From NTLM to Kerberos: The Evolution of Authentication Relaying Attacks
Show transcript [en]
Thank you. All right. Can we hear me? Okay, in the back. >> All right. Great to see some uh familiar faces. Good morning, everybody. If you're sitting in the room right now, you want to talk about some NLM and Kerros. Yes. Active Directory, Windows on prem, maybe cloud, right? All right, thank you for the intro. Like he mentioned, Alberto Rodriguez. I'm a senior managing security consultant at Guidepoint and my team just performs offensive security services for various different industries, different industry verticals. I've been there for almost three years now. So, it's it's been a long time, almost a full enlistment commitment, right, to the military in the room. Uh, I served in the army. I
was stationed here, left here in 2020. So, been in Florida back home since I got out and yeah, it is cold. When I woke up this morning, I'm like, "Ooh, this shirt maybe wasn't the right idea." Um, I've spoken here before. I believe it was 2122, I can't remember, but I've also given presentations at other conferences. Uh, they're mostly on YouTube if you want to check some of those out. Heat fan. Any Heat fans in the room? >> Damn. Hey, we got one. All right, cool. Dolphins fans. No Dolphin. Oh man, let me let's not talk about that one. Um, yeah, huge basketball fan. Unfortunately, the Heat. We'll see what happens this year. Uh, I also practice
Brazilian jiu-jitsu, so if you, you know, practice, happy to chat about that. And also a huge Pokemon fan now. Getting back into the hobby. Anybody else? Awesome. Yeah, there we go. Charmander. I like that. All right. Why this talk? So, NTLM is apparently going away. Anyone hear that recently? Awesome. It's still around. It's still going to be around. We'll talk about that. Uh Eliad Shamir, who I believe works at pretty well-known company called Spectre Ops, mentions that while many security practitioners think NTLM relay is a solved problem, or at least not so severe one, it is in fact alive and kicking and arguably worse than ever before. That quote really resonated with me because I think that highlighted
slashbold statement is re is the reality of where NLM attacks are right now. Luckily, some organizations are starting to lock it down. So, as attackers and as defenders, we need to start to think about what's that next step for us once we get into these engagements and NLM is really hardened. Well, what can we do if we want to relay some creds? Just to quickly touch on the image there. I see NTLM as in the basketball court, right? You got this OG. He's still hooping. He's still out there grinding, teaching the young boys how to play. Uh but eventually he's going to sit out. It's not right now, but it's going to happen. And that's where I
think NLM sits. So, here's the quick agenda. I think I have an hour minus questions and stuff. So, hopefully we get through it. I think we will. So, buckle up. It's going to be a fun one. 50 minutes. All right. Cool. So, NLM Sunset. So, it is official news now by Microsoft that NLM will be decompensed
