Ransomware: The Playing Field has Changed
Show original YouTube description
Show transcript [en]
All right. Uh, thank you, Marlene, and welcome back to Bside St. John's for 2023. Uh, we're going to kick things off with a talk that I'm really looking forward to. Um, here is Glenn Stacy. Oh, don't set me up to fail. Start off strong. Y Okay, perfect. Yeah. Just got to hook up my laptop. We'll be all set. Sound check.
Make sure the sound works on the
computer. Let's just do a check check check. I'm going to give it away. Perfect. Alrighty.
and make sure this works. All right. Um, my name is Glenn Stacy. Um, I'm the regional director for Forinet for all of Atlantic Canada. We've grown a lot. I've been with Fordinet for about eight years now. Uh, we've grown a lot in Atlantic Canada. Um, I actually live here. So, I'm from Newfoundland. Grew up in Newfoundland. Grew up in Mount Pearl. Moved away for a little while and now I'm back and I love it. So, I'm in Conception Harbor, uh, Newfoundland, but I am the director for all of Atlantic Canada. Uh, seeing everybody here, there's a lot of faces that I recognize over the years. So, it's, uh, I've been in this industry for 27 years now. uh as
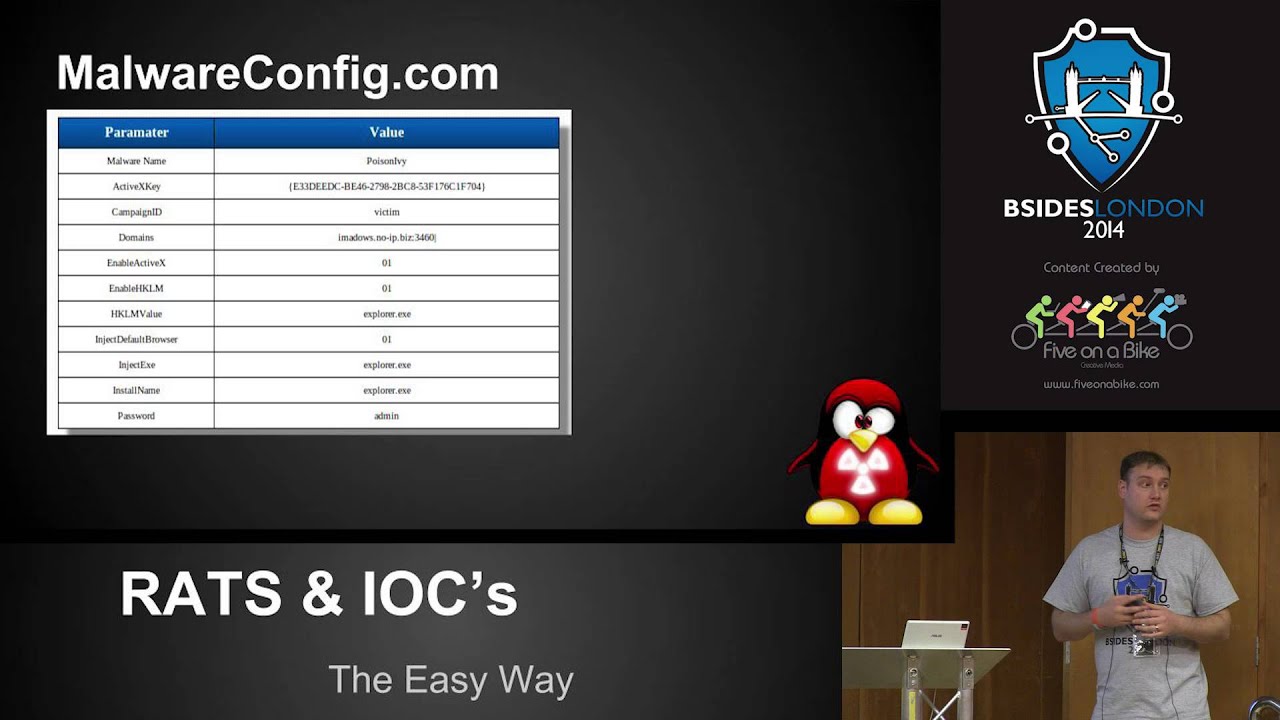
an engineer for 26 and a half of those and regional director for the last 5 months. So we're going to go through some stuff the topic that was on the actual thing. I'm not doing that. We're I'm not we had a different speaker going to do it and it was all super high level and yeah that's not me. So I spent two days with uh one of our inside of our organization with a guy that actually goes around in deep web dark web and I've seen a lot of cool stuff. I got really excited. So I created a whole presentation around what I seen and a lot of it is towards ransomware because ransomware is actually not the same as
it used to be. It's very very very different than what everyone thinks it is. So let's just go through it. So let's go through episode one. So this hasn't changed. The fund the reason why most people get hit with ransomware is financial gains for these organizations that are doing the ransomware against you. Okay. One thing that has changed though is the espionage piece. So that's getting bigger and bigger. We've seen a lot of it now, especially around what happened with uh the Ukraine. There was a ton going on there. There was denial of service attacks against the organization or against the country trying to disrupt anything that was going on from a military standpoint trying to get
internal information from the government. Um yeah, they were three and a half days trying to stop the de dos attack from Russia against the Ukraine and it was all around the espionage side of the house. This is an interesting slide. This actually surprised me immensely. 6.9% of ransomware happens in fishing. 6.9 Four years ago that was 89%. Four years ago now it's not. Valid accounts is the biggest thing now by far the biggest thing. So if you look at this valid accounts exploit public facing applications. So anything that you have out there that's public facing and external remote services is where most of the ways that they're getting in to hit you with ransomware. So if you look possible to
mitigate 82% of intrusions just by changing your role base access that's the way it is today. Used like I said used to be fishing and you used to get a file through email that you clicked on some kind of botnet that caused you all kinds of issues. someone downloaded some malicious piece of software. It's not that still happens, don't get me wrong. It's just not the number one way people are getting in. Uh also, for the most part, part uh antivirus will not work with ransomware today. And I'll show you how that works. The zero malware attack. So in our ultimate wisdom as IT people, we've created all these security capabilities within our OS. So Microsoft has built in Bit Locker
inside of the Microsoft OS which does what? Encrypts your hard drive so that people can't get your data. Well, how many people here are actually using Bit Locker in their organization to encrypt their hard drives on every machine? Yeah, not many. Right? We're what less than 1%. But this is still on the machines. So what hackers are doing is they're getting in and they're actually encrypting you with your own software. There is no bad there's no malware. There's no malware. How is antivirus going to pick it up? It's not it's not going to see it. And by the way, all of these are different things that people can get in because it's built into the OS, right?
So the days of oh you know I downloaded a bad file and I clicked on it and it created some kind of ransomware which the last going off when it was super prevalent was about 18 files that would get built on a machine. So again antivirus wouldn't work then either but now they're actually using your software against you. There is no malware here. No malware no antivirus is going to pick it up. like this is really surprised me that this is actually one of the number one ways today that they're actually encrypting you. So let's go through something. So big game hunting most ransomware organizations are still going after big organizations with big paybacks. OT OT is the number one thing that
