Outmanoeuvring Threats Beyond Earth - Cyber Counterspace
Show transcript [en]
[Music] Hey, how are you guys doing? So, um I'm going to ask you guys just to bear with me. Not feeling too well, uh unfortunately. Um so, topic today is cyber counter space. Um my name is Nathan. I live in Vietnam, right? and uh like a few other places in the world, it's a bit of a hot bed for um hybrid warfare right now. Um many reasons, Taiwan, South China Sea, etc. If you look at the dotted line over there, right, that's essentially the part of the South China Sea that China um believes it owns. and I stay just to the left of these dots and all these dots represent Vietnam's presence in in in in the South China Sea. Now, what's
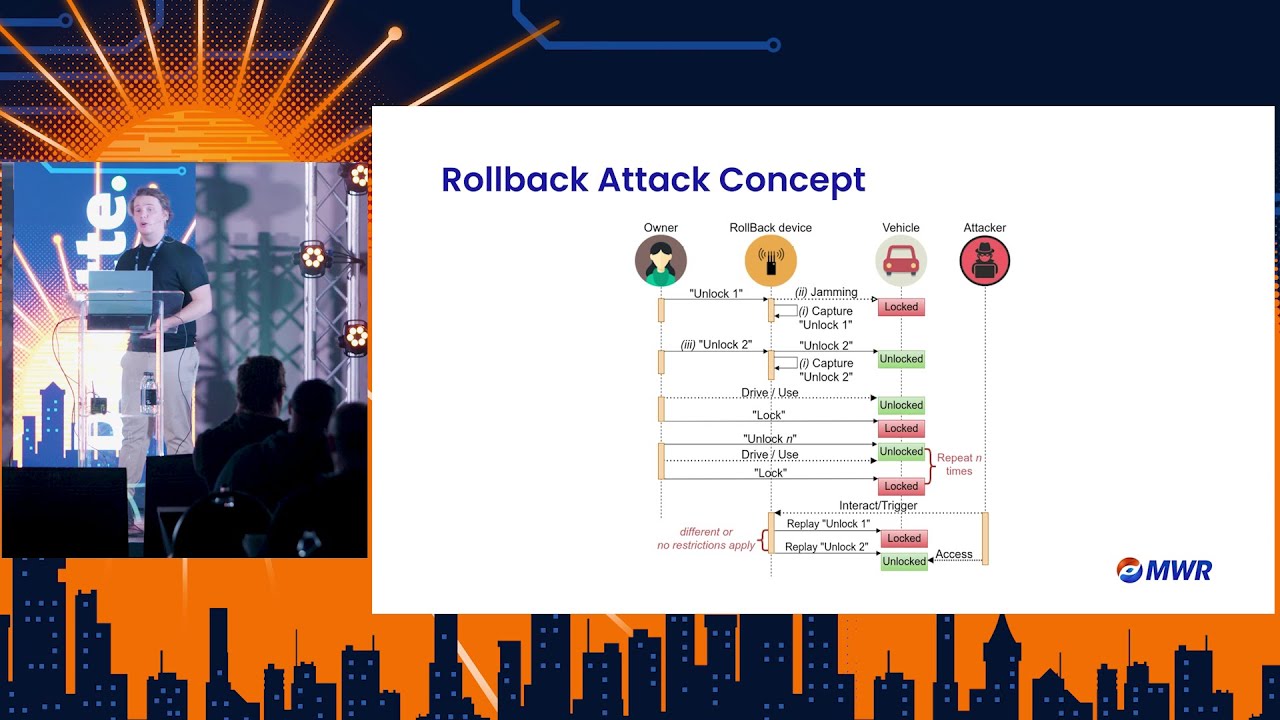
super interesting is um I I'm I'm staying just to the left of that and every now and then we have these sporadic incidents where like GPS goes haywire. Right now, it's not a GPS outage because those are monitored for, but it certainly it certainly strikes me as like counterpace activity. So, what is counterpace activity? Uh, anything that can disrupt, deny or degrade uh space systems, but also manipulate space systems, right? And um if you take a look um one of the places we see this a lot is with Russia and Ukraine, right? Interestingly enough, I got this picture of a defense analyst website for Pakistan, right? And the whole point that the defense analyst was making
correctly so was that because Pakistan now and India are having an issue and India has basically aerospace dominance right so um the argument was that with the absence of launch capability right Pakistan can't launch right um the analysts were saying that Pakistan needed to develop counterpace capability and I believe this is true so there's different types of counterpace um kinetic non kinetic, electronic and cyber, right? But in truth, right, there's two types of weapons you get. You get kinetic weapons, you get non-kinetic weapons. Under non-kinetic, you get electronic and you get cyber, right? That's how the flow goes. But theoretically, there's four types. Now, when you talk about kinetic, it's super interesting. Um, but in terms
of counter space, it's basically ASAT, right? Which is anti-satellite like missiles, right? kinetic missiles, right? I'm not going to have a lot of time, but you guys should actually check out what's uh you guys familiar with what's rods of God. Yeah, you are. That's quite impressive. Okay. And um the picture is actually that DF21. It's called a Dongfang 21. And it's super interesting because it's u supposed to be like a top secret Chinese missile. What's interesting is the picture is like a Lego set of the top secret Chinese missile. Um, and actually got the link to the the block, but the Dongfang essentially the D20. It's a D21 um DF21-d [Music] anti-arrier missile. I don't know if you
guys ever seen this. Has anybody seen this before? So, there's a desert in China and they've got replicas um that are built to scale of all the various different uh American ships. And the Dongfang essentially goes up into space, right? So, you see it launch, you don't see it after that because it goes into the it into the space realm and then it comes down and it hits you in the terrestrial world, right? So, we're really interested in the non-kinetic. So, you've got the electronic. Electronic is like jammers and dazzlers. Um, a dazzler is like if you were looking at uh shooting something with the scope and I kept like reflecting light into your scope, right? Um, and