by default. NTLN's been around longer than I've been alive, right? Uh I was born in 94, so not too far off. Uh but yeah, introduced in 1993. It's been around ever since. So you can imagine the attack surface for NLM started, you know, 30 plus years ago now and it's still used every single day by offensive security professionals and criminals to this day. Uh so 30 days of attack surface to me is pretty wild, right? And as we get into the space of okay, NLM needs to go away. It needs to go away. There's a lot to think about, you know, what do we replace it with? Every application that communicates with NLM, what does that mean? If you're not
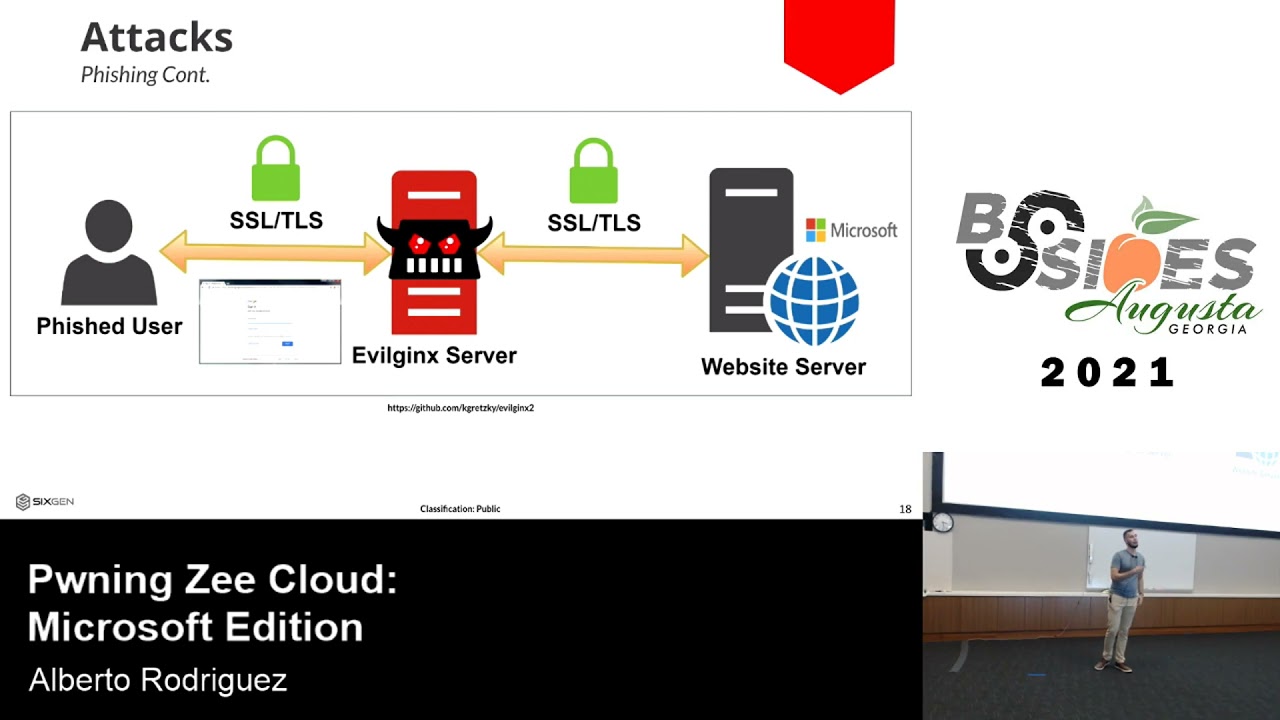
familiar with NLM, it's a challenge and response authentication protocol. Uh, three messages really. client sends out the negotiation, the server responds with a challenge and then the client sends a response with an encrypted challenge. That encrypted challenge is the problem because it is derived for the users from the user's password. It's a hash of the user's password. So you can imagine when you're sending that across the wire how it is advantageous for an attacker. Uh now this does cross protocol compatibility. You know you want to access something NLM's in the middle of that exchange. It makes it a pretty seamless integration and experience for the users. Right here's just a quick visual. I'm a visual
person myself. So again, client on the left, server on the right. Negotiate. Hey, I want to authenticate to you to the server. The server sends back that challenge. And then you as the client, you says, great, here's my encrypted response. That's what the attacker is looking for. So, here's what we want to do as attackers. We want to be in a machineinthe- middle scenario where when the client sends that response, that third response, we're in the middle. We're utilizing that credential matter and we're relaying it or potentially cracking it offline if we need to do so. Right? So, that's the position we want to be at. And let's just take a quick pause because the reason we're talking today
about NLM and Kurros is because NTLM is now going away allegedly. Let's talk about some other technologies that quote unquote went away. Windows XP went away a long time ago. Do we still see it? Right. I still see XP. I don't want to say weekly, but maybe every two weeks, right? in Windows Server 2008 and Windows 7, we saw eternal blue and we still see that, right? So, how long until I don't see that anymore? Uh, so NLM officially in June of 2024, Microsoft said it's going away. Let's take a quick poll. Who says we will see NLM in five years? By a show of hands. Five. Okay, hands down. 10 years. 15. I'm with the 15 crowd personally.
Uh the reality is that because it's so integrated into the Windows ecosystem and there's still many applications that leverage NLM as their on-prem authentication mechanism. I think that decom process is going to take a hot minute just like everything else has. Maybe AI will expedite that. Am I right? Fun times. All right. So now that we understand NLM a little bit, let's talk about Keraros. So Keraros is quote unquote the recommended authentication protocol in a on-prem environment. Single sign on mutual authentication effort. You have the client, you have the KDC, the key distribution center, which in Windows land is your domain controller. And then you have the service or the server that you're trying to authenticate to.