people are going after today. So when we went through everything on the dark web, well deep web first and I'll talk about the difference between the two uh a lot of it was a lot of the work that hackers are actually creating is around the OT side of the house. It's the biggest opening for most organizations today because let's face it OT environments have been they've been in place for 2530 years. OS wasn't created 25 or 30 years ago for O for OT. There was no security in the OS. They're also headless. There is no two-factor authentication. There is nothing for an OT environment. So that's a good place to go in. Also, it's very disruptive, right? Take out a
power grid, take out a healthcare infrastructure, take out a government, all based on the OT side of the house. But there's lots of conflicting information. So veh published that 80% of all ransomware gets paid. Uh other organizations say that they don't pay ransomware anymore. Cyber cyber security insurance companies especially in Europe are saying we're not going to pay out for ransomware anymore. Uh it's just too costly and if we keep paying the the the ransom then it's going to keep the business alive of ransomware. Well near the end we'll go through a debate on that of whether you should or you shouldn't. But really what we're seeing is in 2021 there's a 10% increase. 2022 there's a 16%
increase in the amount of ransomware. And a lot of that's got to do with ransomware as a service. So these organizations are actually now created. Actually I'm going to show you kind of is it on the next slide? No. I'm going to show you organizational um how they're built. They're actually built like any other organization on the planet. Their help desk, I wish every help desk on the planet was as good as their help desk. And I'm going to show it to you. Very cordial, super business-like. You think it's all cloak and dagger and some guy with a wife beater shirt on and stuff. It's not. There was suits and ties and CFOs and CIOS. It's
insane. So, when I was on the dark web, we spent about two hours kind of going through stuff. You can buy anything you want on the dark web. Like seriously, anything. And the reason why I have up even mermaid tales is because for $10,000 you can get an authentic mermaid tail on the dark web. It's everywhere. There's everything from drugs to guns to to a tank. Could have bought a tank day before yesterday if I had the money. It's all there. Like everything is there. So this scared me. this slide when we went through and looked at the numbers only 4% four so think of the entire internet worldwide everything that you search for on a regular basis YouTube you know
anything anything Twitter Facebook any kind of news anything that's out there only 4% makes up searchable information 4% of the entire internet makes up searchable information 96% % of all traffic on the internet is not searchable. Think about that for a sec. 96% is made up of deep web and dark web. So money laundering, guns, drug control, everything else. And here deep web, that's credentials. That's all information. Medical records, student records, everything else. That's all in the kind of the middle, not as dark as as what's down here. So here they're gathering information. Down here they're doing a whole lot of other stuff. Uh that's completely legal and and not fun. So from a business standpoint, so
it used to be you'd have one organization that did everything. It's not like that anymore. So we have access broker. So this is a company and I'm going to use the word company because that's what they are. They build entire infrastructures just to get credentials from you. They build social social hacks. They build anything you want. They'll come up to get compromised credentials from you, but that's all they do. Then you have this ransomware as a service person. They're the ones that actually write the tools to actually create ransomware on your environment. So these are all the deep tech guys that actually build all of the malicious tools that people will use against every OS, every software vendor on the planet,
every hardware vendor on the planet. That's all they do. So these guys get paid on any kind of ransomware. These guys get paid on any ransomware, but they get paid less than this guy, which is the affiliate. He takes the information from both sides. And again, these are three different companies. There might be a little bit in the same company, but overall, this is three different organizations that are partnering together. They partner together to create this. These guys get hit the mo or get the most money out of a ransomware because they're taking the biggest risk. They're the ones that are actually hitting you. They're the ones that are actually executing the ransomware against you. So, they take