jammers I think you guys are pretty familiar with. So, why cyber counters? Because that's what we're here to talk about. So cyber counter space pretty much because low barrier for entry it's easy to do and also the problem is very very very um um the problem is like sort of easily understood right because pretty much cyber and engineering don't bite together so similarly to like OT in a mine um space infrastructure is like riddled with vulnerabilities Now um one may think this is something for the future right so there's um there's a research uh paper done by a university in Zurich and they essentially count about 120 uh counterspace incidents between February 22 and September 24
that means there's a counterpace incident just more than one a week right so counterspace activity is rife. Actually, the reason why we were doing this research is we believed uh you guys know the space agency got hit, right? Our South African space agency. Did you guys know we have a space agency? Okay. So, and then um um we had a couple of attacks in South Africa which led me to believe it could be counterpace related. However, we did the research and it wasn't right. So where's space exactly? Well, it starts about 180 km up, right? And if you think about it, like a lot of people think of LEO, right? Lower Earth uh orbit, right? And um when you think
of LEO, you're thinking about 2,000 km up, right? And that's correct, but that's the upper bound of LEO. The lower bound of LEO is about 180 km up. And that's about 10 times what your normal aircraft flies at, right? the basic space system. When any you talk to anybody about a space system, what they typically think is it's only the satellite, right? But it's a satellite, it's a ground, it's a user, and it's the link between all three, right? And there's multiple cyber security frameworks. But recently there was like a space industry um discussion around the cyber security frameworks. And what these guys said is the compliance to these frameworks actually detracts from proactive security. Now why is this? Are you guys
familiar with Sparta and and Space Shield at all? But it's like it's like the tech, right? Uh the MITER attack framework. The problem is like post-launch maintenance is like really difficult, right? You can't send a 40 gate firewall into space. And if you did send a 40 gate firewall into space, well, firstly, it takes a lot of mass. It does not fit for purpose, but it needs to stay up there for 10 years, right? Nobody here keeps a firewall for 10 years, right? The next thing that makes it really really difficult is over that 10 years the accuracy of the detection mechanism degrades. And essentially what swap is is it just takes too much resource. It
takes too much weight. It takes too much memory. Right? The other problem you have is you have all these binaries in space and a lot of these binaries either come through a supply chain and for IP reasons or just the fact that they're 10 years old sometimes there's no source code. So if you take a look at like what we do in in snow technologies for those of you guys who do know so last year we presented on our digital twin technology and simulation and at it web we did how we're using large language models for deception but none of that technology is feasible to go into space and what's happening is we're actually um adding GPUs and this is not just
