The evolution/revolution of Cryptography & Quantum Computing in Cyber Security
Show transcript [en]
[Music] hello welcome to our presentation my name is Verlin niker I'm joined by Ivan Burke from Blue vision itm and sad Ki a master student at Vitz University today we will be discussing the fundamentals of cryptography RSA and ECC shaes algorithm the future of cryptography Quantum resistant cryptography and pqc post Quantum cryptography we will also be discussing the basics of quantum Computing and talking about superposition superposition that's a big term and entanglement another big term but we want to avoid buzzwords such as Quantum Supremacy wormholes time travel and other spooky concepts for me this topic is fundamentally about change change happens through Evolution or revolution Evolution happens slowly we know what we don't know and using the
scientific method we find out what we don't know a good example is Moos law we know that the capacity of the CPU can be increased over time we just need to figure out how to do it a revolution on the other hand is completely different we don't know what we don't know and that's where we have scientific disco discoveries scientific breakthroughs when we discover something new it's amazing it changes the world like the discovery of penicillin was amazing Discovery quite often scientific breakthroughs are followed by engineering breakthroughs Quantum Computing is currently going through a series of engineering breakthroughs but the error rates are too high hopefully the error rates will start dropping soon and that
would lead to the spread of the technology the theory of how technology spreads is explained by the diffusion of Innovations or do DOI model and you taught that's a mouthful the unified theory of acceptance and use of Technology as an example the use of electricity in the US started around 1900 it reached 20% in 1915 65% in 1930 85% in 1945 and 100% in 1960 it took 60 years to reach saturation the use of the internet started around 1990 and reached 52% in 200 76% in 2010 90% in 2019 and 95% in 2023 it took just over 30 years to reach close to saturation the not notable observation here is that it took 60 years for electricity to read saturation
and only 30 years for the internet so that Trend continues the time frames are getting shorter and shorter for new technologies although the time frames for saturation are getting shorter the adoption rate follows a typical bell curve starting what a group called The innovators and then another group the early adopters which is followed by the early majority the late majority and finally the laggards you got to ask yourself in terms of quantum Computing which group do you fall under hopefully not the laggards quantum mechanics and Quantum Computing may seem abstract to a lot of people but today we we will be presenting the practical uses of quantum Computing to be sure Quantum Computing quantum computers are real and used in
real world environments there are many Quantum Computing companies in existence companies such as d-wave IBM Google Microsoft quantonium retti atos ion Q ion Q does something technology called the trapped ion the Chinese are there with Cas the Chinese Academy of Sciences and then the old favorites Intel and Nvidia and these are just the Front Runners d-wave is a company that specializes in optimization also known as Quantum kneeling in jobber we have the Vitz Quantum initiative which is at V University and there's a IBM lab in jutah Street slightly off campus um we have quite a lot of quantum in South Africa and sad will be presenting more on that thank you okay so good morning everyone and thank
you for attending our presentation very quickly so there's been a realization by a lot of the academic professors that we need a road map for Quantum in South Africa and so South Africa stance has always been to focus more on the software developments as opposed to the actual engineering of quantum because we don't have enough money for that so actually there's five involved universities we have V UK stalon BOS University of Zulan and K Peninsula University and our focus is on as I've mentioned software so very quickly I'm going to drive into cryptography a very quick overview so many of us may have came across cryptography working in s security so I'm going to run through this quite
quickly so cryptography simply put is the science and art of hiding information using various different forms of techniques so cryptography provides confidentiality integrity and non-repudiation so confidentiality make sure that the information is only for the intended recipient Integrity makes sure that the message stays as the message was sent and of course non- repudiation allows for individuals to have responsibility so some of the questions that cryptography answers is how do we transmit messages securely through through an insecure Channel I.E the internet how do we keep the Integrity of a message how do we ensure that the message is only for the internal recipient and how do we prove that we are who we claim to be so cryptography
can be separated into three Frameworks generally we'll have symmetric cryptography asymmetric cryptography and hashing as well so mathematically hashing are most hashing algorithms are one-way functions so we're not going to be covering that in today's presentation very quickly symmetric cryptography is the idea of having one cryptographic key per partner so whenever there's a communication link from one party to another you use the same key to encrypt and the same key to decrypt so it's often used for encrypting bul data and data at rest and it's a fast form of cryptography that's generally used some examples of the modern day cryptography techniques is a and 3ts so our presentation will be mainly focused on asymmetric cryptography so in a in