the biggest chunk of whatever they get out of you. Okay, we can't think of this as cloak and dagger anymore. These are very organized wearing suit people. It's it's insane. only way to stop ransomware is to kind of make the field a little le. So what they did the SS FSB in Russia they kind of said that they took out um Revel our evil some people call but it's that they call themselves Rebel. So but give me a break. 440,000 that's nothing. It's nothing to these guys. They're billions. they're making billions and billions of dollars. So, United States, if you offered a reward, if you know of any person that's associated with Revel or uh Kanti or
um oh, what's another one? Kilnet, they'll give you $10 million if you can point them out and prove that they're actually part of that organization. that'll help, but everyone's scared to actually give up the get the $10 million because now you have a a very big crime industry coming after you. So, until that levels out, the riskreward kind of levels itself out, you're going to see this stuff. It's not going it's not going to change. The guy that hacked Yah Yahoo and got all the emails, so he got about 2.6 million different email addresses and credentials. He then sold those to five different hacking communities for $318 US per per credential and he sold him five
times. He got arrested. He was in in Ashawa, Ontario. So he got arrested. So they took all of his, you know, he had a Hummer and he had a Maserati and all this kind of stuff. They took all his stuff, but they couldn't find his money. So they put him in jail. But it, let's face it, it's a tennis club jail. It's a white collar crime. He was in jail for three years. They sentenced him to seven. He was in there for three, got out on after three on good behavior. And no one has seen him since cuz no one found his money. So now he's a billionaire. And he went to a tennis court for three years, right? I'm sorry,
but I'm a straight shooting, honest individuals. They come. Someone offered me to go to if I went to jail for three years and came out with a billion dollars, I'd go to jail for three years and come out with a billion dollars. That's that's family life-changing money forever, right? Um, yeah. So, again, as as nice as I am, it would be it'd be scary. This is also something interesting. So this actually shows uh most active ransomware campaigns that are going on which is a lot of them. This is the countries that are getting hit the most based on this is as of two days ago but look where majority of it's coming from. A lot of it's
coming from Asia. Now having said that how do we guarantee it's actually come from Asia Pac because it might be Russia going through Asia to actually get out to do the stuff. So takes some you know just look at the numbers in a little bit of just but still it's still massive. So as organizations we should be putting in all kinds of geo filters of where the traffic is coming from. Be very specific in where it's coming from u to stop some of this. You're not going to stop it all but stop some of it. So this is uh I'm going to show you two videos. one from Revel and another one from uh Kilnet. Uh these were posted in June of
this year. And by the way, found these on the dark web, which is kind of funny. If God rules Russia, then who rules Europe? That's right, the banking system. No money, no problem. Rebel is sufficiently familiar with the European financial infrastructure. See you soon. This is not a DOS attack. Games are over. We call on all active groups to engage in destructive activities against the European banking system. No money, no weapons, no key regime. This is the formula for the death of Nazism and it will work. Within 48 hours we are launching this global company. Nothing will save you and this is not a warning. I am just informing you. You have never seen such problems before. We are killed
it. Yeah, that was just June. Like it's insane this I mean that's really cloak and dagger. That's something that's going to come out of Mr. Robot TV show, right? I mean, it's it's it's kind of interesting to see, but they're still doing it and they're calling out to other organizations to join in with them to actually do it. And when I say organizations, I mean other bad actors. Okay. So, it's getting more and more and more organized. So, let's go into ransomware attack real quick. So, this is this is the business of ransomware. It's exactly what this is. So, we have these Crimeware producers. They're developers the same as every developer in here except they're
creating all kinds of nasty stuff. They have senior developers, junior developers. They all work from a central source code. They turn around and they sell their information to criminal organizations. As far as I'm concerned, this is also a criminal organization. They sell that stuff there. criminal organizations have sales, marketing, support. They have these people and they're very nice about it. They do partnerships with with different affiliate programs and then they have all kinds of people on the consulting services side. So they have consultants on how to mule money between countries and hide it and everything else. These are these are three different organizations from each other. They are very very very organized and not as
