Stop Writing Malware! The Blue Team Has Done It for You

Show original YouTube description
Show transcript [en]
guys welcome to track two uh this morning
led by Alberto Rodriguez
thanks this is stop writing malware the blue team has done it for you by the time I finish this sentence over 200 unique binary samples will have been submitted to virustotal this is your real enemy if you're an offensive security practitioner it's warehouses full of servers running machine learning algorithms doing all these detections against your binary trying to determine is it malicious or not but what if I told you that there was a way that you could bypass all of this instead of getting your code run through these warehouses of machines you could get a green stamp a check mark a lock icon that says this is trusted we don't need to do any more analysis
that's what we're going to talk about today in this talk so my name is Eric hunstad I'm the CTO at 6th gen a cyber security uh consulting firm out of Annapolis Maryland I'm also the adversary simulation leader on that team I'm on Twitter as bad sector labs and I run a weekly blog where I scroll through Twitter and find the interesting things so that you don't have to hey good morning everyone Alberto Rodriguez I work at PayPal doing cybery things and you can find me on Twitter as well and uh yeah I hope you guys enjoy this talk it'll be great all right so today we're going to go through the state of offensive security
tooling this is everything from remote access tools to actions on objective tools your memory dumpers things like that we're going to talk about how these tools are getting detected we'll talk about how people are starting to write their own c2s and what that entails we'll introduce a concept called Trader wear and then we'll round it out with some detection ideas to help The Blue Team out all right so offensive security tools a lot of you guys know these everything from your Cobalt strike probably the most popular but there are a bunch of commercial tools that you can go out and buy that will give you remote access to systems as long as you run a binary or
load something in memory those are the commercial offensive security tools a lot of names up here and then they're open source versions of these same things they accomplish the same goals and there's so many of these Frameworks too many to list on a slide we've got some logos up of some of our favorites but this is kind of the space that we're talking about with offensive security tools these are becoming more and more detected every day they're known signatures if you just download the latest open source uh C2 framework off of GitHub it's going to get detected as soon as it hits disk from defender or whatever EDR that you're running and that's a good thing it should be
they're also Advanced uh signaturing and fingerprinting techniques like jarm and jaw 3 jaw 3s these will actually scan a server determine its TLS stack and then see if that matches a known fingerprint of a offensive security tool or a team server or something like that then people have written these rules like you see in the pictures here where they're looking specifically for those names you saw in the keynote uh Travis ormandy's name is is now a signature for malware and likewise some of these authors are also being detected and then on the right side I just did a code ql search for Cobalt strike Yar rules on GitHub and had thousands of hits so there are specific Yar rules
looking just for specific commercial open source security tools and commercial security tools and this is only getting more and more intense so you can see this graph is going to the Moon everyone is scanning for Cobalt strike and these offensive security tools so if you're using one of these know that you are becoming kind of a target for the blue team and the uh you know offensive blue teams and cyber threat intelligence is confirming this uh Cobalt strike by by almost 10 times more than any other tool is being used by actual adversaries so the adversary simulation tool is now becoming the actual adversary tool having become a self-fulfilling prophecy perhaps there's also other open source tools
Mythic Covenant and sliver were used in 2021 for actual adversary attacks on on companies to deploy ransomware so you can see the table on the bottom shows how many attacks where we're using those tools and basically if you can stop using Cobalt strike or those tools maybe you'll get around some of those detections so naturally what does everyone think well fine if those are getting detected I'll just write my own how hard could it be there are tons of Open Source E2 Frameworks the last time I checked there were 97 on this website called the C2 Matrix that attempts to track them all but there was even One released called Havoc framework just yesterday so