asymmetric cryptography each party has two keys one is called a public key and one is called a private key it's often quite slow and mostly used to establish session keys and authentication such as digital signatures and so forth so it's also generally used to prepare for symmetric key establishment so very quickly why do we need public key cryptography which is another term of asymmetric cryptography is because symmetric cryptography has three core core challenges the first the first challenge is key a key distribution problem of course um communicating to our party and transmitting a plain text key can cause a lot of a lot of problems the second situation is the number of keys per party that's a second challenge which is
given by the following equation so essentially 20 parties would require 1,225 keys if we were only to use sometric apography and the third example is that there's repudiation so one example of that is if LS sends a purchase order to a vendor she can then change her mind later on and claim that the vendor falsely generated something so asymmetric cryptography was actually introduced in 1976 and provided a solution for all of these challenges so in asymmetric apography as I've mentioned we have two types of keys we have public keys that are available to anyone while private keys are kept private as the name suggests so one rule of time for for asymmetric cryptography is that public keys are always used to
encrypt while private keys are used to TP so so Ellis will compute her own private key a and public key F Bob will compute his own private key p and public key and if Ellis wants to send a message to Bob essentially Ellis would use Bob's public key to encrypt and then send the message for so this solves the the the challenge as we've mentioned previously on the slide before this so in RSA these public keys and private keys are large integers which are essentially very long numbers whereas in eptic curves apologize these keys are coordinates on a curve okay so very quickly introduction to RSA so RSA is fundamentally based on something in mathematics called modular
arithmatic right so I'm going to go through the first example it's actually I'm going to explain it in a simplistic way so essentially what it tries to do is to find a remainder so if we have seven and we divide it by five our remainder would be two so that's generally how the equations work so there'll be two parties Ellis and Bob the way RSA actually works is that Bob will compute his private key and public key as we've mentioned previously C in our case would stand for Cipher text in other words the the jber that would be that that would be Central and network M would be the plain text and P would be the prime modulus so if
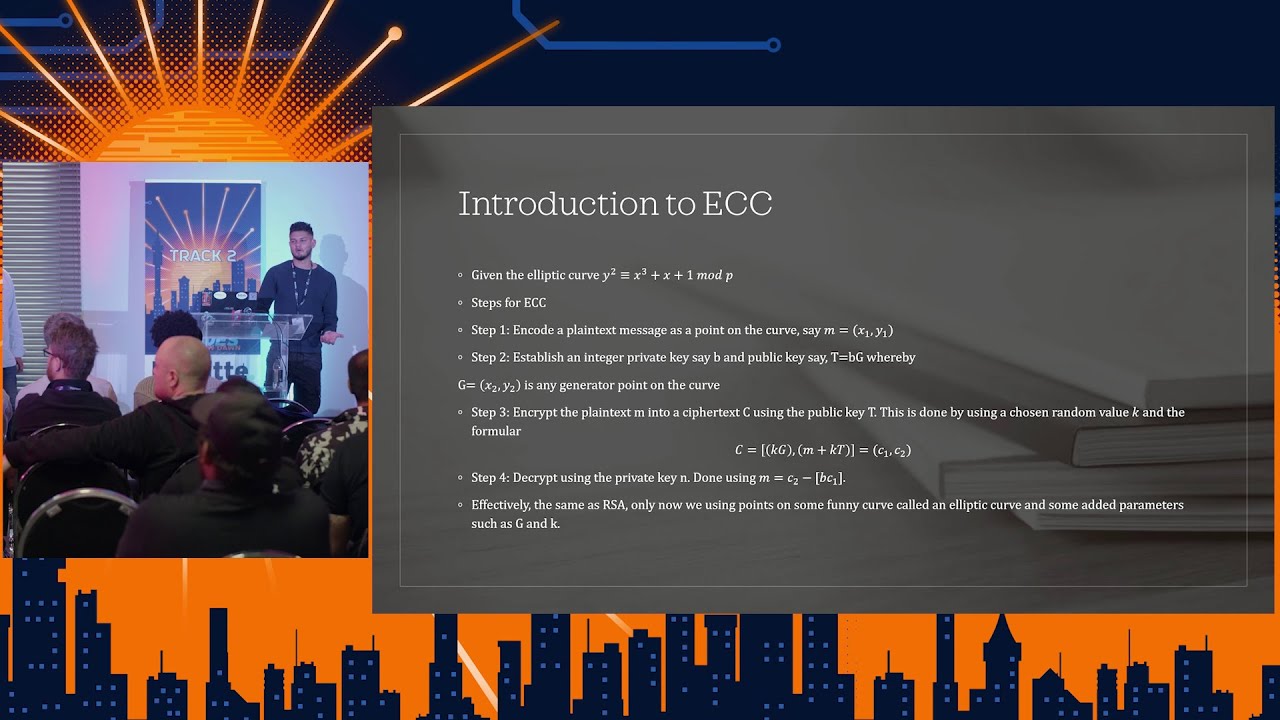
Ellis wants to send a key if he wants to send a plain text message to pob she would then use the following equation and if when Once po receives the cipher text he can then use use the following equation from them so very quickly introduction to elliptic cve cryptography so elliptic C elliptic curve cryptography is often seen as the bigger brother of RSA and this is generally what a real elliptic curve would look like which is a cluster of points but for explanation purposes a lot of mathematicians have realized that we could explain these type of Curves through the following graph so for the sake of completing elliptic curves actually plotted over a domain which is
referred to as a finite Prime field but for purposes of explanation we can explain this using a real line so this is an idea of what an elliptic curve actually looks like so introduction to elliptic C cryptography if you use a specific example we be given that particular equation so as you can see if you compare this equation to what we add at RSA essentially tic curve cryptography it add spice to RSA essenti making it more making it more difficult to to to solve and to break so a few steps that are involved in this process the first step will be encoding our plain text message which could be a it could be a video it could be it could be
voice recording it could be anything of that sort the first step would be to incode that plain text message as a point on a curve we'll then follow it we then follow it by step two where we'll establish as we've mentioned previously a private key and a public key and then step three will then be to encrypt using the following formula and to decrypt using the following formula so here's an actual example with some real numbers so this is an example of eptic curve so if Ellis has a plain text message M which is given by 4A 5 and Bob has a public key which is given by T Ells can then use the following
formula and then Bob can then decrypt and get 4A 5 as well so I'm now going to pass you on to Ian which is more practical hi everyone um I'm just going to be talking a bit about like some of the bad implementations that that sometimes can lead to uh issues with these encryption algorithms that was just mentioned by S um so I mostly use this type of stuff for uh cyber security challenges so I set up a lot of cyber security challenges uh for other students or for companies uh so one of the popular ones that we did uh is we give people a partial public partial private key and see how much of the data we can emit
from the private key and have them still recover the private key so this was quite popular especially around 2012 is when a lot of attacks could get you partial data so for example heart bleed and there was a lot of attacks at that time that focus a lot on retrieving partial data from hard drives or from Communications so then the concern was but how much of a private key would you actually need to recover before you can actually reconstruct the whole thing uh so we did a lot of work uh back then about this so basically because it's fairly well documented the structure uh of RSA public a private key uh a lot of the data in there is is bit redundant so
