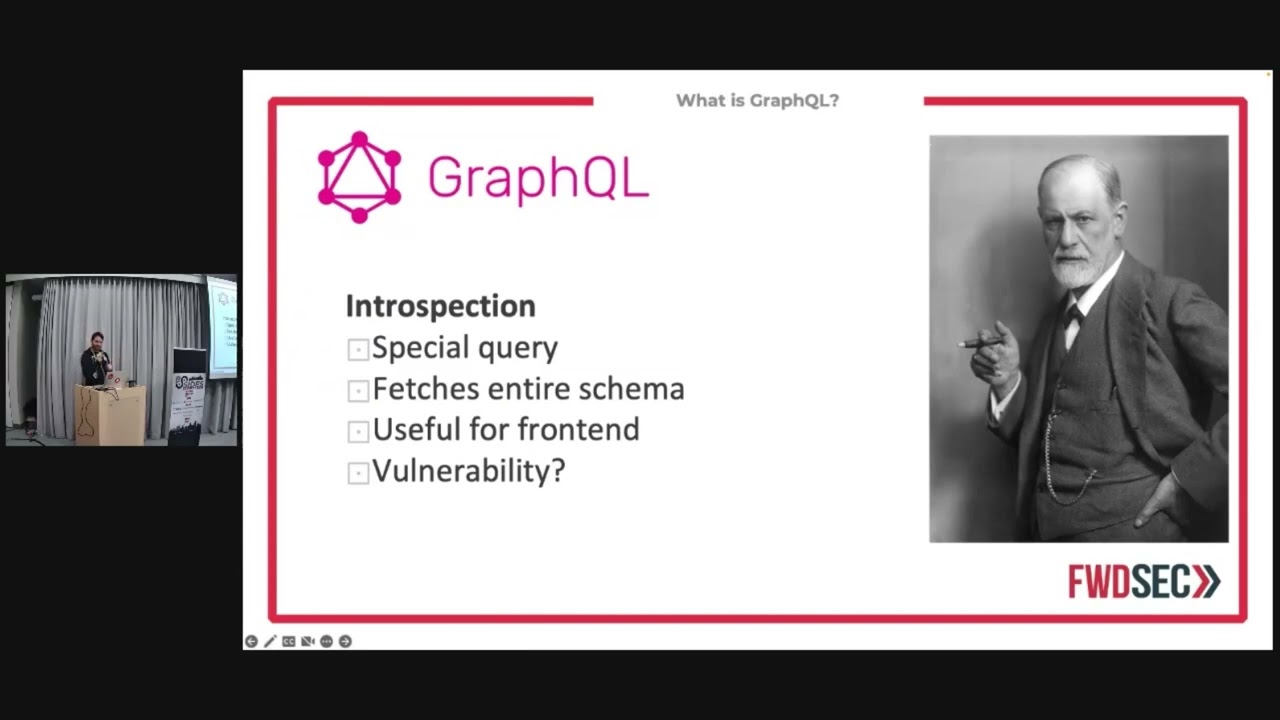
that deep nesting nowadays the thing is that it's not as interesting because a lot of libraries the default is five nests deep like you know you have to misconfigure it to allow a lot more than that for that to be an issue there's also cyclical references which are harder to catch um and also can be a vulnerability for to have a service but not as interesting right we're not trying to tie up the server at least I'm not I'm trying to get the heroes you know debit card or whatever so uh the other nice thing is that itself documents it's really cool so there's this there's this special query that you can make uh this one here
recording for the hero and we're asking for the name and the hype but there's also this special query called in introspection query where you ask for everything that's available on the website everything that the API offers and it uh I think my next slide might actually do this but anyways it pulls in everything and you can it's it's useful like it's it's in it's intentionally there um I feel like this will be I don't want to jump around okay so um I will talk about this more but anyways uh so in your back end you kind of like Define a schema which is again why they call it query language so I don't want to get into the nuts and
bolts of the server just trust me if you looked up the documentation it wouldn't sound so mystical you just you build a schema which is like you said you have your models and then you map to database whatever anyways not important the important thing is that that exists on the server and we want to know about it and you can make this special schema request and it just sends you everything it's great now is that a vulnerability that's a question to be to be asked um some people have turned it off but it's useful because the front end the whole point of graphql is to allow your front end to make any kind request it
wants um it makes development a lot easier right uh makes development a lot easier introspection yeah some people turn it off if that's the case if you're developing so if you're I'm assuming your white hat and you're working on this because you've been asked to if the introspection is turned off which it might be for the reasons uh there's also you could just download the schema file and put into the API into the plugin it'll do the exact same thing what will it do I'll get into that baby tax it okay uh so oh okay this goes into further detail so how does it work in your application code you import the graphql library we
talk about that there's a bunch of them there's Apollos where the popular one I don't uh make money from Apollo just because someone I can remember right now but anyways uh then you define your schema you define the resolvers the resolvers again those are the functions that like when you get the request you see what the request is made of and you that's where your code goes and you say oh they've requested these things this is how I'm going to fetch that data and this is how I'm going to return it uh and then there's also three request types that you need to know about in graphql there's the query that's like your yep request there's the mutation by
the way these all happen through post requests because we're not using rest apis we're using graphql so you have to actually Define and say this is a query which is where you get data you can also do a mutation you can also do a mutation where it's like a post request where you actually you you it changes uh something in the back end and then there's a subscription we'll get too much into this but this is sort of like you can subscribe to like a websocket type of thing um but uh still hackable but it's just not as interesting because it's kind of the same uh so yeah this is Sigma 40 is the master of introspection
what is it special Point wow I really got ahead of myself here um it fetches the entire query sorry it fetches the entire schema um is it vulnerability that's previous time I think it's useful I can understand why people might think it's a vulnerability um because it allows a hacker to see everything that's there but if you're using if you're properly authenticating and properly authorizing your request then it shouldn't matter what they can see right it's security by security if you turn it off um but here's the thing right we want to use birth I like using burp burp has this great tool called the active scan and for those of you don't know the
active scanner it's only available in a pro virtually Pro um so you give it a URL or you go in the proxy you can click around and people will start swallowing up all those URLs and it will find all the insertion points it'll find injection points where input might go where the back end might do something with that data and it'll start fuzzing it'll start adding payloads right it'll add cross-site scripting a SQL injection and all this kind of stuff it's also it doesn't just send them it's also this kind of cool Smart Tool where actually can look at the response and go oh this looks successful and if it's for instance something it'll do for SQL