cloak and dagger as the video I just showed you. So let's look at a timeline. Now this is an actual ransomware and it is using fishing. But let's go through it. So they do a ton in recon. This is where they find their this is where they spend most of their time is on the recon side of the house. How do I get into your infrastructure? Is it credentials? Is it a fishing tack? How do I get in there? So then they turn around and they do a weaponized office document or something, a PDF of some sort, something like that. If that gets clicked on, uh, so they send it as a fishing attack. If it
gets clicked on, uh, now you have your victim. Have the victim malware is installed, usually a botnet of some sort. Then the victim is infected. Now the attacker gains control. Now here's the kicker. they they have it this long thing. This is a fairly long timeline, but that could be really short or it could be really long. So, they're already in. So, the average is 21 days. So, 21 days that someone's dwell time within your environment before you find them. It's usually 21 days. I've seen some up around 380 days. But 21 days is kind of the norm if you're a very good security posture as an organization. uh thing is is that they can actually
tell if you're catching on to them, if they catch on to you. So, until they you know that they're there, they're going to download every bit of information they possibly can from you. Every record, go east, west, do whatever they can. But if they find that you're actually catching on to them, they'll instantly do ransomware. Instant. They'll stop right there and just go ahead and and deploy. Okay? So, some kill change takes hours, even weeks. Some are a lot shor shorter. So this is an actual fish fishing attack. I want one and I'm going to pause this at one point. So this is just on a GitHub. You can actually go and download it. Actually, you don't
download it. You actually go to their site. You actually run it. It's actually kind of neat. That's the technical guy in me thinks it's neat. It's horrible to people, but yes, it's kind of cool. So they go and they click on it. They run it. And I'm going to pause right there. Can I pause that before it goes? Yes. So, they've already built all of these screens for all of these applications. It's already pre-built. I want to do one for LinkedIn, click on LinkedIn. I want to do one for Shopify and blast it out to a whole bunch of people. Go ahead. It'll create the screen exactly for what? Well, I wouldn't say exactly. You can
tell the difference if you pay attention, but most people don't pay attention. This is a lot. PayPal, right? So, you can actually click it and they actually create it for you. So, we'll just run through. So, choose nine, which is actually LinkedIn. So, they run their server, goes through, it actually creates it, gives you back a link. So, waiting for victim. So, there's the link. Now you put that link, you send it out to whoever. But if you click on the link, it actually pops up with your sign in for LinkedIn. This again, you're not on LinkedIn. That's what it comes up and looks like. So, and then if you actually go and sign in, you can actually see a
little bit of a difference here. So, this is the actual LinkedIn versus the the fake one. Screen backgrounds are different. Everything else kind of looks the same. So, we're now going to actually log in to what we think is the real LinkedIn, but it's not. Um, once you actually go and put in your password and you sign it in, don't save the password. No one ever saves the password. Um, it actually goes back here. It actually gives you all the information on the person. what IP address they're coming from, what agent they used, where they came from, and then credentials down here. Actually shows you the actual password that they used to get on to
LinkedIn. It's all there. Then you can actually test it if you want. Go ahead and download it and run it and see if it passes or not, which it does. I didn't create a bloody thing. I just clicked on a link and got someone to make it for me. like it's getting kind of scary on how readily available this stuff is. Now, this is an actual so I actually found when we're going through stuff an actual ransomware negotiation and you'll see what I mean by the help desk. I wish every help desk on the planet was as nice as these people because it is phenomenal. So, this is what pops up on your screen when you get ransomware from
