Encapsulate and Exfiltrate: Exploiting RCE via DNS
Show original YouTube description
Show transcript [en]
started again uh we have Heidi mler uh presenting a talk entitled encapsulate and exfiltrate exploiting RC via DNS uh please give hard a warm [Applause] welcome hi everyone can you hear me all right yes great okay welcome to my talk I'd like to thank the organizers of bides Boulder 2024 this has been an awesome event so far and I've attended so many cool talks um thanks also to the sponsors we are in the rule four room which is pretty cool and thank you attendees for uh yeah deciding to spend your Friday at a at a bsides conference this is super cool so today uh welcome to my talk this is encapsulate and exfiltrate today we'll be discussing exploiting remote
code execution vulnerabilities via um DNS my name is Heidi metler I work in application security uh I'm a SE senior security engineer at Summit Security Group this is a Portland based security consultancy so um 90% of the work that I do is application related so whether that's web applications or mobile applications or thick clients or iot setups or apis that's the sort of sort of stuff that I test day in and day out and today I'm going to be talking about uh what I consider to be the crown jewel of application security vulnerabilities remote code execution um if an application is a castle and I find a remote code execution in it then the castle is mine
I win I can do anything that the application uh can do and have any access that that user can have um so if the application is like for a bank or something like that and there are Bank balances and customer number and customer information not only could you do something like deploy ransomware um you could just take down the site with the denial of service um type of type of exploit uh you could exfiltrate all of the data you could change the balances you could control money you could steal information do whatever you wanted you could also set up subdomains and you could um potentially use the bank's good name to do nefarious things um and widen your access there's
also something called scope change in the CVSs rating system which is when you find a vulnerability in one type of system but this changes you know you're no longer testing an application the vulnerability is no longer in the application it changes the scope to like being within an internal Network or something like
that so today the plan is I'm going to give some background about remote code execution and DNS and then we're going to talk about the problem so these days a lot of organizations have uh Security Solutions um EDR like crowd strike or sofos or other Technologies deployed with their environment in case there is this type of bug it will help protect the infrastructure or so you might think um the problem is that those Solutions are deployed in those environments and you might want to get around them so the solution will be leveraging DNS to exfiltrate your payloads I used to think that DNS lookups were pretty silly and just good for like Dem demonstrating to clients
that remote code execution vulnerabilities exist with their environments but I didn't think that you could get very far with them um due to a recent experience I've discovered that you actually can get quite far with them and they're a lot quieter by quieter I mean it's not like a a reverse shell or something like that where it's going to be really noisy and set off alarm bells and get shut down really quickly it's quiet it allows you to exfiltrate a lot of information so as it turns out you're only going to be limited by the size of a DNS lookup um your command line skills and your creativity so oh yes we're also going to
have a demo or a mini CTF how many people in here are red teamers or pentesters or do that sort of work great great Bryce you didn't raise your hand but I know you're there um wonderful and for the rest of you I hope that this will present an opportunity for you to see what a remote code execution vulnerability is like and have the opportunity to exploit it yourself on your phone or your computer whatever you have with you we will briefly touch on prevention towards the end of the presentation because I know a lot of you are responsible for securing your environments okay so uh here's the first background section what is remote execution and why should you care so uh
as Matt and Austin discussed ear C in their fascinating talk uh various technologies have these vulnerabilities within them um and when these vulnerabilities are found people can exploit them and gain access long term uh they were discovering how nation state actors were were able to do this and um that was a really cool talk this has to do with exactly that type of vulnerability it's usually in applications a result of unsafe inclusion of user supplied input in backend commands you find it in um in file manipulation operations like uploads or downloads if someone is uploading files into the web root of an application and they can upload say a PHP file uh or another executable type