they're constantly coming out everyone thinks that well easy I'll just write my own C2 they don't take into consideration how difficult it's going to be to maintain these things Dominic shell here is uh with MD SEC who released the Nighthawk commercial OST and he said it was a full-time job just to do the QA testing so imagine you've got to make your C2 framework work not only on your test box but also on every box that you could encounter in a customer environment so your old Windows 7 machines maybe even a Windows XP machine is it going to cause problems on that it was a full-time job for a year and a half for two people working
full-time for for Dominic So today we're going to say that's maybe not the way to go what about this thing called Trader wear so what if we take software that's already developed to be stable cross-platform work on everything it's already trusted in the environment and what if we turn that and use that for red team goals so Trader wear is software that betrays the trust place in it to perform these malicious actions and it's going to allow you to do your red teams without those detections this isn't a New Concept we're not uh we're not that novel it's been around for a while this is one of my favorite tweets that says the only difference
between an antivirus and a root kit is a malicious intent and today I think we're going to show that that is very true but first to get a feel of what the blue team is working with I'll hand it off to Alberto to talk through that all right all right you guys hear me okay in the back thumbs up cool I'm Gonna Keep My Water just because my throat's a little itchy um I'm from Florida and in case you didn't know it's been raining there a little bit so yeah fun times all right cool so defensive primer right you know we're familiar with these tools like Sim EDR xdr whatever right we have these Telemetry enhancers such as sysmon Etc
that can collect better data for us to enable our security operations right we're all familiar with these tools and usually we deploy them in our environment to get better visibility better actions on the the defensive posture that we're trying to get at so we've all seen this life cycle from an attacker perspective this is yet another one of those uh we just wanted to map what sort of software Solutions are uh and what's the term English is evading me involved there we go thank you involved in each of the faces right so you have you know the reconnaissance phase previous escalation Etc I'm not going to sit here and talk through all of these vendors but the point we're trying to
make with this slide is there's a way to do a phase of the operation with known trusted software vendors Etc okay and I just want to quickly focus on the end there exfiltration and complete mission um you know the the concept of exfiltrating data and getting your objectives out of the environment from I don't know OneDrive as an example is becoming more and more of of de facto to be successful right so keep that in mind if you're a security analyst monitoring your network when you see a lot of OneDrive traffic coming in it might not necessarily be what you think it is so for Recon right I love that Meme it's great okay anyone familiar with rocket
reach sales people raise your hand boom it's great unfortunately though the free tier sucks I think you get like five only so test that out if you're a red teamer but you can get quite a bit of information if you target an individual from rocket reach excellent platform we have chart Lube this was not modified whatsoever your targets yes all right you can map your targets out with these this type of software again we have a lot to go through so I'm not gonna discuss every detail of the software itself but definitely check it out finding assets we're all familiar with things like Showdown Zoom I Etc there's a million one tools out there that you can perform
your recon without you having to again build your own which is the whole intent of this conversation attack surface mapping uh software spider foot's been around for a long time it's open source you plug in one domain you click go you go get coffee and then you get sidetracked because your kids you know on top of the room all of a sudden and you come back and you have a plethora of data around your target infrastructure you didn't have to code this yourself it's readily accessible for you I'm going to turn things over to Eric so we can discuss initial access all right so once you find your targets you got them on Rocket reach you send
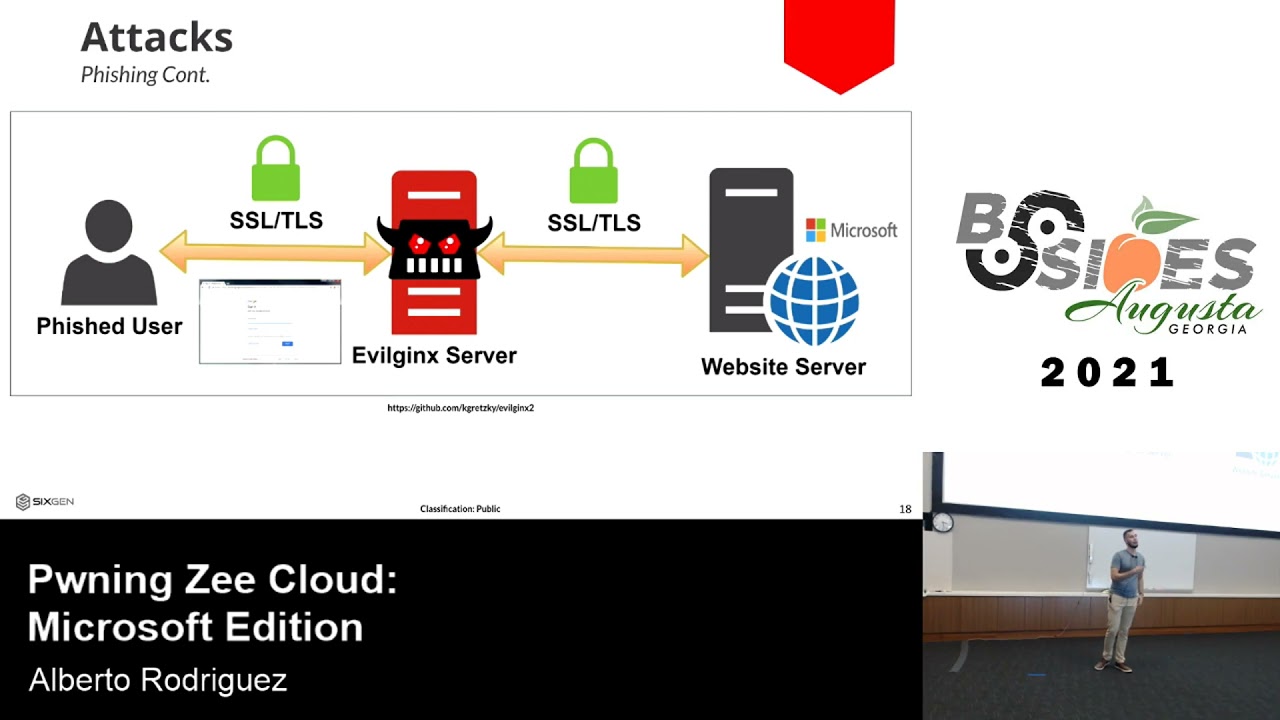
them some emails how are you going to get initial access into that machine this is normally where you'd write a custom loader trying to get around the EDR that's maybe on that desktop or you've got to convince them to install some app that you wrote again trying to bypass EDR what if you just gave them a link to Chrome remote desktop and said hey I'm from it and I need to install something it's a priority click here and give me access Chrome remote desktop is already a trusted piece of software 0 out of 72 on virus total why are you trying so hard to evade EDR if you can just use what's already out there or