this particular organization. And a couple things I'm going to point out is do not touch anything cuz you may damage the files and we won't be able to do anything as the person who ransomware you to to get it back. Uh you have two days to get back to me. And if you do, you'll get a very special price. Very salesy. Like isn't that cool? Yeah. Limited time offer. If you get back quick, we'll give you a special price. Your whole network was fully compromised. We downloaded more than two terabytes of private sensitive data off your infrastructure. Like they're very specific. They will tell you. They even show from file structures that you actually have in your
environment. So let's look at the actual chat. So this is a chat room between an actual ransomware organization and a customer. So support, hello, how can I help you? Right? Uh hello. What do we need to go do? Get our data back. uh get the data deleted first off your servers and unlock our files, right? Well, you have 30,000 infected machines in your environment worldwide, right? Uh the price of uh $10 million, you get two services from us. The we'll decrypt your stuff and we'll delete all of the downloaded information that we got from you. We'll delete all of it so it we don't put it we won't put it out in the world. And on
top of that, we will actually down here, we'll actually do two files for you to prove that we can actually decrypt your files. Two random files just to prove because just so everyone knows, not all ransomware people out there, even though you get it and you're encrypted, a lot of them don't actually get the crypto key when they do it. So, you pay it and they still can't decrypt you. So if you do get hit, make sure that you get them to proof of life that your files still exist. Okay. But yes, support says we will turn around and we'll make it. We'll show you that we can. So in your message, you left us. You mentioned a
very special price. We reached out to join. Uh we did get to you in two days, but like how is 10 million a special price? They come back. Yeah. No, it's not special, right? But um we did offer you a we will give you a special price if you're willing to pay immediately. Okay. So their special price though is 20. They try to negotiate. So again, I appreciate the discount. I don't know about you, but as a customer, I would not be this polite. I wouldn't super polite. I guess they're afraid to piss these guys off. So anyway, 8 million is not really a special price either. They gave him 20% discount. They're trying to go in at 3.7
million. They come back and say, "Yeah, we appreciate your offer, but we're not going to touch that because our service is very important to you." Right? So, unfortunately, the amount is not not good for us, but we'll give you another 5% in in discount if you pay right away. Um, or we'll put you on payment plan. give me four million now and we'll decrypt all of your stuff and then we can put you on a payment plan and once we receive the rest of the money then we'll delete all your files off our servers. Like how cordial is this? Like this is insane. Also part of their service is they tell you how to avoid this in the
future. Again, how nice is help desk and support to actually give you how they got into your infrastructure. Now, do I believe that this is how they got in? Yeah, I don't know, right? But at least it's something to look at. They're saying turn off all local passwords, force force end on administrator access, so have timers associated to it. Inroup policy set um W digest to zero. So, it never stores credentials, right? Most cases enough standard Windows software. So, what they're saying is that don't count on antivirus. Antivirus will not work for most most ransomware solutions today. Install endpoint detection and response security because that's behaviorbased not not signaturebased. Okay. So huge difference today than what it used to be. Also for
huge companies suggest three system administrators working 24 hours, maximum of four admins working three shifts eight hours per day. I'm sorry, man, but I don't know of any organization that has necessarily that capability. Also, with the cyber security shortage. So, that's out there. Um, take a look at services to add and augment to your environment. Then they go back, thank you for all this in a very timely manner. Again, super cordial guy. You're welcome. It's a pleasure to work with professionals. My help desk isn't this nice to anybody. at all. So, please confirm you write down all the important stuff because we're going to remove but we'll leave the chat open to you for any support if necessary. Well,
how nice of them. Just gave you 8 million and you're going to keep a chat open into a very bad organization. So, just a couple closing thoughts. So, these are lessons learned. This is for everybody, right? So, patching visibility. If you can't see it, if you can't see it, you can't protect it. You just can't. It's impossible. So having traditional layer three at your core just doesn't work anymore. It doesn't because you're only seeing that layer three. You're not seeing layer 7. So ensure you have the right tools. Oh, also if you fail the plan, you plan to fail. So you should have all of these incident response plans in place. You should test them. Not just put the plan in place,
