COM Hijacking Voodoo
Speakers
Tags
CategoryTechnical
About this talk
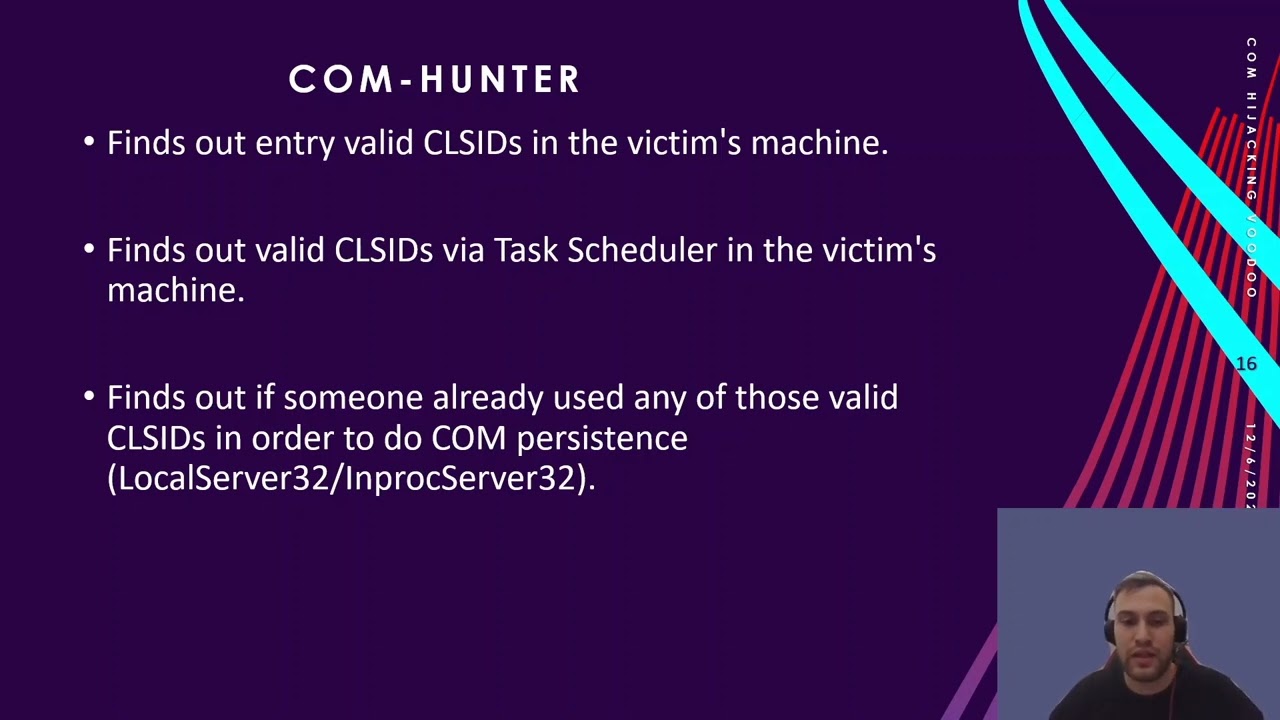
Abstract: During long-term adversary simulation engagements, host persistence is a useful method of regaining access to a compromised workstation or server, without having to reabuse the initial foothold all over again. COM object hijacking is a unique technique in which a default system-wide COM Object can be replaced by malicious software and loaded in its place. In this presentantion will release COM-Hunter tool. COM-Hunter is an open source upcoming tool written in C# which helps you to find valid CLSIDs more eficiently. Moreover, it automates all the process of the persistence in a workstation/server. Bio: Nick Vourdas is a «Young Padawan» and Cyber Security Consultant based in Greece. He has a dream that one day will become a «Jedi Master». Nikos studied at University of Western Macedonia (Kozani, Greece) as a Informatics Telecommunication Engineer. He holds OSCP and OSWP certifications. His prior working experience includes the Cyber security Directorate department of the Greek National Defense. From the age of 18, Nikos participates in Bsides Athens and Bsides Cyprus as a CTF organizer. He loves open source but one day Microsoft's Active Directory «stole» his heart... He evolves to Web Application, Internals, Externals Infrastructure Penetration Tests and Source Code Reviews. You can call him «nickvourd» or «ncv». His favorite phrase/slogan is «Last but not least, It is what it is, boyz!».