Chrome extensions this one's a little trickier if you can get them onto disk there's a way that you can load them with the dash dash load Dash extensions flag where it will load a unpacked extension and won't even tell the user so you won't get a prompt you won't get developer mode or anything like that and all of a sudden you now have a hook into that user's browser and as Things become more SAS heavy everyone's doing everything through a web app maybe you only need access to their browser to accomplish your mission it's not always about trying to get domain admin if their valuable information is in their browser that's where you want to be
another thing if you've ever run an installer 50 of the time it's going to be made by this open source uh tool called Inno setup and this is what creates that dialog box that you have to click through you know do you want to install it in program files and all that kind of menu there was a POC that came out where a gentleman figured out how to run Shell Code inside of this setup window so you can just put your payload directly into your Setup Wizard and the edrs aren't looking at what's happening in the setup wizard because they do all kinds of crazy things so you get very low detection rates and the user is
familiar with clicking through this and has already been trained to click through these dialogues and give you access basically so once you have access to a machine you want to stay there right you've earned your access we'll come back to persistence this is going to be the the heavy point of this talk once you're persisted on a machine it's time to to look around and see what else is around and how you can move to those other machines the the default for this one is Bloodhound I'm sure any offensive person in the room who's been in an internal network has used Bloodhound to map out the network it's a great tool but what if it was signed what if it was
trusted what if the organization saw something running instead of sharp Hound as malware sharp pound as oh we know that that's a good defensive tool well there's Bloodhound Enterprise the uh the new product from Specter Ops and it comes with a Enterprise version of sharphound The Collector that gathers all this data so if you can get yourself a copy of Bloodhound Enterprise perhaps that trusted version of sharphound we'll get you your data without any detections there's also a product called ping Castle mapping ad for attack paths is not just an offensive thing the Defenders want to do it too so let's use their tools to do that pincastle is another product that will do that for you will give you a
nice attack map again these binaries might be trusted in the environment that you're targeting and then of course all the big vendors had to join in ad managed plus tenable has their own Etc if you get access especially if the blue team is already running these products if you get access and just log into their big database of all their machines you already have that data and you don't need to collect it yourself in a way that could be detected this is one of my favorite products it's called run zero used to be called Rumble run it's made by the guy that wrote Metasploit excellent tool for finding Shadow I.T and what shadow it is that
that Windows 2012 box that you set up 10 years ago to test out that one web app or something and then you forgot about and it's still running off in the side and not being patched and could be vulnerable to who knows what so this is a great scanner that you can run once you're inside a network or even outside a network to try and find just all the assets fingerprint everything basically tell me what's on this network and where could I possibly go this is a great tool once you get to a Target that you need to do something more on you got to do some actions On Target
you know Microsoft Visual Studio has these Nifty and I had to double check with Eric I asked them like five times is it really called Ajax being used by a Microsoft and in fact it is right so you can actually a Jack the dll using a Microsoft sign binder binder that is called inject dll I mean that just blew my mind right uh driver abuse again process Explorer Explorer there's a drive kill EDR or 80 products in the environment so now you can tamper with security products leveraging again Microsoft signed binaries and I'm sure if you go hunting for these there's going to be more here's another one process hacker everyone here use processor fill in yeah great tool again
driver abuse uh signed binary Runners uh we use red JSM as red tumors for a long time right everyone use red JSM and then Ms build all these things were getting costs exe you can execute code using parts or executables which are again signed as well they're at the bottom default pack.nic there's tons of these living off the land binaries which you can leverage their sign you can leverage to execute your malicious code that you need sign memory numbers right Etc instead of dumping you know memory process from memory using mini cats why don't we use steam miners when you're a gamer yeah there's there's a little you can't really tell but there's a binary in the