injections it'll sound like a single uh a single Pro yeah one single quote let's just say a single single chord and you'll see in the response you get some SQL error and it won't just go oh yeah we've got SQL injection now it'll it's smart enough to go let's make a second request and do two single quotes and if the error disappears we probably have a SQL objection and then it'll try even further right so the active scanner is wicked it saves us a ton of time and burp loves rest apis it knows how to speak the language of rest apis right it eats that for breakfast um but the thing is it doesn't understand
graphql when you try to give the graphql you'll see I'll show you later why that's the case but it really actually you know I think it might be too I don't know yeah okay man I really I did a good job of doing these slots okay so let's talk about safe injection sites these are places where you want to put your payloads um so in the previous example where were we supposed to put it they were just properties right yeah you could try putting you could try fuzzing the properties but you're just going to get graphql errors uh by the way side little uh vulnerability but similar introspection if you mistype if I have human if I do humor or something like
that um the response will go did you mean human so that you can fuzz that way and find properties it but anyhow as you see now we now have input right um human and we want we want humans but we only want the one with the ID of one thousand so that's our input we also have the second input the units of the foot the thing is that foot is an enum as you can you can probably tell it's it's a constant right it's it's all capitalized it matched it probably to some integer in the back so it's not going to be great for buzzing um the string on the other hand great Professor that's because uh this is
probably going to some like you know uh dynamically type language or something like that and we get to play around with all sorts of things so um we can do things like uh take our old payloads and put them in a new location so this is where you put your payload you put it in um where the 1000 is okay like we could end the talk here because this is now how you write graphed you out um the thing is that um this is what a graphql query looks like so I've been showing you the beautified version of it but when you actually send it this is Imagine on the bottom of this actual request this is
all one line This is why it's not too much so yeah so uh you look there's there's all this like white space stuff new lines new tabs um and it's all in one life first so it is a Json object and we have the query and the query is a type query and then inside we have all this so it's it's it's it's dirty looking but if you can imagine because this is a Json object looks at this and goes oh yeah I see a property I see a value so um Robert's like yeah yeah I got this we're just going to inject it like this right you put it at the end of the value
right that's where my injection Point goes if I want to test for SQL injection I'm going to put some string and then at the end of that string at the end of the value I'm going to put my single taken in my test um but for it's not a graphql Works um so what we want it to do is get it to work that's what I feel like it moving kind of fast here um so this is what I wanted to do I wanted to make a burp extension because I love the active scanner it does all that extension on it um I wanted to use introspection to pull down the schema take that schema and
then write some code to turn that into every single possible request we can make and then send that to the active Scanner with the correct insertion points so there are plugins that will do the introspection query and there's even there's one called inql which is wicked I'm actually using a bit of their code to do this um and uh it's okay it's a patching list so we're going to what we do is we take each respection and we convert it into all the possible requests that's what the ql does right but they don't then find insertion points there's another plugin called brachial Raider which well on a single request show you the insertion points but yeah it doesn't do
introspection it doesn't convert it back into the possible request and you can only send one request at a time to the active scanner I want a one-click solution please it seems obvious in my brand how is this not happen already I point burp at a URL I hit go I might need to add I've got there's a space to have custom headers if you need like authorization but if not URL hit go boom downloads everything sends it to active scanner and you go get coffee and come back and write a report this is what the result ends up looking like um so this is not the plugin this is the result of the active scanner where's my
cursor there okay nope I saw it for a second for those of you following along at home I'm like parallel to the screen okay so um this year is showing that we've got an active audit going on extension driven this is the extension of the building um so it's currently doing a scan and on the right side we see all the um all the issues that it's been on oopsies and on the bottom uh we see that it has successfully injected into the right place hold for Applause