if you know the structure which is defined by ASN you can go and seek out specific uh key offsets within the data sets uh to find where where where for example the first Prime second prime is um RSA mostly works on the principle that that two large primes are multiplied together to get you this value n and n is basically very difficult then to factorize back into it its original primes again but for the private key to work it needs to store those two primes um so yeah so if you can recover either one of those two primes the other one can be retrieved by just dividing n Again by one of the primes and you get the other Prime so we
we did a lot of these type of challenges the CTF that was available for uh this event also use one of these as an example um then one other weak implementation is shared primes problem so um because RSA keys they they need to generate a prime and it's it's fairly difficult to or computationally um expensive to calculate a a prime a lot of companies what they would do is they would take shortcuts they would choose a short list of primes and they will just reuse them and select random two out of the these sets the thing is uh uh ukl came up with a formula over 2,300 years ago that can easily factorize this so
this is this is a couple of thousand year old formula but yeah so ukas formula you can use to if if two large numbers share a prime you can use UK formula to um find one of the primes between them and then then you can get the other Prime by just dividing n Again by The Primes so uh uus formula is used for that um so some company they they presented in uh 2017 at blackhead they basically what they did is they turned this into a big data problem and they started harvesting public keys because for this you don't need the the the the the prime so you you just need someone's public in the public already con
contains the value in so that's that's the the product of the two uh primes so what they did is they just saw how many primes can they collect and how many of those primes actually share uh primes and how many can they then crack as a result of this so they went and they harvested from GitHub from all the sources because that's sort of the thing you're you want to share your public key remember your private key want to keep secret but your public key you want to make as widely available so they collected from pgp they collected from all kinds of sources and they collected about uh 220 million keys and they had about a 65% of of of the keys they
harvested they could crack again um so they literally just turned this into a big data problem instead of a security problem um yeah um and then another bad impation that's fairly common is if they use uh what's known as IM meral Prime so IM meral Prime is basically 2 to the^ xus one that tends to be a prime so a lot of companies what they would use if they just want a quick way to generate a prime they'll generate the merer number and then just validate if that's a prime if that's not they just increase 2 to^ x + 1 and they go on with this until they find a a suitable Prime but those primes are
very easy to look up for a computer and very easy to to crack for a computer so if if your algorithm uses a merer prime to generate its two primes with a private key uh that uh can lead to to security vulnerabilities um another implementation would be If You're vulnerable to the forat algorithm so forat algorithm that that tries to determine if two of if your two primes are fairly close to each other then the easiest way to find one of the two primes is to uh get the root of of of N and then just go to the roof of that and then test if that's a prime if it's not increment by one if not repeat this
process until you find it if the two primes are fairly close to each other this is a very trivial problem to solve and it's like the algorithm is right there it's it's four lines of code so it's very nice uh I think one of the challenges this year was also based on that um yeah so I'm just going to head back to uh s to explain the rest of wum thanks so I've just got two slides here just to give you a little background of how we get to Quantum Computing uh the binary principle is the foundation of all modern computers when we look at the history of modern computers we will see that it started with the punch
card you have a hole no hole simple binary principle building on the binary principle was vacuum tube computers in the 1940s you had two possible States on and off another example have you seen this CD have a bump no bump if you look closely you'll actually see where there's bumps and no bumps so uh I actually wanted I went onto the net looking for punch cars I thought I'll do a little show and tell you know buy some and pass it out to your guys and you know wow you guys but then I found this in my locker and I said save all that money I'll just show you guys this you can you can actually touch it it it
won't break yeah absolutely I'm not young I had my mustache died by the way um so generally speaking we have two distinct States that's the binary principle and it served us well for over 100 years so the transistor can be considered as one of the greatest inventions of the 20th century the first CPU had only a few thousand transistors that has evolved to billions of transistors today and continues to evolve still following Moore's Law this brings us to the fundamental difference between classical comp computers and quantum computers classical computers follows the binary principle you have two distinct states in the transistor you have a high voltage and a low voltage quantum computers use something totally different it uses the concept of