then they can just put their code in their upload and when they render the page uh their code will be executed uh another one is if you can change the name of a file or something like that and that's done on the back end and you can include special characters in those commands um you may be able to do something interesting there and if you're downloading files sometimes the names of files are not included safely in backend commands and other plac is when you know you're entering an email address so that the server can use a command line utility to send you an email and if output en coding is not done correctly there then
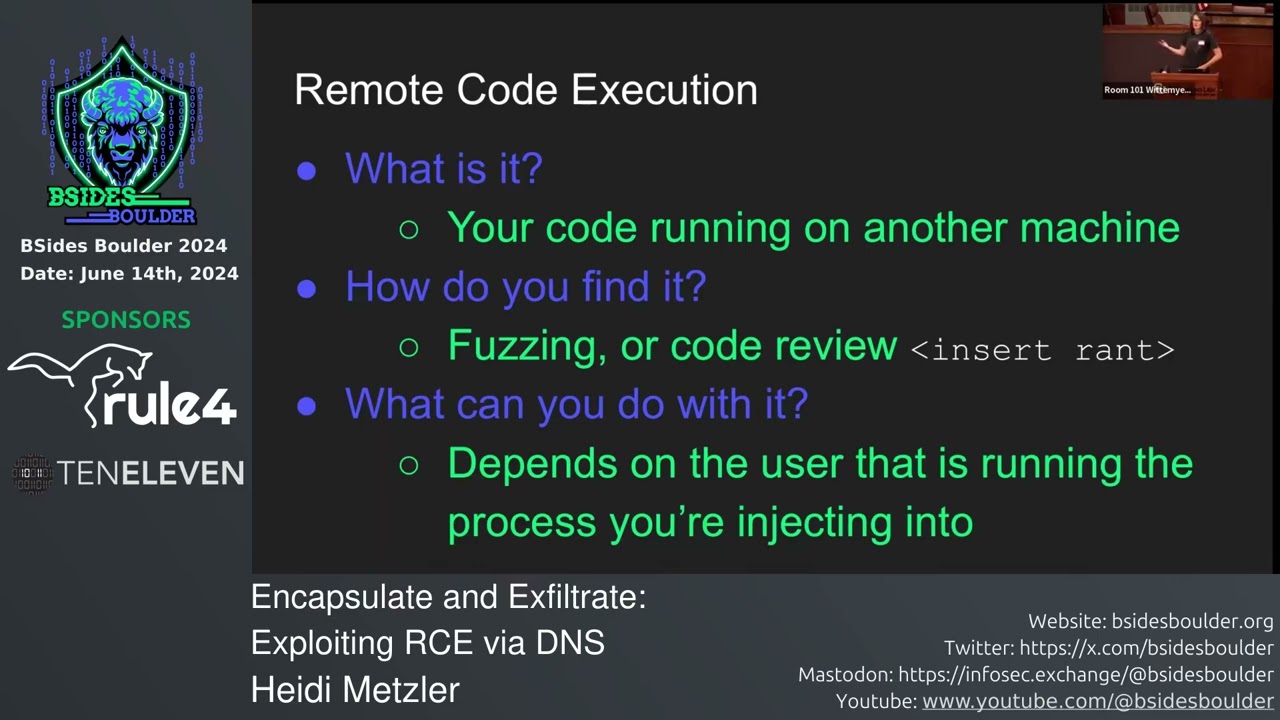
it will be a problem so to summarize remote code execution is your code running on somebody else's machine um you find it via fuzzing there are a few different ways that when you're fuzzing you might look for them you might try to do DNS lookups uh just simple ones to reach out to a server that you control and then if you get a DNS hit on there and it's the payload that you put in there then you know that it's there um or via code review so now I'm going to go on a small rant about how I believe that application security testing should be done um when when folks provide us during an assessment with their code we
can actually search for the vulnerabilities that we're looking for much more easily uh applications can be written in a variety of different languages and many of those languages will let you execute commands on the back end if you catch an application um putting user supplied input into those commands it's really easy to do um another one is looking for cross-site scripting vulnerabilities or SQL injection vulnerabilities those can also be helped by um doing code review so once you found remote code execution vulnerability what can you do with it that depends entirely on the Privileges of the user that's running the process you're injecting into so if you're just the standard user on an Apache web server I believe it's the
data- www user um if you are running an application in the confines of a container often times the container default account is the root account so if you find a remote code execution vulnerability on those then you have extra special powers okay so that's it for remote code execution now we're going to be chatting about DNS DNS is the phone book of the internet and it Maps domain names like reddit.com to an IP address it's useful because the way that the DNS system works is you ask a question to your DNS server and then that triggers a a series of queries that ends up wherever the end server is located and then the the IP
address corresponding to that is sent back to you the important thing is that whatever you look up arrives at where you're asking it to so for us it's going to be useful because we can use it to um exfiltrate our payloads after they've been evaluated in whichever environment we found the bug in okay so as we discussed a few minutes ago the problem is that there are Security Solutions that shut down reverse shells and it happens pretty quickly so um there are canned exploits there are met exploit modules you can use to exploit remote code execution bugs once you found them but they're pretty noisy and these uh these Security Solutions they find them and they ruin your good
time as a security tester it's it's a great thing that they exist but there are um there are other ways to to get around them um you need another way to get around them and there are a lot of legitimate reasons why an application will do DNS lookups I used to think that DNS lookups were just kind of a silly way of demonstrating to our clients that there was a problem in their environment but you can really do a lot more with them so they don't have to just be do um you can fit into one single DNS lookup a lot of information you can fit in two 153 characters total you'll need to separate them into parts for example
only 63 characters can be in a subdomain and you can see better details in the RFC which is 10:35 or if you just look it up on the internet you'll be directed to a very helpful stack Overflow article okay so that's enough for the talk so far uh now we're going to do a demo if you could if you have your phone on you I encourage you to do this even if you have absolutely no experience whatsoever with application security go to jimthe cat.com and if the page isn't coming up for you I don't know just try just try refreshing and it's an HTTP I built this a couple days ago and um you can tell that this wasn't really
made by a web designer and it has limited functionality but it it serves its intended purpose so there are two vulnerabilities on this site if anybody thinks they found either of them if they could raise their hand that would be really helpful one of them is a cross-site scripting vulnerability and the other one is a remote code execution vulnerability so a few minutes ago we were talking about how to detect vulnerabilities or remote code execution vulnerabilities within an application um I don't think I'm going to give too much away when I say that this is running on Linux server it's an Apache server and it's hosted by digital ocean um you could find that information
yourself if you look at the server responses I'm sure um does anybody know how to look for for example a cross-site scripting