but test them to see if they work. And you have to include all scenarios, not just technical ones. Social engineering is a huge thing. Everyone's heard of MGM and what happened with them for the most part. That was social engineering. That had nothing to do with technical. It had to do with planning and procedures. It's not technical. Let's face it, Vegas was created by mob. They have more money than anywhere on the planet. they can spend the money to put in the proper security. Plus, they have to because they're a lottery group and they still got hit by something very simple which I'm going to show you in a minute. Um, so yeah, just kind of pay
attention to some of this. Now, this I'm so uh chat GBT and all that kind of stuff. Um, AI. So, what we did and we did this actually on uh day for yesterday. We put in a bunch of words, right? So, we created this and then based on 10 seconds of recording somebody 10 seconds, it the AI came back with "Hi sweetheart. It's me. I've just been arrested for speeding on my motorbike. It isn't a problem, but I need to pay $5,000 dollars bail. Can you quickly send it to my bank so they can release me and I can sort this out? Here's my paid. Love you. Okay, so that's a 10 seconds of anyone in this room like
all of you guys could have been recording me for the last 25 minutes or 30 minutes and you would get a much better sample size than 10 seconds. But this is based on 10 seconds. Okay. So, let's look what happens with 10 minutes. So, again, think of every public person that speaks in the world. That's Hi, sweetheart. It's me. I have just been arrested for speeding on my motorbike. It isn't a problem, but I need to pay $5,000 in bail to get out of lockup. Can you quickly send the money through to the police station so they will release me and I can sort this out? Here's the police's pay ID. Love you. See, you can. That sounds a whole lot
better, but it's still only 10 minutes of a person's clip. So, so MGM Grand got hit because someone left a voicemail for support and support changed their password and sent it to them because they were high up within the organization. It's part of the reason why they got in. Anyone can do this. This is on any AI platform around the world. So you can do deep fakes, not only a voice, but you can do it a video, too. It's not a problem. As long as you got some form of pictures of an individual, you can create it. So don't just think of the technical side. Think of the social engineering side because this stuff is coming fast and furious
because it's all open. Hi, sweetheart. Hi sweetheart. It all right. Final thoughts. So I got two. Yeah, this is final thought. So this is a company called Blackax. They're created in 1977. They're a really nasty group of people. They have 30,000 employees or axemen. They're out of Nigeria. Their main business was since 1977 street crime, torture, human trafficking, uh moneyaundering, that kind of stuff. But their number one revenue now is internet fraud. So think of it in 1977 there was very little internet fraud but now their main their main revenue stream is internet fraud. That shows you what's happening with these organizations. Now this is the whole debate of do you pay ransomware or not. So if you pay it say
against a company to someone like black they're using that money to do more of the nasty stuff on the back end also. So it it enables them to buy guns, hire more people, finance terrorist groups, that kind of stuff. But then you have the other side. A hospital gets hit with ransomware or someone's life's in danger. So again, I hate I wouldn't never want to pay for ransomware because it just creates a business for them. But if I'm in an alley and someone comes over with a gun and asks me for my wallet, I'm giving them my goddamn wallet, right? I am. I'm going to give it to them because someone's life is at stake. So, everyone can debate and do
the high moral ground say I'm never going to pay for ransomware. Um, I don't think it's as cut as cut and dry as that. So, I want to make sure everyone understands it's if you need help with that kind of stuff, there's lots of people out there that have gone through it that can help you through it. And that's it. Any Thank you very much.
Oh, and we're by our booth is by the bar, so anytime you want you can come and hang out. Oh, it's Chris. Yeah, Glenn, just a quick question. Do you know why Turkey was by far the number one ransomware attacked country? Uh, so did everyone hear that? There was Turkey and then there was Italy and they were far and away way higher than any other country for ransomware targets. Do you know why? So from my understanding, so don't quote me on it, but my understanding when we were going through it two days ago, uh it's because Turkey has some of the lowest IT capabilities in the world. They're not as advanced from a cyber security standpoint. So that makes them
easy easy targets. Got it. Okay. Thank you. No, thank you. Any other questions? Wow, you guys are quiet again. We'll be near the bar. Or I bet you won't be as quiet