okay so um let me introduce to you Auto gql give it a URL optionally customize headers click get out okay it's going to run the instruction query this is in the background it's going to run the introspection query it's going to determinative possible request it's going to find all little spaces where we should be injecting ship and then it's going to take that and send it all the way out to Canada um it it will actually before it sends it it'll give you the option to deselect stuff some stuff I'll get it right so I'm going to show you how that works uh let me pull I'm cursor back on this screen uh
starting verb okay so let me pull this over and now this is going to be a bit of a task here let's do this one so I'm running this right now I've got um this application called The Dan vulnerable has anybody heard the damn vulnerable web application it's this thing on graphql I'm sorry assisting on GitHub it's a vulnerable application that you can use to test your tools or just if you want to play around it's kind of like a lot this is someone made a graphql version of it so that's what I'm using to test um so uh here is my plugin Auto gql so we'll go over to this tab we're going to put
in the URL for um that tool for that oh let me show you what that looks like before I can do this uh
I just want to give you guys all the context in the world so it's as easy to understand as possible um damn vulnerable so you see it's kind of like a paste bin they made like a fake paste bin website and it's all just uses graphql um so you can have private Pace public place create them import them upload them all sorts of cool stuff and behind here in the back end it's vulnerable to injection attacks so um I'm gonna put in the URL for that which is um 5013 and usually the endpoint is forward slash graphql isn't always you can look it up for most websites or just browse the website and look in the network
inspector and see what endpoints using but normally it's forward slash graphql so um I would add any custom headers here authorization editors if I need it I don't so I'm going to hit fetch scan will take about two or three seconds okay so now we have every single possible request that we can make to this side it shows all the different query types so let me expand it yeah one thing I got to do is work button UI to uh size everything properly but uh so we've got these check boxes to know which ones we want to send to the active scanner some of them are deselected that's they don't take any input so they're not
interested to us we might want to send them to graphql so sorry we might want to send it to active scanner because it'll still test uh the header values and things like that but it's going to do those on the other ones as well so you know save yourself the time the more of these would select the longer your action scan is going to run for you um so it's pre-selected those that have inputs on the far right column you can see how many insertion points there are um and if I pick one here let's see can somebody read that out to me I can't actually see what this is read and burn so read and burn if you
look wherever it says code star that's our insertion point that means it's phenomenon insertion another thing I want to add to this is just like actual visual highlighting but that one is unchecked that one's oh sorry thank you very much this one what's this one system oh this is a this is the beauty this one was the source of a lot of good stuff look at the uh I don't know if you guys can see but look at the uh the parameter name what's the parameter name CMD right yeah that was this one was a beauty so um okay so what I'm going to do is I'm going to hit run scan and uh another thing I need to do is kind of
add like an indication that it started working but it started working and if I head over to the dashboard foreign too but here we just see here so this this wasn't here before in this last one um all the results on the right side these were found before it does usually take about for this small application it took about a half hour to find all this stuff a less Community injection SQL injection across the scripting um I mean this is an intentionally vulnerable app you're not always going to find stuff like this right but um depending on the size of the application uh I would just let it run until it exhausts its payloads uh on a really big
app that can take a day sometimes running it overnight on a small application it took only half an hour um and well to be fair I'm also running on localhost so a little faster than normal but um but that being said it's also running the docker so and this is a 2015 Macbook so maybe even slower but if we go to audit items what this is going to show us so now we're looking by the way this is the user interface for the active scan so we're looking at when you start an active scan you get this box um that's what it means that's that's what so this this area extension driven um