vulnerability yep absolutely um so are there any places on here where input is being requested yep absolutely has anybody found a cross-site scripting vulnerability does anybody have a pro proof of concept to show me please yeah open script okay let's let's see that in action okay so it once wait a second what are you talking about it's asking for an email address so what's the email address you just gave me
okay and so this is a vulnerability so what's going to happen when I click subscribe taada okay excellent so you can see in the URL up above email equals script open tag alert uh parentheses one uh Clos script tag uh this is a wonderful additional proof of concept for across-site scripting vulnerability is it reflected or is it stored perfect very good okay um if a normal user somebody who just you know does things when they're told is is entered it could just be you know like Heidi at um bid.com subscribe and usually it would just output and and give it whatever you put into it um the problem with this application is that it is output en
coding is is not being done correctly so it's outputting characters that become a part of the page and they're rendered into JavaScript you could also do um let's see here does anybody have a more creative payload uh let's do document domain okay and now it's giving you back the domain of the site on which the code is running that can be useful because sometimes cross- site scripting bugs are in places you don't actually think they are lovely um great so has anybody done any more exploring on the site and has anybody else find found say a a different type of vulnerability remote code execution vulnerability
okay so how do I find this vulnerability okay site name competition let's see here I am always looking to expand my territory whether it's claiming a new box or creating a site help me pick a new domain and I'll check if it's available for purchas okay great so how does this help me run code on a remote server oh you did
uh so which which the the back quote okay the back tick yeah I don't know whatever it is yeah oh a web hook to a site that you control clever that's very good that's the whole point of this okay so that's wonderful um another way that you could find it okay so enter site name here you submit it and uh J is going to check and see if it's available for purchase uh so he's going to actually be doing an NS lookup doing some sort of a domain name system lookup to that site to see if it's available for him to purchase so ideally you should just be doing like example.com or whatever and then you
know he says that he's received your site name or his server does rather um but because because there is a remote code execution vulnerability in here we can put in back to and enter whatever we want um so one of the ways that you can find a remote code execution vulnerability in an application is using something like sleep if you tell the computer to go to sleep for five seconds and then when you submit that the computer doesn't respond to you for about five seconds that's a pretty good indicator that there's a bug there so let's try it sleep five okay Enter thinking thinking thinking great okay so there was a bit of a pause there
maybe it wasn't exactly 5 seconds but it seems like there's something going on all right so you're right this is currently a blind remote code execution bug but we are now going to make it less blind um one moment please pay no attention to the man behind the curtain here
okay please turn
on uhoh
oh thank goodness all right um yeah I should make more like burnt offerings to the demo Gods beforehand always yeah for sure okay so if you refresh your page or you just try it again your output is now going to be um a little bit different so instead of sleep five we're now going to try an echo command and so Echo Fu which is basically computer print the word Fu and we're going to submit it aha the output has changed your site name has been received and the output is the output of an NS lookup and it says server can't find Fu so our Command has executed our computer has said Foo on the back end um so it is turned from a
blind remote code execution vulnerability until you know we're just ating a situation in which you can actually see this um this Foo you could put uh you know like um fu. example.com and then your server can't find that uh in fact you can just you don't need to put a back tick on the end in this particular case um you can just put whatever you want to evaluate between those back ticks and then send it off to your DNS server of choice you don't need to see what's on the computer because this domain name this um this NS lookup here it's going to arrive home at your DNS server like this gentleman was able to do what's your name Garrett Garrett
like Garrett was able to do over there uh that's exactly the point of this
exercise the problem with NS lookups in this particular case is that there's only a single line of information that's exported to you so what if you want to do something more interesting you want to like search The Bash history or you want to see if the current user has um SSH to a different server or something like that does anybody have an idea of how you would go ahead and and try to find that information and Export it to your server if you've only got one finite line that you can you can work with