steam installation which allows you to dump a kid's memory Wicked you can use your gaming race to do some hacking now as well obviously a bass I think that's that's the memory definitely well guess what not only if you land in an environment that has a bass and you leverage that capability or you can just bring it along right you can just yourself it's already signed it's probably not going to get caught this is very similar to the tactic attack the folks who did the solarwinds hack leverage you know they brought like their own version of a Windows that's vulnerable and then they leveraged it and their operations so again attackers are leveraging these you know I'm good
for data exploration you're gonna talk about in the beginning please if you have your notepad write this down there's this site called living on the land trust it inside we have LOL Biz LOL bass LOL everything buying for my daughter but now we have a lot okay which is all these awesome sites that will allow you to exfiltrate data you know legitimately quote unquote right I'm talking one drive cloudflare uh Google Drive uh Google that's great people think you're doing work but I mean technically you are people think that employers will work damn they're all over Google drive today for excellent traded data so that that's a method of you know getting rid of your
data Network without essentially tipping your hand off so now here's kind of a big chunk of the top I'm going to turn thing over to Eric so we can talk about persistence right so we're focused on persistence today and we're going to introduce what we call the Iscariot Suite so this is how we use blue team or CIS admin tools to perform our Command and control we're going to reduce your development efforts so instead of you doing all the QA and testing to get your software to work on every version of Windows plus Linux plus Mac OS make it stable every update you've got to have some crazy CI pipeline instead we're going to use
tools that are already doing that for us so we're using these trusted and signed binaries Within These tools to execute our code and this is going to minimize your detections and make it even easier to start off with we'll talk about Splunk all right show hands who's you Splunk or at least know what Splunk is right it's a pretty popular Sim you know it's like super cheap you can get it you know for the low low it's great um so Splunk right in case you didn't know what Splunk was you have an agent component and then you have like a plethora of server components so to speak and that server components that can be search head indexers deployment
servers which we're going to talk about right uh as a deployment server that allows you to centrally manage what you get the agents to do okay then you have your deployment client which is really the agent side of things so okay we got this deployment server over here we got this client over here they kind of talk to each other this one sends commands to the other you can see where I'm going with those and then you have a deployment app that app is kind of like the package deal where the deployment server right tells the client hey buddy you're gonna get this app and that app is going to contain things for you to do
execute scripts load some stuff right you see where I'm going with this Splunk as a C2 why not right why do I have to go build a custom loader you know pay some exploit Dev to do some fancy stuff just kidding keep doing that it's great um you know a lot of technical work which is hard let's be real if if you're out here trying to evade you know the Sentinel ones crowdstrikes Etc of the world it's it's not like it used to be right you can't just roll up and change a string and call it a day most of the times nowadays you have to understand those win32 API calls and really understand the EDR to evade them so
let's use Splunk as your C2 right we're going to use obviously the server as our server side which comes with a great UI by the way has dark mode for those that like that and it comes with an agent side which is the official Splunk Universal forwarder for for the Splunk folks in the room uh there has been some prior research done by this in the past so I'll link some of those in our get lab when we release the project which I think it's already out so on the server side easy enough I'm not a Splunk engineer so if you're a Splunk engineer you're like oh this is so manual I hear you just bear with me
all right you're going to configure it to receive data and then you're going to set it up as a deployment server boom done awesome on the agent side this is my implant right awesome we're going to install the agent we're going to set it up to be a deployment client you know this these are Splunk terms we're going to change the service name which you can do in Splunk that's awesome right a little upset consideration built in nice touch so we can change the service the service name we can enable it on reboot there's that persist side of things and then do the TLs change supports etc etc okay this is kind of how it looks the command line