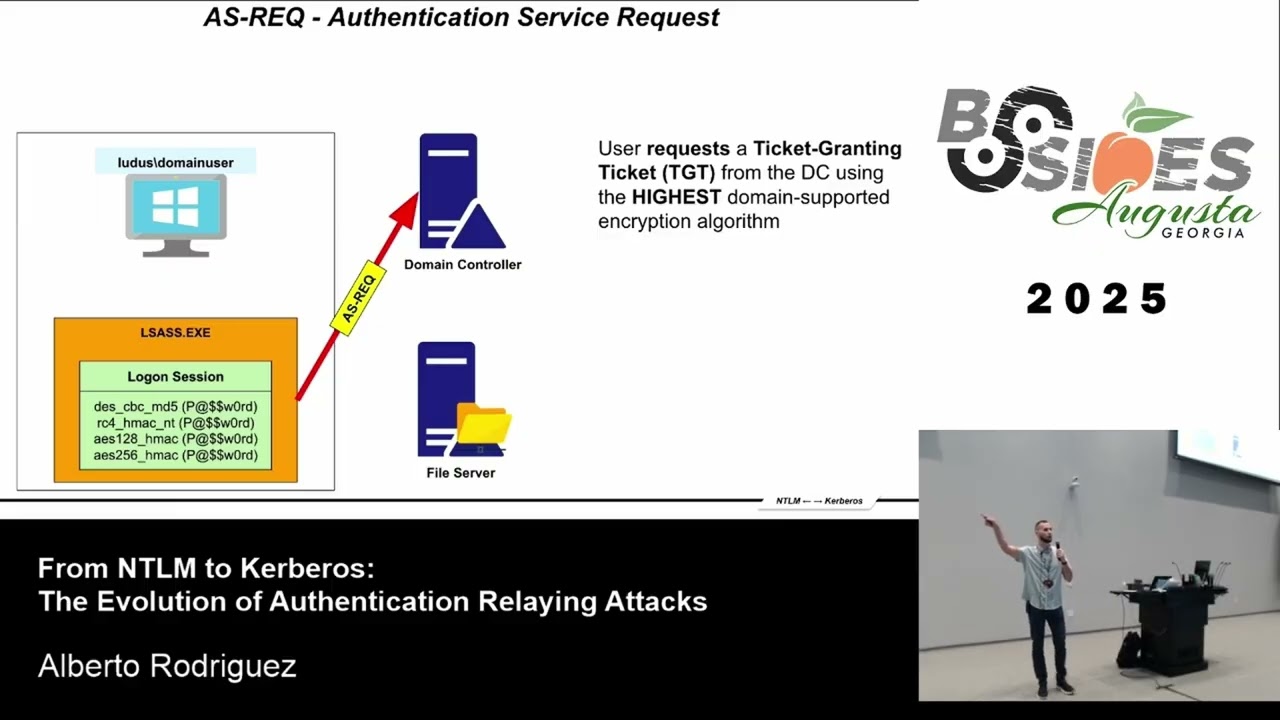
And here's how that authentication workflow goes. It's a little more involved than just three little messages. You have the user user logs into the workstation and then a password hash in various different encryption algorithms are put into the LSAs process. And that's important because depending on the supported encryption algorithms within the active directory domain will depend on which one is extracted from LSAs. Secondly, the client sends a authentication request to the domain controller and says, "Hey, I need a TGT." Let's pause for a second. I love the Kerros analogy of a uh those like popup uh carnivals they call them, right? English is my second language, so bear with me. Uh the carnivals, you know, the ferris wheel, the random
people with like interesting looks. Yeah. Thank you. So, you pay for your initial ticket and then sometimes, you know, they'll give you the little wristband, right? But then sometimes that cool ride you want to go to is like an extra ticket, right? You got to go to the little kiosk and get like another ticket for that one ride, which makes no sense. Kerros is sort of that way. You request a TGT, that's your entry into the carnival, but then if you want to access that cool ferris wheel, you need a service ticket, which we're gonna talk about. So think about that analogy as I explain this a little bit. So again we have our uh password in LSAS. We reach
out to the domain controller requesting for a TGT. Domain controller gives us that TGT. Now we have entrance into the carnival. And once we have that TGT we can then go back to the domain controller and say hey DC I want to access a file share you know file server one. We no longer provide our encrypted hat, our encrypted password to the domain controller. We now deal with the TGT, right? Hey, I'm in the carnival. I'm good to go. Here's my TGT. Domain controller sends back a service ticket. Think of it as that extra charge fee for the Ferris wheel. That's really cool. And let me go back for a second. That service ticket contains and it's derived from the
service account password hash. So here's a little bit of an, you know, a credential matter that might be useful to us as attackers and we present that service ticket to the service. Let's say it's a file server. The file server says, "Yep, this service ticket checks out. You're legitimate. Here you go. Good to go." So here's how that authentication workflow looks like. Again, it's a little more involved than the original three steps like NLM. Take a look. Uh the client in this depiction is actually in the middle. So we go to the domain controller TGT a lot of back and forth. We just went through it and then eventually we can access the file server.