for example Haven done yet okay cool um let's see here I'm gonna go back to my slides for a sec okay I have some hints here sorry that font is a little bit smaller um there's there's a lot of commands in bash that can help you out and uh you know if you're using Windows they'll just be slightly different you just need to read the docs or check stack over or chat GPT or what have you and they will give you the the commands that you actually need to use um head- N1 will um give you the first line of a file name head n- N2 is going to give you the first two uh there's also a
corresponding command tail so you could sort of um shift the lines ask for the first line and then the second line and sort of um grab and trim as necessary using head and tail there's also said um said teac n 3p in quotes for a file name is going to print the third line of that file and then you can also do something like you know you can look in the history and use GP to search for specific commands that the user has run before okay so now I'm going to ask for some challenges and if you guys could just like find the answers to these questions then then we could solve this mystery and then we could look at the
answers together so which user is running this application that's very good and how did you figure this out who Am I who am I okay who am I so the command who am I if you if you type it onto a command line it's going to print the current user in this case this is being run on an application so whichever whichever user is running this application is going to be the name of the user that we see so we submit it lo and behold it's jim. example.com very good okay next challenge does the user have privileges how can we figure this out sorry you name okay so for example ID dashu 102 is it a SSE
no very good okay we're just we're just moving right along through these challenges I should have put more challenges on the board but I'm sure you know with some creativity we can we can still figure these things we can find more to find out oops wrong window uh are there any interesting files around this might be a little bit trickier so as Bryce mentioned a few minutes ago we have LS that we could use to list some files but then we would need to control the output so that yeah what if we just try LS in here what happens ls. example.com there's no output so what does this mean good yeah it seems to be too long uh the
NS lookup doesn't seem to be evaluating and like nothing's taking place or nothing that we can see is taking place all right back to the site name competition um yeah so has anybody found any interesting files I also understand if somebody just started up a remote shell because you know I'm not running crowd strike in this environment or something like that like you guys can do whatever you want please don't take down the site until you know the presentation is over though out of respect I would really appreciate app it's intended to be hacked but it would be nice if it would be nice if things didn't break while I was trying to show them
off
okay okay so CD and then CD and PWD
CD CD Etsy or try to VI shadow um so cat Etsy is it Shadow computer says no how can we modify this so that we could get how how could we yeah modify this command so that we could get a single line say the first line of this file so head and and then what very good that did not
work okay that gave us
something um where else can we look for interesting files us home directory users's home directory okay so LS how do we find their home directory Tilda no output so there must be more than one line so how do we how do we do this yep pipe to head dashn one so that it's only um giving us the single is this visible at all is this too small okay sorry okay make bigger control sh
plus oh please
okay better Okay cool so LS home uh piping that to head Tac and one submit no
output um let me
um sorry what was that yep
yep let's try [Music] one too many what it should my bad is it working for
you okay so which file are you looking at what's your command C password then I'm feeding that to a and I'm doing four and I'm getting the sys user very nice who do you work for you wouldn't have heard of them okay I I'll talk to you after class okay so let's get back to our challenges all right we found some interesting files um How Could You conceivably pivot to another server so an application is running as an account sometimes account account have access to other servers how would you find out if your server has you know remotely accessed some other server any thoughts uh host sorry the know host file know host file okay pardon my
mess um so for example which command would you use
this is actually yeah um this this cat decided to uh pay me in piles of like vomited up grass and and bits of kibble to to hack his site um so cat known hosts did you say ch. SSH underscore yeah okay does this look for as far as you can see gy okay we'll try home
gym thank
you h some sort of error here something's not working quite right let's try LS home gym and see what the first line is private journal. text this cat's been keeping a private Journal it's not just his blog how dare he um we should read his private Journal how would we do