superos that that is huge as I said earlier on sard will be speaking about that just now but I just wanted to go through some of the logic gates so in terms of logic gates in a classical computer again it uses the binary principle you have your not gate your an gate your no gate your nan gate there quite a few Gates and then you obviously can combine those Gates and you you have different type of computation the in terms of quantum Computing the quantum logic gates include the headart gate the poy or po X gate the the PO y gate the PO Zed gate you have the controll notot gate and the list goes on actually
for for Quantum logic gates I'm just giving you these terms because you will be coming across these terms so you're not only talking about Nan Gates and your your basic building blocks the hamat gate at the moment is a lot of people use it for as I spoke about d-wave earlier on um for optimization the headat gate is is is one of the most common used U Quantum logic gates sad will explain the basics of superposition and Quantum
Computing okay so very quickly as a revision classical In classical computers the zeros and ones effectively don't represent anything in nature right so the zeros and ones are mathematical representations of high voltage and low voltage so what exactly is a butt and how does it affect us in application so essentially two buts if we use two buts we can have four possible combinations we can have a 0 0 0 1 1 0 or a one one so that would mean that we require two buts of information in order to describe it in other words if I were to say choose one of the four possible combinations you would have to keep one value followed by a second value so
we'll see later on in the next slide how that's going to to defer with Quantum Computing so a classical computer would have to also compute each possible combination individually as opposed to how quantum computers work and it should make it will make more sense as we progress so quantum computers are built on two primary principles we have the quantum entanglement and we have superposition right so I mean we can just ignore the notation of the straight line and the incomplete triangle but essentially we can represent a cubit state by five so we we using the same idea of the binary digit where we had zeros and ones but just now in a different notation right so as you can
see we have a * that 0 plus P * that 1 whereby if we take the modulus squar of a we get the probability of an electron being in that particular state so in other words our cubt is essentially at both the zero and one simultaneously so if you look at the diagram if we make zero represent purple and blue represent one can actually see that at any given moment in time you can't distinctly say that the electron is at a one or it's at a zero it's effectively at both at the same time this is a bit counterintuitive but it ends up working right that's uh quantum physics which has been scientifically proven and is a natural
phenomena so a two Cubit State system can be can be represented by the following equation and then as I've mentioned previously we'll touch on a little bit on entanglement and superposition so I know this a very bad looking cve but essentially if we make the y- axis our probability just to explain superposition in a different manner if we have positions A and B then we have a probability curve that's how the quantum physics um explanation is described so what is the chance of an electron being at position a as opposed to being at position B so if you look at the curve you can you can more or less say there's a 70% chance of it being at
a and a 30% chance of it being at B so at the end of the day even though we have the superposition principles we have to come back to classical computation because we need to solve classical real world problems so then we utilize something that's called a collapsing over state so it turns out whichever position you measure the electron at being if as an example as depicted if we measure the electron at being at position a it will then end up only being at position B for the rest of the time and if we end up measuring the electron at position a it will only remain at being at position a so all of these principles are utilized in Quantum
Computing through the use of quantum engineering to allow us to solve real world problems so how cubits are measured so if you consider two cubits as we've mentioned previously but now with some real numbers if you describe the first Cubit by 51 and the second Cubit by 52 essentially in Quantum Computing you have to Define things as a system so we don't deal with each classical bit individually the more cubits you addir into the system you have to describe them relative to each other so due to entanglement effects which basically to give a practical example if if we had to prepare two cubits in in entanglement right now we could send one cubit to to Ma and have
the other one here and essentially whatever happens to the cubit in this room would directly and simultaneously happen to the other Cubit at Mass so it's a bit gets a bit more crazier than that but essentially so we can see if we have two cubits two separate cubits and we want to bring them together they then described by by FF in the following manner so the point that I was making at the slide is that if we if you look at the the Zero from 51 and the Zero from 5 2 we can see that we multiply 3 over 5 by 1/ < tk2 which gives us 3 over 5 < tk2 so essentially the final State