So we understand NLM, we understand hopefully a little bit about Kerros and that authentication workflow. Now let's talk about coercion in general. Um, I don't know if there's a formal term for this, but in the hacking scene, we just call it authentication coercion. It's essentially you ask yourself the question as an attacker, how can I get a computer to authenticate to me? How can I get a user to authenticate to me as the attacker? Because again, we want the machine in the middle presence. We want to be in the middle of that conversation. Uh, Disney, please don't come after me. So that's the big question, right? If we look at NLM again, how can we get in the
middle of this conversation? How does machine in the middle even become a thing? Right? There's a couple ways of doing it. For starters, we can poison the network. And some of these have been around again for a very, very long time. We have we still see legacy protocols in an active directory environment. LMNR, MBTNS, MDNS, which is like a Windows proprietary thing that if DNS doesn't work, it falls back to this and it kind of tells the world your your hash, right? Secondly, DHCP, DHCP v6. If IPv6 is enabled in your environment, which by default on Windows clients it is, as the attacker, I can pretend to be a DHCP server, become your DNS server. Boom.
I'm in the middle again. Uh, traditional ARP. Let's not forget about just standard ARP poisoning and ARP spoofing. Just be careful with that. Don't doss the network. You know, be very specific in your commands on what it is that you're trying to poison. So, that's one way of doing it, getting that machine in the middle presence. Another popular way is sort of this ondemand way, right? And this is a good screenshot slide here, but there's a lot of tools and different wind32 APIs that can be leveraged in order for you to tell a computer object, hey, you come authenticate to me, right? And this is what we call the ondemand authentication coercion. I think I think don't quote me
on it but I believe printerbug was one of the first by uh Tiffken and Elad Shamir this was years ago now but since then many many more have continued to come out so there's a tool out there make sure you check it out great documentation uh they try to implement all these methods of this ondemand coercion called coercer it's written in Python excellent tool and I believe like a day ago some new thing came out of this. I didn't put it on the slide because I haven't tested the tool myself, but it's out there. So, again, seems like every week or every month, a new method of ondemand authentication corion is coming out. Another notable way, which we often
forget about, especially if you're new to the offensive security scene, you might not have heard of this back in the days, uh, but this stuff still works, where you're able to plant, let's say you have writable access to an SMB share that gets a lot of user traffic, like a file server as an example, you can plant the right file on that uh, share. So that way, as users are browsing that specific share, they will authenticate over to you. There's a couple of these different files. These are just sort of the popular ones, right? Call it farming, if you will. You go out, you plant the file, and then you sit and wait. That's another method of getting somebody to
communicate to you. And an honorable mention is your vulnerability scanners, defenders. Uh this is my recommended method. It's also the lazy method. Uh, but you start the engagement, you start doing some recon, but before you start that recon, you set up a listen a little listener and you wait for Nessus, Qualis, whatever to authenticate to that Linux device that you have on the network or that Windows device that you have on the network and then you pray that like in most instances those vulnerability scanners were given DA rights. Yes. So that when they authenticate to you trying to scan you because they just have a blank slash24 or a blank slash16 without any tuning that Nessa scanner
will authenticate to you trying to scan your device for vulnerabilities. And what they're really providing you is some awesome creds. So love vulnerability scanners. Highly recommend it. Sort of the lazy method uh but it works. Anyone ever get creds from a scanner here before? Yeah, plenty of hands. Awesome. All right, let's take a quick pause for some CIS admins in the room. We've talked about NLM. We understand Keraros. Hopefully, we now understand coercion and how for some of these Keraros relaying attacks, we want to be in a machineinthe- middle sort of foothold. You can restrict NLM right now if you want. Okay, like most things in Windows, there's probably a group policy for it. Uh, good screenshot slides. The slides
will be available on GitHub, though. So, if you want to save some storage and not pay for iCloud like I do, something a lot of people don't know about is if you're hesitant to start implementing this, there is a protected users group in your active directory environment. I'm sorry. There's an active directory group called the protected users group in your AD environment that when you add users to that group, it will force Kerros authentication. So for all all of those that are well, you know, I have these service accounts and I don't know if it's going to break and I can't just implement it for the whole domain and everybody has a thousand1 excuses of why we can't patch