Snowd right this is everybody We're adding more memory requirements. We're adding more processor requirements. And we're getting further and further away from something that's actually usable in space. So if you had to take a look at like okay, what happens if we take a U-turn and then we go in an opposite direction, the firstly first thing is you're looking for something we call a a massless embedded sensor, right? So essentially you want threat detection that's built into the firmware, right? And it can't be signature based. You guys understand why, right? Because number one is it goes up for 10 years and now you can't get the signatures up there. And also the signatures aren't really uh relevant. So it's got to be ML
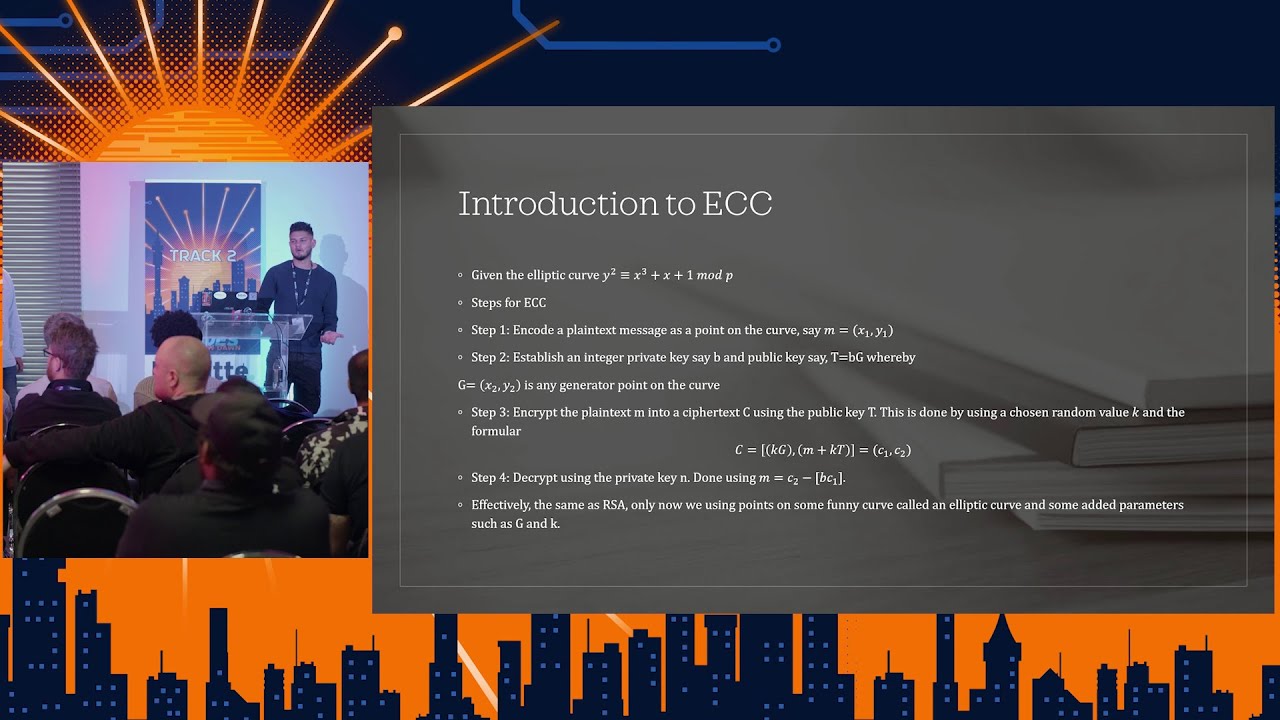
or AI based for anomaly dete detection. And um and typically like I think a um a good solution would be if it use something like fully homorphic encryption. You guys know what's fully homorphic encryption. Okay. So when you transmit data right um you'd uh encrypt it with like something like SSL. Um and typically we transmit data, we store data and we process data, right? And when you store it, you you can also encrypt it, right? But today when we process data, you have to decrypt it, right? To process it. So wouldn't it be more secure if you could store, transmit, and process all in encrypted form. That's fully homorphic encryption, right? The next thing is you need it to be
autonomous, right? You can't have human in the loop because there's no sort of human in the loop for space. And then you need self-healing infrastructure. Uh a short micro patching. A short micro patching is is really interesting. It's so I don't I don't have the source code to a binary, right? I find a vulnerability in the binary and then I patch it without shutting the stopping the binary from running. Um you guys are familiar with binary patching though? Yeah. Okay, good. So although you're making this U-turn, there's 1.8 trillion reasons why we should be making this U-turn. And why I'm really thinking this is a really good idea to speak uh about today is simply because how well positioned South
Africa is to provide this kind of capability. Firstly, I don't know if you guys know but a lot of aerospace components come from South Africa. Did you guys know that we parts for the Euro fighter um parts for like space shuttles right come from South Africa. The other thing is we've got deep cyber capabilities and we've got deep history of engineering capabilities right because of our mining history etc. And so we're really well positioned to bring these two worlds together, right? So collaboration between us as a community and the people who are like Etion create. Etion create does the the components for the Euro Fighter, right? It's like working together with these guys to produce
components that are, as Steve would say, um, secure by design. Um yeah, thanks guys. By the way, this this orbit is called the Lrang uh orbit and it's the orbit uh around where the sun um uh casts a shadow with the Earth. I just thought it's pretty cool. Anyway, thank you guys. Cheers. Bye. [Applause]