depends individually on every Cubit so if we have a quantum computer with 100 cubits every Cubit has to be described relative to the other 99 cubits that's partly the reason as to why it's so difficult to build this quantum computers and also partly the reason as to why we can compute we can compute things quite quickly so mqs require 2 to the power of M buts of information in Quantum Computing whereas classically n buts require n buts of information so as we've shown earlier in the first slide one example of this would be three cubits so in order to describe three cubits we would need eight BS of information whereas classically three cubits you would need three BTS of
information or to use a smaller example as we've mentioned earlier for the two butt situation we required two butts of information to be given cuz we had 0 0 0 1 1 011 so we' have to give two values whereas Quantum mechanically as you can see from this equation would have we have to describe 3 over 52 and the second 3 over 52 then the 4 52 and the 4 over 52 which is for two Cubit system so Quantum mechanically a two Cubit system you need to provide four equivalent parts of information so if there's anything to take away from those slides it will be this last line so essentially nine operations to find something
classically versus a maximum of a square root of nend times on a quantum computer so to put this into perspective if we had a bag wor 100 Balls and the question is which of those balls are blue a classical computer would have to individually solve for each and every single ball so that would be 100 times cuz there's 100 operations whereas for a quantum computer that would be the square root of of 100 which is equivalent equivalently 10 so solving the same question on on classically we had 100 operations on a quantum computer we can do that we can get the same answer with as little as 10 operations so I'm now going to pass you on to
Ivan hi um yeah so I'm going to just quickly talk about Shaw's algorithm so um before I do that I'm just going to explain how you decrypt again a RSA key um uh after you've now got into two primes so over there you'll see there's there's three basic steps that you need so first you need to calculate the the Theta of n so so the way you do that is basically you get um p and Q well P minus 1 * Q - one and that would be the Theta and then you PL you put that into the inverse Square the inverse um of of of B to get back your original message so so this is basically just it's a lot
of maths but it's basically just explain to you that you need pnq once you've got your encrypted message to get back to your unencrypted message so get back to your your your your PL text message you need PQ and that's the sort of the problem that that you're trying to solve with trying to crack um RSI cryptography is because p and Q is quite difficult to get because n is is very difficult to factorize if you can get either P or Q you can follow these steps basically to get back to the original message um so what what David what Peter Shaw did is he developed this in 1994 so that's 30 years ago he came up with this idea and
this is more based on a numerical Theory so instead of trying to calculate this out with a physical machine what he did is is let's look at the the the properties of numbers and how numbers interact with each other and and what type of pro uh properties you can can deduce from certain behaviors or certain patterns you can observe so one of the things that you observed is is if you're looking for a a shared Prime between if you're looking for a Shar Prime between two large numbers one way that you can do that is is represent them in the following way so in his theorem so he's got three theorems in total we're only going to be focusing on the first
theorem uh the second and the third theorem more focus on ECC U cracking that the first one is more on RSA the first theorem basically states that if you're looking for um a different way to basically represent um a a a a shared Prime between these two values you can multiply either one of the the two numbers uh with each other with itself as many times as you want um and eventually that will equal to M * the second number + 1 so the way it does the reason he does this is he's trying to guess what is one of the primes because remember when you start off this exercise you have no idea what either of
the primes is but using this algorithm you can guess a value and this will actually give you a very good approximation what that what um what one of the primes might be so your guess will then be popped into this this this formula and if you do a bit of uh manipulation you can see you get get down to the uh equation a to ^ P equals MB + 1 uh so if you simplify that uh you can convert that to the difference of two squares so in this example I'm just going to show you some examples of where I basically said okay so in the first example for example the is a and b so
I'm looking for a shared Prime between uh yeah 7 and 15 where that would fit in so 72 = 3 * 15 + 4 so that one doesn't work so you try each example until you get 7 ^ 4 = 160 * 15 + 1 so there you find out okay now I can get a share Prime from that right and then you you uh if you put that back into his formula you can say I can now work out the difference of two squared numbers so if you go uh so so if we take the first example 7 to the^ 4 so um difference between two primes basically is you say the difference between two squared numbers