or fix things or, you know, vulnerabilities or misconfigurations. You can start with your, you know, sort of high-end users that are service accounts, put them into the protected users group, and then see if something breaks and then send it. Here's how that looks like. Again, you can go into your environment tomorrow, put some users in the protected users group. If it's good to go, start patching, you know, start disabling NLM. Of note, there are three settings to disable this fully. Uh when I started prepping for this talk, I started with one and I could still fall back to NLM. So you have to disable it on the client side, you have to disable it on the
server side, and then you have to disable it on the network side. So sure, it's a little more extra, but not really. It's really interesting how a lot of the tools that we use as attackers and how Microsoft just makes things work. It always reverted back to NLM somehow someway. I'm like, man, I can't prep this demos unless I truly know only Kerros is going to be used. And you'll see in the demos how I was crafting a TGT by hand every single time because I wanted to use Kerros. All right. So, let's quickly pretend I don't know what year it is, but NLM is gone. Awesome. It's Kurros land now. You're an attacker. You're cooked
because those NLM relay scenarios that were just so sweet uh are now no longer feasible. Let's start with an ADCS example. Okay. Right now, a lot of pentesters out there, one of the first things they're going to look for is a certificate authority in the active directory enterprise. Yes, offensive people in the room, that's something you look for, right? Money maker right here. Uh I think June 2021, the white paper came out about all these ADCs exploit uh or misconfigurations there rather. And one of them was ES8. ES8 essentially means or what the misconfiguration is is that your S your certificate authority has HTTPbased enrollment enabled. Okay. So when you have that enabled, you can effectively
uh relay the credentials into that web enrollment endpoint and then get a certificate for that specific user that you relayed. Now there was a huge flaw. I forget when this came out, but it was unauthenticated uh coercion petif. And this was patched, so don't freak out. But what this enabled attackers to do was to coersse a domain controller to authenticate to you. Bad. And then you coupled it with ES8 and you could tell a DC to authenticate to you, get a certificate and then you had a domain controller certificate and then with that you could DC sync and it was game over with no credentials in the domain. That has been patched obviously, but when this first came out it was pretty
bad. uh but this is still you know one of the primary methods uh your you know red teamers pentesters in the environment are getting high higher privileges in the domain. So here's a quick steps of how we're going to relay from SMB to HTTP using strictly Keraros. Okay, let's walk through some of the steps. And it's a lot of them, so I had to like write them down so I can walk through them because memorizing this by hand will be brutal. Um, in this scenario, we're going to poison DNS. Okay, we're going to get that machine in the middle foothold by becoming a DHCPv6 server and taking over a client's D uh DNS version six. Right.
So, we advertise this. Awesome. We've now spoofed. we have the machine in the middle footprint. Then we're going to set up curb relay X which is a tool written in Python that will allow us to do this relaying behavior. Once we poison those DNS requests, we're simply going to wait for a legitimate request to go through. We're going to sit in the middle of that conversation. We're going to relay that Keraros uh traffic and we're going to generate a AP request on behalf of that attacker's SPN. And then we're going to relay that directly to the web enrollment service of the ADCS uh certificate authority. Once their certificate authority accepts that Kerros relaying, then we're going
to simply request a certificate on behalf of the victim. Once we have a valid certificate, we can effectively act as that respective user or that machine object. Uh so here's a quick visual of that. There's a tool called Certipy. If you haven't played around with this, really easy for you to mock up. We'll talk about that towards the end. Set up the relayer poison DNS, get the certificate from that specific machine account, authenticate with it, set it in your environmental variables on your attacking machine. Um, and then we'll do some impersonation, which we'll talk here in a second. It's really not a main focus of the talk, but you can expand the impact by doing this built-in
kerros uh impersonation. and then we can access the file system of that respective machine. So I have the commands for you but let's look at it in in this specific demo. So Kerros relaying ver uh via the network spoofing. So this was the first method we could get that machine in the middle footprint.