that's the tool that we look for that does all the automatic payload and checking response checking out so as you can see it's making thousands of requests already we just started it the audit items are all the items that we've sent to um so these are the individual requests that we send to it it's going to take each of those and go to the injection point and start hammering it and finding looking at the responses and um making sure that you know checking whether or not there's a vulnerability then I think we can actually look at yeah here we can actually see just the request that it's making I'll pick a random one here um I'm still on camera here so I can
okay so here it has injected search keyword uh a bunch of weird yeah I think you're right you see realization it's running the search query and the keyword is used is it's used one of these um randomized tokens at first use it so that I can find it in the response and then yeah it's um it's using object class which is yeah for testing for deserialization uh green yeah creating objects in the packet so this is the network um that was I mean for the most part that's the demo we just now let this run and then what ends up happening is you uh while it's going or when it's done you can look over here and see all the
results so um an exclamation mark a red explanation mark means it down something of high criticality and uh it's a certain other uh Bert will tell you if it's certain or if it's you know undetermined or a firm Which is less concerned um that's because it you know it runs it runs extra tests once it finds something it'll run extra tests and verify whether or not it really is the problem I think it thinks it is and in this case the problems where price command injection this one is something about uh going over the network if I recall correctly it's uh yeah identify code objection that's actually a new one um but anyway so if I click on one of
these let's look at what's command injections is that what this is I can't see all right so it gives you purpose grid it gives you a little example as to why this is I mean a little description as to why this is a problem uh we can look at the request that it sent and highlighted in red is the payload and then in the response is it an echo what is it okay so that means that it sends a dentist lookup and then burp pro has this other feature called the collaborator where it's kind of like spins up I don't know if you've heard of canary tokens it kind of spins up like a server at a particular IP address and
then does sends an nslookup as a payload with the IP address to this machine and if this machine gets pinged then there's a high chance that you know it's found something so that's that's how it checked it here there's other cases where it uses Echo and then it just use the response more spots yeah this would be an ssrf and uh but it's an rce so at that point it's whatever you want um so the response here this I think is the content like the collaborator hosts like a little HTML server so I think it is and then the collaborator evidence says like yeah this collaborator was it was it has been pumped um and then it follows up with some
extra job elements but anyways that's the tool of action it's running in the background as we speak that's all there is to it uh as you said I just put in the URL fetched it picked the ones I wanted ran into the scan uh Negan you may want to add like authorization bear token headers or whatever maybe a real browser user agent if you need that but um that's it it works okay let's get back to the uh I want to talk I'm going to get a little bit more in depth about it um so we talked about this oh yeah okay so again enter the URL my headers fetch query it does these three things frenzy and
suspection query builds a requests Parks insertion points I learned animation on PowerPoint on the planet right here and it has the request listed listed on the left you can view an example on the bottom and then you hit the golden button click run scan and you know about your envelope in uh we get to say duplicate that stuff um so here were our goals again I want to make a verb extension I wanted to find a possible Quest I wanted to leverage active skin and I successfully did all those things and it's available on my GitHub and actually um this link will still work but I moved it to our company's GitHub which is just
fwdc don't worry about it this is um so just this is my estimation before the Q a let me do a little PC so just before that um it's graphql it has the same vulnerabilities as rest apis it's going to be lack of input validation just like you have in everything so it's not magic this thing isn't Magic it just makes it so that verb can scan it can the same way it automates rest API scanning where you can just click around and then walk away didn't know how to do that with graphql and you have to click around uh unless you had like a Swagger definition um so this is sort of akin to that where