that cat cat the cat's Journal okay so cat home gym um
actually just thinking one one big block also do tr- D and then quotes the new line okay okay uh give me the tr- D solution so what's your what's your command yeah so you want to type it into tr- D and then single quote d v is in Victor uh no d d as an echo as in delete as dog okay TRD and then single quote back slash and Nancy and then what close the quote Yeah close the quote okay and then get R of your head you need to get rid of the head got it uh the as well yeah yeah all right so we've got listing the home directory of Jim and then uh TR
tchd um new lines someone's been doing things here okay so who is uh who is ap3x who is it huh Apex who who's Apex Bravo Bravo this is wonderful um Okay cool so there is a flag there is a flag on in this environment shall we say you might want to think about solving this particular challenge um pivoting to another server in order to find that flag so um if someone could work on that that would be awesome in the meantime uh how could we do something along the lines of exfiltrating a private key just theoretically that most private keys are going to be kept in pretty known directories so just start looking for the the known
ones ID RSA SSA yep perfect good but then um yeah so so say that we're doing that but let's just look at the structure
we're just going to kind of cheat and look at the answers here because it takes a long time to run commands um so we are now Jim on the machine that's running the application Apex was here not the flag very nice okay um private journal. text there's that as well but yeah so if we look in the directory in which the SSH uh yeah in the SSH home directory of the user we see two files up top I'm sorry this is so small I'm not an expert at making things big on my screen um basically the idore ed25519 that is the private key the corresponding public key is in the same file with the pub at the end of it what
we want to see if we're an attacker and we can steal this private key and we know that this user can access some other servers then we can just NAB that private key um and we can use their private key to access anything they might be able to access to the problem that one might have here um is that are DNS lookups case sensitive no they are not case sensitive are there characters in this that you think might be case sensitive how could you get around that on the command line if you were trying to export this file line by line is there a way that you could change some of those characters or use some sort of different
command encoding that's on the command line and manage to export this uh line by line to a server of your choice Natalie a64 yes absolutely base 64 should work but is base 64 case sensitive as well it might also be case sensitive as well in which case HPS are already based 64 we could try decoding it hex encoding I don't know there's [Music] there's be letters and digits to the key encrypted it's not coded okay but is there a way to take bits of information out you know you could it would be a real pain in the neck to try every Alpha character on here and try it like you know both cases when you're trying to like not Bruce
brute force a private key but having to try all of those different combinations just aaine access to to a server would be a pain in the neck so you would need to find some way with a command line that you could encode this so that it comes out the other side in a way that you could decode easily and recreate this file uh what other challenges do we have does any progress on the flag does anybody have my flag okay keep trying um what else what else could we do with remote code execution earlier Matt and Austin were talking about all of these fun things you could do I want to just curl down something and execute it so
just curl pipe to bash and then use that for persistence rather than messing around with the the small window and like little little bits of space I have yeah for sure that's a great idea any other ideas you can also do something like zip up their home and upload it somewhere yep just just exfiltrate a whole mess of information did you raise your hand PR yeah have the flag tar through neck t t cat yep could totally work I've seen people set up whole command and control exfiltration like uh downloads through DNS as well so you can encapsulate um entire offensive applications and publish them in a known DNS location use the queries to pull
down those chunks of data and reassemble them back into the tools that sounds like a lot of work but with a very pleasing result cool I think someone something like what I think someone killed you somebody killed the site oh no
try refreshing try clearing your cash because that kept happening to me when I was like testing out this demo okay any any look on that flag anywhere nothing yet has anybody found out that there is a is there a different server anywhere that the gym is accessed sorry who who said something boomx yes boom box boom box is a is a is a great place to look for flag