you you pick the first the root of the first number minus one and then the root of the first number again plus one so um yeah uh so for that you'll see on the right hand side that's the formula for that um and using this type of maths you basically Pro that no matter what number you pick you can pick any number at random whether the number is bigger than than one of the primes or smaller than one of the two primes you still have a 37.5% chance of getting to a better guess the only situation where this won't work is is where either the number you guessed itself shares a shares a prime with the
two numbers or um if it's a multiple of either of the two prime numbers that's that's where you sort of run into problems um so just to make it a bit clearer I I figured I would um show you a bit of a graph about this so this is now for example um here I'm looking for uh another example um and I'm guessing 31 and as you can see each time I write down what is the error rate so in other words what is the remainder I'm looking for a remainder of one but every time you'll see in the first iteration the remainder is 133 then 4 then 19 and then finally I get to one then it goes to 10
then 16 then 13 then 4 so there's a repetition so the nice thing about this repetition is that forms a waveform so as you'll see on the right hand side here I represent this as a waveform and with Quantum Computing you can do what is known as a Fior transform of that waveform um sorry next slide and then you can figure out how frequently this repetition happens the problem with Quantum Computing is once you do the measurement you collapse the States you then you don't know um what so for example over here once you do the measurements you might get to the state where where the the exponent was was settled to to to the value of three for example and then
you don't get the value that you actually wanted you'll get say for example then the remainder is 13 um but you wanted the remainder to be one but because there's a there's a a a a a waveform that basically expresses how frequently the value will be 13 you know what is the um the max distance that this will basically be and this max distance will always be the same because this always a sort of a repeating pattern right so you actually just want to know how frequently do I get even the wrong answer so using quantum computer you can even get the wrong answer but because of the properties of it you can deduce the correct answer um due to the
collapse State because you know that if you know how frequently it gets the wrong answer then you can know what is the distance between those two points and you'll know okay this is how many times you actually have to do that operation so it's it's sort of working more a side effect of quantum Computing than working with qu Computing directly um yeah so over here sort of more the the exact formula so on the top left hand side you'll see the exact formula basically how it works so for this to work you would need quite a lot of cubits so for example if you have a 256bit key you need at least double that many number of cubits so at then of 512
Cubit system to try and calculate because you need at least two waveforms to be completed because with a single waveform there might be due to some interference you might have a offset might make it go wrong um so you need at least two wave forms to complete for it to to have a reasonable chance of actually being accurate uh we'll later get into the whole how accurate is because there is some some interference that can occur but basically that's how many cubits you'd need to solve this so you can imagine if we're now already at at at 2,000 uh bit Keys then you need 4,000 cubits and we're we're still quite a bit away from that but using this
formula you can basically prove that you can calculate any of these um um uh you can basically Square any of any large number in as much as four operations because basically because all these operations that at the same time because as soon as you collapse it that's it you measure it once it's done so you went from trying to calculate this with with a classic comput of a Brute Force Through many many iterations to four quantum Computing State calculations that you basically have to do um and you have a 37.5% chance to get it right on your first try and within five tries you have a 99.999 chance to get it right so just shows you how much Quantum Computing
actually speeds this up um yeah so yeah and now going to finish about the the the the future of quantum [Music] Compu okay so essentially what we've established in the session is that theoretically speaking modern day encryption is proven or can is is is theoretically proven to be broken by quantum computers that's essentially what we've explained and it's just a matter of the quantum computers catching up to reach the correct number of cubits once that's reached it's proven that modern day encryption would essentially break so since we use encryption in almost everything that we do in our daily lives we use encryption to serf the internet we use encryption in WhatsApp messaging we use encryption in
banking so of course they they have to propose new ideas as to how we should move forward so if ly um Nest which is an organization which regulates cryptographic algorithms for the world have opened a challenge previously to mathematicians of the world to propose new ideas as to what type of mathematics to use so from that that challenge there were 66 submissions that were made or approximately 66 and four of those submissions have been accepted by Nest so we have crystals kber crystals the lithium Falcon and sphinx plus so essentially why this is proposed to work is because now the mathematics has changed generally speaking most of these Solutions follow what we call ls-based cryptography so as you can look from a