you sort of download the Swagger file equipment which is introspection and then just tell it to go to town um so it will automate your vulnerability and hunting it does the insertion points yeah yeah and go get it there um and it'll save you lots of money uh so ask me questions now once yeah but so you can definitely follow the requests that's um you can think so I can go into for going to the active scan and do the configuration
thank you that's a great question I think I know if if I don't answer your question then then yes so let's go to um let's go back to the query damn cursor how far am i there we are okay so this is another reason let's give me an example the audience weblog without creating a course we cannot touching Elite folks yeah let me give you an example what if we have a pace bin and we want to make sure that we create a pace before we delete a paste doesn't make sense to delete paste if it doesn't exist we can't test that endpoint how about if I want to test whether or not I can access somebody else's Pace well we
can't do that if there are no pastes in there or there's no there's only one user so this is another reason why it's useful to have the check boxes so it's not just for I mean it'll automatically select the ones that have insertion points that are yeah that happens but for instance one of these I can't see it but I know that one of them is like delete all pastes right I would probably deselect that on my first run I would maybe just select all the creation ones on my first run hit go once it's done then I might select the other ones and do it sequentially that way to make it smart enough to know that
delete should come second I could do it with some word matching I could be like look for delete remove clear or something like that do those last but uh but it's not going to work in all cases
yeah of course and then we can see who consumes a post and then we can reorder the infer the relationship if uh if the response we get gives us enough information we could but I think at this point it would mean a human eye to be able to do that um yeah but actually in my wait till you see the reading on my GitHub you guys are gonna love it it's I even go into some recommendations about that and I say like remove the delete ones first uh yeah any other questions yes direct exposure yeah uh yeah yeah so the question is um will the European for the people at home so the um the question is will it
be able to find like information disclosure vulner votes so the yeah it um the birth active scanner does all that kind of stuff um it will add payloads I need to look at the results and it'll even send I think it even will just send regular requests to begin with and look to see like oh does this response have a password field does it have a server header all that stuff is actually built into the active scanner um and all that will happen automatic what's that we can use authorize
so for Access Control issues yeah that's a good question um I don't know that I don't know that there's specifically a payload for that in active scan uh what I would do is is what this guy's saying um is uh I would use autorize which is another plugin um okay what's cool is that it doesn't rely on doesn't rely on needing to find injection points insertion points the way it works is it's a whole separate plug-in um that I'm not responsible for but I'll just give you a little certain rundown which is um you log into the site you get the headers that you need or the cookies that you need and you stick those into
authorize and then you log out or you log into a different user with different Privileges and you turn authorize on you start browsing around the site and authorize will browse the site at the same time as you using the other cookie so that way you get like and it'll do like unauthenticated uh your cookie and then you know the lower privilege camp that you're now clicking through it and it'll tell you like if it was able to access things through all three or just two of them are just wondering um so that that's how I would check for Access Control using parts authorize it's like authorized but without the age
um
foreign
user can get to 200 from you cooking um yeah
I was having a back and forth with my computer yeah so what is this situation about that okay so ideally the ideal situation for turning on or off introspection my opinion if you know it's not a standard but my opinion is that you should leave it on um and that you should do your authorization properly on the back end because by hiding it it's just security through obscurity right you're just saying these it's less hackable because people can't find a documentation for it essentially right but then all it takes is for one person who hasn't been privileged to click around and I don't know write a little blog post about it and talk about all the different
functions they were able to use and then that gets out of the open and you know then then what like you may as well just turn it on all right yeah I mean I would hide in Min functions sorry I understand what I mean is I understand the I understand the desire to hide immune functionality but um if your authorization checks are in properly it doesn't matter it shouldn't matter does that make sense yeah so I I personally I would leave it on there may be some rare circumstances where it would be vulnerability to expose within schema but then my other opinion about that has been you've done your scheme around does that make sense yeah yeah