side of things again you can modify that server's name to make it opsec friendly which is great and at the end of the day we're going to have a C2 framework over https cross-platform it's going to support all your different operating systems that you might you know need to have access to you can task it remotely and it's all signed binaries right and then you may say hey okay sign binary is like what else well virus total things are pretty cool as well right no detections whatsoever I'm talking splunk.exe Splunk d.exe Splunk Dash wmi.exe more on that later and then Splunk Dash powershell.exe again all signed by Splunk all our Gucci per buyers total awesome
what does Cisco have to say about this and I'm not picking on Cisco if you worked for Cisco or Cisco if you're listening I'm poor uh Cisco you know they have these exclusion lists on on their on their EDR I think it's called um amp right something like that Cisco amp so they exclude flunk binaries from triggering their alerts right like you need Splunk to work in most environments so sorry Cisco but thanks for proving the point a little bit worth mentioning uh about June of this year there was a cve that came out that was like I think it was a nine point something on the criticality scale it was two days after this talk got
rejected by Defcon by the way no no you know I'm just saying so two days after we receive our rejection this cve came out and the CV was super interesting because essentially if a user compromised a deployment client one universal forwarder there was a way to compromise every single deployment client that married with that deployment server through Splunk apps so again I don't know if there's like a coincidence or anything like that but this came out shortly after it just goes to show that the trust that we give to these security products are something to keep in mind when you're doing your don't kill me for this you're threat modeling I I know buzzword but when you're threat modeling
in your environment you should now be bringing this sort of Trader wear into the conversations and into the tabletop exercises so have a little demo for you uh let me go ahead and stand behind cool on the top we have Splunk sorry no dark mode on the bottom I have the Splunk server so that's the CLI okay so I have an agent installed and there's the version I pulled it up pretty new I did this like a week ago um even though the talk you know we've been working on it for a little bit I go on interact mode all this code will be available for you so there's a quick ipconfig now at the same time you see the Splunk
app is being sent to the client there it is Splunk C2 app obviously pick a upsec friendly name that is written a bunch of things will happen there at the top a little Splunk exe action going on awesome cool and then you can come back to the UI and then you have your output that's a pretty nice C2 framework right just like the standard stuff I mean we're not hating you can determine what source type you know you have you can organize it by the source as well so if you want to do fancy dashboarding you can as well there's my quick you know mandatory Echo statement into the desktop just so you know obviously there's code executioning
taking place so I'm writing splunking and there here I'm getting ready to show you so it comes with a full same capability right I can you know put a whole bunch of deployment clients in one server class so I can essentially execute code in the masses I can group them together maybe I want to Target the workstations differently than the servers for lateral movement and here in the last piece the wmipoc so for the wmi I'm going to pause it here for a second this is a splunk-wmi.exe it's an executable signed by Splunk Etc that will execute wmi query language uh syntax okay which is great I mean you can do a lot with W
I want to hear mess around with wmi yeah so full wmi stuff I'm I'm game for it and let me just fast forward it here as well foreign and I have the syntax there you can see wmi.exe is going to pop up on the top here boom signed again virus total has nothing to say about this this is great I don't think your edrs are going to scream too much at Splunk because uh then there'd be like trouble in Paradise on the vendor Department and I'll pause it here again there you can see the queries everyone here familiar with like women get object Dash WQ or yeah wql select star from win32 process or user
account or computer system Etc so you can perform your entire enumeration through wmi which again that's pretty awesome and it's going to be performed by a signed executable from Splunk so I mean and and hey I'm not a Splunk you know wizard but I'm pretty sure I can do some fancy dashboarding too right and make it look really nice so I didn't play around with that capability of the Sim but a gut tells me that you know it'll be good for your Ops if you do some dashboarding as well so that was Splunk okay again the co the code that we used is going to be readily accessible I think you can Google it now