All right. So we got certify domain user. We're going to go ahead and find any certificate authority based misconfigurations. And a lot of the times the output is accurate, but if you've messed with certify, just know you should always double check that work. And we can see that ESA is in the environment because the web enrollment endpoint is enabled. And now we're going to relay. Uh I was supposed to pause there. Oh, there you can still see it at the top there. So we're going to target a domain controller. We're going to say our victim is a Windows 11 client and we want to request the machine template of the ADCS server. And now at the bottom, we're going to
set up our IPv6 spoofer. So again, when I do any of this networkbased machine in the middle stuff, you always want to be as specific as possible because if you do it against the whole network, that's when you get get the nasty grand emails, that's when you get the client calls that you do network, whatever. So keep that in mind. And eventually, I'll pause it there. We were able to poison one specific client. And as you can see there uh right over here we have a pfx a certificate file for that respective client. Now I kill it. Boom. With that we can authenticate and get the nth hash of that specific client. Right? So at this point we've
compromised that respective computer object and with that once you compromise a computer object you can do this fancy thing called S42U self and kerros which essentially means if I have the computer object uh compromised we can if configured by default there's some nuances here but most of the time this works we can impersonate a user in the domain on that specific client machine or server. So if I compromise a computer object I can then act as a domain admin as an example on that respective machine and most of the time domain admins are highprivileged users in clients not always though if the environment is pretty hardened they're going to separate that they'll have workstation admins server admins or maybe even more
uh separation there. So here we're telling Kerros, hey Kerros, I want to authenticate to you now and I want to do it as a domain admin and I want to do it for the CIFS service which is for file servers and network shares. And then I switch my TGT I check out the shares and there is the C dollar share. So I'm effectively an admin user on this specific client when I never was. I was just a regular domain user. Right? So we've now gone from regular domain user to machine in the middle foothold to poisoning to getting a certificate for that respective client. Once we get the certificate for that respective client, we can use some
Kerros magic uh self to for you. We'll talk about that in the next slide I believe to impersonate a domain admin after that smooth sailing right post exploitation whatever the case may be. Now worth noting that these tools uh a lot of the impact tools etc. you can run them like I am here in this sort of lab environment you know Linux machine to uh victim machines etc. But because a lot of this is networkbased you can also run this from a let's say a cobalt strike beacon or a mythic agent through proxy sock proxy. So you don't necessarily have to be on the network to leverage some of this tooling. you can proxy all
of this traffic through an implant of some sorts which make this makes this a more realistic scenario if it was a thread actor. Majority of the time they're going to proxy a lot of this traffic back and forth and that is the first one. So here's the S4 to self. Uh I just wanted to quickly mention it again I it's not a main focus of this talk but you can impersonate users as long as you've compromised the computer object itself on that specific device. That's how this sort of plugin I believe they reference it as a plugin. Um don't quite recall what the official extension that's what it is. I wrote it down. Awesome. uh Microsoft calls this a
kerros extension uh used for delegation and things of that nature. So builtin always a thing. Can you prevent this? Yes. Uh you should make sure that all of your domain admins tomorrow are not allowed to be impersonated. Like do that tomorrow, right? Because a lot of the times when we compromise a computer object, we're going to impersonate your domain admins because they have the keys to the kingdom. uh we cannot do that if they're in the protected users group or if you check the box that says do not allow delegation for this user. Again, not a focus on this stock, but worth mentioning because this falls into your post exploitation trade craft. All right, we're about 30 minutes in.
How we feeling? >> Awesome. Now, Besides Augusta is awesome. I've been here before. Love the people. Love the vibes. They've got swag for y'all apparently. So, I'm gonna ask you a quick question. Uh, I'll just pick somebody. We haven't talked about it in full detail, but I've already mentioned it. What is the second way we can get that machine in the middle foothold? Anybody? We've talked about the network aspect. What's the second method of getting machine in the middle foothold on the network? >> On demand. Who said who said that? Right there. There you go. Free awesome book. Can't beat that. All right, we got two more of those. So, keep keep your wits about you.
I've always wanted to been to Ireland, by the way. I'm just a wannabe. So, anyone watch Outlander? No. Out. Okay. Two. All right. Man, y'all y'all sleeping on Outlander. That's a great show. All right. Cool. Let's Let's keep going. Uh Relaying from SMB. Let's talk a little bit more about this. James Forshaw or Forsaw, uh, amazing security researcher. I think he's still at Project Zero, Google Project Zero, maybe. He's done like a ton of stuff regarding Kurros, one of the pioneers, if you will. Uh, so he found that when an SMB client builds an SPN, they don't follow a simple format. Okay? Uh, they have this weird sort of gibberish at the bottom. If you can see
there, you see all those A's. Very peculiar. And he did a little bit of research on this and he basically figured out that when Keraro's communications take place, respectively if you're trying to communicate with an SMB service, they add like that those additional strings which sure, right? Uh it's called cred marshall target info. So very interesting back in 2021. So if you want to exploit this, you can effectively do a DNS record registration for the target you want to go after. Right? So if you want to if you're able to, which depending on their environment, you might be able to uh as a regular domain user, you can create a DNS record registration and what'll happen is you point that to your