please if you're the one I'm asking questions so ask as many as you want your mind you're my number one fan right now so the authorization authentication setting is gone properly yeah because I was trying to create that instead of a way to bypass authorization yes it's really dependent on that application and what I mean is let me be really clear about what I meant so I'm going to go back to the slide here uh let's go to this one I want the one that had input is it not changing all right I'll flip it over and say um okay back back so um let me give an example so here we're asking for the human of our d1000
now maybe only people within the group one thousand to two thousand are allowed to view is user guys um so in the back end I need to be doing that test um okay they've requested ID 1000 I'm going to look at your your token uh your session token and I'm going to use that to determine whether or not you have privileged accents right um and whether or not you can break that is completely dependent upon the developers who made it some of them will make mistakes some of them will will you know mistakes they'll either do it they'll they'll do it improperably using the knowledge that they know or they've gleaned some some bad knowledge
somewhere and they do it so that is there's no like special way to bring authorization that's kind of our job in a way is to find the problems that the developers leave behind uh so there's no gold unfortunately there's no golden ticket to do there's no like one key one key for all goals does that answer your question if you like it yeah yeah yeah yeah yeah so I would leave introspection turned on personally and um then just make sure that you've got really good authorization checks in here and you're using a strong session token yeah uh any other questions I know that coming in here a lot of you didn't even know graphql was so I know some of you
are like oh I'll just look this up later but you got me here right now uh does this you know um any other also you can ask me questions afterwards yeah okay number one fan so uh I think well I was trying to go and try the extension yeah
yeah so I was trying to send my request to repeater and to modify that
specific to me or some or something it sounds probably like it is specific to that application it's probably it's probably application specific so they have somewhere in the back and they've decided that to make this kind of request or to request these items from the schema you need to have this role or whatever that your session token probably doesn't contain that role I'm just guessing but that sounds like that's that was the issue I can see more questions [Music] also we can we can talk after this yeah yeah um anybody who didn't know what graphql was before do you kind of get what it is now heading out here okay cool um let me demystify it before you after
this talk feel free to answer ask me any questions yeah actually I've got lots of time but I don't want to yeah I don't know if you can use also subscriptions okay um subscriptions look like regular queries actually I think there might be an example of one
the Quarry type yeah there's one subscription audits so let me see if I can uh very carefully okay so um if you look at the the query and actually okay so this this little tab here doing this upside down this tab here is part of graphql rated um maybe I should build something like this too easy just have it in my app but it's graphql reader that it takes the that like stupid looking Json with all the white uh space characters in it and turns it into what the back end you'll see as the word um so if you look it looks like a regular quarter mutation right except it starts with the word subscription
um and so just like that it takes input so it's it's fuzzable in the same way as all the other ones the only thing that's special about it is that um it's the purpose of a subscription it's not always used that's why I didn't get into it too much but the purposes of a subscription is to have like uh if you want to have like like a chat a chat bot on your website anything that uses websockets where you want to um uh yeah where you want to have some real-time interaction you subscribe to a model um and you give it some input to say you know like here where what is this paste oh we're subscribing to face
uh okay I actually don't know what this does on the dvga I'm a damn vulnerable applications but it looks like um yes when a paste is made you get notified about it I don't know um but imagine a chatbot it would work it was basically saying like I want to subscribe to a chatbot you send that request you send the subscription request and then it like initiates a website and I believe the websockets policy is graphql um but I haven't dug into that too much I think it also depends on how you set it up um any other questions no yes okay you guys been great thank you [Applause]