there will be a QR code at the end you can trust us all right um just the final piece I want to hit on uh before I turn things over to the next product we weaponize edrs xdrs you know that whole shebang right that could be a whole talk on its own I'm talking The Sentinel ones the crowd strikes all those folks that have rce on your endpoints right we all know about it and you know it kind of like we openly joke about it at work but really you know hold the vendors accountable to providing those artifacts to understand what's good and what's not good you know within the realm of possibility from their products right what is the
Baseline what is the parent to child relationships what's really supposed to happen a lot of these EDR xdr tools I mean full-fledged software suite right excuse me you have our back right you have all the dashboarding all the reporting uh the code execution obviously you know it'll be a plus and a lot of the times when you have multiple adrs it used to be back in the days they like fought each other right anyone here like you installed one EDR and they started fighting each other I think nowadays they don't really fight too much I don't know I like my experience especially when I was a consultant I would install things on top of each other and I didn't
have too many issues like I used to back in the days right so keep that in mind because an attacker can bring in some of these software tools like an EDR anyone here familiar with like the ateras of the world right rmms uh zabix all these Jokers well they can bring them into the environment and it can really cause Havoc into your infrastructure there's uh you know obligatory Twitter posts from rastamouse himself elastic recently announced that you know they have like an EDR capability that allows you to Modern you know code execution et cetera et cetera so obviously red teamers on Twitter are like cool another rce tool right another C2 framework so turn things over for some always query
all right so we got this Splunk we got we talked about edrs there's another tool called OS query you might not have heard about this one it started at Facebook which is now meta they turn it over to the Linux Foundation but what it lets you do is write SQL like uh queries against any computer that has an OS query agent installed on it so if you're familiar with SQL syntax you can do your selects you can do joins where Clauses all that kind of stuff to look at information about your endpoints Facebook used it to just monitor their entire fleet of servers as well as their workstation endpoints and it's really powerful it's a great tool but it's also
signed and it comes from a trusted source and it's whitelisted on virus total so obviously we're going to see what can we do with it on the left side you'll see that's an example query where it's just looking for show me all the processes that are listening globally on an endpoint and give me their name the port in the pit so that's kind of an example of what you can do with OS query on the right side you'll see there are many open source as well as commercial dashboards this one's called Fleet and you can get a web interface as well as a command line interface to query your endpoints from all right so on the left side I've
installed Fleet and I'm connected to one of my test endpoints you'll see it has a lot of things like disk space the status the last check-in the first check-in your agent options how how long it takes to call in the TLs options sounds a lot like a C2 if you ask me there's no difference here between an offensive tool and what we're seeing with OS query on the right side there's an example query that I did in the web interface and it just shows you the power it's tying the process and the PID and the process name to the listening Port so you can combine all that data so that's how you would use it normally
so to recap OS query it has no noticeable artifacts and installs as a service so if you put it on a machine the user isn't going to get a tray icon or a pop-up or anything like that it installs in the background it communicates over https so everything's encrypted it's cross-platform across all three major os's you can task it remotely either through the command line or the web interface the binary signed by senior software engineer at meta and it does signed automatic updates so you can keep your agent up to date with the latest features it also supports this thing called extensions and so that is very interesting and we're going to get into that today with Iscariot OS query
and that's our extension for OS query that we wrote it's written in go and it allows you to execute binaries directly execute shell commands with a full shell environment it can run unmodified Cobalt strike Buffs if you've used Cobalt strike there's a module structure called a beacon object file or both that allows you to directly access the windows API through your process so you're not spawning or forking or doing anything like that it also runs c-sharp assemblies directly in memory in your same process space so we'll load the CLR and actually run those binaries for you and it patches etw and amsy so you won't get caught so here's an example query of us querying who am I slash priv with u