um okay so I see we have about 10 minutes left in here and so we're just going to go back to the slides and talk on prevention but if anybody has any interesting developments like you know a flag or something like that just raise your hand and and I'll I'll get back to you okay so preventing this type of vulnerability it's very language specific if you're writing you know an application in Python Your solution is going to look a little bit different than in uh PHP or something like that but basically do not include user supplied input or even user influenced input in in backend commands um in so far as it could be used to exploit this
type of vulnerability um I also recommend using the principle of lease privilege because if Jim had been a pseudo user on on the server then we would have owned the entire server immediately we could have done anything that we wanted and my final recommendation is to patch patch patch it's a good Mantra because um like some others have spoken about today new vulnerabilities are being found in Technologies all the time and they need to be fixed so in this particular case
um what did I call it okay so the file that is called when we're exploiting the vulnerability is site comp. PHP who can tell me oh gosh can you guys see this at all no no okay
um I'm just going to copy it
uh oh that was showing up initially yeah it was I was uh playing with Chad GPT or no not chap gbt but some I think maybe it was Dolly too for a Christmas card and yeah it came up with some pretty cute pictures actually I have to say um okay so this is the content these are the contents of the file the PHP file that we are exploiting this contains the bug where is the bug
very good okay so it's taking the get parameter site and it's putting it in this variable called minnos Jim loves minnows and then it is executing an NS lookup on the content of that variable so it's just taking the user supplied input and plop it it into a command and execute it on the back end of the application so it's line if you can't see the output um but because these two lines here Echo output and Echo some output are not commented out specifically this last one here we can actually see what's going on it's being output to the page so you can see the results of your command execution so if the in the DNS exfiltration example you
would do the two back scks with your command and then sub dot whatever your control domain is exactly just be whatever the output was B and what not those get encoded some they might get encoded in some way on the back end that's why if what you are trying to exfiltrate is case sensitive like an sshd or something like that you will need to you know check for a Basics maybe not a Basics before um encoding in this case but find some sort of encoding that you can use on a command line um that you can that you'll be able to decode on the other side when it comes out of your server does that make sense
so you were trying to detect this
yeah you could you could but you know um so we've been looking where you can you can we've been dealing with very short lines and files so far so just a few characters each what if the first line of the file is huge you're going to it need to take it out in shots you might also need to take it out in characters if you know you have some sort of a security Solution that's looking for heex encoded payloads or what have you that are being exfiltrated elsewhere um you might need to just take it out in smaller chunks if someone were looking for this thing but that's that's very creative and that's an elegant
solution just use an Amper with this too for getting multiple lines could do that like an and and uh so probably just the single a for just to allow for the NS lookup to fail give more space for example uh I just did example erson LS slash no back ticks the other way forward slash no back ticks require no back
ticks also Escape out of it just with a semicolon the with a what semicolon after example and then just straight up LS that's true uh get rid of the ound comption right sorry you want the site name competition for uh yeah am I on the wrong form oh that's embarrassing form oh gosh okay so example and then Ampersand LS one of the other sorry it's either the semicolon or the ERS my bad the whole CH that was beautiful that would work if you were still running
yeah cile splits it into 256 PA of chunks do like DNS lookups for every single chunk exactly do that yeah so you can do a lot um yeah the message in this talk has been basically be worried about remote code execution vulnerabilities even if you're running some security some really fancy expensive security solution in your environment it's important to pay attention to vulnerabilities have your have your stuff tested um look for look for problems early in your code so that you don't end up uh victim to one of these attacks and yeah are there questions sanitize sanitized all input yeah absolutely who has my flag has anybody got flag itex huh that vexin flag it the contents of
it you got it brace yeah [Applause] awesome1 me here I don't know who it is you what AP1 me there who's AP1 it's me is that Matt yeah that's me dang where to go on CTO good work all right so I think that's my talk thank you guys so much [Applause]





