ICS Intrusion KillChain explained with real simulation

Speakers
About this talk
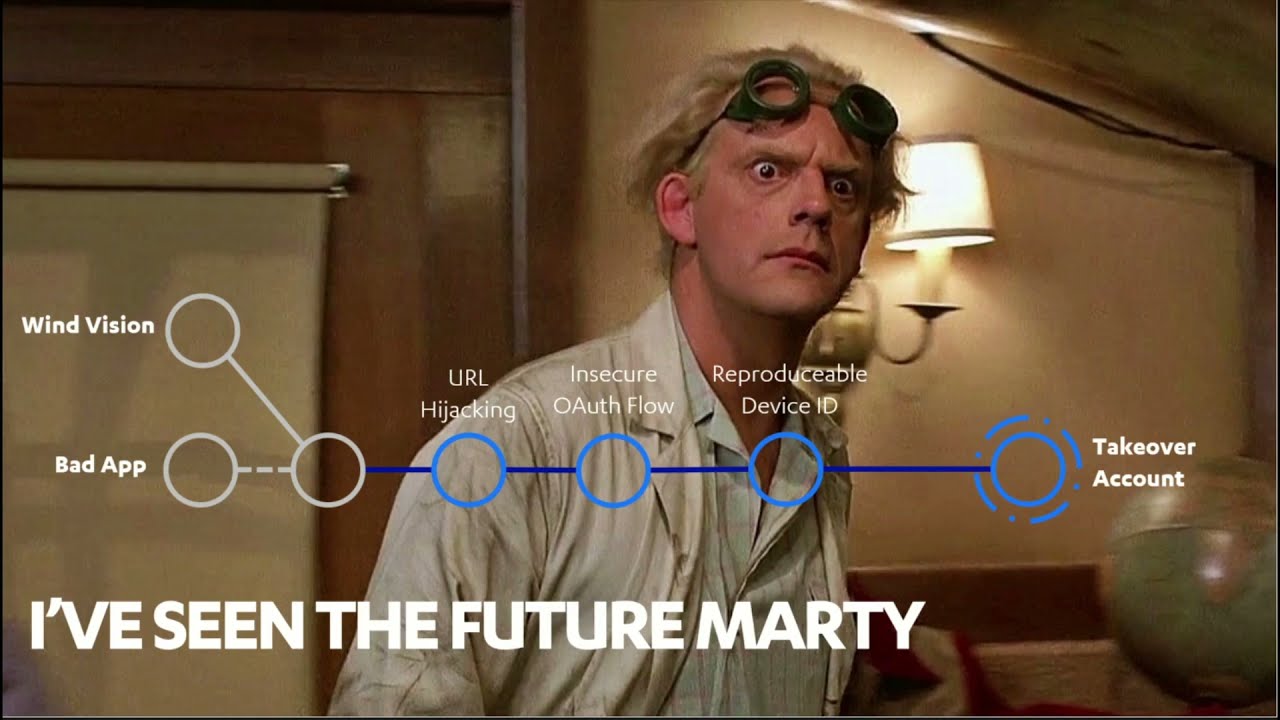
Abstract: Cyber attacks on Industrial Control Systems (ICS) differ in scope and impact based on a number of factors, including the adversary's intent, sophistication and capabilities, and familiarity with ICS and automated indutrial processes. In order to understand, identify and address the specific points that can prevent or stop an attack, a systematic model known as «Cyber Kill Chain» is detailed, a term that comes from the military environment and registered by the Lockheed Martin company. While most are familiar with terms and theoretical diagrams of how security should be implemented, in this talk we want to present live how an attack chain occurs from scratch to compromise industrial devices, the full kill chain. The goal is to land these threats into the real world without the need to carry out these attacks with a nation-state budget. We will present: Introduction to the industrial security model Real scenario attack with a laboratory of industrial devices on stage for simulation. Kill chain in real time step by step: form Internet to ICS internal network. How to discover and exploit new vulnerabilities. Recommendations to follow. All this regardless of the brands and models of the devices and software used, where the most predominant factors are mostly the lack of projility in the implementation and operation of these environments and specially what are the skills level of the attackers. Bio: Professional with solid skills and knowledge in pentesting methodologies such as OWASP and OSSTMM, with extensive expertise in projects of Ethical hacking web applications, mobile applications and infrastructure, ATM Pentesting and Code analysis. He has extensive experience in the development of exploits for the Metasploit Framework, with excellent command of Python, PHP, Java, C #, C and Ruby programming languages. He developed a translation extension for Mozilla Firefox that currently has more than half a million active users: https://addons.mozilla.org/firefox/addon/to-google-translate/. He has participated in international computer security competitions, together with the Latin American team NULL Life.