shell equals zero so that means we're just going to run the Who Am i.exe binary directly give us that output and put it in a a SQL table it's a little uh user unfriendly with output because you have to return an element for each row in the column so that's why you see a lot of repeats but don't worry we've cleaned this up into a nice shell for you can also execute shell commands with full shell environment so this is going to actually spawn cmd.exe and allow you to you know go into environment variables you can pipe commands together all the things that you would normally do in a shell you can now do through OS
query and these shell processes are going to be child processes of your signed binary from meta which is great Cobalt strike Buffs so if you want to get a little more advanced with your tradecraft and you want to do some uh low-level win32 API calls now you don't have to write your own uh you know low level C code for Windows you can take what's off of GitHub people have already pre-compiled these Cobalt strike Buffs and you can run them through OS query and so this is an example of just a simple one that's getting the ARP table from a Windows machine and again this is not forking or running any processes it's directly inside that process space
calling those windows apis you can even pass arguments to these Buffs it's a little bit dirty right now especially in the query syntax you have to know the type of the argument and pass it in that way but it is possible to give arguments to the boss all right let's see a demo all right there's no tricks up my sleeve antivirus is on so the latest Windows Defender on Windows 11 Enterprise I did turn off Cloud delivery and automatic sample submissions so that Microsoft doesn't get all my stuff right away on the left side you'll see the iscaria process is running as a child of os query D and so that's our sign process OS query D and then our extension is
running as a child of that I'm ssh in to the fleet server so this is the control server for all my OS query agents and I'm going to run our client that we wrote first it's going to give us the hosts that are currently connected to this system right now we've only got one our window Windows 11 test machine that's the one you can see in the background on the left it's going to ask us what we want to operate on and then give us four options of how we want to do it that's the four options I just went through so to start off with we'll execute a shell command and to demonstrate the full
power of the shell I will pipe a task list into a fine stir so you can chain multiple commands together and we'll see who's running a CMD on this box after a little bit it comes back and we see the user that's already peed in has a couple shells open and then there's us at the bottom running as services and we have a CMD to run this command chain if we go back we can execute exes directly without spawning a CMD and so this time I'm going to do that same who am I slash priv and this will task the agent to just run that exe directly and then give us the outpat output back in a
nice format it was a little too quick to see on the left side but it did actually spawn that exe and give us the output next we'll run a boss in this case I'm going to run the art buff the same one that we did in the in the slides this won't spawn any processes it's going to directly call those apis within our process context and give us the output back and these will you can run any Cobalt strike buff without modification they work out of the box same thing with c-sharp assemblies so here I'm going to run seat belt with just the anti-virus function of that to display the antivirus on this machine this is going to patch event tracing for
Windows as well as the anti-malware scan interface so you're not going to get detected by amsi or any product that's using etw this is a stock seat belt directly off of GitHub no modifications so you don't need to change anything about your existing c-sharp tooling to use it in OS query with this carrier all right as we start to wrap up what can we do about this and and what does it do to help us so we talked about how people have gone to creating their own c2s to try and get around the massive amounts of detections there are for Cobalt strike and other similar commercial and open source c2s unfortunately if you're a red teamer
it's hard to find time to do this that you can justify as a billable hour for a client if you're on an engagement when you go to an engagement they expect you to have a tool set that's going to be able to perform the objectives and help them get better at security so oftentimes people are doing this after hours or it's it's on overhead time and it's tough to find a way to cover these costs so if you're not a boutiquing red a boutique red team shop it could be difficult to get a high quality C2 that you know Works across versions and things like that also the barrier to entry to writing your own C2 these days is very high back