few screenshots with the simple Google search we can see that there are a lot of different companies which are already adapting to this postquantum methods such as Zoom as an example so this of course been a major concern for the world so this is one methodology of moving forward in order to solve the problem which is a traditional mathematical way so take out the existing algorithms that you use and then Implement these following algorithms however we do also have a physics solution which is generally used by by companies or organizations within the military or something of that nature so what happens here is that communication is done through the use of photons and it utilizes the effects of
Quant physics so that whoever is on the line or whoever tries to decrypt information can never do that based on the hardness of quantum physics so the idea of quantum phography and Quantum key distribution actually started at it actually started with BB with the bb84 protocol which was developed in 1984 it then moved on to the B92 protocol and then the e91 protocol so Quantum photography is also used for Satellite Communication in fact in China they you that's how they that's the means of communication between the ground and between the SAT and between various satellites as you can see from from these Google searches so that will be the end of the presentation and thank
you a lot for paying
attention any questions then so so two questions the first one is when it comes to the probability W for collapse on observation or measurement how do you know whether or not you've got interference are you eff effectively are you effectively running three or four of those in parallel and then using that as a probability distribution amongst the three different um computations okay so how it currently works is is that's why they they say you need at least double as many cubits as as the key length so your first indicator that there might be an error is if if if those two waves don't repeat like that like I said it's supposed to be a perfect repetition if
it doesn't repeat properly then you you you have your first indication of of of a fault um and then obviously your second way of doing it is if this says that is a shared Prime and it's and you you because that's L the calculation you just go n divided by that number if that isn't a shared Prime that would also indicate for you that but your first indication would be that there's a there's a disc discrepancy between that waveform that would your first indicator okay and and so then you you're running the fast 4A transform on top of that yeah yeah okay cool and then the the second question is really like how can cyber Security Professionals protect
themselves it seems like what you're sharing here just based on the complexity of the key length is that increasing your key length to obsurd numbers might be a real good way to at the very least in the short term um make it more difficult for the story store and decrypt strategies and then in the long term is it is it then moving to a swingx algorithm or something like that that's easily implementable yeah so um I think we'll both cover so essentially the amount of key length in RSA and EC hardly has an effect when it comes to the quantum computers breaking it however in symmetric cryptography so there are cryptographic levels of security that
are used to measure the secureness of an algorithm so something like a is actually mathematically more secure than asymmet cryptography but now the two different forms of cryptography so in terms of something like a or 3Ds if you increase the key length on that side it will make it essentially a little bit more difficult for quantum computer but not to say that it's it's not possible okay cool so the answer is switch to a Quantum resistant uh technology as soon as possible I guess I guess that's why so so Nest is working towards um regulating it and they coming quite close to the final stages of passing it out in the public and in our example we
specifically just now talked about RSI because that's really the easier one to explain with with um ECC um as I mentioned you need about double as many cubits as as the key length for ECC you need about uh um yeah six times as many so so so ECC is already like levels above that and um so so the current largest uh uh and something for ACC or 600 even yeah yeah but the the current largest um quantum computer what's its size it's how many 1,000 something yeah about 1,000 is the largest but even that one there's lots of caveats about in an ideal situation in ideal when everything works perfectly well it has a, cubits so we're still
quite a bit away from that but the thing is what we're trying to just say is is it will eventually happen so that that that that technology is getting there but it's still going to take a while so having logically will help to that degree but you're just delaying the inevitable so having something that's Quantum resistant is a bit more of a longer term solution than you just gotta so that effectively means if you're if you're taking the 1024 cubits uh divided by two um we're looking at asymmetric encryptions at 512 bit being assumed to be uh decryptable today absolutely right in theory in theory yeah just to add to your point so I had on my slide I didn't touch on
it too much there's the the concept of harvest now decrypt later and a lot of governments are already doing that so if you are running 512 now and theoretically we got thousand but I remember I spoke about the error rates are very high so in the lab they they're getting the Thousand cubers to work but you cannot make it work in production basically so it's it's in test basically so so Harvest KN decrypt later so be careful what you're doing right now because 5 years time the guys can decrypt especially at the 512 bit rate gotcha awesome so yeah okay whoever gets the mics first there's two hands here so follow the mic is it on a very