attacker machine. And so what'll happen is as people are using that service because that DNS entry is pointed to you, they're going to go through you again gaining that machine in the middle footprint. Um, now there are some limitations there at the bottom, but honestly like those limitations are not bad at all. Something to do with the DNS name and how long it is. Um, something to do with the Marshall buffer. None of these limitations really hinder you unless you have an environment that is monitoring for that, detecting for that etc. So when we look at relaying from SMB uh we want to look at this cred marshall info and how can we exploit it. So we've got this DNS
registration and we want to get this machine in the middle footprint. Once we have that, once we have the machine in the middle footprint, we're ready to go. We're ready to relay those Keraros credentials. And that's what we're going to do next. Uh, so here we're going to relay from SMB to SMB. Okay. And again, I had to write the steps down because it's a little more involved, but once you play with it in the lab, you're good to go. So, we register that malicious DNS record. It'll have that weird string in the middle with a bunch of A's. We set up our curb relay. uh we then coers a machine object to authenticate to us. So
you you you'll get to see that. Uh and then it's everything else we just saw. Once they communicate with us, we relay the credentials, get a certificate, business as usual. All right, let's quickly walk through the steps and then I'll show you in the demo of how this will work. Register a malicious DNS with the Marshall data pointed to your attacker machine. Right? Check. Set up your relay with curb relay X. Again, Pi Python written tool. Then we're going to coers authentication from the victim using the one of many. It started with printer bug spool sample whichever you know C or Python version. It started with the printer bug, but then many more methods of doing that have come out since and
continue to come out since. So we coersse. We when we do that, we get that machine in the middle footprint. We generate an AP request for that real target. We connect using the valid AP request. We relay it to the SMB server. The SMB server says, "Yep, you're good to go." And then we access the admin shares. So here's the steps in full. Again, these will be in the slides when they come up, so you don't have to take a screenshot of this. This was really just more for documentation and for when you want to try this out later. And let's go ahead and relay again just with the coercion this time. All right. So step one,
we got to register those DNS records. Python tool again called DNS tool. I believe Durkjan wrote this one. We're the domain user. We're going to add that record for the client. Notice the marshaled string there. We're going to point it to us, the 100, which is the attacker. And then we're just going to specify the DNS server and all that fun stuff. So everything works as intended. And we're going to do this a couple times if we want because we can put it for various different servers, right? We can have various different victims and they can all point to us. That can expand the attack surface essentially. But as you'll see later on, as an attacker, you
got to be careful with how this looks from an opsac standpoint. So here I switch from the Windows 10 client and then I point this DNS uh record from the domain controller to me as well because I can just sit here and spam as many of their computer objects as possible. Register this DNS entry and just point them all to me. Obviously keep in mind depending on the environment you might be generating a lot of traffic for yourself and you might tip your hat to the defender. If you're a defender you'll like a slide here in a bit. Uh this is really easy to detect. But you'd be surprised how many don't actually. Hold on. No one has ever
caught me with this. Has anyone actually gotten caught using credit marshall info in an environment? Okay, so yeah, defenders, like this one's for you. This is a good one because now that I think about it, I don't think I've ever been told this uh on a on a readout. Cool. So, here we're just doing a quick lookup to make sure that the registration has taken place. I'm quering the DNS server directly. And as you can see, let me pause it. As you can see that client string and the domain controller string in the lutusdomain points to my attacker machine. So we have basically the first half of the equation done. Now all we need to do is
essentially wait or we could coers the authentication to take place. In this scenario, I'm using uh WSP coerc, which is one of the newer methods that's cooking for me. And at the bottom, we do the coercion. At the top, we're going to do the relay. So, we're going to set up the relay just like we did before using the machine template pointing to the Windows 11 client machine object. And then at the bottom, we'll just quickly kind of pause as we go. We're going to use that coerc method and we're going to say hey I want you to authenticate to this domain right the marshaled string which points to me share using the domain user credentials we can
do this and as soon as I coersse that machine object you're going to see the authentication come through and at the very top you're going to see that it comes through my relay just like we did for we have that pfx for the Windows 11 client. With that we can get the machine account hash. With that we can create a ticket granting ticket.
Again, full Kerros, no NLM in the environment. That's fully disabled, not working. Uh some of the Impaca tools don't actually have the Kerros code in them. So, I found that out the hard way as well. Uh you'll have to do some manual steps unless the tools obviously migrate to leveraging Keraros from from the default stands. And then once we're able to get the Windows 11 client, we're able to do the S4 to use self impersonate domain admins. Once we're a domain admin impersonated in that machine object, we can interact with the CIFS service i.e. the file server and get full system access. And then here you go into more post exploitation whether it's putting an implant or getting rce whatever the
case may be.