in the day you could take command run it through base64 and then decode It On Target and run it in memory and you'd be okay it doesn't fly anymore the edrs have gotten very good and the AI ml blockchain whatever Voodoo plus some big data it's actually pretty good so it takes a lot of low level knowledge you're going to be writing assembly you've got to know the win32 API in order to get around these edrs so our dream with the Iscariot Suite is we want to shift some power back to the red teams and say you should be focusing on making meaningful change to your customers instead of how do I bypass this one EDR for this assessment so
let's focus on the bigger more impactful changes instead of the cat and mouse game of get around an EDR
all right so again this is kind of a message to vendors right if you're a vendor out there uh you know we just want to say do your best we understand hours of limited Etc do your best to provide your customers with that deep technical knowledge of what your product does and what it can and cannot do right I'm talking parent to child process relationships how you're writing the service you know on that operating system higher you know persisting on that system whether it's a register key or a scheduled task Etc provide your customer with all this technical information so they can build detections around those specific products okay if you are a customer that doesn't use any
of these then you should be you know hopefully your vendor can help you you know your existing products can help you with some of this but if you don't have that from your vendors and your security products you should also be building out detections and preventions against Splunk right if you don't have Splunk then look for it right if you don't have always query go and look for it okay we want to ensure that everyone you know from today on in case you didn't know I'm sure many of you did know that you're tracking all the capabilities of the many many security products that are out there and you find a way to prevent or detect them in your environment
especially if you're not using them right because we've all had this connotation and security especially on the blue team side and I I remember when I was a blue teamer as well that oh you know it'd be it'd be horrible if somebody gained access or Splunk cluster okay yes that makes sense but what if that's not your Splunk cluster they're just hosting it on AWS your attacker is and they're using Splunk to do their entire operation right it's a different bit you know it's a bit of a Twist as our conversation before whether it goes from we need to defend our defensive posture yes you still need to do that because if they pone that then you're
you're still done but now we're also going to have to detect and prevent against these security products that are not in our environment okay and that's kind of the messaging with this specific talk is try to alert for or try to prepare for Trader wear there might be an official term for it we think Trader aware makes sense and yeah just made sense so we've got many references for this talk this talk started as like a conversation between Eric and I probably two years two years right where we were just like yeah like Sentinel one rce cool and you know we just kept bickering about it and then we're like you know what we're gonna make a talk about how
Trader work can really be a security implication to the industry as a whole so there's a ton of references that'll be on the gitlab repo uh previous conferences previous white papers Etc you can find them all here there's a lot of people to thank for as well because we obviously pulled some code from the internet we're not in the business of writing and Reinventing the wheel in case you didn't notice so you know we definitely want to give a shout out to those folks there at the bottom definitely check out that Lots project uh personally speaking I think that's going to be pretty big coming up especially your detection engineering efforts where you have pretty much
legitimate traffic always leaving your environment and you're not going to know which one's which and especially when TLS 1.3 is like widely adopted and they do some you know Security hinding on that effort as well so here's our contact information Eric over there a right over here QR code to the get lab link so you can check out the code you can check out these slides which I think are up as well if not we'll get them up there as a PDF for you uh so you can you know maybe dish it out to your to your co-workers Etc and uh you can follow us on the socials um there's Twitter LinkedIn Etc thank you guys for your attention and your
dedication thank you guys for being here and I hope you have a great rest of your day oh we uh before I forget I was probably gonna get