quick question roughly estimated how far off are we before we get to like 4,000 Cubit machine no we we we're not going to prognosticate on that absolutely so that's actually the hard topic there differing opin deping I covered that in my opening remarks we're not going to talk about about that yeah yeah so there is I mean a lot of differing opinions yeah sking okay uh so this is just a bit of a follow on from the question of the first gentleman but um so I was fortunate enough to partake of the CTF so thank you for that but um during that research uh I saw theography challenges and part of that was seeing that AES um I'm not sure how accurate
this information is but app handy as is considered to be um Quantum resistant and I just want to understand what is the uh difference between something like that and what you've shown us here like for example the um crystals KY algorithm and is it getting to a point where for as a sec Professionals for us to protect these systems are we actually going to need quantum computers to do the encryption like will classical computers no longer be sufficient at some point okay so firstly so what makes a slightly better than RS is is RSA is heavily dependent on these primes and the factor factorization of these primes being difficult AES doesn't use that so so Shaw's algorithm is specifically
developed to try and factorize primes it so to our current knowledge there is no similar algorithm for trying to decrypt anything that use like a block CER or anything like that that us but's algorithm yeah okay you know so my question is sort of more physics I guess engineering based how do they what are they doing currently to induce State on cubits and um physically what's the difficulty of collecting a lot of cubits do they collapse if there's too many of them um and yeah how do they indu state is it a modified still in GAC are they still doing that yeah yeah so that's more of a Quantum engineering question what of the electrical engineering but
essentially I mean they still use the semiconductor chips right so if even in Quantum Computing so they would use a semiconductor material that's something like Silicon which is made up of Isotopes we have silicon 28 silicon 29 silicon 30 so essentially that would provide a vacuum in which phosphorus atoms are actually doped into that and then essentially they use they um they use a similar analogy to how it's done classically where we have a transistor but what tends to happen is that we'll have a source in a drain and then whenever an electron Falls onto the transistor it reaches through various different means mainly through magntic um magnetic resonance that's used in order to change the probability because
so you can actually apply magnetic resonance to manipulate how probable you want a zero or how probable you want a one and then you'll reach a stage where the electron is both off and on the transistor at the same time that's essentially where the superposition comes from yeah thank you are there any other questions one last one um sorry I felt like this part of that question wasn't finished um I think he asked what would make some of the uh Quantum resistant algorithms what actually about them makes them Quantum resistant and then I think he did ask do we need quantum computers to be able to do the encryption for normal systems to keep them Quantum resistant for like
attackers okay so the first question is the mathematics of postquantum cryptography has nothing to do with modular arithmetic anymore it's essentially as I've mentioned LS based cryptography which is more algebraic it's more dimensional so it's taking problems and it's adding more dimensionals which makes it significantly more difficult to solve so essentially mathematicians have used creativity to get away from the problem that we face and then the second question no you wouldn't need a quantum computer in order to do encryption it's just that the way the quantum computer works you can design your mathematics in a way which doesn't give an advantage to a quantum computer so there's mathematic Solutions and then there's physic Solutions but
those are a bit impractical because you you physically send through light beams in order to communicate or through optical fiber as well one last question are we in between you guys and lunch okay there's one more talk oh there's one more talk okay um hi um I just wanted to ask in terms of the hardness between um RSA and Li to curve cryptography is it based on the discrete logorithm problem between the two yes essentially that's that's what it is it's just that elliptic curve cryptography is more efficient significantly more efficient so as we've seen if you look through directly from the equation what eliptic curve cryptography just tends to do is that it takes a basic like m to the power of E
and makes it a polom so actually like a 256 butt elliptic curve is as secure as like a 2,000 butt RSA key but the hardness of the problem is based on modular arithmetic and one example just to get it through is if you look at a clock right so if I say it's now 12:00 and later on it's 1:00 how many hours you have passed so if I don't specify if it's A.M or p.m. or which day it could be someone could say 1 hour someone could say 13 hours and so on so forth so the idea of modular arithmatic is that there's a very large set of possible answers and that large set is
quite significant so for classical computer it would in fact take thousands of years to just break and go through one one algorithm so it's based on the idea of modular arithmetic I don't know if that answers the question yeah okay thank you guys I think we'll have to wrap it up we over time thank you