All right. So again for CIS admins, how many group policy? Yeah, group policy object sort of line items should you be modifying to get rid of NLM? Does anyone remember the number? >> Three. >> Exactly. There's the client side that you have to disable. Uh the young young fella right there >> right right there in the sweater. Yeah, we got the client side that we have to disable on the server side we want to restrict it. And then on the network side we have to restrict it. So three different settings and they're all like on top of each other so you can't even miss them. All right. A notable mention of this presentation was actually a flaw that a few people in
the industry literally discovered at the same time because everybody's now starting to migrate to Kerros exploitation in general. Um, but one of my co-workers discovered what he called loopy ticket. Uh, but it's it's essentially a reflection attack on Keraros. uh this was now patched but if an environment has not patched this this is a full way of doing the last step that we did without credentials so it gets pretty wild and you can escalate to domain admin that way as well uh I'm not going to go into detail of it but I put it on the slide because it was just patched in June we still see it it's still cooking it'll probably stay cooking for like another three months
and then hopefully the patch management stuff kicks in and you know the CVE goes All right, defenders in the room. What do you think of that? Has anyone seen a legitimate DNS record that looks like this? >> I mean, that's wild. As I was like trying to clean up for, you know, because when you record it takes like three hours to record five minutes, right? Um, I had to keep going back and cleaning this stuff up. I'm like, man, this is really bad opseack, right? Or is it? Cuz I've never been told I got caught with this. If you're not looking for it, it's good to go. So, if you're a defender, just pop in a quick query on
your SIM or your EDR, whatever tools you have nowadays, and query your DNS entries and just see if there's any of this AAA garble in there, the Marshall data, the Marshall string. And if there is, you may want to check that out. The the good thing is the attacker has to point to their attacker machine, so you kind of know where the attacker is or the pentester or whoever's in your environment. Uh, but yeah, this is a great IOC. So again, we can disable this. Go to old GPOS's, your old friend, disable it in the environment. Uh something we didn't talk about too much because time is of is of the essence is some mitigations
uh to some of this that's additional to the group policy object like I don't know let's enable SMB signing who still sees SMB signing disabled in environments right like it's very rare I would say maybe 5% of our clients have SMB signing enabled fully. There's always some stragglers out there and SMB signing helps prevent some of this relaying as well. So, as I finish up my presentation, you know, I I demoed a lot. There's a lot of configuration that takes place. And I did this because of a product called Ludis. Sort of a shameless plug here, but it's a product me and my my partner are working on. And this is fully open source, fully free. At the
bottom there is a URL. It's not up yet, by the way. I have to do a little get push, but it will be up at the end of this weekend, if not Monday, depending on how I feel tomorrow. Um, and depending if I, you know, dinner with friends tonight, all that fun stuff. But Ludas Keraros Relay, it'll be on my GitHub. And if you have a Luda server, hopefully some of you do. Uh if you don't, check it out free and open source. You can run through a lot of these Kerros relaying scenarios similar to GOAD. It'll be on GitHub. Okay. So if you want to play with some of this stuff, you can roll out a fully quote
unquote patch, no NLM, full curros, full scenarios, but you'll be able to play with this. On top of that, it's going to have an elast elastic server with agents. So, you'll have detection data as well. So, you don't necessarily have to go in there, configure your own SIM. It'll it'll be ready. So, you can play with the attacker aspect. You can play with the defender aspect and hopefully use some of that data and some of that labbing, if you will, to bring it into your organizations and start getting after this problem. So in conclusion, I think NLM is going to be here for at least another 10 years. But if you're in those mature environments, Kerros
relaying is what I think the next hotness, right? You should be using it. You know, start messing around with some of the tradecraft. I think it's really untapped at this moment. I think we're only going to continue to see, you know, uh, Kerros being used from an abuse scenario. Not to mention Microsoft doubled down on Kerros and now has the Entra ID integration as well. So Kerros is not going away. Not to mention they're also rolling out I haven't checked on it but they're rolling out a local cre distribution center component as well on the clients. So it's staying. Kerros is not going anywhere. If you're not familiar with the protocol, if you're not familiar with the abuse
scenarios that have been around for a very long time, high ROI for you to go out there and get some of that information, some of that knowledge. Uh, I think the attack primitives are like barely scratched the surface. I can't wait to see what other people do with it. Uh, I used a lot of reference for this presentation. I just started copy and pasting them as I'm building the slides and working on the research to be honest. So, there's about three slides of this. Uh, if you're one of these people, thank you. Great content, great information. You know, I couldn't have built the presentation without the resources and the information that's readily accessible to me. And that's pretty much
it. Thank you guys for listening. I appreciate everything.